This info will be displayed after pressing the <INFO> button:
*************************
PROTECTION LEVELS **
*************************
### The below settings are the same for DEFAULT, HIGH, and MAX Protection Levels:
BASIC DEFENDER SETTINGS
- Behavior Monitoring = ON
- Block At First Sight = ON
- Cloud-delivered Protection = ON
- Automatic Sample Submission = Send
- Scan all downloaded files and attachments = ON
- Script Scanning = ON
- Average CPU load while scanning = 50%
### The DEFAULT Protection Level applies the other settings as follows:
BASIC DEFENDER SETTINGS
- PUA Protection = Disabled
- Cloud Protection Level = Default
- Cloud Check Time Limit = 10s
ADMIN: SMARTSCREEN
- For Explorer = User
- For Edge (not Chromium) = User
- For Internet Explorer = User
EXPLOIT GUARD ---> All settings set to Disabled
ADMIN: HIDE SECURITY CENTER = Visible
### The HIGH Protection Level applies the other settings as follows:
BASIC DEFENDER SETTINGS
- PUA Protection = ON
- Cloud Protection Level = Highest
- Cloud Check Time Limit = 20s
ADMIN: SMARTSCREEN
- For Explorer = User
- For Edge (not Chromium) = User
- For Internet Explorer = User
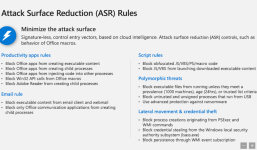
EXPLOIT GUARD ---> All settings set to ON, except the below:
- Block executable files from running unless they meet a prevalence, age, or
trusted list criteria = Disabled
- Block credential stealing from the Windows local security = Disabled
- Block process creations originating from PSExec and WMI commands = Disabled
- Controlled Folder Access = Disabled
ADMIN: HIDE SECURITY CENTER = Visible
### The MAX Protection Level applies the other settings as follows:
BASIC DEFENDER SETTINGS
- PUA Protection = ON
- Cloud Protection Level = Block
- Cloud Check Time Limit = 60s
ADMIN: SMARTSCREEN
- For Explorer = Block
- For Edge (not Chromium) = Block
- For Internet Explorer = Block
EXPLOIT GUARD ---> All settings set to ON
ADMIN: HIDE SECURITY CENTER = Hidden
**************************
TAMPER PROTECTION **
**************************
The below settings cannot be disabled while Defender Tamper Protection is enabled:
- Behavior Monitoring = ON
- Scan all downloaded files and attachments = ON
- Script Scanning = ON
***********************************************
SOME NOTES ABOUT ASR RULES AND CFA **
***********************************************
## Block credential stealing from the Windows local security
This rule can make a lot of noise in the Defender Security Log. Most of the blocked events are usually false positives when the legal application tries to enumerate running processes and attempts to open them with exhaustive permissions. These applications can be excluded by using <Manage ASR Exclusions>.
## Block executable files from running unless they meet a prevalence, age, or trusted list criteria
This rule is strong prevention against Polymorphic malware (EXE, DLL, etc.), but one has to accept the higher rate of false positives for application installers/updaters. The prevalence is related to 1000 machines and age to 24 hours. The trusted list criteria are managed by Microsoft. The rule can recognize the executable as suspicious only when Defender can connect to the Microsoft cloud.
From my experience, most executable files blocked by this rule (application installers/updaters) are allowed after 48 hours. Anyway, some applications with a very low prevalence can be blocked for several days, and the users usually do not know how to unblock them.
Please note: It is useless to add exclusions for this rule. The proper procedure to unblock files is as follows:
- Set the rule temporarily to Audit.
- Run the installer/updater > install/update application > run the installed/updated application.
- Set the rule to ON - Defender is smart enough to allow running the application.
## Block process creations originating from PSExec and WMI commands
This rule is important because malware can try to bypass the parent-child checking by using WMI. So, other ASR rules based on checking child processes will fail. On some computers, the WMI can be used by the computer firmware so it is better to set initially this ASR rule to Audit.
## Controlled Folder Access
It can be very useful, but only after excluding the applications that need to access protected folders and applications that need to access the protected disk areas. The second group can include backup applications, disk management applications, and disk optimization programs. It is recommended to set initially this rule to Audit.
Post updated.