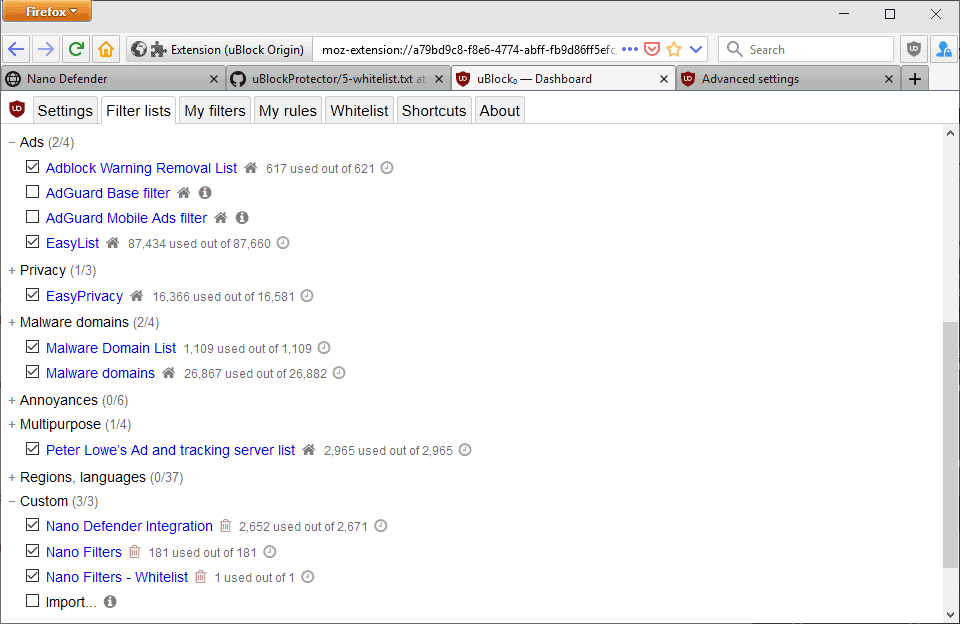
As some of you might have noticed, Nano Adblocker is now months behind upstream. It became clear that I simply do not have enough time to properly maintain the Nano projects.
At the beginning, there was no backlogs. As the projects grow, I added a backlog system to better manage open issues. That was unfortunately not enough, so I added another level of backlog -- the triage queue. Then a third level. And then a fourth one. Now the fourth level of backlog, the notification queue, has 178 issues waiting for my attention. No matter how well I organize incoming issues, if I do not have enough time to look into them, I will simply fall further and further behind. With thousands of issues backlogged, it is only a matter of time that the Nano projects collapse.
But there is good news. A team of Turkish developers is in the process of acquiring Nano Adblocker and Nano Defender. With more people and resources, hopefully they will be able to put an end on this backlog madness, and finally give Nano Adblocker some real development time instead of constantly trying to catch up to upstream. The transition is still taking place, so I would like to ask for your patience. I will have more details on this in the upcoming days or weeks.
I know some of you might be concerned about cybersecurity. So far, the new developers kept all of their promises and rarely made any excuses. On top of this, Google is making the WebStore review process stricter and stricter. So strict, in fact, that I had problems publishing updates in the past. While annoying to developers, this strict review process is exactly what shielding users from cybersecurity incidents. So I do not believe there is a reason to be concerned at this moment.
Full announcement and discussion here:
[Announcement] Recent and upcoming changes to the Nano projects · Issue #362 · NanoAdblocker/NanoCore
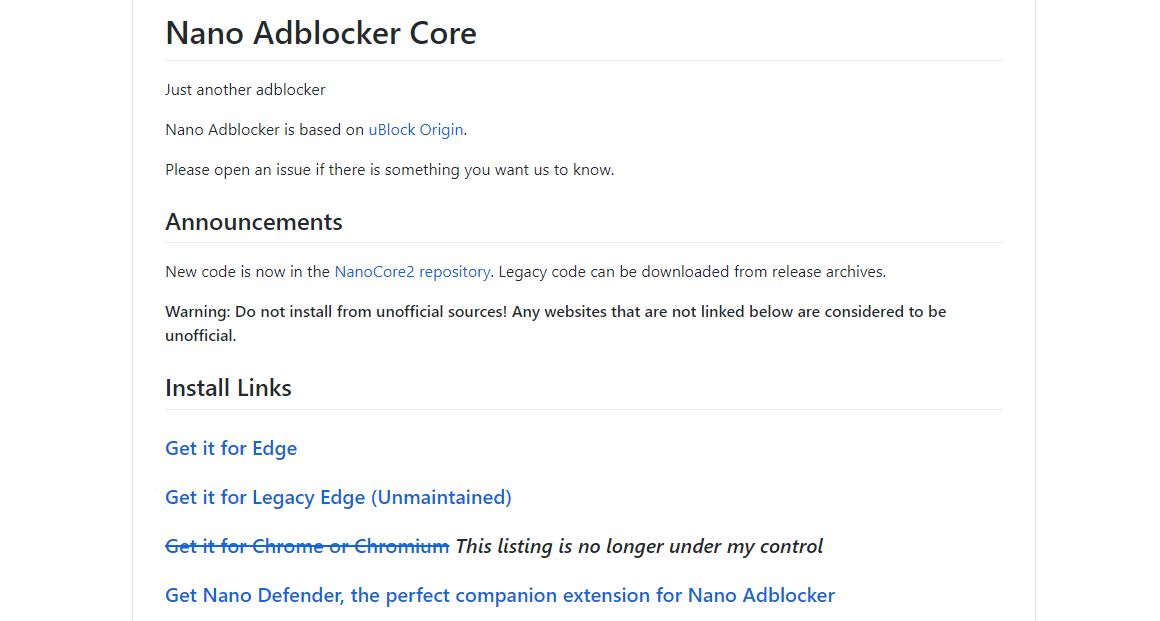
Important updates and disclaimers: The WebStore listings are no longer under my control. I am not responsible for the actions of the new developer(s). If you feel concerned about the recent changes...