Backdoor:Win32/Rbot.gen is a generic detection for a family of backdoor Trojans that allows attackers to control infected computers.
After a computer is infected, the Trojan connects to a specific IRC server and joins a specific channel to receive commands from attackers. Commands can instruct the Trojan to spread to other computers by scanning for network shares with weak passwords, exploiting Windows vulnerabilities, and spreading through backdoor ports opened by other families of malicious software. The Trojan can also allow attackers to perform other backdoor functions, such as launching denial of service (DoS) attacks and retrieving system information from infected computers.
Backdoor:Win32/Rbot.gen can give a malicious hacker access and control of your PC. They can then perform a number of different actions, such as:
- Deleting files
- Downloading and running files
- Logging your keystrokes or stealing your sensitive data
- Modifying your system settings
- Running or stopping applications
- Spreading malware to other PCs
- Uploading files
Always opt for the custom installation and deselect anything that is not familiar, especially optional software that you never wanted to download and install in the first place. It goes without saying that you should not install software that you don’t trust.
How to remove Backdoor:Win32/Rbot.gen (Removal Guide)
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
-
To remove Backdoor:Win32/Rbot.gen, follow these steps:
- STEP 1: Scan your computer with Malwarebytes Anti-Malware
- STEP 2: Scan your computer with HitmanPro
- (OPTIONAL) STEP 3: Scan your computer with Zemana AntiMalware
STEP 1: Scan your computer with Malwarebytes Anti-Malware
Malwarebytes Anti-Malware is a powerful on-demand scanner which will remove the Backdoor:Win32/Rbot.gen malware from your machine. It is important to note that Malwarebytes Anti-Malware will run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download “Malwarebytes Anti-Malware”) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup” to start the installation of Malwarebytes Anti-Malware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
- Once installed, Malwarebytes Anti-Malware will automatically start and will update the antivirus database. To start a system scan you can click on the “Scan Now” button.
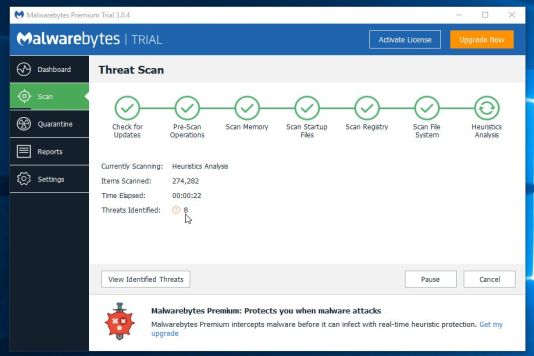
- Malwarebytes Anti-Malware will now start scanning your computer for the Backdoor:Win32/Rbot.gen browser hijacker. When Malwarebytes Anti-Malware is scanning it will look like the image below.
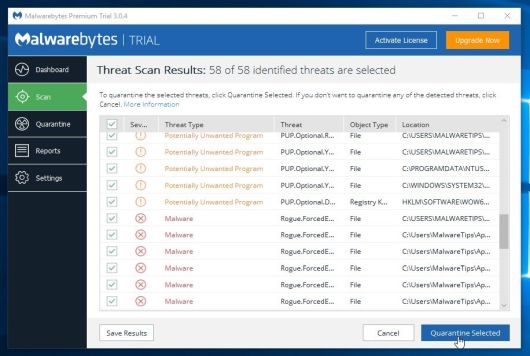
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Remove Selected” button.
- Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
STEP 2: Scan your computer with HitmanPro
HitmanPro finds and removes malware, adware, bots and other threats that even the best antivirus suite can oftentimes miss. It’s designed to run alongside your antivirus suite, firewall and other security tools.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows).
Click on the “Next” button, to install HitmanPro on your computer.
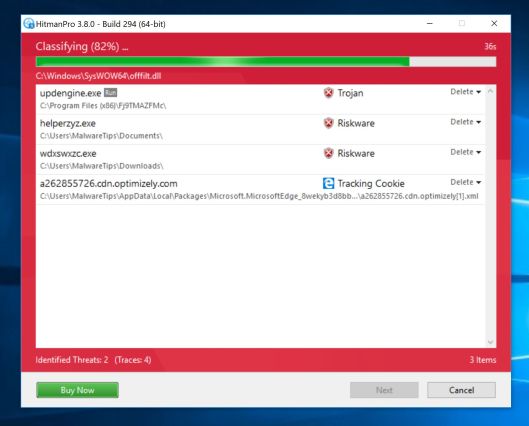
- HitmanPro will now begin to scan your computer for malware.
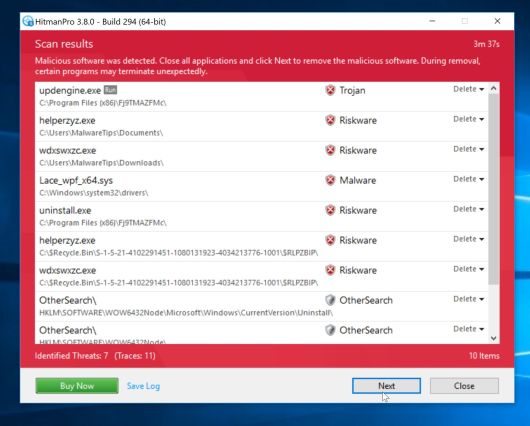
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
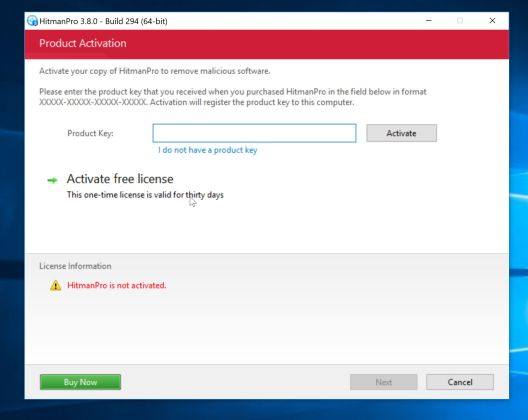
- Click on the “Activate free license” button to begin the free 30 days trial and remove all the malicious files from your computer.
(OPTIONAL) STEP 3: Scan your computer with Zemana AntiMalware
This step should be performed only if your issues have not been solved by the previous steps.
- You can download Zemana AntiMalware from the below link:
ZEMANA ANTIMALWARE DOWNLOAD LINK (This link will start the download of “Zemana AntiMalware”) - Double-click on the file named “Zemana.AntiMalware.Setup.exe” to start the installation of Zemana AntiMalware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- Click on the “Next” button, to install Zemana AntiMalware on your computer.
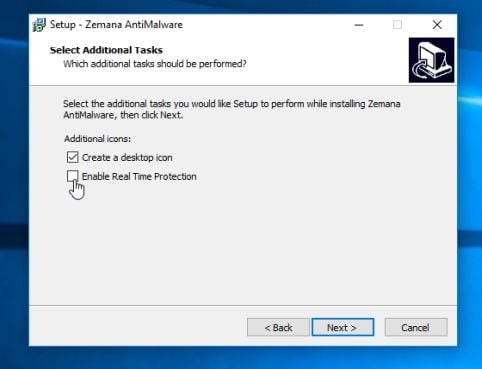
When you reach the “Select Additional Tasks” screen, you can opt-out the “Enable Real Time Protection” option, then click on the “Next” button.
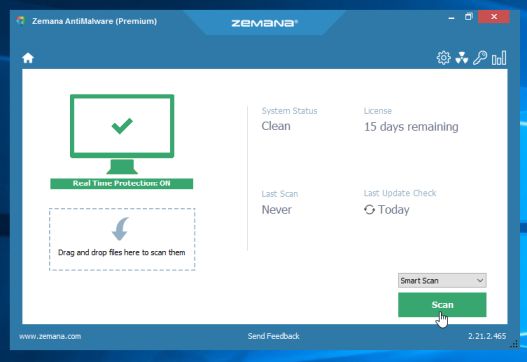
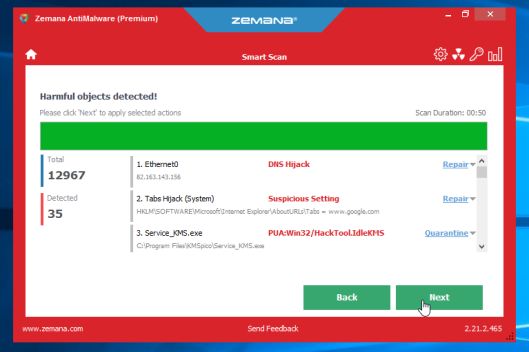
- When Zemana AntiMalware will start, click on the “Scan” button.
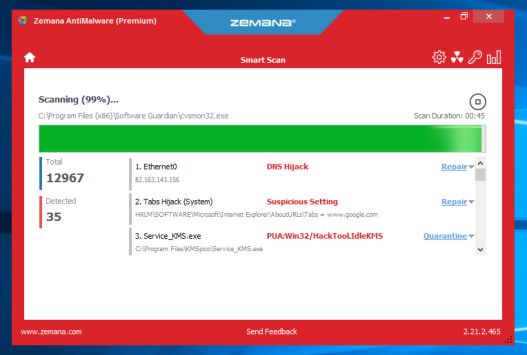
- Zemana AntiMalware will now scan computer for malicious files. This process can take up to 10 minutes.
- When Zemana AntiMalware has finished it will display a list of all the malware that the program found. Click on the “Next” button, to remove the malicious files from your computer.
Zemana AntiMalware will now remove all the detected malicious files and at the end a system reboot may be required to remove all traces of malware.