- May 17, 2015
- 705
Sandboxie+ BETA RELEASE v0.9.0a / 5.51.0
https://github.com/sandboxie-plus/Sandboxie/releases/tag/0.9.0a
Note: Pre-release
This build is a Test build, a BETA RELEASE, testing the new functionality to use Windows Filtering Platform (WFP) to implement a per sandbox firewall.
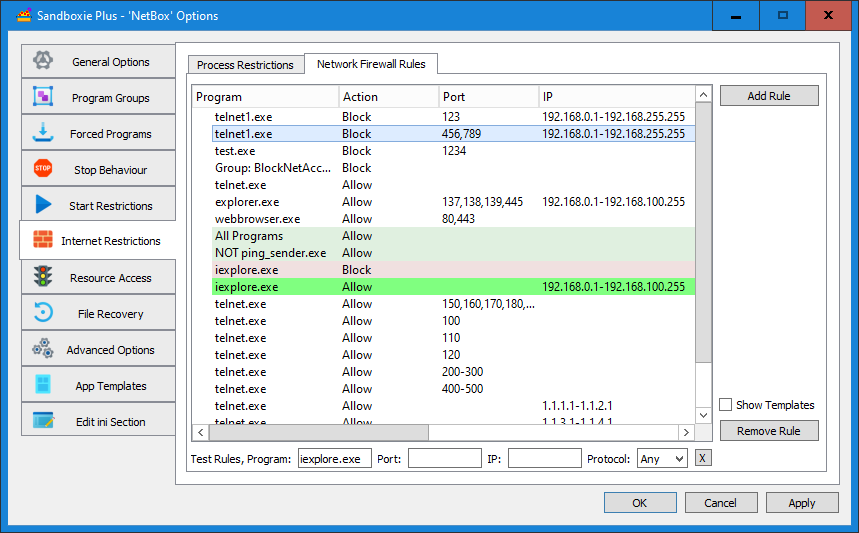
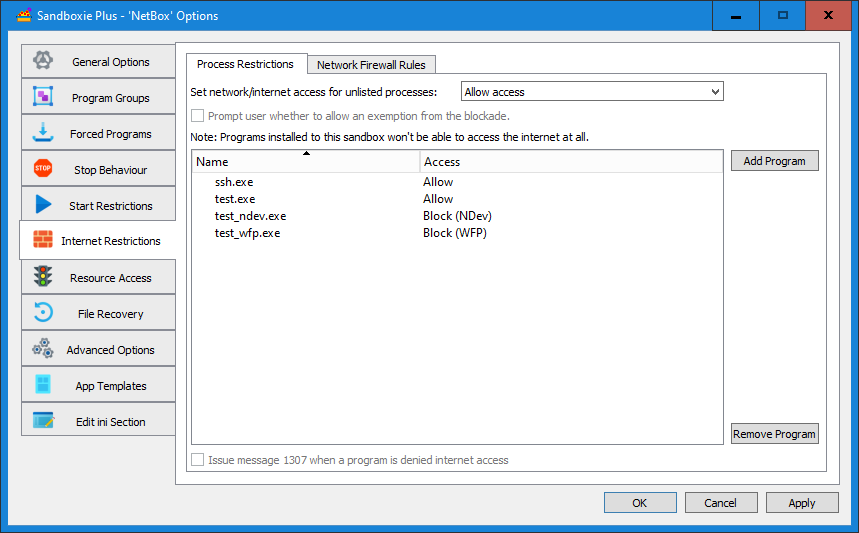
This functionality needs to be enabled in the global Sandboxie settings, and the driver needs to be reloaded (or the PC rebooted) for the feature to be activated. Once this is done the firewall rules which can be configured in the network options of each sandbox, will be enforced by the driver.
If the WFP support is not enabled the same rules still can be set and are used, but will be applied only by a set of user mode hooks, unlike the WFP implementation they will apply only to outgoing connections and there are no enforcement guarantees as user mode hooks can be bypassed or disabled by a malicious application.
The rational behind implementing this functionality in user and kernel mode (driver) instead of driver only is twofold for once it allows for debugging of the rule processing code as booth modes use the same code to make decisions based on the preset rules. Second the WFP callouts are global i.e. they are triggered for any process on the system whether its sandboxed or not, in the lather case they don't do anything and the use of a hash map to identify sandboxed programs that require action should provide optimal performance. That said users who run a 3rd party firewall which they may prefer may not want to many firewalls being active at once, while still wanting to use some per sandbox network rules for compatibility and not security reasons.
Also please note that with this build the old "BlockPort=..." functionality is completely dropped, the default port block rules are now implemented by the new user mode firewall component, if you have custom BlockPort entries in your sandboxie ini they will need to be updated by hand to the new format, for example "BlockPort=137,138,139,445" -> "NetworkAccess=Block;Port=137,138,139,445"
The rules are applied based on a specific decision priority:
When configuring per process network access restrictions and WFP is enabled it is possible to choose between a WFP based approach and the old sandboxie way of blocking the network device end points. The later approach is more absolute, but is know for causing some application to crash.
If you have issues with an update installation, just uninstall the previous version keeping the sandboxie.ini and reinstall the new build.
[...]

 github.com
Note: pics r paste from https://www.wilderssecurity.com/threads/sandboxie-plus-0-9-0.439305/
github.com
Note: pics r paste from https://www.wilderssecurity.com/threads/sandboxie-plus-0-9-0.439305/
https://github.com/sandboxie-plus/Sandboxie/releases/tag/0.9.0a
Note: Pre-release
This build is a Test build, a BETA RELEASE, testing the new functionality to use Windows Filtering Platform (WFP) to implement a per sandbox firewall.
This functionality needs to be enabled in the global Sandboxie settings, and the driver needs to be reloaded (or the PC rebooted) for the feature to be activated. Once this is done the firewall rules which can be configured in the network options of each sandbox, will be enforced by the driver.
If the WFP support is not enabled the same rules still can be set and are used, but will be applied only by a set of user mode hooks, unlike the WFP implementation they will apply only to outgoing connections and there are no enforcement guarantees as user mode hooks can be bypassed or disabled by a malicious application.
The rational behind implementing this functionality in user and kernel mode (driver) instead of driver only is twofold for once it allows for debugging of the rule processing code as booth modes use the same code to make decisions based on the preset rules. Second the WFP callouts are global i.e. they are triggered for any process on the system whether its sandboxed or not, in the lather case they don't do anything and the use of a hash map to identify sandboxed programs that require action should provide optimal performance. That said users who run a 3rd party firewall which they may prefer may not want to many firewalls being active at once, while still wanting to use some per sandbox network rules for compatibility and not security reasons.
Also please note that with this build the old "BlockPort=..." functionality is completely dropped, the default port block rules are now implemented by the new user mode firewall component, if you have custom BlockPort entries in your sandboxie ini they will need to be updated by hand to the new format, for example "BlockPort=137,138,139,445" -> "NetworkAccess=Block;Port=137,138,139,445"
The rules are applied based on a specific decision priority:
- A rule for a specified program trumps a rule for all programs except a given one, trumps rules for all programs
- A rule with a Port or IP trumps a rule without
2a. A rule with ip and port trums a rule with ip or port only
2b. A rule with one ip trumps a rule with an ip range that is besides that on the same level - Block rules trump allow rules
- A rule without a protocol means all protocols, a rule with a protocol trumps a rule without if its the only difference
When configuring per process network access restrictions and WFP is enabled it is possible to choose between a WFP based approach and the old sandboxie way of blocking the network device end points. The later approach is more absolute, but is know for causing some application to crash.
If you have issues with an update installation, just uninstall the previous version keeping the sandboxie.ini and reinstall the new build.
[...]
Release Release v0.9.0a / 5.51.0 · sandboxie-plus/Sandboxie
This build is a Test build, a BETA RELEASE, testing the new functionality to use Windows Filtering Platform (WFP) to implement a per sandbox firewall. This functionality needs to be enabled in the ...
Last edited:
