Trojan.Modified is a generic detection used by Malwarebytes Anti-Malware, Microsoft Security Essentials, Norton Antivirus and other antivirus products for a file that appears to have trojan-like features or behavior.
What is the Trojan.ModifiedUPX infection?
Trojan.ModifiedUPX is a is a broad classification used by Avast Antivirus, Microsoft Secuirty Essentials, Malwarebytes Anti-Malware and other antivirus engines a file that appears to have trojan-like features or behavior for software that exhibits suspicious behavior categorized as potentially malicious.
The Behavior Monitoring feature observes the behavior of processes as they run programs. If it observes a process behaving in a potentially malicious way, it reports the program the process is running as potentially malicious.
Due to the generic nature of this detection, methods of installation may vary. The Trojan.ModifiedUPX infections may often install themselves by copying their executable to the Windows or Windows system folders, and then modifying the registry to run this file at each system start. Trojan.ModifiedUPXwill often modify the following subkey in order to accomplish this:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
Again, the generic nature of this detection means that the Payloads performed by Trojan.ModifiedUPX may be highly variable, and therefore difficult to describe specifically. Trojan.ModifiedUPX has been observed to perform any, or all, of the following actions:
- redirect Web traffic
- manipulate certain Windows or third-party applications including settings or configurations
- drop or install additional malicious programs
- download and run additional malicious programs
Please note that this list is not exhaustive.
Is Trojan.ModifiedUPX a False Positive ?
Files reported as Trojan.ModifiedUPX are not necessarily malicious. For example, users can be tricked into using non-malicious programs, such as Web browsers, to unknowingly perform malicious actions, such as downloading malware. Some otherwise harmless programs may have flaws that malware or attackers can exploit to perform malicious actions. Should you be uncertain as to whether a file has been reported correctly, we encourage you to submit the affected file to https://www.virustotal.com/en/ to be scanned with multiple antivirus engines.
How did Trojan.ModifiedUPX infection got on my computer?
The Trojan.ModifiedUPX virus is distributed through several means. Malicious websites, or legitimate websites that have been hacked, can infect your machine through exploit kits that use vulnerabilities on your computer to install this Trojan without your permission of knowledge.
Another method used to propagate this type of malware is spam email containing infected attachments or links to malicious websites. Cyber-criminals spam out an email, with forged header information, tricking you into believing that it is from a shipping company like DHL or FedEx. The email tells you that they tried to deliver a package to you, but failed for some reason. Sometimes the emails claim to be notifications of a shipment you have made. Either way, you can’t resist being curious as to what the email is referring to – and open the attached file (or click on a link embedded inside the email). And with that, your computer is infected with the Trojan.ModifiedUPX virus.
The threat may also be downloaded manually by tricking the user into thinking they are installing a useful piece of software, for instance a bogus update for Adobe Flash Player or another piece of software.
How to remove Trojan.ModifiedUPX virus (Removal Guide)
This page is a comprehensive guide, which will remove the Trojan.ModifiedUPX infection from your your computer. Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
STEP 1: Remove Trojan.ModifiedUPX Master Boot Record infection with Kaspersky TDSSKiller
STEP 2: Remove Trojan.ModifiedUPX virus with Malwarebytes Anti-Malware Free
STEP 3: Remove Trojan.ModifiedUPX trojan with RogueKiller
STEP 4: Remove Trojan.ModifiedUPX infection with HitmanPro
STEP 5: Double check for any left over infections with Emsisoft Emergency Kit
STEP 6: Remove Trojan.ModifiedUPX adware with AdwCleaner
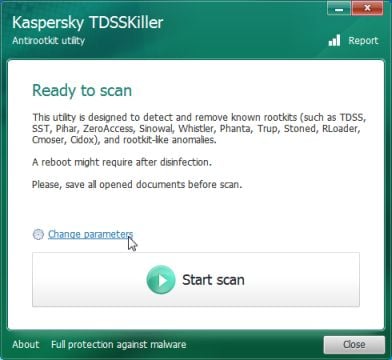
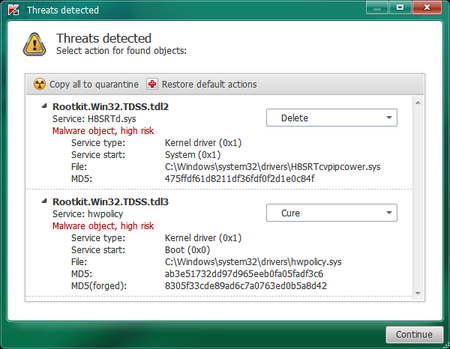
STEP 1: Remove Trojan.ModifiedUPX trojan with Kaspersky TDSSKiller
As part of its self defense mechanism, Trojan.ModifiedUPX virus will install a ZeroAccess rootkit on the infected computer.In this first step, we will run a system scan with Kaspersky TDSSKiller to remove this rookit.
- Please download the latest official version of Kaspersky TDSSKiller.
KASPERSKY TDSSKILLER DOWNLOAD LINK(This link will automatically download Kaspersky TDSSKiller on your computer.) - Double-click on tdsskiller.exe to open this utility, then click on Change Parameters.
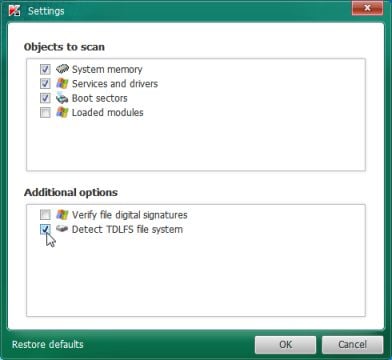
- In the new open window,we will need to enable Detect TDLFS file system, then click on OK.
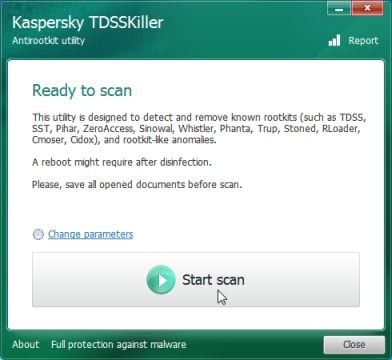
- Next,we will need to start a scan with Kaspersky, so you’ll need to press the Start Scan button.
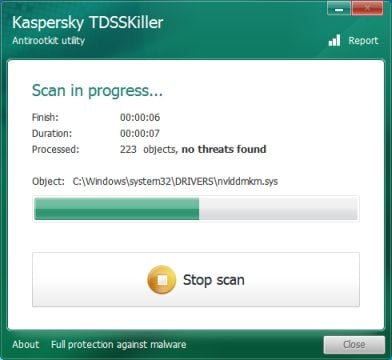
- Kaspersky TDSSKiller will now scan your computer for Trojan Trojan.ModifiedUPX infection.
- When the scan has finished it will display a result screen stating whether or not the infection was found on your computer. If it was found it will display a screen similar to the one below.
- To remove the infection simply click on the Continue button and TDSSKiller will attempt to clean the infection.A reboot will be require to completely remove any infection from your system.
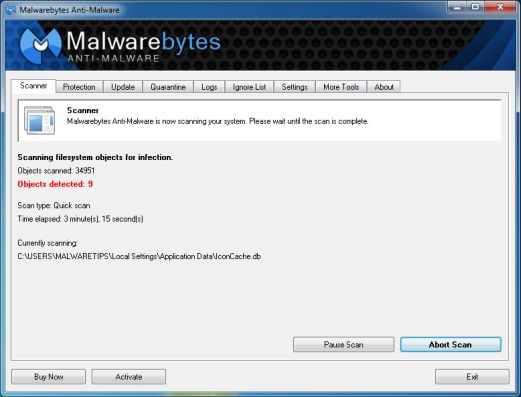
STEP 2: Remove Trojan.ModifiedUPX virus with Malwarebytes Anti-Malware FREE
Malwarebytes Anti-Malware Free is a powerful on-demand scanner which will remove Trojan.ModifiedUPX malicious files from your computer.
- You can download Malwarebytes Anti-Malware Free from the below link, then double-click on the icon named mbam-setup.exe to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK(This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process, then at the last screen click on the Finish button.
- On the Scanner tab, select Perform quick scan, and then click on the Scan button to start searching for the Trojan.ModifiedUPX malicious files.
- Malwarebytes’ Anti-Malware will now start scanning your computer for Trojan.ModifiedUPX virus as shown below.
- When the Malwarebytes Anti-Malware scan has finished, click on the Show Results button.
- You will now be presented with a screen showing you the computer infections that Malwarebytes Anti-Malware has detected. Make sure that everything is Checked (ticked), then click on the Remove Selected button.
- Once your computer will restart in Windows regular mode, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats.
STEP 3: Remove Trojan.ModifiedUPX rootkit with RogueKiller
RogueKiller is a utility that will scan for the Trojan.ModifiedUPX rootkit, registry keys and any other malicious files on your computer.
- You can download the latest official version of RogueKiller from the below link.
ROGUEKILLER DOWNLOAD LINK (This link will automatically download RogueKiller on your computer) - Double click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds, then click on the Scan button to perform a system scan.
- After the scan has completed, press the Delete button to remove Trojan.ModifiedUPX malicious registry keys or files.
STEP 4: Remove Trojan.ModifiedUPX infection with HitmanPro
HitmanPro is a cloud on-demand scanner, which will scan your computer with 5 antivirus engines (Emsisoft, Bitdefender, Dr. Web, G-Data and Ikarus) for the Trojan.ModifiedUPX infection.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a web page from where you can download HitmanPro) - Double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.
Click on the Next button, to install HitmanPro on your computer.
- HitmanPro will now begin to scan your computer for Trojan.ModifiedUPX trojan.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the Next button, to remove Trojan.ModifiedUPX virus.
- Click on the Activate free license button to begin the free 30 days trial, and remove all the malicious files from your computer.
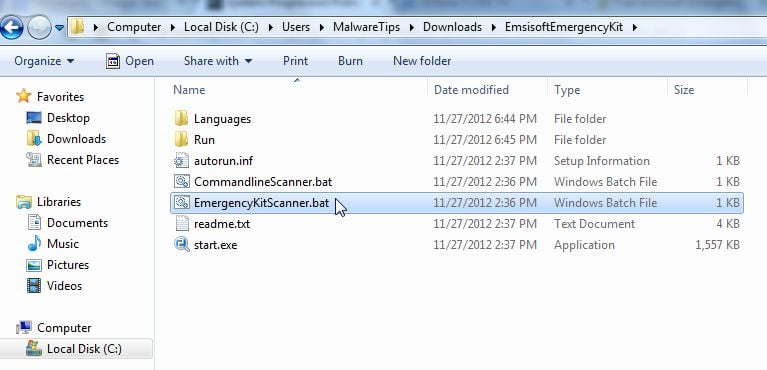
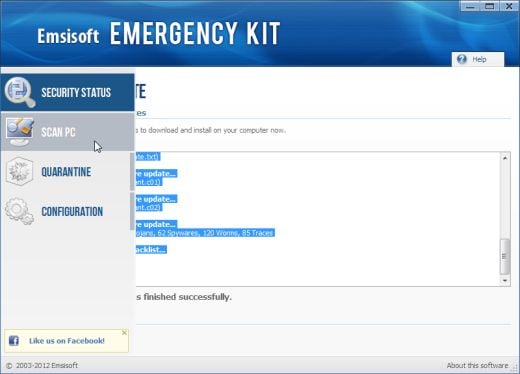
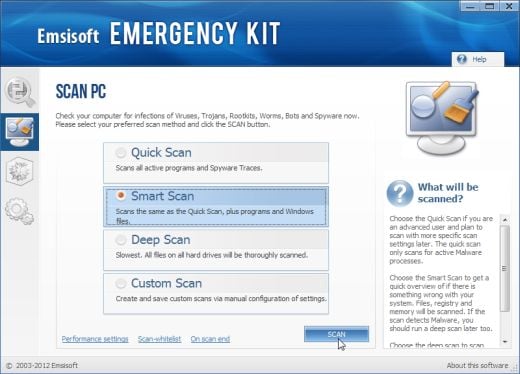
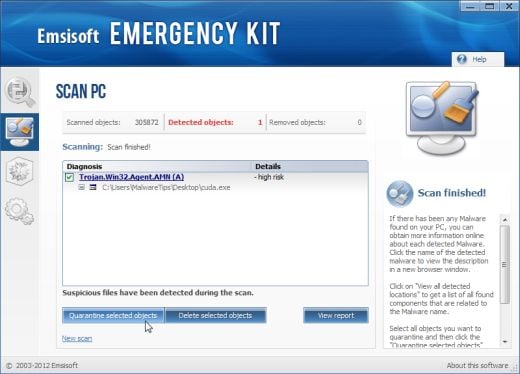
STEP 5: Double check for any left over infections with Emsisoft Emergency Kit
- You can download Emsisoft Emergency Kit from the below link,then extract it to a folder in a convenient location.
EMSISOFT EMERGENCY KIT DOWNLOAD LINK ((This link will open a new web page from where you can download Emsisoft Emergency Kit) - Open the Emsisoft Emergency Kit folder and double click EmergencyKitScanner.bat, then allow this program to update itself.
- After the Emsisoft Emergency Kit has update has completed,click on the Menu tab,then select Scan PC.
- Select Smart scan and click on the SCAN button to search for “Antivirus Security 2013” malicious files.
- When the scan will be completed,you will be presented with a screen reporting which malicious files has Emsisoft detected on your computer, and you’ll need to click on Quarantine selected objects to remove them.
STEP 6: Remove Trojan.ModifiedUPX adware with AdwCleaner
The AdwCleaner utility will scan your computer for Trojan.ModifiedUPX malicious files that may have been installed on your computer without your knowledge.
- You can download AdwCleaner utility from the below link.
ADWCLEANER DOWNLOAD LINK (This link will automatically download AdwCleaner on your computer) - Before starting AdwCleaner, close all open programs and internet browsers, then double-click on the AdwCleaner icon.
If Windows prompts you as to whether or not you wish to run AdwCleaner, please allow it to run. - When the AdwCleaner program will open, click on the Scan button as shown below.
AdwCleaner will now start to search for Trojan.ModifiedUPX malicious files that may be installed on your computer. - To remove the Trojan.ModifiedUPX malicious files that were detected in the previous step, please click on the Clean button.
AdwCleaner will now prompt you to save any open files or data as the program will need to reboot the computer. Please do so and then click on the OK button.
Your computer should now be free of the Trojan.ModifiedUPX infection. If your current anti-virus solution let this infection through, you may want to consider purchasing the PRO version of Malwarebytes Anti-Malware to protect against these types of threats in the future, and perform regular computer scans with HitmanPro.
If you are still experiencing problems while trying to remove Trojan.ModifiedUPX from your machine, please start a new thread in our Malware Removal Assistance forum.
![Malwarebytes Anti-Malware installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Malwarebytes Anti-Malwar removing Trojan.ModifiedUPX virus [Image: Malwarebytes Anti-Malwar removing Trojan.ModifiedUPX virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)
![Click on the Start button to perform a system scan [Image: RogueKiller scaning for Trojan.ModifiedUPX virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-scan.jpg)
![Press Delete to remove Luhe.Sirefef.A [Image: RogueKiller Detele button]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-delete.jpg)




![HitmanPro free 30 days trial [Image: HitmanPro 30 days activation button]](http://malwaretips.com/blogs/wp-content/uploads/2012/11/hitmanpro-activation.jpg)
![Click on Scan button to search for Trojan.ModifiedUPX infection [Image: Adwcleaner Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/08/adwcleaner-scan.jpg)
![Click on the Clean button to remove Trojan.ModifiedUPX virus [Image: AdwCleaner removing infections]](http://malwaretips.com/blogs/wp-content/uploads/2013/08/adwcleaner-cleanup.jpg)







