The attack begins with apps that were previously available on Google Play that appear to be simple tools such as cleaners, games, or gallery utilities. When a user downloaded and opened one of these apps, it appeared to behave as advertised, giving no obvious signs of malicious activity.
In the background, however, the app contacts a remote server, profiles the device, and downloads root exploits tailored to that device’s specific hardware and software. If the exploits succeed, the malware gains full control of the device. From that moment onward, every app that the user opens are injected with attacker‑controlled code.
This allows the operators to access any app data and exfiltrate it to their servers. One of the targeted apps is WhatsApp. We recovered a payload designed to execute when WhatsApp launches, gather all necessary data to clone the session, and send it to the attacker’s infrastructure.
In total, we identified more than 50 of these malicious apps on Google Play, with at least 2.3 million downloads.
McAfee’s mobile research team identified and investigated an Android rootkit campaign tracked as Operation Novoice.
- Thread starter Khushal
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
That report describes a very serious Android threat, but the important point is that the WhatsApp part should be understood carefully.
What the report is claiming
According to the McAfee write-up you quoted, the attack chain is roughly this:
So the WhatsApp compromise is not being presented as a normal remote WhatsApp hack by itself. It appears to depend on the device first being infected and rooted successfully.
Important limitation
I cannot independently confirm from the VirusTotal link alone that the sample definitely steals WhatsApp sessions in the exact way described. A VirusTotal page mainly shows detections, metadata, and sometimes behavior clues, but it is not a full malware analysis by itself.
Also, I would avoid treating “targets WhatsApp” as meaning “all WhatsApp users are directly vulnerable.” Based on the quoted report, the threat seems to be:
That is a very different scenario from a direct flaw in WhatsApp itself.
What this means in practice
If McAfee’s analysis is correct, the real risk is from installing trojanized Android apps, especially on devices that are vulnerable to the root exploits used by the campaign.
Once malware gets root on Android, app isolation becomes much weaker, and theft of messages, tokens, or session-related data becomes much more plausible.
Reasonable next steps
For anyone concerned about exposure, the safest standard actions would be:
If the goal is to validate the specific sample technically, that needs deeper reverse engineering or sandbox analysis rather than just the VT page.
Bottom line
The report is plausible as a post-compromise Android malware scenario, but the WhatsApp theft claim should be read as a consequence of successful device rooting and code injection, not as proof of a standalone WhatsApp vulnerability. The safest takeaway is to treat this as an Android malware/rootkit issue first.
Sources
What the report is claiming
According to the McAfee write-up you quoted, the attack chain is roughly this:
- A seemingly normal Android app is installed
- It contacts attacker infrastructure in the background
- It profiles the device
- It tries to download and use a root exploit that matches that device
- If rooting succeeds, it can inject code into other apps
- That level of access could allow theft of data from apps such as WhatsApp
So the WhatsApp compromise is not being presented as a normal remote WhatsApp hack by itself. It appears to depend on the device first being infected and rooted successfully.
Important limitation
I cannot independently confirm from the VirusTotal link alone that the sample definitely steals WhatsApp sessions in the exact way described. A VirusTotal page mainly shows detections, metadata, and sometimes behavior clues, but it is not a full malware analysis by itself.
Also, I would avoid treating “targets WhatsApp” as meaning “all WhatsApp users are directly vulnerable.” Based on the quoted report, the threat seems to be:
- Device compromise first
- Then app-level abuse after root access
That is a very different scenario from a direct flaw in WhatsApp itself.
What this means in practice
If McAfee’s analysis is correct, the real risk is from installing trojanized Android apps, especially on devices that are vulnerable to the root exploits used by the campaign.
Once malware gets root on Android, app isolation becomes much weaker, and theft of messages, tokens, or session-related data becomes much more plausible.
Reasonable next steps
For anyone concerned about exposure, the safest standard actions would be:
- Uninstall suspicious apps immediately
- Run a scan with a reputable mobile security product
- Check Google Play Protect status
- Update Android and all apps to the latest available versions
- Change important account passwords from a known-clean device
- Re-link or review WhatsApp linked devices and active sessions
- If compromise is strongly suspected, back up essential data and consider a factory reset
If the goal is to validate the specific sample technically, that needs deeper reverse engineering or sandbox analysis rather than just the VT page.
Bottom line
The report is plausible as a post-compromise Android malware scenario, but the WhatsApp theft claim should be read as a consequence of successful device rooting and code injection, not as proof of a standalone WhatsApp vulnerability. The safest takeaway is to treat this as an Android malware/rootkit issue first.
Sources
F
ForgottenSeer 123960
Executive Summary
Operation NoVoice is a modular Android rootkit campaign distributed via over 50 malicious applications on the Google Play Store, resulting in at least 2.3 million downloads.
Confirmed Facts
The malware utilizes polyglot image files to hide its initial payload and executes privilege escalation using legacy vulnerabilities (2016-2021) to replace core Android system libraries like libandroid_runtime.so.
Assessment
Due to the rootkit's ability to patch pre-compiled framework bytecode and install a persistence watchdog, the infection survives factory resets on vulnerable devices, requiring a complete firmware flash for eradication.
Operation NoVoice is a modular Android rootkit campaign distributed via over 50 malicious applications on the Google Play Store, resulting in at least 2.3 million downloads.
Confirmed Facts
The malware utilizes polyglot image files to hide its initial payload and executes privilege escalation using legacy vulnerabilities (2016-2021) to replace core Android system libraries like libandroid_runtime.so.
Assessment
Due to the rootkit's ability to patch pre-compiled framework bytecode and install a persistence watchdog, the infection survives factory resets on vulnerable devices, requiring a complete firmware flash for eradication.
Technical Analysis & Remediations
MITRE ATT&CK Mapping
T1404
Exploitation for Privilege Escalation (Targets IPv6 use-after-free and Mali GPU driver vulnerabilities).
T1574.004
Hijack Execution Flow: Dynamic Linker Hijacking (Replaces libandroid_runtime.so and libmedia_jni.so to inject code).
T1626
Steganography (Initial payload is an encrypted file hidden after the PNG IEND marker of an image asset).
T1636
Data from Local System (PtfLibc plugin targets and extracts WhatsApp's Signal protocol encrypted databases).
CVE Profile
Relies on legacy Android CVEs patched between 2016 and 2021.
[NVD Score: High/Critical]
[CISA KEV Status: Active for historical kernel flaws]
Telemetry
Hashes 03e62ac5080496c67676c0ef5f0bc50fc42fc31cf953538eda7d6ec6951979d8
066a096a3716e02a6a40f0d7e6c1063baecbebc9cbcc91e7f55b2f82c0dad413.
IPs/Domains
api[.]googlserves[.]com
fcm[.]androidlogs[.]com
stat[.]upload-logs[.]com
prod-log-oss-01[.]oss-ap-southeast-1[.]aliyuncs[.]com.
Constraint
The campaign uses a silent audio resource named R.raw.novioce to persistently keep a foreground service alive, and disguises its malicious components under the tampered package name com.facebook.utils.
Remediation - THE ENTERPRISE TRACK (NIST SP 800-61r3 / CSF 2.0)
GOVERN (GV) – Crisis Management & Oversight
Command
Issue a fleet-wide advisory regarding unapproved third-party utility applications (e.g., cleaners, battery savers, gallery utilities) on corporately managed Android devices.
DETECT (DE) – Monitoring & Analysis
Command
Query MDM/UEM telemetry for the presence of known carrier apps (e.g., com.filnishww.fluttbuber.storagecleaner and com.wififinder.wificonnect).
Command
Monitor network telemetry for persistent beacons to api[.]googlserves[.]com or stat[.]upload-logs[.]com occurring at 60-second intervals or fallback connections between 1:00 AM and 4:00 AM.
RESPOND (RS) – Mitigation & Containment
Command
Quarantine non-compliant Android devices exhibiting indicators of compromise or running an OS security patch level older than 2021-05-01.
RECOVER (RC) – Restoration & Trust
Command
For confirmed infections on legacy devices (Android 7 and below), execute a complete firmware re-flash. Standard factory resets are insufficient because the rootkit installer (CsKaitno.d) writes directly to the system partition.
IDENTIFY & PROTECT (ID/PR) – The Feedback Loop
Command
Enforce strict MDM policies restricting app installations entirely to an approved enterprise app catalog, disallowing end-user downloads from the consumer Play Store.
Remediation - THE HOME USER TRACK (Safety Focus)
Priority 1: Safety
Command
Disconnect from the internet immediately if you suspect an infection and your Android Security Update patch level is older than May 1, 2021.
Command
Do not log into banking/email until verified clean.
Priority 2: Identity
Command
Revoke all active sessions for messaging apps (specifically WhatsApp) and reset passwords/MFA using a known clean device (e.g., a secondary trusted computer or a phone on 5G), as the malware explicitly extracts the device's Signal protocol identity keys and registration ID to clone sessions.
Priority 3: Persistence
Command
Understand that a standard factory reset will not clear this rootkit if the exploitation phase was successful. If the device was compromised and runs Android 7 or older, it must be reflashed with official firmware by the manufacturer or completely replaced.
Hardening & References
Baseline
CIS Benchmarks for Google Android.
Framework
NIST CSF 2.0 / SP 800-61r3.
Vulnerability Check
All Android devices with a security patch level of 2021-05-01 or higher are immune to the rootkit exploits associated with this command-and-control server. Enable automatic OS updates to ensure consistent baseline protection.
Source
McAfee Labs / Advanced Threat Research
This exploit sounds horrific, i.e., an infection that can't be fixed with a factory reset. OTOH, on first read—especially with the post above—it might not sound so bad; who still has (or uses) a 12-year-old phone (Android 7)?
This is a good warning for a user using an out-of-date phone: minimize app use to the absolute minimum and only install from the most trustworthy sources — and even then those sources can be compromised or pass apps on to others.
On reading the fine print, the Android 7.0 vulnerabilities are what the researchers were able to observe; there could potentially be other payloads in this delivery framework that can exploit newer Android versions that no longer receive security updates.All Android devices with a security patch level of 2021-05-01 or higher are not susceptible to the exploits that we were able to obtain from the command-and-control server. However patched devices that downloaded these apps could have been exposed to unknown potential payloads outside of what we discovered. The attack begins with apps that were previously available on Google Play that appear to be simple tools such as cleaners, games, or gallery utilities.
This is a good warning for a user using an out-of-date phone: minimize app use to the absolute minimum and only install from the most trustworthy sources — and even then those sources can be compromised or pass apps on to others.
Doesn't seem like many other AV vendors are well aware of this malware before Mcafee's post despite the exploit being quite dated.This exploit sounds horrific, i.e., an infection that can't be fixed with a factory reset. OTOH, on first read—especially with the post above—it might not sound so bad; who still has (or uses) a 12-year-old phone (Android 7)?
On reading the fine print, the Android 7.0 vulnerabilities are what the researchers were able to observe; there could potentially be other payloads in this delivery framework that can exploit newer Android versions that no longer receive security updates.
This is a good warning for a user using an out-of-date phone: minimize app use to the absolute minimum and only install from the most trustworthy sources — and even then those sources can be compromised or pass apps on to others.
Great discussion so far. While the technical analysis highlights that newer devices are safer, I think there’s a vital takeaway here regarding "App Hygiene."
Even if your Android version is patched, these malicious "Cleaners" and "Battery Savers" often request permissions they don't need. Operation NoVoice proves that Google Play isn't 100% foolproof. A good rule of thumb: If an app is a "Utility" from a developer you’ve never heard of, it's a red flag.
A quick tip for anyone reading: periodically check your "Linked Devices" in WhatsApp. If you see a session you don't recognize, log it out immediately. It's the simplest way to spot the session cloning mentioned in the report.


Even if your Android version is patched, these malicious "Cleaners" and "Battery Savers" often request permissions they don't need. Operation NoVoice proves that Google Play isn't 100% foolproof. A good rule of thumb: If an app is a "Utility" from a developer you’ve never heard of, it's a red flag.
A quick tip for anyone reading: periodically check your "Linked Devices" in WhatsApp. If you see a session you don't recognize, log it out immediately. It's the simplest way to spot the session cloning mentioned in the report.
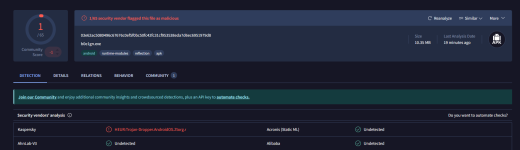
I checked VT for the first few apps. They’re no longer listed on the Play Store (or I searched wrong). For the first few, only Kaspersky flags them; I guess McAfee on VT hasn’t gotten the memo yetDoesn't seem like many other AV vendors are well aware of this malware before Mcafee's post despite the exploit being quite dated.
ps: The McAfee article is referencing a Kaspersky blog a month ago, explaining the VT Kaspersky flags.
Last edited:
No but the malware samples are not keenadu. But still how original Mcafee result is questionable.I checked VT for the first few apps. They’re no longer listed on the Play Store (or I searched wrong). For the first few, only Kaspersky flags them; I guess McAfee on VT hasn’t gotten the memo yet.
I think McAfee was flagging the new delivery framework (the loader apps); the old exploits come from the C2 and are executed by the loader.
ps: The McAfee article is referencing a Kaspersky blog a month ago, explaining the VT Kaspersky flags.
You may also like...
-
Seniors targeted in global Facebook scam spreading new Android malware
- Started by Brownie2019
- Replies: 1
-
F
-
FSecurity News Cloudflare tracked 230 billion daily threats and here is what it found
- Started by ForgottenSeer 116559
- Replies: 3
-
Fake Avast Antivirus Sites Are Spreading SpyNote Android Malware
- Started by enaph
- Replies: 1