Canon not firing on all cylinders: Fledgling cloud loses people's pics'n'vids, then 'Maze ransomware' hits
"Canon has had a double shot of bad luck lately. First, its brand-new photo-and-video-hosting cloud started losing files. Now it's reportedly fallen victim to ransomware.
The Japanese camera maker noticed at the end of July that footage uploaded before June 16 to
image.canon had started going missing. The service launched in February, and offers 10GB of long-term storage space for people's personal photos and videos. Some cameras can automatically upload material to the cloud, too.
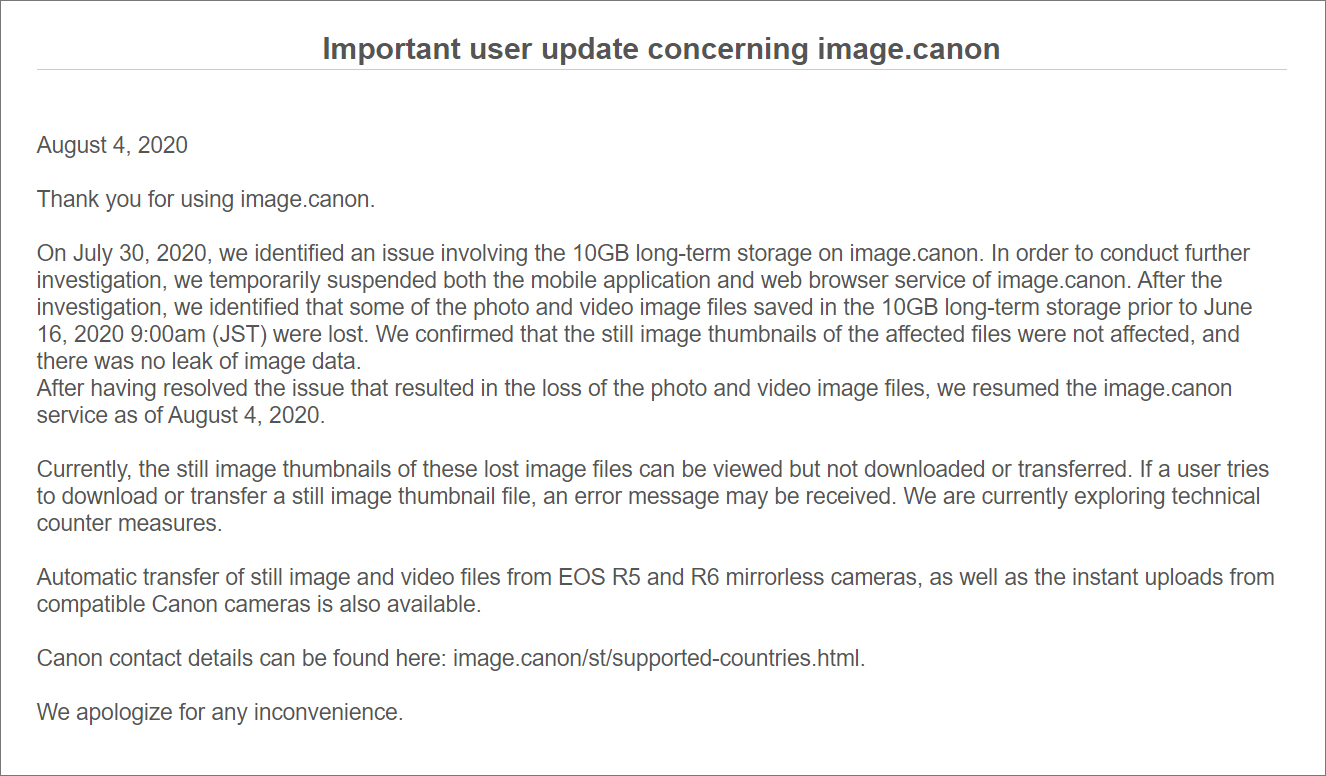
Canon pulled the plug on service, and restored it days later, on Tuesday, August 4 when the data-gobbling glitch was fixed, we're told. Strangely, it said no data was leaked. In a statement, the biz said:
On July 30, 2020, we identified an issue involving the 10GB long-term storage on image.canon. In order to conduct further investigation, we temporarily suspended both the mobile application and web browser service of image.canon. After the investigation, we identified that some of the photo and video image files saved in the 10GB long-term storage prior to June 16, 2020 9:00am (JST) were lost. We confirmed that the still image thumbnails of the affected files were not affected, and there was no leak of image data.
After having resolved the issue that resulted in the loss of the photo and video image files, we resumed the image.canon service as of August 4, 2020.
Currently, the still image thumbnails of these lost image files can be viewed but not downloaded or transferred. If a user tries to download or transfer a still image thumbnail file, an error message may be received. We are currently exploring technical counter measures.
Then on Wednesday, according to Bleeping Computer, Canon was
hit by a Maze ransomware infection.
This appears to have disrupted the manufacturer's internal network. A message apparently sent by its IT support desk at 6am to staff said there were "widespread system issues affecting multiple applications," and that Microsoft Teams, "email, and other systems may not be available at this time." Said systems included Canon's US website, which fell offline. A ransom note was apparently found claiming internal files had been scrambled, and would be restored if payment was made.
The Maze team reportedly boasted it broke into Canon's systems, exfiltrated 10TB of databases and other files, and was holding the encrypted information to ransom. Canon has not appeared on the Maze gang's website, where the crew usually lists its victims,
such as Xerox, though.
You might link the two snafus – the file-wiping cloud and the reported ransomware infection – though there is no smoking gun connecting the two, we note. The Maze gang apparently said they didn't have anything to do with the image.canon downtime.
"We are currently investigating the situation. Thank you," a spokesperson for Canon told
The Register regarding the ransomware infection report."
'We are investigating the situation'

www.theregister.com
Canon hit by Maze Ransomware attack, 10TB data allegedly stolen
Canon has suffered a ransomware attack that impacts numerous services, including Canon's email, Microsoft Teams, USA website, and other internal applications.
BleepingComputer has been tracking a suspicious outage on Canon's image.canon cloud photo and video storage service resulting in the loss of data for users of their free 10GB storage feature.
The
image.canon site suffered an outage on July 30th, 2020, and over six days, the site would show status updates until it went back in service yesterday, August 4th.
However, the final status update was strange as it mentions that while data was lost, "there was no leak of image data." This led BleepingComputer to believe there was more to the story and that they suffered a cyberattack.
When we contacted Canon about this outage, they referred us to the notice on the image.canon site.
If you work at Canon or know someone working there with first-hand information on this incident, you can confidentially contact us on Signal at +16469613731.
Canon suffers ransomware attack
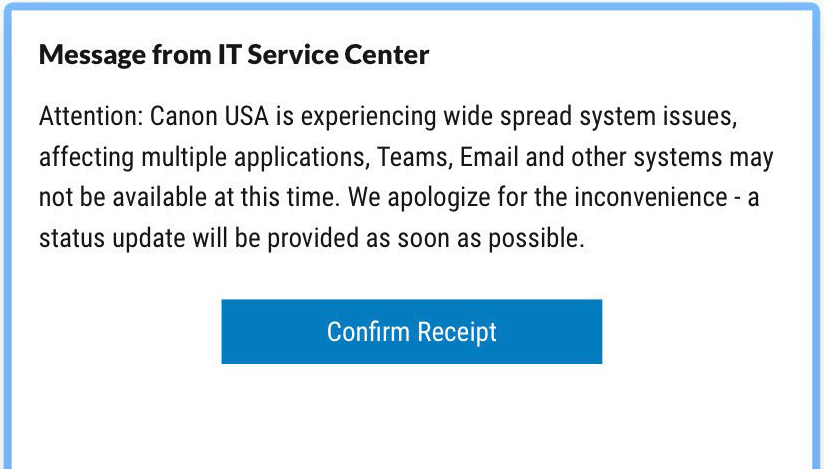
Today, a source contacted BleepingComputer and shared an image of a company-wide notification titled "Message from IT Service Center" that was sent at approximately 6 AM this morning from Canon's IT department.
This notification states that Canon is experiencing "wide spread system issues affecting multiple applications, Teams, Email, and other systems may not be available at this time."
Notice from Canon's IT department
Source: BleepingComputer
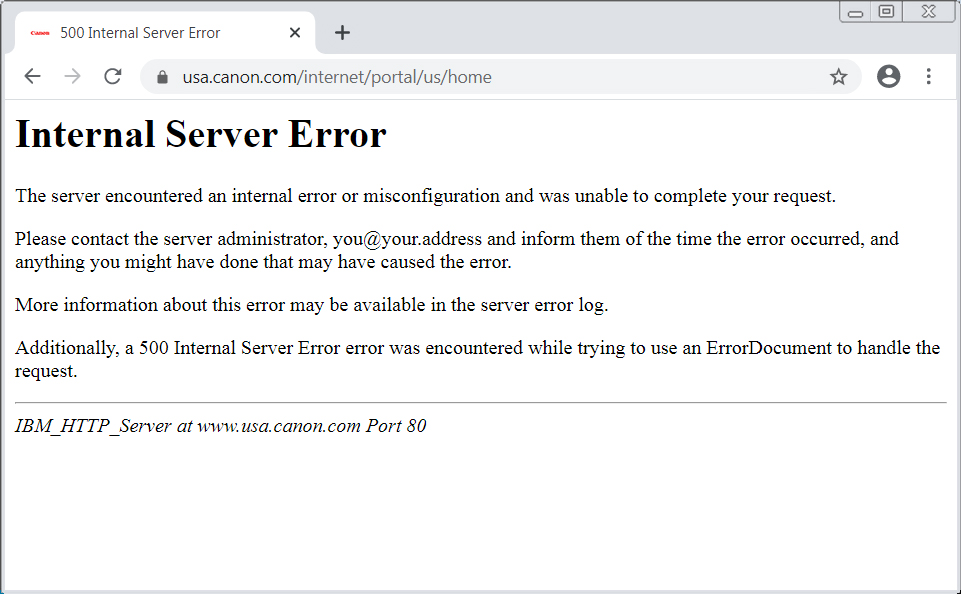
As part of this outage, Canon USA's website is now displaying errors or page not found errors when visited.
Canon USA website is down
Source: BleepingComputer
The list of Canon domains that appear to be affected by this outage, include:
Code:
www.canonusa.com
www.canonbroadcast.com
b2cweb.usa.canon.com
canondv.com
canobeam.com
canoneos.com
bjc8200.com
canonhdec.com
bjc8500.com
usa.canon.com
imagerunner.com
multispot.com
canoncamerashop.com
canoncctv.com
canonhelp.com
bjc-8500.com
canonbroadcast.com
imageland.net
consumer.usa.canon.com
bjc-8200.com
bjc3000.com
downloadlibrary.usa.canon.com
www.cusa.canon.com
www.canondv.com
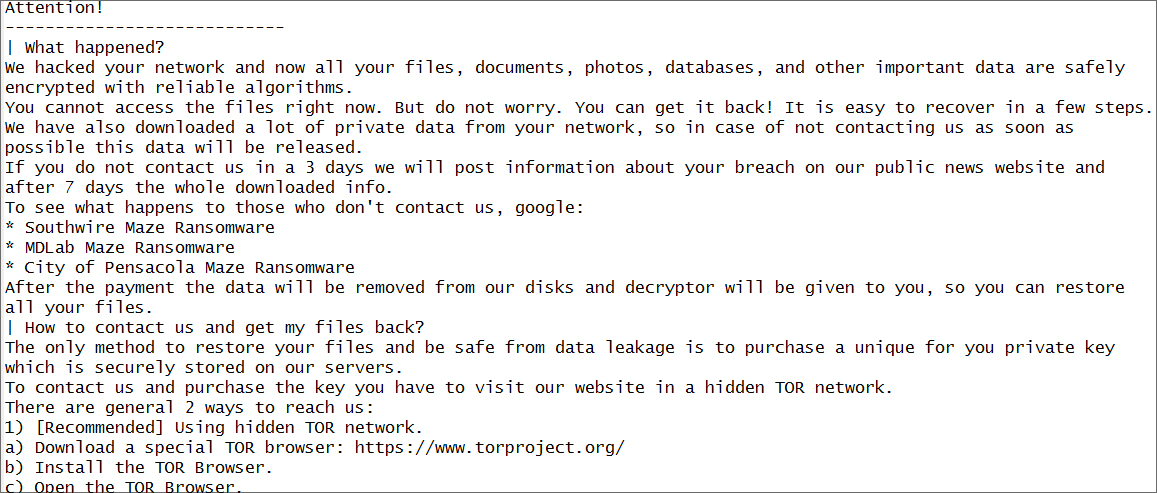
Since then, BleepingComputer has obtained a partial screenshot of the alleged Canon ransom note, which we have been able to identify as from the Maze ransomware.
Partial Maze ransomware note
Source: BleepingComputer
Maze claims to have stolen 10TB of data from Canon
After contacting the ransomware operators, BleepingComputer was told by Maze that their attack was conducted this morning when they stole "10 terabytes of data, private databases etc" as part of the attack on Canon.
Maze declined to share any further info about the attack including the ransom amount, proof of stolen data, and the amount of devices encrypted.
While we first thought that the image.canon outage was related to the ransomware attack, Maze has told us that it was not caused by them.
Maze is an enterprise-targeting
human-operated ransomware that compromises and stealthily spreads laterally through a network until it gains access to an administrator account and the system's Windows domain controller.
During this process, Maze will steal unencrypted files from servers and backups and upload them to the threat actor's servers.
Once they have harvested the network of anything of value and gain access to a Windows domain controller, Maze will deploy the ransomware throughout the network to encrypt all of the devices.
If a victim does not pay the ransom, Maze will
publicly distribute the victim's stolen files on a
data leak site that they have created.
Maze has claimed responsibility for other high-profile victims in the past, including
LG,
Xerox,
Conduent,
MaxLinear,
Cognizant,
Chubb,
VT San Antonio Aerospace, the
City of Pensacola, Florida, and more.
In a statement to BleepingComputer, Canon says they are "currently investigating the situation."
Canon has suffered a ransomware attack that impacts numerous services, including Canon's email, Microsoft Teams, USA website, cloud photo and video storage service, and other internal applications.

www.bleepingcomputer.com