Have you ever noticed a process called “ltsvc.exe” running in your Windows Task Manager and wondered what it is? In this article, we will explore the details of ltsvc.exe, its purpose, and how to uninstall it if necessary.

What is ltsvc.exe?
Ltsvc.exe is a legitimate executable file that is associated with the Logitech Download Assistant, a software component that comes bundled with Logitech devices and drivers. The Logitech Download Assistant is responsible for automatically checking for and installing driver updates for Logitech devices connected to your computer.
When you install Logitech software or connect a Logitech device to your computer, the Logitech Download Assistant is installed as a background process. Ltsvc.exe is the main executable file for this process.
Is ltsvc.exe a Virus or Malware?
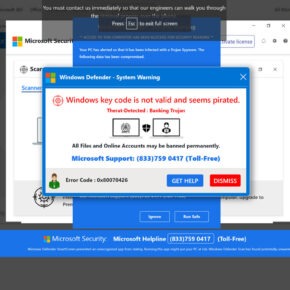
No, ltsvc.exe is not a virus or malware. It is a legitimate file associated with Logitech software. However, like any executable file, it is possible for malicious software to disguise itself as ltsvc.exe. Therefore, it is important to ensure that the ltsvc.exe process running on your computer is indeed the legitimate Logitech Download Assistant.
If you suspect that the ltsvc.exe process on your computer is malicious, it is recommended to run a scan with an antivirus program such as Malwarebytes Free. Antivirus software can help detect and remove any potential threats.
How to Uninstall ltsvc.exe
If you no longer use Logitech devices or software and want to uninstall ltsvc.exe, you can follow these steps:
- Open the Control Panel on your Windows computer.
- Click on “Programs” or “Programs and Features.”
- Locate Logitech Download Assistant or any Logitech software in the list of installed programs.
- Right-click on the Logitech software and select “Uninstall” or “Remove.”
- Follow the on-screen instructions to complete the uninstallation process.
After uninstalling Logitech software, the ltsvc.exe process should no longer be running on your computer.
Should You Uninstall ltsvc.exe?
Whether or not you should uninstall ltsvc.exe depends on your usage of Logitech devices and software. If you still use Logitech devices and want to receive automatic driver updates, it is recommended to keep ltsvc.exe installed.
However, if you no longer use Logitech devices or prefer to manually update your drivers, you can safely uninstall ltsvc.exe without any negative impact on your computer’s performance or functionality.
Conclusion
Ltsvc.exe is a legitimate executable file associated with the Logitech Download Assistant. It is responsible for automatically checking for and installing driver updates for Logitech devices. While it is not a virus or malware, it is important to ensure that the ltsvc.exe process running on your computer is legitimate.
If you no longer use Logitech devices or software, you can uninstall ltsvc.exe by following the steps outlined in this article. However, if you still use Logitech devices and want to receive automatic driver updates, it is recommended to keep ltsvc.exe installed.
Remember, if you suspect any malicious activity on your computer, it is always a good idea to run a scan with an antivirus program such as Malwarebytes Free to ensure the security of your system.

![How to Remove Jeiia.co.in Pop-ups [Virus Removal Guide] 3 McAfee scam 4](https://malwaretips.com/blogs/wp-content/uploads/2023/08/McAfee-scam-4-290x290.jpg)