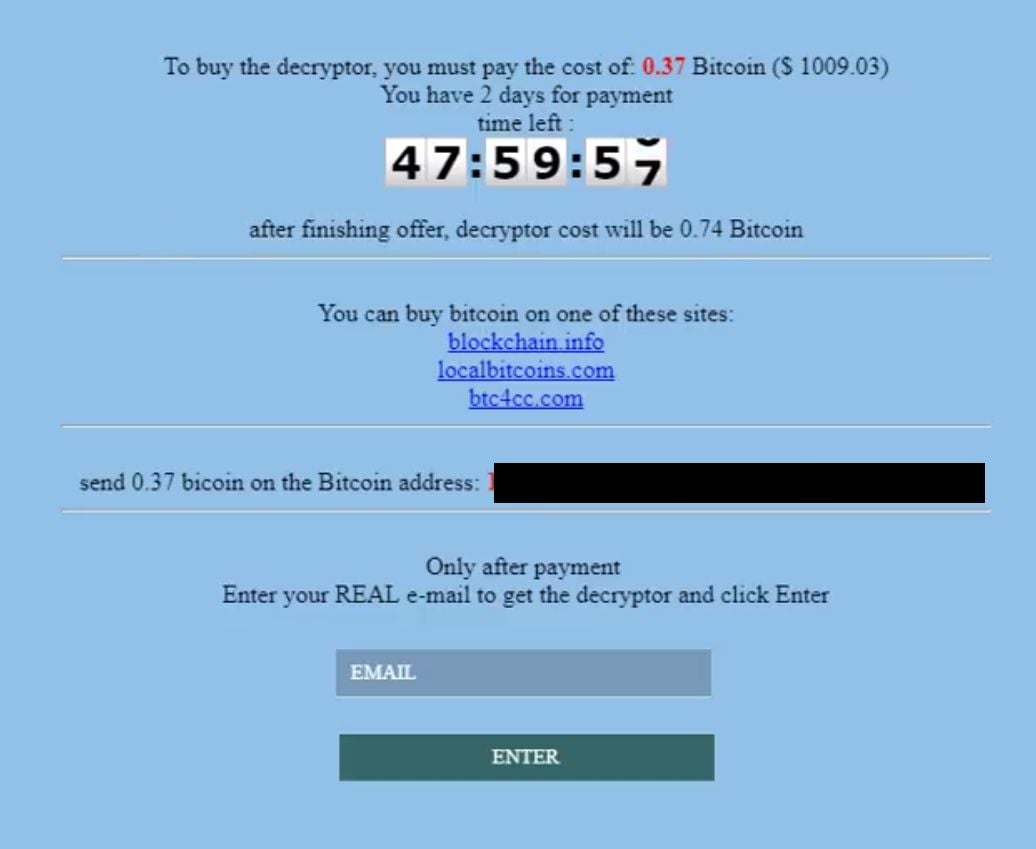
GlobeImposter is a file-encrypting ransomware, which will encrypt the personal documents found on victim’s, appending the ..726 extension to encrypted files. The GlobeImposter ransomware then displays a message which offers to decrypt the data if a payment between 0.37 to 0.74 Bitcoins is made.
Files encrypted by older versions of the GlobeImposter Ransomware may be recovered with the Emsisoft Decrypter for GlobeImposter tool.
There is no decryption tool available for the .”.726″ GlobeImposter Ransomware. However, you can try to search these webpages for updates:
- 1. What is the GlobeImposter Ransomware?
- 2. How did the GlobeImposter ransomware get on my computer?
- 3. Is it possible to decrypt files encrypted by GlobeImposter ransomware?
- 4. How to remove the GlobeImposter ransomware (Virus Removal Guide)
- 5. How to protect your PC from the GlobeImposter ransomware
1. What is the GlobeImposter ransomware?
- Ransomware name: GlobeImposter Ransomware
- Added Extensions: ..726, .txt”, “.ACTUM”, “.492”, “.astra”, “.coded”, “.mtk118”, “.cryptch”, “.PLIN”, “.sea”, “.help”, “..726”, “.RECT”, “.ocean”, “.rose”, “.GLAD”, “.725”, “.[tramkal@protonmail.ch]cryptall”, “.write_me_[btc2017@india.com]”, “.BRT92”, “p1crypt”, “.MAKB”, “.skunk”, “.au1crypt”, “.GOTHAM”, “.s1crypt”, “.GORO”, “.707”, “.3ncrypt3d”, .626, .blcrypt, .blscrypt, .nopasaran, “.xyrpottim228@ya.ru”, “.VAPE”, “.crypt”, “.pscrypt”, “.oni”, “.pizdosik”, “.[File-Help1@Ya.Ru]”,”.[aezakmi@india.com]”, “.GRAF”, “.fix”, “.virginprotection”, “.WRITE_US”, “.MIXI”, “.HAPP”, “.troy”, “.write_us_on_email”, “.PRIAPOS”, “.515”, “.nCrypt”, “.hNcrypt”, “.medal”, “.paycyka”, “.2cXpCihgsVxB3”, “.vdul”, “.keepcalm”, “.legally”, “.crypt”, “.wallet” or “.pizdec
- Ransomware note: RECOVER-FILES-726.html
- Ransom: From 0.37 to 0.74 Bitcoins
The GlobeImposter ransomware restricts access to data by encrypting files with the ..726 extension. It then attempts to extort money from victims by asking for “ransom,” in form of the Bitcoin cryptocurrency, in exchange for access to data.
The GlobeImposter ransomware targets all versions of Windows including Windows 10, Windows 8.1 and Windows 7. This infection is notable due to how it encrypts the user’s files – namely, it uses AES-265 and RSA encryption method – in order to ensure that the affected user has no choice but to purchase the private key.
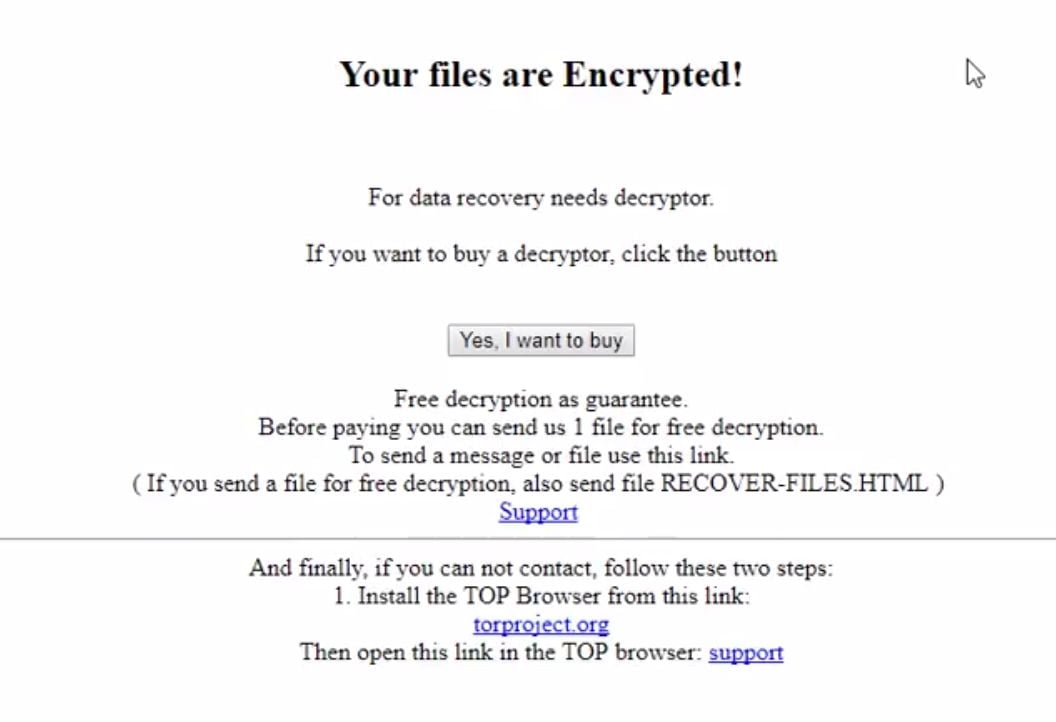
When GlobeImposter ransomware infects a PC it will scan all the drive letters for targeted file types, encrypt them, and then append the ..726 extension to them. Once these files are encrypted, they will no longer able to be opened by your normal programs. When GlobeImposter ransomware has finished encrypting the victim’s files, it will also display a RECOVER-FILES-726.html ransom note.
These RECOVER-FILES-726.html files are located in every folder that a file was encrypted as well as in the user’s Startup folder so that they are automatically displayed when a user logs in. These files will contain the information on how to access the payment site and get your files back.
The message of the RECOVER-FILES-726.html ransom note is:
Your files are encrypted!
All your important data has been encrypted.
To recover data you need decryptor.
To get the decryptor you should:
pay for decrypt:
site for buy bitcoin:
Buy 1 BTC on one of theses site:
1. localbitcoins.com
2. coinbase.com
3. xchange.ccBitcoin address to pay:
Send 1 BTC for decrypt. After the payment: Send screenshot of payment to sendmebtc@india.com, byd@india.com. In the letter include your personal ID (look at the beginning of this document). After you will receive a decryptor and instructions. Attention! No Payment = No decryption. You really get the decryptor after payment. Do not attempt to remove the program or run the anti-virus tools. Attempts to self-decrypting files will result in the loss of your data. Decoders other users are not compatible with your data, because each user’s unique encryption key.
When the infection has finished scanning your computer it will also delete all of the Shadow Volume Copies that are on the affected computer. It does this so that you cannot use the shadow volume copies to restore your encrypted files.
2. How did the GlobeImposter ransomware get on my computer?
The GlobeImposter ransomware is distributed via spam email containing infected attachments or links to malicious websites. Cyber-criminals spam out an email, with forged header information, tricking you into believing that it is from a shipping company like DHL or FedEx. The email tells you that they tried to deliver a package to you, but failed for some reason. Sometimes the emails claim to be notifications of a shipment you have made. Either way, you can’t resist being curious as to what the email is referring to – and open the attached file (or click on a link embedded inside the email). And with that, your computer is infected with the GlobeImposter ransomware.
3. Is it possible to decrypt files encrypted by GlobeImposter ransomware?
Depending of the GlobeImposter ransomware version that has infected your PC, the documents can be recovered with the Emsisoft Decrypter for GlobeImposter tool.
GlobeImposter ransomware is notable due to how it encrypts the user’s files – namely, it uses AES-265 and RSA encryption method – in order to ensure that the affected user has no choice but to purchase the private key. The RSA public key can only be decrypted with its corresponding private key. Since the AES key is hidden using RSA encryption and the RSA private key is not available, decrypting the files is not feasible as of this writing.
Brute forcing the decryption key is not realistic due to the length of time required to break an AES encryption key. Unfortunately, once the GlobeImposter encryption of the data is complete, decryption is not feasible without paying the ransom.
Because the needed private key to unlock the encrypted file is only available through the cyber criminals, victims may be tempted to purchase it and pay the exorbitant fee. However, doing so may encourage these bad guys to continue and even expand their operations. We strongly suggest that you do not send any money to these cyber criminals, and instead address to the law enforcement agency in your country to report this attack.
Restore the files encrypted by GlobeImposter ransomware with recovery software
Option 1: Restore your files encrypted by GlobeImposter ransomware with ShadowExplorer
GlobeImposter ransomware will attempt to delete all shadow copies when you first start any executable on your computer after becoming infected. Thankfully, the infection is not always able to remove the shadow copies, so you should continue to try restoring your files using this method.
- You can download ShadowExplorer from the below link:
SHADOW EXPLORER DOWNLOAD LINK (This link will open a new web page from where you can download “ShadowExplorer”) - Once you have downloaded and installed ShadowExplorer, you can follow the below video guide on how to restore your files while using this program.
Alternatively, you can use the System Restore to try to recover the encrypted documents.
Option 2: Restore your files encrypted by GlobeImposter ransomware with File Recovery Software
When GlobeImposter encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you can use file recovery software such as:
- Recuva
You can follow the below guide on how to use Recuva:
- EaseUS Data Recovery Wizard Free
- R-Studio
4. How to remove the GlobeImposter ransomware (Virus Removal Guide)
It’s important to understand that by starting the removal process you risk losing your files, as we cannot guarantee that you will be able to recover them. Furthermore, your files may be permanently compromised when trying to remove this infection or trying to recover the encrypted documents.Malwarebytes and HitmanPro can detect and remove this infection, however these programs cannot recover your encrypted files.
STEP 1: Use Malwarebytes to remove the GlobeImposter Ransomware
Malwarebytes is a powerful on-demand scanner which will remove the GlobeImposter Ransomware from your machine. It is important to note that Malwarebytes will run alongside antivirus software without conflicts.
- You can download download Malwarebytes from the below link.
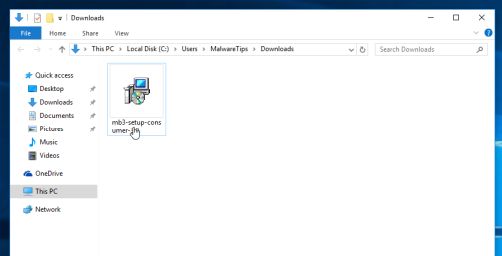
MALWAREBYTES DOWNLOAD LINK (This link open a new page from where you can download “Malwarebytes”) - When Malwarebytes has finished downloading, double-click on the “mb3-setup-consumer” file to install Malwarebytes on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- When the Malwarebytes installation begins, you will see the Malwarebytes Setup Wizard which will guide you through the installation process.
To install Malwarebytes on your machine, keep following the prompts by clicking the “Next” button.
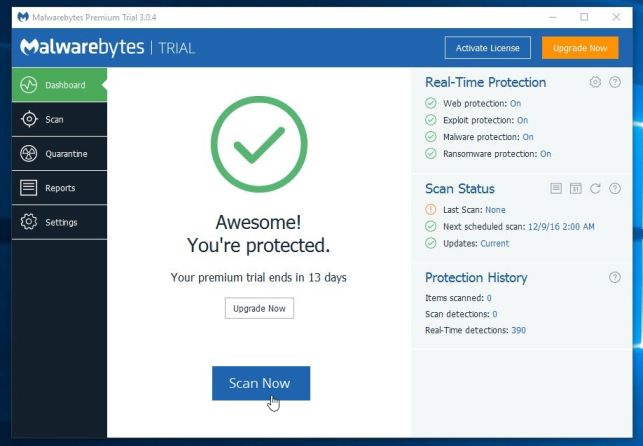
- Once installed, Malwarebytes will automatically start and update the antivirus database. To start a system scan you can click on the “Scan Now” button.
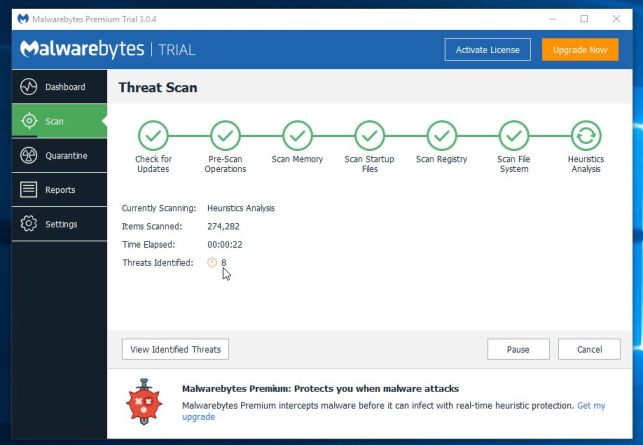
- Malwarebytes will now start scanning your computer for malicious programs.
This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
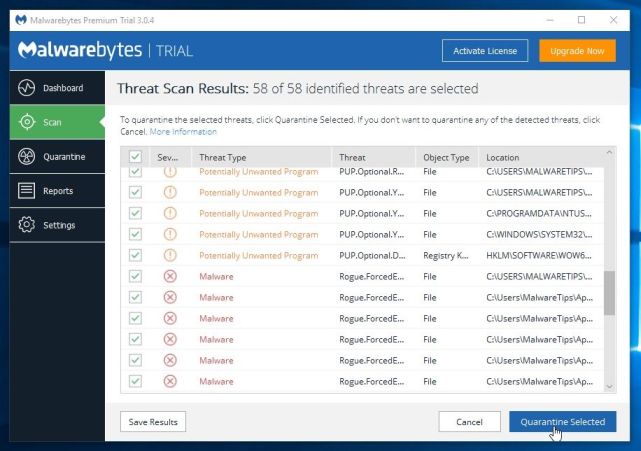
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected.
To remove the malicious programs that Malwarebytes has found, click on the “Quarantine Selected” button.
- Malwarebytes will now quarantine all the malicious files and registry keys that it has found.
To complete the malware removal process, Malwarebytes may ask you to restart your computer.
When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
STEP 2: Double-check for the GlobeImposter ransomware with HitmanPro
HitmanPro finds and removes malware, adware, bots, and other threats that even the best antivirus suite can oftentimes miss. It’s designed to run alongside your antivirus suite, firewall, and other security tools.
- You can download HitmanPro from the below link:
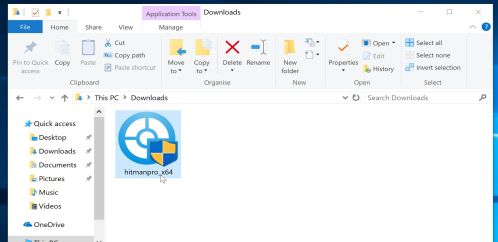
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - When HitmanPro has finished downloading, double-click on the “hitmanpro” file to install this program on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- When the program starts you will be presented with the start screen as shown below. Now click on the Next button to continue with the scan process.
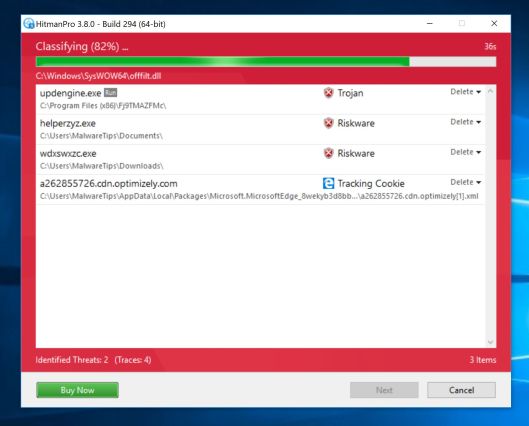
- HitmanPro will now begin to scan your computer for malware.
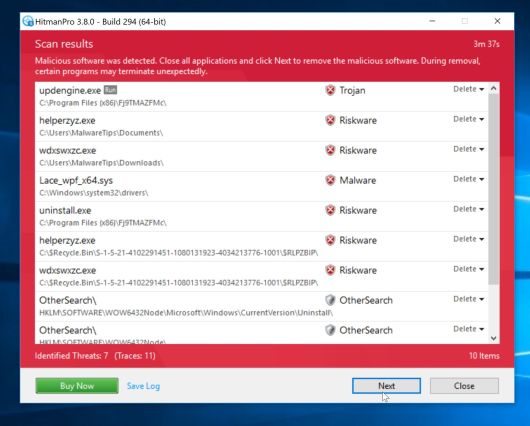
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
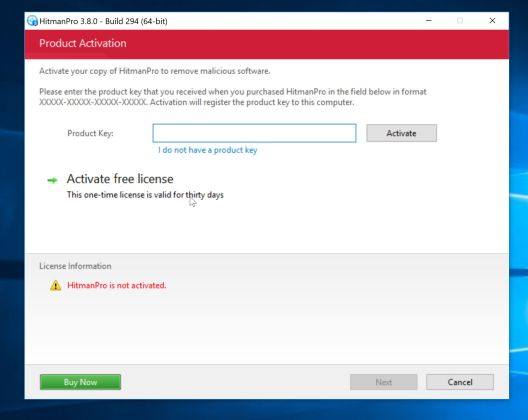
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
When the process is complete, you can close HitmanPro and continue with the rest of the instructions.
5. How to protect your PC from the GlobeImposter ransomware
To protect your computer from the GlobeImposter ransomware, you should always have an antivirus installed on your computer and always have a backup for your personal documents.
Your computer should now be free of the GlobeImposter ransomware infection. If you are still experiencing problems while trying to remove GlobeImposter ransomware, please do one of the following:
- Run a system scan with Emsisoft Emergency Kit
- Ask for help in our Malware Removal Assistance forum.