- Jul 3, 2015
- 8,153
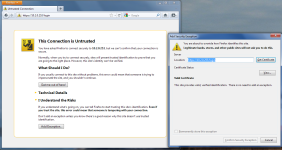
For as long as we’ve had access to public Wi-Fi networks—the ones in the airport, the Starbucks around the corner and your hotel room—we’ve been told the same thing. They’re unsafe. You should never enter sensitive information while on a public network, the advice goes, or even think about logging into your bank account. The second you log on, you’re practically begging hackers to steal all your data.
But while you should always think twice before entering sensitive information, the public Wi-Fi story has changed. In recent years, the internet itself has gotten more secure. So have your devices and the networks themselves. It’s still true that logging on to a public Wi-Fi incurs certain security and privacy risks—but they’re generally the same ones you encounter anytime you’re online, at least in the U.S. Connecting to networks comes with different risks in different countries.
The most problematic thing about public Wi-Fi isn’t security but privacy. You know those login pages that show up when you connect at a coffee shop or hotel? Don’t confuse that login with a security measure. You’re actually agreeing to the network’s terms of use. Usually that includes a list of things you can’t do while online, such as mining cryptocurrency.
Read more at Wall Street Journal.
But while you should always think twice before entering sensitive information, the public Wi-Fi story has changed. In recent years, the internet itself has gotten more secure. So have your devices and the networks themselves. It’s still true that logging on to a public Wi-Fi incurs certain security and privacy risks—but they’re generally the same ones you encounter anytime you’re online, at least in the U.S. Connecting to networks comes with different risks in different countries.
The most problematic thing about public Wi-Fi isn’t security but privacy. You know those login pages that show up when you connect at a coffee shop or hotel? Don’t confuse that login with a security measure. You’re actually agreeing to the network’s terms of use. Usually that includes a list of things you can’t do while online, such as mining cryptocurrency.
Read more at Wall Street Journal.