Often times, users are unsettled that with F-Secure, you can "kill" F-Secure in Task Manager by terminating the F-Secure/Ultralight Hoster processes. This is definitely true, but it doesn't necessarily mean malware can do the same.
Here's some tests. At the conclusion of each test, I tried to execute a script that downloads an EICAR test file and executes it, instead of trusting the Windows Security Center status:
Test #1: Kill in Task Manager: F-Secure Killed
Test #2: Use Services.msc, stop the F-Secure related services: F-Secure killed.
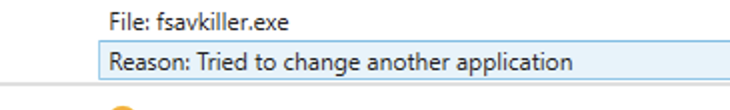
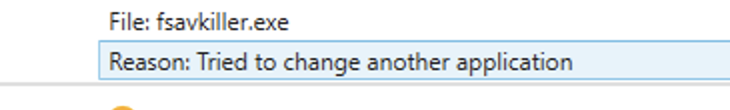
Test #3: Use .NET executable, kill "fshoster" and "fshoster64" processes: Protected. DeepGuard triggered, "Tried to change another application"
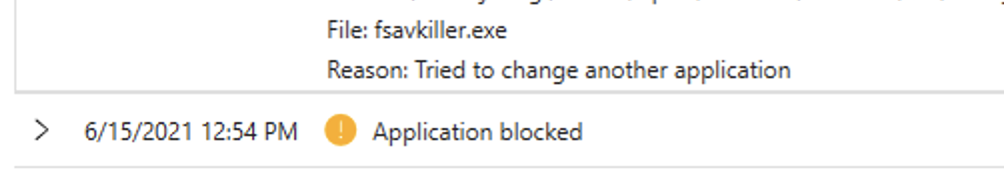
Test #4: Use .NET executable, stop F-Secure services: Protected, DeepGuard triggered, "Tried to change another application"
Test #5: Use Batch file and taskkill or net stop to do the same thing as test 3 and 4: F-secure terminated, protection lost
Test #6: Use Python script (and Python from the Windows Store) and shell out to taskkill or net stop to do the same thing as test 3 and 4: F-secure terminated, protection lost
Conclusion:
DeepGuard stops certain methods of killing F-Secure but not others, pretty consistent with DeepGuard's strengths and weaknesses. This protection is relatively weak and can easily be defeated by use of trusted binaries to do the dirty work.
Here's some tests. At the conclusion of each test, I tried to execute a script that downloads an EICAR test file and executes it, instead of trusting the Windows Security Center status:
Test #1: Kill in Task Manager: F-Secure Killed
Test #2: Use Services.msc, stop the F-Secure related services: F-Secure killed.
Test #3: Use .NET executable, kill "fshoster" and "fshoster64" processes: Protected. DeepGuard triggered, "Tried to change another application"
Test #4: Use .NET executable, stop F-Secure services: Protected, DeepGuard triggered, "Tried to change another application"
Test #5: Use Batch file and taskkill or net stop to do the same thing as test 3 and 4: F-secure terminated, protection lost
Test #6: Use Python script (and Python from the Windows Store) and shell out to taskkill or net stop to do the same thing as test 3 and 4: F-secure terminated, protection lost
Conclusion:
DeepGuard stops certain methods of killing F-Secure but not others, pretty consistent with DeepGuard's strengths and weaknesses. This protection is relatively weak and can easily be defeated by use of trusted binaries to do the dirty work.