Slerion- If you will allow me to make some comments-
1). The most important thing to do when malware testing is to make absolutely positive that all samples to be used in the test are actually malicious. This is a very time consuming process and would be a burden for 20 samples, no less 800+. The issue is that so many malware repositories will include stuff like legitimate applications that use certain packers, things like keygens (with snappy tunes), hacktools, and many files that are essentially duplicates of the exact same thing. So although at first blush an extensive data set seems impressive, it may not be as pertinent as a 15 file set of verified malware working by differing mechanisms.
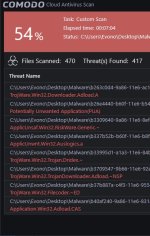
2). If the Comodo AV was as impressive as your results show, I would be posting this over and over (in BOLD CAPS, CAPITALIZED) until Jack banned me from MT until this Universe winked out. As an example, I just tried a pack of 13 (Bakers Dozen) malware against both Comodo Internet Security and Qihoo Total Security. Twelve of the samples were from the past 12 hours, one was from 2016. The results:
a. CIS- using an on-demand scan, the Comodo AV detected 1/13 (the old sample, needless to say). On running the remaining samples another was detected by the Cloud AV; all the other were contained and dismissed by the Sandbox.
b. Qihoo Total Security (with BD Engine enabled)- 11/13 were detected and deleted by on on-demand scan. On running the undetected 2 files, one was blocked mechanistically, and the other, a new Cerber, trashed the machine.
So- although I (and I'm sure everyone else) appreciates the time you put in to this project, my suggestion would be using a small number of verified quality malware over sheer numbers of unknowns (quality over quantity); and if the results seem to be incorrect, they probably are.