- Nov 10, 2017
- 3,135
- 1
- 22,994
- 4,269
Trace blocks multiple tracking techniques in Firefox and Chrome
race is a privacy add-on for Mozilla Firefox and Google Chrome web browsers designed to block several tracking techniques used to track Internet user activity.
The extension is available for Chrome and Firefox officially but it may run on Chromium or Firefox based web browsers such as Vivaldi or Opera.
User tracking is a big privacy issue on today's Internet. Marketing companies, web publishers, software publishers, and advertising companies use numerous techniques to track users that go beyond dropping cookies on user systems.
Some techniques use, or abuse, new web technologies that browsers support while others track users using functionality that browsers supported for many years.
Trace
Trace is an anti-tracking extension for Firefox and Chrome that protects against the following tracking techniques:race is a privacy add-on for Mozilla Firefox and Google Chrome web browsers designed to block several tracking techniques used to track Internet user activity.
The extension is available for Chrome and Firefox officially but it may run on Chromium or Firefox based web browsers such as Vivaldi or Opera.
User tracking is a big privacy issue on today's Internet. Marketing companies, web publishers, software publishers, and advertising companies use numerous techniques to track users that go beyond dropping cookies on user systems.
Some techniques use, or abuse, new web technologies that browsers support while others track users using functionality that browsers supported for many years.
Trace
- Canvas Fingerprinting
- Audio Fingerprinting
- WebRTC Leaks
- User-Agent Tracking
- Browser plugin fingerprinting
- Beacon Requests
- Bad Top Level Domains
- Hyperlink Auditing
- HTTP Referrer Headers
- Chrome Header Tracking
- E-Tag Tracking
- JavaScript Crypto Mining
- URL Tracking Cleaner (experimental)
- Trace Page (injects code into sites to disable certain functions)
A soon-to-be-released version will protect against specific tracking cookies and URL parameters on top of that.
Trace works right after installation. The browser extension adds an icon to the browser's main toolbar that you can click on to open the Settings or display statistics about the extension's blocking activity.
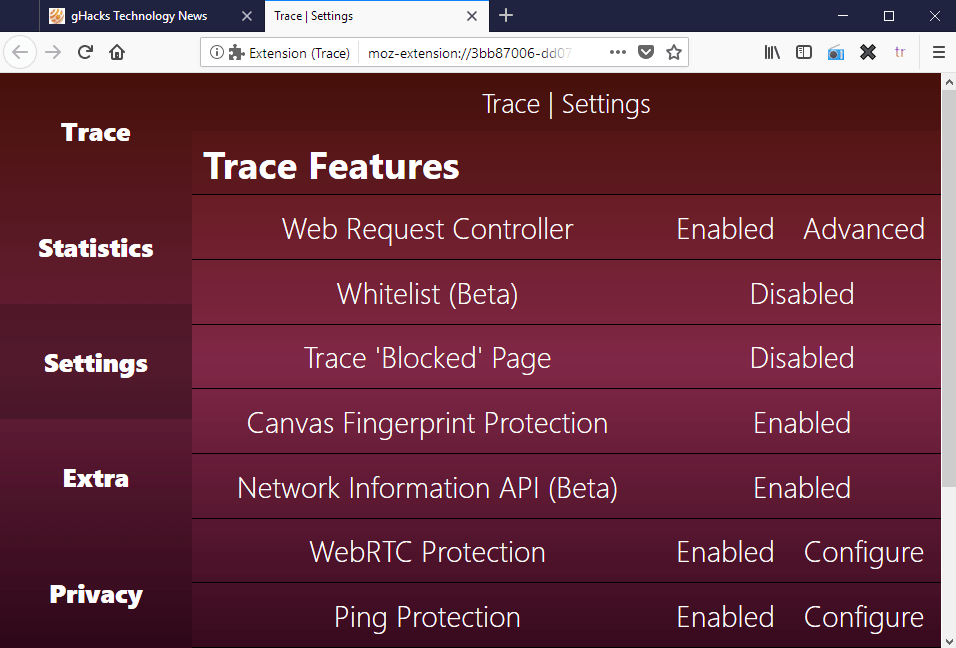
The Settings are divided into Trace Features, Advanced Features, Browser Settings, and Options. The first three list the available anti-tracking features and options to enable or disable each individually.
Some come with configuration options. If you click on WebRTC Protection for instance, you will notice that Trace blocks the leaking of the local IP address but does not disable RTCPeerConnection, RTCDataCahnel, and RTCRtpReceiver JavaScript objects by default. You can enable those but it may break sites and services that use WebRTC functionality.
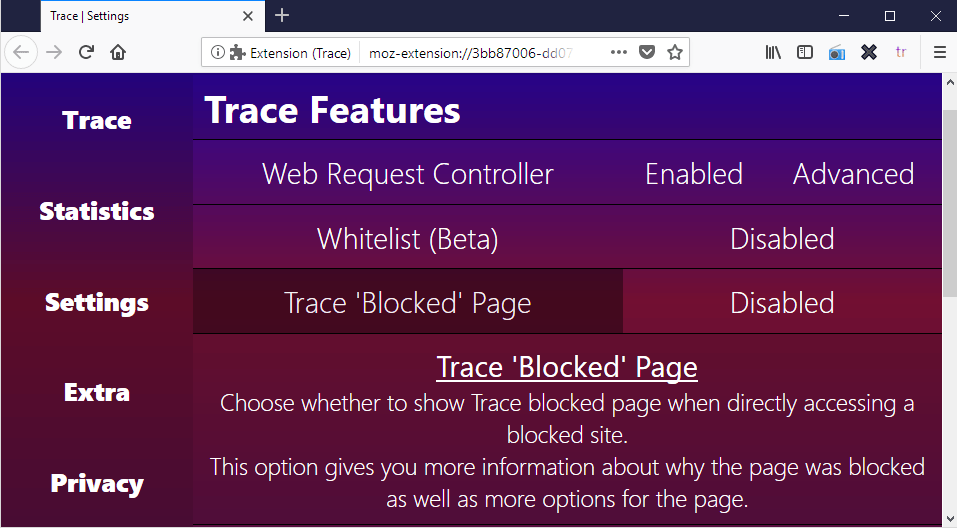
A click on a protective feature displays a short summary of what it does; useful as you may not know right away what enabling Web Request Controller does
Many features that Trace supports, especially those listed under advanced, require that users know what disabling certain techniques has for consequences. While you could use trial and error to find out if enabling a feature breaks certain web functionality, you may prefer to know what disabling a feature does before you configure it.
The following options are provided for instance if you enable Audio Fingerprint Protection:Trace works right after installation. The browser extension adds an icon to the browser's main toolbar that you can click on to open the Settings or display statistics about the extension's blocking activity.
The Settings are divided into Trace Features, Advanced Features, Browser Settings, and Options. The first three list the available anti-tracking features and options to enable or disable each individually.
Some come with configuration options. If you click on WebRTC Protection for instance, you will notice that Trace blocks the leaking of the local IP address but does not disable RTCPeerConnection, RTCDataCahnel, and RTCRtpReceiver JavaScript objects by default. You can enable those but it may break sites and services that use WebRTC functionality.
A click on a protective feature displays a short summary of what it does; useful as you may not know right away what enabling Web Request Controller does
Many features that Trace supports, especially those listed under advanced, require that users know what disabling certain techniques has for consequences. While you could use trial and error to find out if enabling a feature breaks certain web functionality, you may prefer to know what disabling a feature does before you configure it.
- Disable Audio Channel Functions
- Disable Audio Data Functions
- Disable Offline AudioContext Object
- Disable Main AudioContext Object
You can check the developer website for information on all supported protective features. The website links to several fingerprinting and privacy tests as well to test the browser with and without Trace enabled.
Trace comes with whitelisting functionality so that sites may use blocked functionality; you may want to whitelist a site if it is broken after installing Trace and if you need to access it.
Trace is provided as a free extension with a basic blocklist. You can support development by donating three British Pounds; this gives you a premium code that you may enter to gain access to the premium blocklist as well.
Closing Words
Trace is a powerful privacy enhancing browser extension for Chrome and Firefox. Its interface is big and bright, and that is probably something that some users don't like at all. It would be great if the developer could integrate a compact interface next to the default one.
The functionality that Trace provides is what counts, on the other hand. Trace offers numerous anti-tracking and fingerprinting features. The developer is very active and new features are added to the extension regularly.
Source: Trace blocks multiple tracking techniques in Firefox and Chrome - gHacks Tech News
Trace comes with whitelisting functionality so that sites may use blocked functionality; you may want to whitelist a site if it is broken after installing Trace and if you need to access it.
Trace is provided as a free extension with a basic blocklist. You can support development by donating three British Pounds; this gives you a premium code that you may enter to gain access to the premium blocklist as well.
Closing Words
Trace is a powerful privacy enhancing browser extension for Chrome and Firefox. Its interface is big and bright, and that is probably something that some users don't like at all. It would be great if the developer could integrate a compact interface next to the default one.
The functionality that Trace provides is what counts, on the other hand. Trace offers numerous anti-tracking and fingerprinting features. The developer is very active and new features are added to the extension regularly.
Source: Trace blocks multiple tracking techniques in Firefox and Chrome - gHacks Tech News

