Tool introduction
The botnet is a new type of attack that is developed and integrated on the basis of traditional malicious code forms such as network worms, Trojan horses, and backdoor tools. From 1999, the first malicious code with botnet features, PrettyPark, appeared on the Internet. In 2002, due to the release and widespread spread of SDbot and Agobot source code, hackers manipulated a large number of zombie hosts through botnet control programs, seriously threatening users. Information and property security.
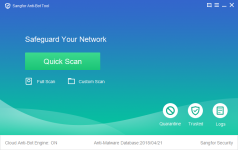
The botnet killing tool came into being in this kind of scene. It is a malware killing tool that combines local killing and cloud killing. The tool has a powerful virus database in the cloud that can identify most active virus threats on the existing network; it also has a powerful scanning engine in the local, through static analysis of the program and dynamic virtual execution, so that windows Malware has nowhere to go.
Function Description
- Feature 1: Multi-engine detection capability
The tool supports scanning of common compressed files (zip, rar, 7z, cab, etc.) and windows executables (exe, dll, sys, etc.). In the process of scanning for suspicious files, the tool uses a variety of methods to troubleshoot suspicious files. The first way is to combine the powerful local hotspot virus database to quickly identify the virus file by means of file feature comparison; the second way is to use the local engine to statically analyze the virus program to determine whether it is a virus file and pass The way of virtual execution, even if the program changes, can determine whether it is a harmful file through its behavior characteristics; the third way is the cloud killing engine, through the rich cloud file reputation library, in the process of using cloud check Protects users' host security from threats by responding to unknown threat files in seconds.- Feature 2: Support multiple scanning methods
Supports users to scan the system for fast scanning, custom scanning, and full scanning. Quick scan is to scan the memory, registry and system key directory, find the virus program that has been running in the system, modify the virus program corresponding to the registry; custom scan is to support the user to scan the specified directory, the speed is even more Fast; full scan is to support users to scan the entire operating system, the scanning range is larger, the scope of killing is more comprehensive, and the virus files are nowhere to be seen.- Feature 3: Flexible virus processing capabilities
For the threat file scanned, double-click the left mouse button or right-click to open the directory to quickly open the directory where the threat file is located, and accurately locate the file. The right mouse button menu provides a convenient and simple virus database sample upload function.
Supports the threat program scanned by the one-button isolation tool, which is fast and convenient; supports single-step isolation, users can freely choose the virus files they want to isolate for isolation operation, and support secondary deletion confirmation and fast recovery for isolated virus files. Ensure the security of user data; support users to manually add files to the trust zone. For programs that may have false positives, let the user manually add trust. When scanning again, the file will be ignored. If a file attribute in the trust zone changes, the file will rejoin the scan queue.- Feature 4: Log and report export
For each scan of the tool, the results of the scan are supported by the report. The simple and detailed report content can bring users an intuitive feeling. The report mainly shows the number of threats discovered by the tool scanning process, the directory where the threat files are located, and the modification time of the threat files. A log is saved for each scan and kill result, even if the user does not report after the scan ends, the latest killing information can be viewed, and the single or multiple packaged output of the log file is also supported.- Feature 5: Fast response capability
Support users to feedback problems found during use by text description or adding attachments. We will respond to the various needs and problems found during the use of the user's email address and phone number.
I downloaded a pack of 90 malware samples and this tool deleted 45 and disinfected 22 the rest were undetected. Not sure which engines it's using but I think I recognized some Huorong detections in there? This is a portable tool so no installation necessary, the scan speed is very fast and with 1 click (green button) it quarantines anything it finds. Neat tool which could be useful to some. I just randomly stumbled across it on virscan.org
http://edr.sangfor.com.cn/tool/SfabAntiBot_X64.7z
http://edr.sangfor.com.cn/tool/SfabAntiBot_X86.7z