5
509322
Avira has a signature for it. It's all over on this one.
Sure, but without signature you're wasted, if HIPS / BB or whatever are not able to stop it.Avira has a signature for it. It's all over on this one.
Sure, but without signature you're wasted, if HIPS / BB or whatever are not able to stop it.
As you correctly noted, "This sample and the test results are a perfect demonstration that at some point all detection\behavioral modules will fail."
P.S. AFAIK, many samples are just altered slightly to make them undetected again, recycling at it's best.
Sorry, misunderstoodI meant if Avira has a signature for it, then due to the practice of signature copying, probably most others will have one within hours.
Sorry, misunderstoodProbably yes

Yes but he wasn't meant to post in the hub - he is a new member.I noticed a new member published a new ransomware in the hub, coded by him. That can be used to reproduce this kind of test by the hub testers
here the sample
http://att.kafan.cn/forum.php?mod=attachment&aid=Mjg1MDA5N3w5ZDk5ZGQ3NXwxNDgyNjY0MzgzfDB8MjA2OTU5OA==
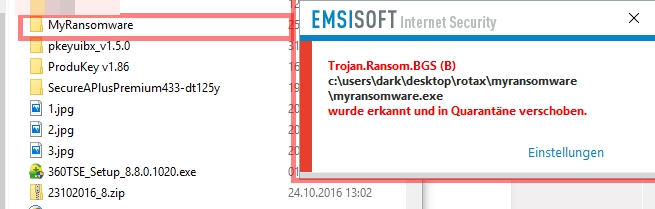
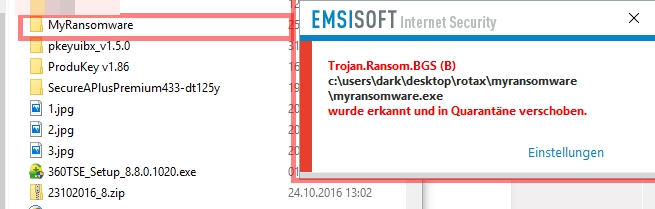
here the Passwort: MyRansomware
here Emsisoft Reaction
Why did you give us a malicious link?
SKG2016 write "Unfortunately I do not have the sample as that tester does not want to spread the ransomware but here is the file info from VirusTotal as per 25/12/2016 "[/QUOTE][/SIZE] That's not true on the Posting URL="[URL="https://malwaretips.com/threads/self-made-ransomware-vs-antivirus-products.66903/ said:Self-made ransomware VS antivirus products[/URL]"
is the Link hxxp://bbs.kafan.cn/thread-2069598-1-1.html.
On the Side is Link to my MyRansomware.7z ! And the Virustotal Result.
Since the At virus total results and the sample at virus total one was sent.
Is an independent audit BB and other technical facilities no longer possible.
It true maybe Possible as the user of the thread It had published.
But not more than he the sample has sent to virus total!
SKG2016 post1 said:I had not made this ransomware and this post was from a virus specialist in testing malware and security product
SKG2016 post29 said:This ransomware is programmed by an amateur IT enthusiast who only has intermediate knowledge to coding
here the sample
http://att.kafan.cn/forum.php?mod=attachment&aid=Mjg1MDA5N3w5ZDk5ZGQ3NXwxNDgyNjY0MzgzfDB8MjA2OTU5OA==
here the Passwort: MyRansomware
here Emsisoft Reaction
Address Ordinal Name Library
------- ------- ---- -------
00499000 CryptReleaseContext ADVAPI32
00499004 CryptAcquireContextA ADVAPI32
00499008 CryptGenRandom ADVAPI32
00499010 FindClose KERNEL32
00499014 FindNextFileW KERNEL32
00499018 SetLastError KERNEL32
0049901C GetLastError KERNEL32
00499020 QueryPerformanceFrequency KERNEL32
00499024 GetCurrentThread KERNEL32
00499028 GetThreadTimes KERNEL32
0049902C GetModuleFileNameW KERNEL32
00499030 Sleep KERNEL32
00499034 QueryPerformanceCounter KERNEL32
00499038 FindFirstFileW KERNEL32
0049903C SetEnvironmentVariableA KERNEL32
00499040 WideCharToMultiByte KERNEL32
00499044 GetCurrentThreadId KERNEL32
00499048 MultiByteToWideChar KERNEL32
0049904C GetStringTypeW KERNEL32
00499050 EncodePointer KERNEL32
00499054 DecodePointer KERNEL32
00499058 EnterCriticalSection KERNEL32
0049905C LeaveCriticalSection KERNEL32
00499060 DeleteCriticalSection KERNEL32
00499064 GetSystemTimeAsFileTime KERNEL32
00499068 HeapFree KERNEL32
0049906C HeapAlloc KERNEL32
00499070 FindFirstFileExW KERNEL32
00499074 GetDriveTypeW KERNEL32
00499078 SystemTimeToTzSpecificLocalTime KERNEL32
0049907C FileTimeToSystemTime KERNEL32
00499080 DeleteFileW KERNEL32
00499084 GetCPInfo KERNEL32
00499088 IsDebuggerPresent KERNEL32
0049908C IsProcessorFeaturePresent KERNEL32
00499090 ExitProcess KERNEL32
00499094 GetModuleHandleExW KERNEL32
00499098 GetProcAddress KERNEL32
0049909C AreFileApisANSI KERNEL32
004990A0 GetCommandLineW KERNEL32
004990A4 RaiseException KERNEL32
004990A8 RtlUnwind KERNEL32
004990AC CreateTimerQueue KERNEL32
004990B0 CloseHandle KERNEL32
004990B4 SetEvent KERNEL32
004990B8 WaitForSingleObjectEx KERNEL32
004990BC SignalObjectAndWait KERNEL32
004990C0 GetCurrentProcess KERNEL32
004990C4 SwitchToThread KERNEL32
004990C8 CreateThread KERNEL32
004990CC SetThreadPriority KERNEL32
004990D0 GetThreadPriority KERNEL32
004990D4 TlsAlloc KERNEL32
004990D8 TlsGetValue KERNEL32
004990DC TlsSetValue KERNEL32
004990E0 TlsFree KERNEL32
004990E4 GetLogicalProcessorInformation KERNEL32
004990E8 CreateTimerQueueTimer KERNEL32
004990EC ChangeTimerQueueTimer KERNEL32
004990F0 DeleteTimerQueueTimer KERNEL32
004990F4 GetModuleHandleW KERNEL32
004990F8 GetNumaHighestNodeNumber KERNEL32
004990FC GetProcessAffinityMask KERNEL32
00499100 SetThreadAffinityMask KERNEL32
00499104 RegisterWaitForSingleObject KERNEL32
00499108 UnregisterWait KERNEL32
0049910C UnhandledExceptionFilter KERNEL32
00499110 SetUnhandledExceptionFilter KERNEL32
00499114 InitializeCriticalSectionAndSpinCount KERNEL32
00499118 CreateEventW KERNEL32
0049911C TerminateProcess KERNEL32
00499120 GetStartupInfoW KERNEL32
00499124 GetTickCount KERNEL32
00499128 CreateSemaphoreW KERNEL32
0049912C GetDateFormatW KERNEL32
00499130 GetTimeFormatW KERNEL32
00499134 CompareStringW KERNEL32
00499138 LCMapStringW KERNEL32
0049913C GetLocaleInfoW KERNEL32
00499140 IsValidLocale KERNEL32
00499144 GetUserDefaultLCID KERNEL32
00499148 EnumSystemLocalesW KERNEL32
0049914C GetStdHandle KERNEL32
00499150 GetFileType KERNEL32
00499154 GetProcessHeap KERNEL32
00499158 WriteFile KERNEL32
0049915C ReadFile KERNEL32
00499160 SetFilePointerEx KERNEL32
00499164 FlushFileBuffers KERNEL32
00499168 GetConsoleCP KERNEL32
0049916C GetConsoleMode KERNEL32
00499170 FileTimeToLocalFileTime KERNEL32
00499174 GetFileInformationByHandle KERNEL32
00499178 PeekNamedPipe KERNEL32
0049917C GetFullPathNameW KERNEL32
00499180 GetCurrentDirectoryW KERNEL32
00499184 CreateFileW KERNEL32
00499188 HeapSize KERNEL32
0049918C FreeLibrary KERNEL32
00499190 LoadLibraryExW KERNEL32
00499194 IsValidCodePage KERNEL32
00499198 GetACP KERNEL32
0049919C GetOEMCP KERNEL32
004991A0 GetCurrentProcessId KERNEL32
004991A4 GetEnvironmentStringsW KERNEL32
004991A8 FreeEnvironmentStringsW KERNEL32
004991AC HeapReAlloc KERNEL32
004991B0 OutputDebugStringW KERNEL32
004991B4 FreeLibraryAndExitThread KERNEL32
004991B8 GetModuleHandleA KERNEL32
004991BC GetVersionExW KERNEL32
004991C0 VirtualAlloc KERNEL32
004991C4 VirtualFree KERNEL32
004991C8 VirtualProtect KERNEL32
004991CC DuplicateHandle KERNEL32
004991D0 ReleaseSemaphore KERNEL32
004991D4 InitializeSListHead KERNEL32
004991D8 InterlockedPopEntrySList KERNEL32
004991DC InterlockedPushEntrySList KERNEL32
004991E0 InterlockedFlushSList KERNEL32
004991E4 QueryDepthSList KERNEL32
004991E8 UnregisterWaitEx KERNEL32
004991EC GetTimeZoneInformation KERNEL32
004991F0 ReadConsoleW KERNEL32
004991F4 SetStdHandle KERNEL32
004991F8 WriteConsoleW KERNEL32
004991FC SetEndOfFile KERNEL32
00499200 LoadLibraryW KERNEL32
00499208 SHGetFolderPathW SHELL32@SKG2016, Apogize, English is not my first language, so could you please help me understand your posts?
1. Are you talking about two different persons or is his/her status changed from specialist to amateur or is the person you are referring to a specialist in virus testing and an amateur in malware coding?
2. Next thing I don not understand is when I surf to the link you provided, I see a table with names of Antivirus products and English text. Later on I again see names of Antivirus with failed and success. Are those reported fails and successes the test against one anti-ransomware sample travelling back in time or are those reported failed/success from different samples?
Thanks
Any pros in this forum would do a detailed analysis of this sample and feedback to some major AV companies to help them improve their BB module?Here are some quick details from my analysis of the sample (reversing):
When the sample is executed it will use the string "RSA_Priv_key.enc" (for whatever purpose). Afterwards, it will call the function SHGetFolderPathW (exported by Shell32.dll - Win32 API); it calls this function for a second time later on. Later on, it will do some string comparisons for "C:\\Users\\asus\\Documents\\visual studio 2013\\Projects\\MyRansomware\\TestFile\\" (therefore I assume the developer of this sample had his user account name as "asus"), and then it will start a Do loop.
Once the encryption pay load has been successfully executed (it will utilize "RSA_Priv_key.enc" and "EncryptedKey.encskip") it will use the following string: " Your files have been encrypted. For decryption, please pay 0.1 bitcoint to the account 13P2J5ButQVJHxmQdrwqRepDai4"
"gQ2G9HY.Then you should send the payment proof along with the file 'EncryptedKey.encskip' on your desktop to mail"
": myransomware@yandex.com.The decryption tool and instructions will be sent to you after the payment.".
The mentioned string above will be placed into a text file called "Recover Your Files! Readme.txt", on the disk.
The sample uses the CryptoAPI for encryption.
The PE exports are listed below:
Code:Address Ordinal Name Library ------- ------- ---- ------- 00499000 CryptReleaseContext ADVAPI32 00499004 CryptAcquireContextA ADVAPI32 00499008 CryptGenRandom ADVAPI32 00499010 FindClose KERNEL32 00499014 FindNextFileW KERNEL32 00499018 SetLastError KERNEL32 0049901C GetLastError KERNEL32 00499020 QueryPerformanceFrequency KERNEL32 00499024 GetCurrentThread KERNEL32 00499028 GetThreadTimes KERNEL32 0049902C GetModuleFileNameW KERNEL32 00499030 Sleep KERNEL32 00499034 QueryPerformanceCounter KERNEL32 00499038 FindFirstFileW KERNEL32 0049903C SetEnvironmentVariableA KERNEL32 00499040 WideCharToMultiByte KERNEL32 00499044 GetCurrentThreadId KERNEL32 00499048 MultiByteToWideChar KERNEL32 0049904C GetStringTypeW KERNEL32 00499050 EncodePointer KERNEL32 00499054 DecodePointer KERNEL32 00499058 EnterCriticalSection KERNEL32 0049905C LeaveCriticalSection KERNEL32 00499060 DeleteCriticalSection KERNEL32 00499064 GetSystemTimeAsFileTime KERNEL32 00499068 HeapFree KERNEL32 0049906C HeapAlloc KERNEL32 00499070 FindFirstFileExW KERNEL32 00499074 GetDriveTypeW KERNEL32 00499078 SystemTimeToTzSpecificLocalTime KERNEL32 0049907C FileTimeToSystemTime KERNEL32 00499080 DeleteFileW KERNEL32 00499084 GetCPInfo KERNEL32 00499088 IsDebuggerPresent KERNEL32 0049908C IsProcessorFeaturePresent KERNEL32 00499090 ExitProcess KERNEL32 00499094 GetModuleHandleExW KERNEL32 00499098 GetProcAddress KERNEL32 0049909C AreFileApisANSI KERNEL32 004990A0 GetCommandLineW KERNEL32 004990A4 RaiseException KERNEL32 004990A8 RtlUnwind KERNEL32 004990AC CreateTimerQueue KERNEL32 004990B0 CloseHandle KERNEL32 004990B4 SetEvent KERNEL32 004990B8 WaitForSingleObjectEx KERNEL32 004990BC SignalObjectAndWait KERNEL32 004990C0 GetCurrentProcess KERNEL32 004990C4 SwitchToThread KERNEL32 004990C8 CreateThread KERNEL32 004990CC SetThreadPriority KERNEL32 004990D0 GetThreadPriority KERNEL32 004990D4 TlsAlloc KERNEL32 004990D8 TlsGetValue KERNEL32 004990DC TlsSetValue KERNEL32 004990E0 TlsFree KERNEL32 004990E4 GetLogicalProcessorInformation KERNEL32 004990E8 CreateTimerQueueTimer KERNEL32 004990EC ChangeTimerQueueTimer KERNEL32 004990F0 DeleteTimerQueueTimer KERNEL32 004990F4 GetModuleHandleW KERNEL32 004990F8 GetNumaHighestNodeNumber KERNEL32 004990FC GetProcessAffinityMask KERNEL32 00499100 SetThreadAffinityMask KERNEL32 00499104 RegisterWaitForSingleObject KERNEL32 00499108 UnregisterWait KERNEL32 0049910C UnhandledExceptionFilter KERNEL32 00499110 SetUnhandledExceptionFilter KERNEL32 00499114 InitializeCriticalSectionAndSpinCount KERNEL32 00499118 CreateEventW KERNEL32 0049911C TerminateProcess KERNEL32 00499120 GetStartupInfoW KERNEL32 00499124 GetTickCount KERNEL32 00499128 CreateSemaphoreW KERNEL32 0049912C GetDateFormatW KERNEL32 00499130 GetTimeFormatW KERNEL32 00499134 CompareStringW KERNEL32 00499138 LCMapStringW KERNEL32 0049913C GetLocaleInfoW KERNEL32 00499140 IsValidLocale KERNEL32 00499144 GetUserDefaultLCID KERNEL32 00499148 EnumSystemLocalesW KERNEL32 0049914C GetStdHandle KERNEL32 00499150 GetFileType KERNEL32 00499154 GetProcessHeap KERNEL32 00499158 WriteFile KERNEL32 0049915C ReadFile KERNEL32 00499160 SetFilePointerEx KERNEL32 00499164 FlushFileBuffers KERNEL32 00499168 GetConsoleCP KERNEL32 0049916C GetConsoleMode KERNEL32 00499170 FileTimeToLocalFileTime KERNEL32 00499174 GetFileInformationByHandle KERNEL32 00499178 PeekNamedPipe KERNEL32 0049917C GetFullPathNameW KERNEL32 00499180 GetCurrentDirectoryW KERNEL32 00499184 CreateFileW KERNEL32 00499188 HeapSize KERNEL32 0049918C FreeLibrary KERNEL32 00499190 LoadLibraryExW KERNEL32 00499194 IsValidCodePage KERNEL32 00499198 GetACP KERNEL32 0049919C GetOEMCP KERNEL32 004991A0 GetCurrentProcessId KERNEL32 004991A4 GetEnvironmentStringsW KERNEL32 004991A8 FreeEnvironmentStringsW KERNEL32 004991AC HeapReAlloc KERNEL32 004991B0 OutputDebugStringW KERNEL32 004991B4 FreeLibraryAndExitThread KERNEL32 004991B8 GetModuleHandleA KERNEL32 004991BC GetVersionExW KERNEL32 004991C0 VirtualAlloc KERNEL32 004991C4 VirtualFree KERNEL32 004991C8 VirtualProtect KERNEL32 004991CC DuplicateHandle KERNEL32 004991D0 ReleaseSemaphore KERNEL32 004991D4 InitializeSListHead KERNEL32 004991D8 InterlockedPopEntrySList KERNEL32 004991DC InterlockedPushEntrySList KERNEL32 004991E0 InterlockedFlushSList KERNEL32 004991E4 QueryDepthSList KERNEL32 004991E8 UnregisterWaitEx KERNEL32 004991EC GetTimeZoneInformation KERNEL32 004991F0 ReadConsoleW KERNEL32 004991F4 SetStdHandle KERNEL32 004991F8 WriteConsoleW KERNEL32 004991FC SetEndOfFile KERNEL32 00499200 LoadLibraryW KERNEL32 00499208 SHGetFolderPathW SHELL32
You can use IDA Pro for disassembly.
It is actually not that sophisticated sample in terms of effectiveness, but I am not a "master" at reverse engineering ransomware... These are just some quick details from my non-sober analysis, so hopefully it is still useful. Maybe I will come back to this another day when I am in a more "right mind".
Thanks for reading.
Kaspersky has a similar module to Bitdefender for ransomware protection. Was it enabled in the test?
Kaspersky: Still cannot block at maximum protection setting, but if the "Perform recommended action automatically" is toggled off and HIPS set up correctly in the application control, a pop up window will ask for action, it is kinda a successful block if the user know what he is doing. But according to my experience, switching off the automatic action setting is impractical since Kaspersky will pop up a million request for action windows whenever a program is accessing any sensitive data in the system and any program attempting to establish UDP connection, even the app is in the Trusted group.
So that is why I marked it as a fail.
They can improve their Behavior Blocker with many techniques (or create one), not just aimed towards ransomware.Any pros in this forum would do a detailed analysis of this sample and feedback to some major AV companies to help them improve their BB module?