The threat activity cluster known as SloppyLemming has been attributed to a fresh set of attacks targeting government entities and critical infrastructure operators in Pakistan and Bangladesh.
The activity, per Arctic Wolf, took place between January 2025 and January 2026. It involves the use of two distinct attack chains to deliver malware families tracked as BurrowShell and a Rust-based keylogger.
"The use of the Rust programming language represents a notable evolution in SloppyLemming’s tooling, as prior reporting documented the actor using only traditional compiled languages and borrowed adversary simulation frameworks such as Cobalt Strike, Havoc, and the custom NekroWire RAT," the cybersecurity company said in a report shared with The Hacker News.
Security News SloppyLemming Targets Pakistan and Bangladesh Governments Using Dual Malware Chains
- Thread starter Captain Awesome
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Finally!! India take cyber w@r seriously. 

Blocking internet connnectivity of the PDF readerThe PDF decoys contain URLs designed to lead victims to ClickOnce application manifests.
Enabling SAC/WDACDeploy a legitimate Microsoft .NET runtime executable ("NGenTask.exe") and a malicious loader ("mscorsvc.dll"). The loader is launched using DLL side-loading to decrypt and execute a custom x64 shellcode implant codenamed BurrowShell.
F
ForgottenSeer 123960
Executive Summary
Confirmed Facts
Telemetry from Arctic Wolf indicates an India-nexus threat actor, SloppyLemming, conducted a cyber espionage campaign targeting Pakistan and Bangladesh entities between January 2025 and January 2026.
Assessment
The actor demonstrates advanced evasion capabilities by utilizing legitimate Windows binaries for DLL sideloading and abusing Cloudflare Workers for command-and-control (C2) routing.
Confirmed Facts
Telemetry from Arctic Wolf indicates an India-nexus threat actor, SloppyLemming, conducted a cyber espionage campaign targeting Pakistan and Bangladesh entities between January 2025 and January 2026.
Assessment
The actor demonstrates advanced evasion capabilities by utilizing legitimate Windows binaries for DLL sideloading and abusing Cloudflare Workers for command-and-control (C2) routing.
Technical Analysis & Remediation
MITRE ATT&CK Mapping
T1566.001
(Phishing: Spearphishing Attachment)
T1574.002
(Hijack Execution Flow: DLL Side-Loading)
T1056.001
(Input Capture: Keylogging)
T1090
(Proxy)
CVE Profile
N/A [CISA KEV Status: Inactive].
The attack relies on abusing native Windows features (ClickOnce, .NET runtime, Office macros) rather than exploiting specific unpatched vulnerabilities.
Telemetry
Hashes
Unknown (Not provided in source).
Target Binaries/Strings
NGenTask.exe
mscorsvc.dll.
Constraint
The structure resembles a highly modular remote access framework. BurrowShell masquerades C2 traffic as Windows Update service communications and encrypts payloads using a 32-character RC4 key.
Execution Flow
The primary attack chain begins with PDF lures that direct targets to ClickOnce application manifests. These manifests deploy a DLL sideloading package . The package uses the legitimate Microsoft .NET runtime executable (NGenTask.exe) to load a malicious module (mscorsvc.dll), which ultimately decrypts and runs the BurrowShell x64 implant. The secondary chain uses macro-enabled Excel files to drop a Rust-based keylogger.
Remediation - THE ENTERPRISE TRACK (NIST SP 800-61r3 / CSF 2.0)
GOVERN (GV) – Crisis Management & Oversight
Command
Initiate supply chain and geopolitical risk assessments if your organization operates within or adjacent to South Asian government, telecommunications, or energy sectors.
DETECT (DE) – Monitoring & Analysis
Command
Deploy SIEM hunting queries looking for anomalous child processes originating from NGenTask.exe or phoneactivate.exe.
Command
Alert on the loading of unsigned or unexpectedly located instances of mscorsvc.dll.
RESPOND (RS) – Mitigation & Containment
Command
Isolate impacted endpoints from the corporate network immediately.
Command
Block network traffic matching known SloppyLemming Cloudflare Workers infrastructure.
RECOVER (RC) – Restoration & Trust
Command
Reimage compromised systems entirely, as BurrowShell establishes deep file system and SOCKS proxy tunneling access.
Command
Validate clean state through comprehensive memory and file scanning before re-introducing assets to the domain.
IDENTIFY & PROTECT (ID/PR) – The Feedback Loop
Command
Disable ClickOnce deployment mechanisms via Group Policy if not explicitly required by business operations.
Command
Enforce strict macro execution policies for Microsoft Office to neutralize the secondary Rust-based attack chain.
Remediation - THE HOME USER TRACK (Safety Focus)
Priority 1: Safety
Command
Disconnect from the internet immediately if you opened a suspicious PDF or enabled macros in an untrusted Excel document.
Command
Do not log into banking/email until verified clean.
Priority 2: Identity
Command
Reset passwords/MFA using a known clean device (e.g., phone on 5G), as the secondary payload includes a dedicated Rust-based keylogger.
Priority 3: Persistence
Command
Check Scheduled Tasks, Startup Folders, and Browser Extensions for unrecognized entries. Run a full scan with a reputable endpoint security product.
Hardening & References
Baseline
CIS Benchmarks for Microsoft Windows Workstation / Microsoft Office (Disable VBA Macros).
Framework
NIST SP 800-61r3 (Incident Response) / NIST CSF 2.0.
Mathematical Security Posture
To reduce the probability of a successful sideloading execution, organizations must decrease the attack surface by stripping unnecessary binaries. Evasion probability decreases as strict application control increases.
Source
Arctic Wolf Labs
The Hacker News
The second chain of attacks using Excel documents is interesting:
It would appear that the malicious macros contained in the document can lower the set macro security level without user intervention.
In this case too, user intervention is required.
.......and macro-enabled Excel documents to kick-start the infection chains.
It would appear that the malicious macros contained in the document can lower the set macro security level without user intervention.
In this case too, user intervention is required.
The "run as admin" privilege.The second chain of attacks using Excel documents is interesting:
It would appear that the malicious macros contained in the document can lower the set macro security level without user intervention.
In this case too, user intervention is required.
The "run as admin" privilege.
Simply opening the Excel document does not, in my experience, reduce the macro level you have set.
Obviously, this is assuming you are using an up-to-date version of X-Office without any critical bugs.
Action is required by the user who has been misled.
Macros are blocked in this way only for documents with MotW:

For documents with no MotW, Macros are blocked, but can be easily enabled:

For documents with no MotW, Macros are blocked, but can be easily enabled:
Could be avoided by changing the default settings?but can be easily enabled
Yes.
Macros are blocked in this way only for documents with MotW:
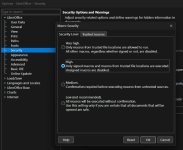
View attachment 296107
For documents with no MotW, Macros are blocked, but can be easily enabled:
View attachment 296108
Does this only apply to Microsoft Office?
With LibreOffice + my “Very High”*** level, there shouldn't be any such problem.
*** = Only macros from trusted locations are enabled for execution.
Other macros, whether signed or unsigned, are disabled.
Last edited:
Exactly, in LibreOffice the handling of macros is different, and with the security level set to 'Very High' they do not run automatically. 
Exactly, in LibreOffice the handling of macros is different, and with the security level set to 'Very High' they do not run automatically.
In fact, they should not be executed at all if included in XML files.
But it has no setting to block all macros regardless of location trustworthiness, as in MS Office.Thanks, as I hadn't verified that setting on my end, which the default is set on High.
View attachment 296114
I didn't realize that either, as I haven't used MS office for a couple of years.But it has no setting to block all macros regardless of location trustworthiness, as in MS Office.
Tried all MS Office alternatives, in attempt to abandon for good.I didn't realize that either, as I haven't used MS office in a couple of years.
Unfortunately, the best one (WPS Office) has some malicious behavior; did not like it, inspite being almost as light as MS Office.
Tried all MS Office alternatives, in attempt to abandon for good.
Unfortunately, the best one (WPS Office) has some malicious behavior; did not like it, inspite being almost as light as MS Office.
In LibreOffice, macro execution is blocked by default for untrusted documents.
So it would be better from a security standpoint for users classified as average.
By "untrusted" LO means with MoTW or something else?In LibreOffice, macro execution is blocked by default for untrusted documents.
MS Office has the option to block for all documents, regardless of being trusted.
You may also like...
-
Experts Detect Pakistan-Linked Cyber Campaigns Aimed at Indian Government Entities
- Started by Captain Awesome
- Replies: 3
-
APT36 Targets Indian Government with Golang-Based DeskRAT Malware Campaign
- Started by Captain Awesome
- Replies: 2
-
Transparent Tribe Launches New RAT Attacks Against Indian Government and Academia
- Started by Captain Awesome
- Replies: 2
-
Serious Discussion The Necessity of Simulating the Full Malware Infection Chain for Security Suite Testing
- Started by harlan4096
- Replies: 3