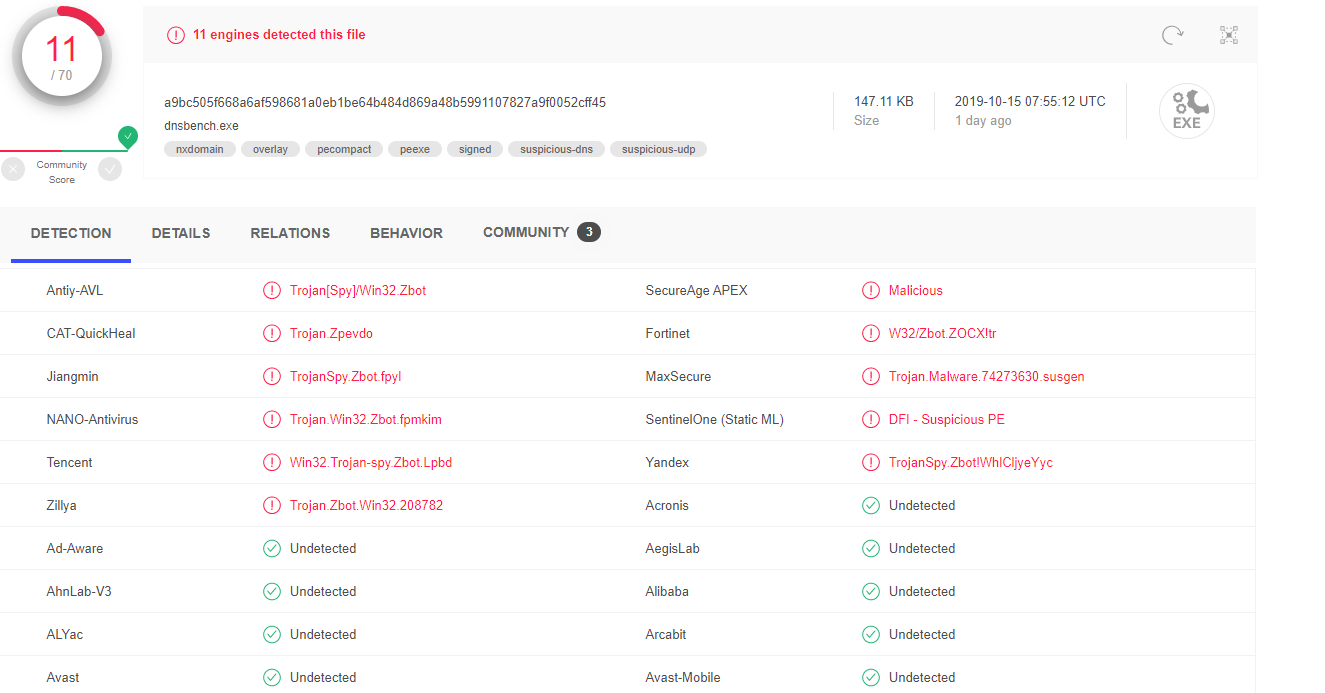
I'm curious what other people's approach is when they hit on potential FPs on something like Virustotal or Hybrid_Analysis? When you check a file from a trusted source such as Steve Gibson's site for DNS Bench and get something like the following screenshot, what do you do? I know a lot of people just say FP all day, but I've always been more prudent. It seems there is usefulness to VT and H_A, but these ML and heuristic detection engines do seem to flag even base Microsoft .exes a lot (looking at you onedrive and processexplorer). In this situation none of the big vendors flagged the file, or the ones that did cleared it over time, but it does always leave a seed of doubt when there's more than one or two FPs. How paranoid are you?
Last edited: