The key to virtual private networks - or VPN - is the creation of the encrypted tunnel from the client to the VPN server. Through this tunnel, all the internet data is transmitted back and forth. The privacy of the VPN connection is based on the encryption used, to keep the data going through it secure from both hackers and others - like your ISP - that want to take a peek.
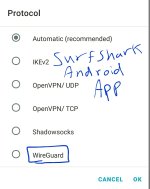
There are plenty of options for the encrypted data VPN protocol, each with its advantages and disadvantages. Some popular ones are PPTP, SSTP, and OpenVPN (which has both TCP and UDP variants). The goals of any of these encryption protocols is to provide a high level of encryption, with a low overhead of computing resources. While OpenVPN remains quite popular with its 256-bit encryption, it does go back to 2001, and much has changed with computing since Windows XP debuted.
WireGuard is a more recent entry into the world of VPN encryption protocols and is just beginning to gain more traction in the cybersecurity sphere. In this article, we're taking a closer look at WireGuard.
A lighter VPN protocol...
WireGuard's developer is Jason A. Donenfeld who has a background in online security, with current development done by Edge Security LLC. While it was initially developed for the mainstream Linux kernel, it is currently cross-platform, with support for the major operating systems of Windows, Mac, iOS and Android.
The main advantage of WireGuard is that it runs much lighter and is designed to offer encryption with less overhead. When compared to the more common OpenVPN and IPsec protocols, WireGuard demonstrates benefits with both faster throughput speeds, and lower ping times.
While WireGuard’s code is said to contain about 4,000 lines, this is far less than the 100,000+ lines of code that comprises either of the competing VPN protocols of OpenVPN or IKEv2/IPsec. This advantage also makes it well suited for embedded devices with less computing power, such as a smartphone, router, or even a RaspberryPi.
WireGuard also endeavors to be simple to deploy with an easy installation. Cryptography is state-of-the-art using modern protocols such as Curve25519, ChaCha20, and Blake2. The much shorter code length also makes it a lot simpler to audit than longer length protocols.
...but still early stages
With these obvious advantages, you may be wondering why everyone is not using WireGuard.
Well, some VPN providers have already embraced WireGuard, with Mullvad off to an early start. In fact, WireGuard is its default protocol for Linux, MacOS, Android and iOS users, and it can be enabled for Windows users, too.
NordVPN is also implementing WireGuard as part of its NordLynx project, which offers the NordVPN to Linux users. Other VPNs that use WireGuard’s protocol include AzireVPN, OVPN, TorGuard, and Private Internet Access.
However, some of the biggest VPNs have taken a more wait-and-see approach to implementation of WireGuard. In general, greater speeds for encryption usually come at the expense of lower security and at the time of writing, there are ongoing concerns that WireGuard is still early in development and so may not be as stable as a more mature project. This is why ExpressVPN and some other VPN providers have not implemented WireGuard to date.
Still, it remains an intriguing new protocol, and is off to a promising start.
Advice Request What is WireGuard?
- Thread starter CyberPanther
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Please provide comments and solutions that are helpful to the author of this topic.
ExpressVPN has its own new protocol. It's call Lightway
 www.expressvpn.com
www.expressvpn.com
Lightway: A VPN Protocol by ExpressVPN | ExpressVPN
Learn how ExpressVPN’s game-changing new protocol elevates your VPN experience.
I installed ExpressVPN beta for Windows, but it didn't have TCP for Lightway, so I uninstalled it. Speeds with Lightway UDP were not also fast comparing to TCP with OpenVPN.
Have you try android? ExpressVPN beta v9.x has LightwayI installed ExpressVPN beta for Windows, but it didn't have TCP for Lightway, so I uninstalled it. Speeds with Lightway UDP were not also fast comparing to TCP with OpenVPN.
Yes, I tried Andriod too. Windows version of ExpressVPN now also has Lightway, but only with UDP.
My Private Internet Access (PIA) just updated recently to a new version with Wireguard as an option to use in place of OpenVPN. I flipped it over to Wireguard but haven't noticed a big diiference yet because I haven't really been looking for one.
I've been using WireGuard since it was supported by Windscribe. Only adds 1ms to my ping. The overhead is near zero. Amazing. The way it instantly connects is the scariest part. You flip the switch and you are connected. No spinning icons, no nothing. I hope they will soon implement real post-quantum authentication and key exchange as well.
Been using it for a long time on Mullvad, Xeovo and Cryptostorm. They there early adapters back in 2019. I think they still have best solution configuration pages. Most flexible and quick.

Lightway: A Superior VPN Experience | ExpressVPN Blog
Introducing Lightway, a brand new, next-generation VPN protocol that will make your connection faster, more reliable, and more secure.
How do you enable it on Windscribe?I've been using WireGuard since it was supported by Windscribe. Only adds 1ms to my ping. The overhead is near zero. Amazing. The way it instantly connects is the scariest part. You flip the switch and you are connected. No spinning icons, no nothing. I hope they will soon implement real post-quantum authentication and key exchange as well.
Open the Windscribe app > Connection > Connection Mode > Manual > Pick "WireGuard", pick whatever port you want.How do you enable it on Windscribe?
Attachments
Got it. ThanksOpen the Windscribe app > Connection > Connection Mode > Manual > Pick "WireGuard", pick whatever port you want.
Has anyone tried Mullvad post-quantum encryption?

 mullvad.net
mullvad.net
You can enable it and it will use the NewHope post-quantum key exchange.
 en.wikipedia.org
en.wikipedia.org

Introducing a post-quantum VPN, Mullvad's strategy for a future problem
As the field of quantum computing progresses, it's possible that today's stored, encrypted information could be decrypted in the future. To mitigate this threat against privacy, we unveil our own post-quantum secure VPN tunnel.
You can enable it and it will use the NewHope post-quantum key exchange.
NewHope - Wikipedia
I gave Lightway a few days ago on the Windows Beta, I think it needs more work as it was the slowest protocol there was, even slower than open, of course it is in beta & there are many other factors involved, but at that time i was surprised it wasn't better - I'll try it again laterExpressVPN has its own new protocol. It's call Lightway
Lightway: A VPN Protocol by ExpressVPN | ExpressVPN
Learn how ExpressVPN’s game-changing new protocol elevates your VPN experience.www.expressvpn.com
It is a new VPN protocol IVPN uses, that is what I know.
Surfshark also integrated it into their IOS App yesterday I guess. I just wonder why it's not on Windows yetIt is a new VPN protocol IVPN uses, that is what I know.
I would try IVPN but I already have a Surfshark subscription till 2023 and it's working well for me. So I will check it out in 3 Years i guessIVPN have a Windows App that uses this protocol.
Ususlly, VPN providers will start with android/IOS first follow by Windows. Just waitSurfshark also integrated it into their IOS App yesterday I guess. I just wonder why it's not on Windows yet
You may also like...
-
Technology Mullvad retires OpenVPN support on desktop, pushing all users to WireGuard
- Started by KnownStormChaser
- Replies: 9
-
New Update ExpressVPN with its Lightway Turbo and Surfshark with 100Gbps servers
- Started by HarborFront
- Replies: 7
-
VPN Infrastructure Update: Privacy First, No Exceptions
- Started by nickstar1
- Replies: 9
-
OOpera’s revamped VPN Pro is here to bring you stronger protection and blazing-fast speeds
- Started by Opera Team
- Replies: 1
-