D
Deleted member 178
Thread author
We've just released a new free tool: SysHardener
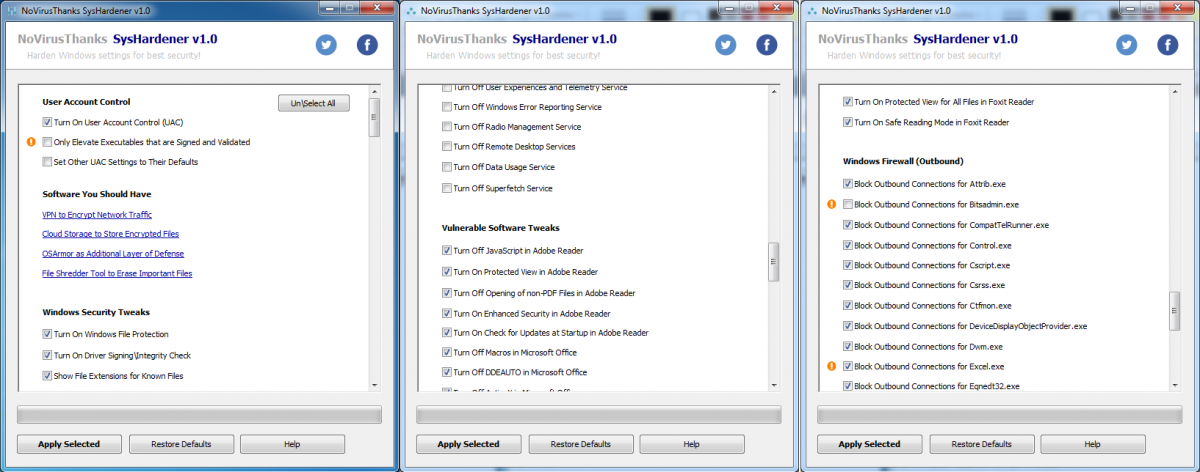
This free security tool helps you harden Windows settings to mitigate online threats. You can enable UAC (commonly disabled by malware), unassociate bad file types (i.e JS, VBS, VBE, WSH, etc), disable autorun.inf on removable devices, enable DEP and SEH on all programs, turn off Windows Script Host (Wscript.exe), turn on SmartScreen, disable unneeded Windows services, disable Javascript on Adobe Reader, disable macros\OLE\Activex on Office, disable Javascript on Foxit Reader, block outbound connections of commonly hijacked system programs (i.e powershell.exe, wscript.exe, winword.exe, etc) via Windows Firewall rules, and much more. All these system hardening tweaks can help mitigate common today threats. Especially useful also the Windows firewall rules to block outbound connections of powershell, wscript, mshta, winword, excel, etc so an exploit cannot download the remote payload.
Product page & download:
Harden Windows Settings with SysHardener | NoVirusThanks
Works on Vista+ OS and is freeware.
Nice tool, tried it, adopted it. it does what i used to do manually.
This free security tool helps you harden Windows settings to mitigate online threats. You can enable UAC (commonly disabled by malware), unassociate bad file types (i.e JS, VBS, VBE, WSH, etc), disable autorun.inf on removable devices, enable DEP and SEH on all programs, turn off Windows Script Host (Wscript.exe), turn on SmartScreen, disable unneeded Windows services, disable Javascript on Adobe Reader, disable macros\OLE\Activex on Office, disable Javascript on Foxit Reader, block outbound connections of commonly hijacked system programs (i.e powershell.exe, wscript.exe, winword.exe, etc) via Windows Firewall rules, and much more. All these system hardening tweaks can help mitigate common today threats. Especially useful also the Windows firewall rules to block outbound connections of powershell, wscript, mshta, winword, excel, etc so an exploit cannot download the remote payload.
Product page & download:
Harden Windows Settings with SysHardener | NoVirusThanks
Works on Vista+ OS and is freeware.
Nice tool, tried it, adopted it. it does what i used to do manually.
Last edited by a moderator: