silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,210
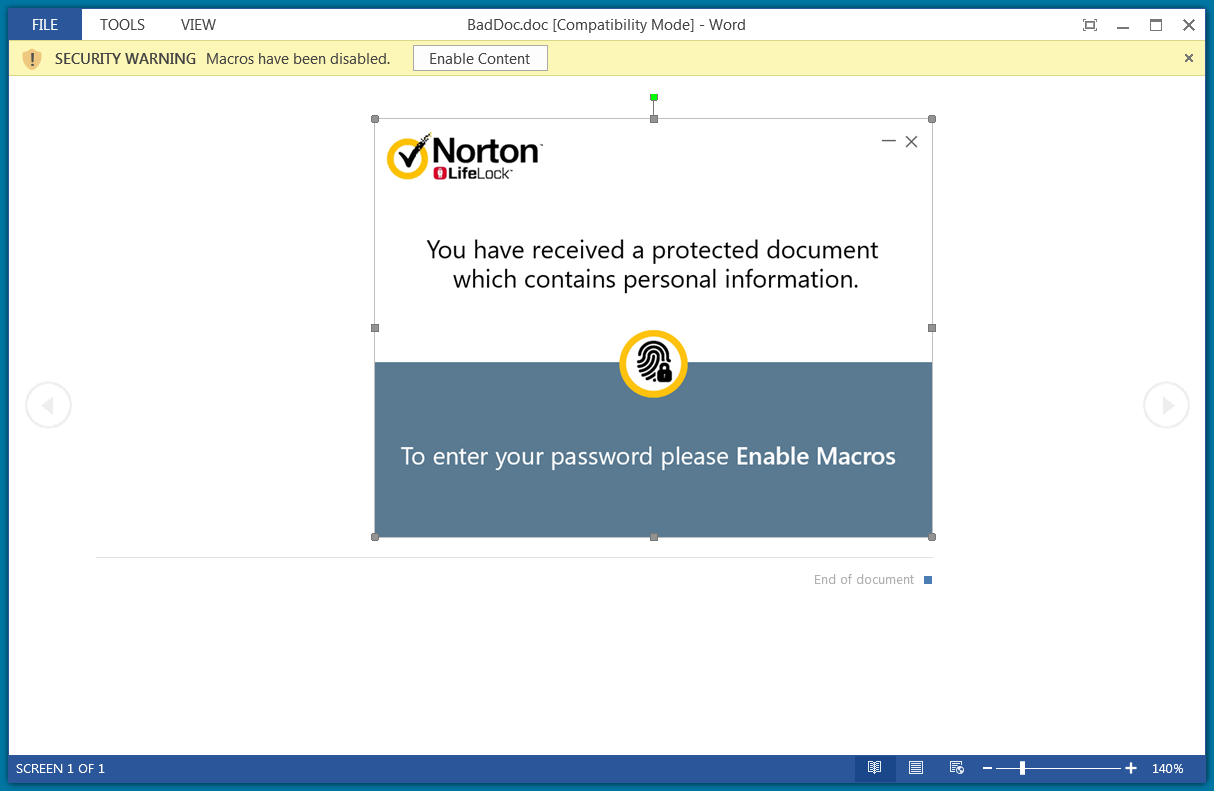
Cybercriminals behind a recently observed phishing campaign used a clever ruse in the form of a bogus NortonLifelock document to fool victims into installing a remote access tool (RAT) that is typically used for legitimate purposes.
The malicious activity has the hallmarks of a seasoned threat actor familiar with evasion techniques and offensive security frameworks that help install the payload.
Hooking the victim
The infection chain starts with a Microsoft Word document laced with malicious macro code. The threat actor relied on a creative tactic to entice victims into enabling macros, which are disabled by default across the Office suite.
Under the pretext of a password-protected NortonLifelock document with personal information, victims are asked to enable macros and type in a password that is most likely provided in the phishing email.
The malicious activity has the hallmarks of a seasoned threat actor familiar with evasion techniques and offensive security frameworks that help install the payload.
Hooking the victim
The infection chain starts with a Microsoft Word document laced with malicious macro code. The threat actor relied on a creative tactic to entice victims into enabling macros, which are disabled by default across the Office suite.
Under the pretext of a password-protected NortonLifelock document with personal information, victims are asked to enable macros and type in a password that is most likely provided in the phishing email.