The other solution is creating the new Admin account (at least one Admin account is required) and change the type of the old Admin account to SUA. That can be often a more precise and quick way.... When I created SUA approx. a year ago I neglected to move those to SUA and it made H_C more complicated than need be. I solved this not long ago simply by moving everything to SUA. Voila! Problem solved.
I am now using Windows10_Recommended_Enhanced Profile as well.
Hard_Configurator - Windows Hardening Configurator
- Thread starter Andy Ful
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Let me get this straight. Apart from the administrator account I have.The other solution is creating the new Admin account (at least one Admin account is required) and change the type of the old Admin account to SUA. That can be often a more precise and quick way.
I have to create another administrator account and then change it to SUA?
No. It is better to convert the old one. Furthermore, you cannot convert both.Let me get this straight. Apart from the administrator account I have.
I have to create another administrator account and then change it to SUA?
D
Deleted member 178
Best practice "a la Umbra" :
1- local admin account (for the "admin" of the house) for maintenance tasks.
2- SUA (with MS account or not) for all the house members including the admin; made for daily usage.
3- Guest account for friends passing by.
1- local admin account (for the "admin" of the house) for maintenance tasks.
2- SUA (with MS account or not) for all the house members including the admin; made for daily usage.
3- Guest account for friends passing by.
@Andy Ful - Can you explain this for me please? Is this going to interfere with Windows updates?
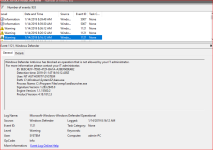
I get the feeling sometimes that while EV shows various WD blocks, the operations actually proceed.
I get the feeling sometimes that while EV shows various WD blocks, the operations actually proceed.
Attachments
You activated the ASR rule "Block credential stealing from the Windows local security authority subsystem (lsass.exe)" (it is not enabled in Defender High settings). This rule does not block the process, but only forbid the access to lsass.exe. From your post I can see that such access is forbidden for Windows Setup Remediations Service in Windows 10:@Andy Ful - Can you explain this for me please? Is this going to interfere with Windows updates?
I get the feeling sometimes that while EV shows various WD blocks, the operations actually proceed.
https://support.microsoft.com/en-us...ions-1507-1511-1607-1703-1709-and-1803-for-up
What are Sedsvc.exe, Sedlauncher.exe Files and REMPL Folder in Windows 10? - AskVG
This is the legal M$ soft, which includes reliability improvements to Windows Update Service components in Windows 10, for versions up to 1803 (it is absent on ver. 1809).
If you have any problem with Windows Updates, then disable that ASR rule.
D
Deleted member 178
This lsass.exe rule is one of the most important, i wont disable it.
Generally, disabling that rule is not recommended. It can be especially important in organizations and businesses, where the malware can attack the user from the local network with administrative rights. Next it can attack lsass.exe to steal credentials, admin passwords, etc.
With H_C settings, the malware originated by the user actions can hardly elevate, because it will be first blocked by H_C settings (default-deny). So, in this special configuration in the home environment, disabling that ASR rule can be more beneficial than the danger of broken updates.
With H_C settings, the malware originated by the user actions can hardly elevate, because it will be first blocked by H_C settings (default-deny). So, in this special configuration in the home environment, disabling that ASR rule can be more beneficial than the danger of broken updates.
You activated the ASR rule "Block credential stealing from the Windows local security authority subsystem (lsass.exe)" (it is not enabled in Defender High settings). This rule does not block the process, but only forbid the access to lsass.exe. From your post I can see that such access is forbidden for Windows Setup Remediations Service in Windows 10:
https://support.microsoft.com/en-us...ions-1507-1511-1607-1703-1709-and-1803-for-up
What are Sedsvc.exe, Sedlauncher.exe Files and REMPL Folder in Windows 10? - AskVG
This is the legal M$ soft, which includes reliability improvements to Windows Update Service components in Windows 10, for versions up to 1803 (it is absent on ver. 1809).
If you have any problem with Windows Updates, then disable that ASR rule.
This helps to expand my understanding. I am still on 1803 and have not been offered the latest feature update. If it is offered and I encounter problems then I will disable. Thanks!
@Umbra - I keep it enabled until I can verify it is blocking a feature update.
It is not very probable, but may happen if the Update will be buggy....
@Umbra - I keep it enabled until I can verify it is blocking a feature update.
is there a default/recommended/best settings using for non advanced user with cf
What is a cf?is there a default/recommended/best settings using for non advanced user with cf
What is a cf?
I think he means Comodo Firewall.
That depends on the CF settings. You can set CF in such a way, that you do not need H_C. But, such CF setup can also break your system or updates on Windows 10.
I found the lsass rule to be the most problematic of all the ASR rules. It conflicted with some of my software.You activated the ASR rule "Block credential stealing from the Windows local security authority subsystem (lsass.exe)" (it is not enabled in Defender High settings). This rule does not block the process, but only forbid the access to lsass.exe. From your post I can see that such access is forbidden for Windows Setup Remediations Service in Windows 10:
https://support.microsoft.com/en-us...ions-1507-1511-1607-1703-1709-and-1803-for-up
What are Sedsvc.exe, Sedlauncher.exe Files and REMPL Folder in Windows 10? - AskVG
This is the legal M$ soft, which includes reliability improvements to Windows Update Service components in Windows 10, for versions up to 1803 (it is absent on ver. 1809).
If you have any problem with Windows Updates, then disable that ASR rule.
D
Deleted member 178
No there is not, all depends of the user's needs, default settings are useless, users must configure everything themselves to get serious protection with Comodo, hoping the disappearing rules bug doesn't show up...is there a default/recommended/best settings using for non advanced user with cf
Are you running CFW at CruelSister settings?is there a default/recommended/best settings using for non advanced user with cf
That depends on the CF settings. You can set CF in such a way, that you do not need H_C. But, such CF setup can also break your system or updates.
Those two in combo seems like it would be asking for problems.
H_C is probably compatible with CF in any settings, but CF can be configured in a similar way as H_C. The H_C default-deny settings are simply more compatible with Windows and Windows Updates.Those two in combo seems like it would be asking for problems.
You may also like...
-
-
FAI Tells It Like It Is - Microsoft's Wonky Default Deny Roadmaps, Users as Guinea Pigs, "Dilemmas and Paradoxes," and Why SRP Remains King
- Started by ForgottenSeer 114717
- Replies: 44
-
Microsoft testing Windows 11 batch file security improvements
- Started by Parkinsond
- Replies: 0
-
Malware News CrySome RAT : An Advanced Persistent .NET Remote Access Trojan
- Started by Khushal
- Replies: 3
-