How would you know or prevent it before you use it ?
Advice Request What would happen if a legimate program, OS, or game somehow had a virus or malware installed on it from the official source?
- Thread starter ng4ever
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Please provide comments and solutions that are helpful to the author of this topic.
- Aug 2, 2020
- 542
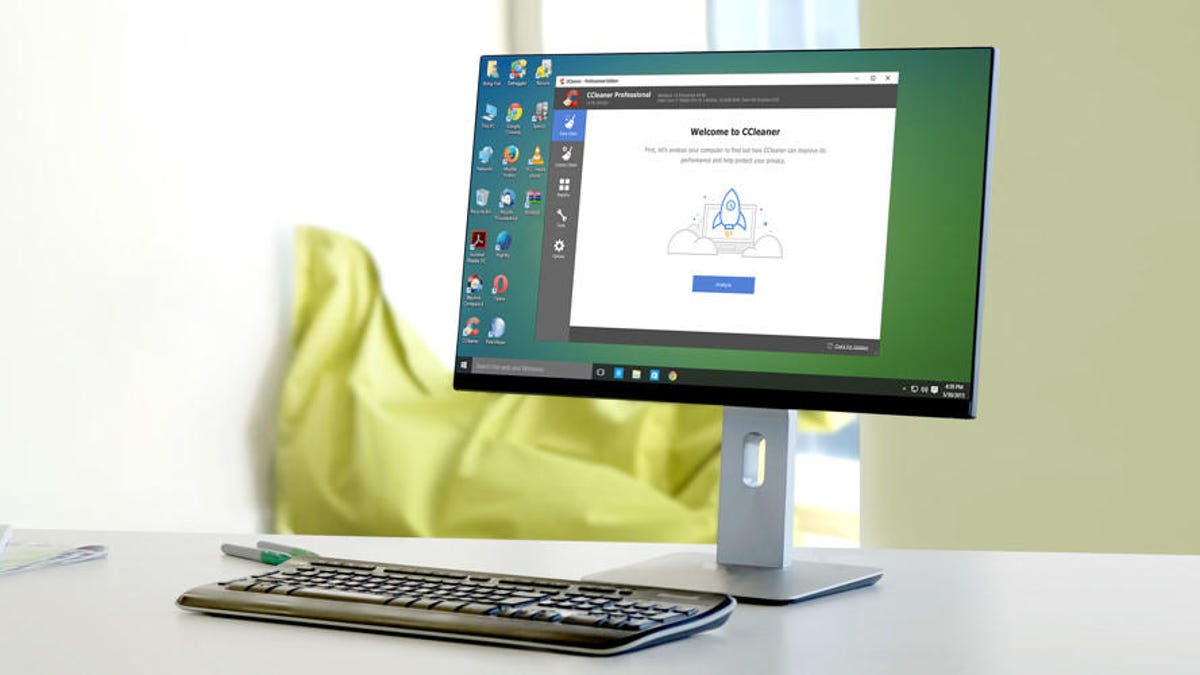
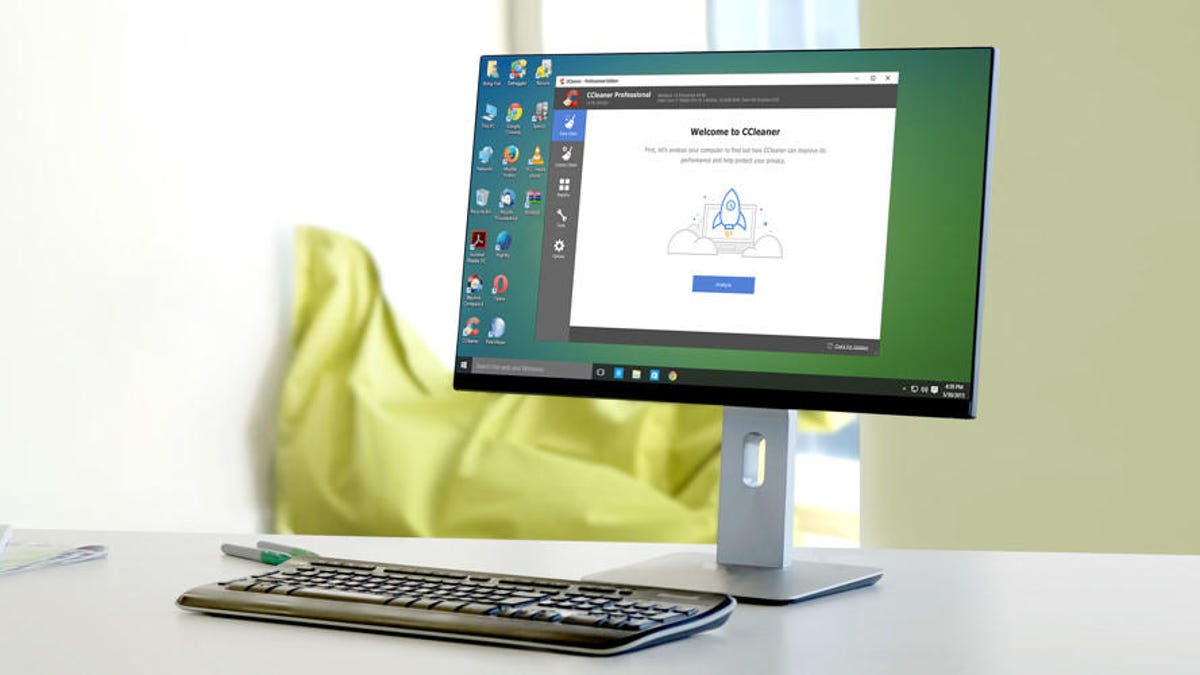
There was an incident with CCleaner being infected with malware sometime ago, but these type of official-source infections are
quite rare from trustworthy companies.
quite rare from trustworthy companies.
Thiagoo
Level 3
- May 10, 2021
- 66
Unusual behavior that is not intended to happen like high CPU/RAM usage, shady processes, weird files appearing.How would you know or prevent it before you use it ?
To prevent it, there's nothing much you can do except having a strong antivirus solution and when possible compare the checksum provided on the website with the file checksum you just downloaded. (the checksum that the website displays can also be modified in some cases, but if only the file is replaced with a compromised one, you'll see that the checksum is different).
It's a good idea to always check the blog from the company/developer to keep yourself updated so you don't keep the compromised version on your PC.
Last edited:
- Jul 2, 2020
- 305
- Aug 22, 2013
- 822
Use of good behavioural blocker/ hips coupled with good hardware firewall and a good malware blocking systemwide Doh ( preferably on router itself). behavioural blocker/ hips does not depend on signatures and whitelisting hence a malware even though signed one can get detected and coupled with a dns blocker would prevent downloading of further payload. I would suggest Nextdns Doh with the below setting enabled ( this setting can block almost all phishing and malware domains as these domains do not last more than a week or so and the malware creators likes to change it every now and then to avoid detection and blacklisting) .How would you know or prevent it before you use it ?
- Apr 16, 2017
- 1,878
There is not much you can do except hope AV will finally discover the malware running on the system. In case of CCleaner malware in 2017 it collected user data for at least 4 days as seen on their C&C server copy.

 www.reuters.com
You could wait for a week to install software updates for apps (to let AVs catch up to new updates and run analysis on them) but sometimes they do include security patches, so not really recommended.
www.reuters.com
You could wait for a week to install software updates for apps (to let AVs catch up to new updates and run analysis on them) but sometimes they do include security patches, so not really recommended.
Edit - Typo
Cisco says it obtained a digital copy of the hackers' command-and-control server from an unnamed source involved in the CCleaner investigation. The server contained a database of every backdoored computer that had "phoned home" to the hackers' machine between September 12 and 16.

Hackers compromised free CCleaner software, Avast's Piriform says
Hackers broke into British company Piriform Ltd's free software that optimises computer performance last month, potentially allowing them to control the devices of millions of users, the company and independent researchers said on Monday.
That's practically not possible for every single app you install, I have more than 50 apps (installed or using portable version) of which 15 are regularly used. The amount of time it would take checking every single app changelog or blog post would be insane, considering they update most updates many times a month.It's a good idea to always check the blog from the company/developer to keep yourself updated so you don't keep the compromised version on your PC.
Edit - Typo
Last edited:
- Aug 2, 2020
- 542
That was the only first incident in 2017 there was another one in 2019There is not much you can do except hope AV running will finally discover the malware running on system. In case of CCleaner malware in 2017 it collected user data for at least 4 days as seen on their C&C server copy.
Avast: No plans to discontinue CCleaner following second hack in two years
Czech intelligence agency: "Data analysis suggests that the attack came from China."
 www.zdnet.com
www.zdnet.com
Thiagoo
Level 3
- May 10, 2021
- 66
When i found out about these incidents, i stopped using Piriform products. In my opinion they are not trustworthy anymore.That was the only first incident in 2017 there was another one in 2019

Avast says hackers breached internal network through compromised VPN profile
Czech antivirus maker discloses second attack aimed at compromising CCleaner releases.www.zdnet.com
- Apr 16, 2017
- 1,878
Yeah that too, 2nd time hackers didn't manage to push out malware to end user though.That was the only first incident in 2017 there was another one in 2019
Avast: No plans to discontinue CCleaner following second hack in two years
Czech intelligence agency: "Data analysis suggests that the attack came from China."www.zdnet.com
F
ForgottenSeer 85179
You can use behaviour techniques @Andy Ful wrote about:
Waiting some days before downloading or installing.
(I sadly can’t find his post about)
Waiting some days before downloading or installing.
(I sadly can’t find his post about)
Yanick
Level 1
- Jun 14, 2021
- 24
Would be good to have working backup solution on hand. Full system image like for every month, incrementals more often.
I tend to keep log on apps that are installed on my computer and have all changes to registery & apps logged via TinyWatcher for any changes.
I tend to keep log on apps that are installed on my computer and have all changes to registery & apps logged via TinyWatcher for any changes.
- Jun 24, 2016
- 2,400
To start with, that would be extremely rare. Possible, yes, but rare. There have only been a few cases in... what, decades?
In order for this ro happen the "trustworthy company" must have been firstly infected, meaning all security measures were beaten, and we're talking corporations-like security.
Given the case, in a scenario where it happened and they were infected, cybercriminals must have taken control over the host where this company sends their software releases/updates, in order for you to get an update on the installed software. Also, they must correctly sign it with the company's certificate in order to not elevate any suspicious looks. Let's set an example that they took an RC copy of a build and just modified it to make it easier.
What would happen next? If the modified copy isn't ridiculous, chances are it won't be detected by almost any antivirus or solution, not even default-deny solutions that work with a trusted vendors list. Within time, two things may occur:
In order for this ro happen the "trustworthy company" must have been firstly infected, meaning all security measures were beaten, and we're talking corporations-like security.
Given the case, in a scenario where it happened and they were infected, cybercriminals must have taken control over the host where this company sends their software releases/updates, in order for you to get an update on the installed software. Also, they must correctly sign it with the company's certificate in order to not elevate any suspicious looks. Let's set an example that they took an RC copy of a build and just modified it to make it easier.
What would happen next? If the modified copy isn't ridiculous, chances are it won't be detected by almost any antivirus or solution, not even default-deny solutions that work with a trusted vendors list. Within time, two things may occur:
- Some lab, user, or company, maybe the trustworthy company themselves detected anomalies and decided to investigate, realizing what occured
- Some bad coding or greed uncovered the operation, like a stupid loop for a callback home, like Ccleaner case, and trigger an antivirus
- Feb 25, 2017
- 2,498
People are stating that the Steam game called "Russiaphobia" is a cryptominer and it's still out there. I can't confirm that but if that's true it's another example of malware on a trusted gaming platform. As people stated above, having an AV with a good behavioural component is essential.
- Apr 13, 2013
- 3,147
This is a case where there is no need for a typical user to worry as there is absolutely nothing one can do about it. On the plus side, however is that such breaches are both difficult and expensive to implement and therefore are really not targeted at Peasants like us (as was the case with the above mentioned CCleaner hack- only those specifically targeted by the first part of the installed Floxif trojan got the actual second part which was the backdoor. Although some still freak the full infection hit probably only 40 systems worldwide, and those belonging to Major corporations).
The more recent case is the massive SolarWinds breach where a malicious dll was woven into a signed update in March 2020. Nothing a typical user could do here as it still would be unknown if not for Mandiant following up on some unusual activity.
The world would be a less worrisome place if Corporations would implement 2FA at every level and Home users would not think WF "is enough" as well as installing every browser extension under the sun.
The more recent case is the massive SolarWinds breach where a malicious dll was woven into a signed update in March 2020. Nothing a typical user could do here as it still would be unknown if not for Mandiant following up on some unusual activity.
The world would be a less worrisome place if Corporations would implement 2FA at every level and Home users would not think WF "is enough" as well as installing every browser extension under the sun.
- Oct 22, 2018
- 435
You're preaching to the choir. Everybody knows Windows Firewall is enough, and if 1 browser extension is good, 2 must be better, and 3 gives you near invincibility. Four makes your browser God like.This is a case where there is no need for a typical user to worry as there is absolutely nothing one can do about it. On the plus side, however is that such breaches are both difficult and expensive to implement and therefore are really not targeted at Peasants like us (as was the case with the above mentioned CCleaner hack- only those specifically targeted by the first part of the installed Floxif trojan got the actual second part which was the backdoor. Although some still freak the full infection hit probably only 40 systems worldwide, and those belonging to Major corporations).
The more recent case is the massive SolarWinds breach where a malicious dll was woven into a signed update in March 2020. Nothing a typical user could do here as it still would be unknown if not for Mandiant following up on some unusual activity.
The world would be a less worrisome place if Corporations would implement 2FA at every level and Home users would not think WF "is enough" as well as installing every browser extension under the sun.
- Jul 3, 2015
- 8,153
Update poisoning is one of the worst and hardest things to defend against. If it is designed very well, it will go undetected for a long time and there is not much you can do about it. But it is not common, and even when it happens, it might be used against a few high-value targets, ignoring home users. That way it flies under the radar for much longer. If it attacks everyone and anyone, it will be detected very fast.
F
ForgottenSeer 85179
Maybe. Maybe not.If it attacks everyone and anyone, it will be detected very fast.
F
ForgottenSeer 85179
found it:You can use behaviour techniques @Andy Ful wrote about:
Waiting some days before downloading or installing.
(I sadly can’t find his post about)

Advice Request - Windows Defender Delay Protection.
Windows Defender Delay Protection is probably stronger than any antivirus Advanced Threat Protection (also that used in Microsoft Defender ATP in Enterprises). WDDP has an advantage that it can be easily understood and applied in a few minutes by most of the average users. So, let's forget...
 malwaretips.com
malwaretips.com
Simply, the user should execute/open the new files with one-day-delay. Why it can be useful? Because after one day, the malware is not 0-day anymore.
- Apr 5, 2021
- 571
This I have to ask about; how does blocking incoming connections help in defending against a malicious process? They typically connect outbound.Windows firewall can block all incoming connections and this is usually enough.
- Jan 28, 2018
- 2,463
It often causes false accusationsA good antivirus will do
Similar threads
- Replies
- 0
- Views
- 1,913
- Replies
- 0
- Views
- 240
Serious Discussion
In the name of stronger security feature, the bank implements this
- Replies
- 2
- Views
- 553

