Hey MalwareTips community,
Privacy Badger (EFF’s legendary “learn-as-you-go” tracker blocker) is now over 10 years old.After all the Manifest V3 drama, uBlock Origin dominance, and browsers baking in tracking protection, does anyone here still run it daily?
What’s new in the 2025 version:
But the eternal debate rages on:
Drop your browser + how many trackers Badger is currently blocking per day!Did the 2025 updates bring you back, or is the Badger finally ready for retirement?
EFF loyalists vs. list gang – fight!
Privacy Badger (EFF’s legendary “learn-as-you-go” tracker blocker) is now over 10 years old.After all the Manifest V3 drama, uBlock Origin dominance, and browsers baking in tracking protection, does anyone here still run it daily?
What’s new in the 2025 version:
- Full Manifest V3 support with declarativeNetRequest + dynamic rules
- Now blocks link-tracking (ampproject, bc.marfeel, etc.) automatically
- “Social Widget Replacement” got smarter – replaces Facebook/Twitter buttons with click-to-activate without breaking layout
- Added first-party tracker detection (yes, even Google Analytics on google.com gets red-flagged if overreaching)
- New “Do Not Track” + Global Privacy Control enforcement
- RAM usage down to ~25 MB
- Still 100% open-source, no telemetry, no accept-list for cash
But the eternal debate rages on:
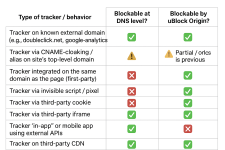
- “It learns what uBlock would block anyway – redundant”
- “I love that it auto-allows when a site breaks – zero maintenance”
- “It still misses half the fingerprinting scripts uBlock catches with lists”
- “I run both – Badger for learning, uBlock for aggressive lists”
Drop your browser + how many trackers Badger is currently blocking per day!Did the 2025 updates bring you back, or is the Badger finally ready for retirement?
EFF loyalists vs. list gang – fight!