Hi Everyone,
Hackers often manipulate or exploit Windows system programs and services, like SVCHOST , TASKHOSTW, File EXPLORER and RUNTIMEBROKER. They can do it because Windows Firewall defaults to allow all Outbound traffic, and some of these do send out and receive returning traffic. In short, these 4 programs accept traffic, and a hacker can manipulate the ip address header to slip thru.
In my Xcitium EDR Alerts, I can see SVCHOST and File Explorer invoking Powershell, and TASKHOSTW trying to manipulate Registry. These invocations are malicious.
My first solution was to use Xcitium's HIDS to Block Powershell from starting until I need to use it, then I would disable that block rule and re-enable when finished. However, that does not stop the malicious registry modifications. In short, the ways that these 4 programs can be used by hackers are infinite; invoking Powershell and changing registry are only 2 variants.
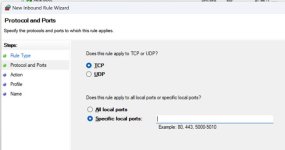
Now I have come up with a better solution. That is to make Firewall Incoming Block Rules to Block traffic to these 4 programs. Windows can do without these 4 programs talking to the Internet.
So, open File Manager and Search for all instances of SVCHOST, TASKHOSTW, EXPLORER and RUNTIMEBROKER. There are Many instances of these 4 programs scattered throughout Windows sub-folders. Right click on each item found by search and choose 'Copy as Path'. And paste it in the Inbound section Firewall Rule creation wizard, and make a Block rule. It is a laborious exercise and takes time to make all the rules. But you will stop the majority of hacking attempts.
Hackers often manipulate or exploit Windows system programs and services, like SVCHOST , TASKHOSTW, File EXPLORER and RUNTIMEBROKER. They can do it because Windows Firewall defaults to allow all Outbound traffic, and some of these do send out and receive returning traffic. In short, these 4 programs accept traffic, and a hacker can manipulate the ip address header to slip thru.
In my Xcitium EDR Alerts, I can see SVCHOST and File Explorer invoking Powershell, and TASKHOSTW trying to manipulate Registry. These invocations are malicious.
My first solution was to use Xcitium's HIDS to Block Powershell from starting until I need to use it, then I would disable that block rule and re-enable when finished. However, that does not stop the malicious registry modifications. In short, the ways that these 4 programs can be used by hackers are infinite; invoking Powershell and changing registry are only 2 variants.
Now I have come up with a better solution. That is to make Firewall Incoming Block Rules to Block traffic to these 4 programs. Windows can do without these 4 programs talking to the Internet.
So, open File Manager and Search for all instances of SVCHOST, TASKHOSTW, EXPLORER and RUNTIMEBROKER. There are Many instances of these 4 programs scattered throughout Windows sub-folders. Right click on each item found by search and choose 'Copy as Path'. And paste it in the Inbound section Firewall Rule creation wizard, and make a Block rule. It is a laborious exercise and takes time to make all the rules. But you will stop the majority of hacking attempts.
Last edited: