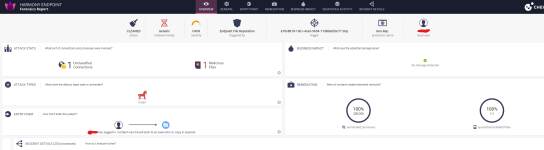
One of the detections (gen.win.processhollowing) seems to be a generic detection for code injection via process hollowing (run process -> pause process -> replace portion of process memory with malicious code -> resume process). Seeing a process hollowing detection by behavioural blocking is quite unusual, many AVs are totally blind to that. Some can catch initial scripts early by using local emulator in memory but the emulator doesn’t have all day, it’s only got milliseconds and by using a JS with useless math operations and malicious actions somewhere in the middle, local emulator can easily be bypassed (unlike full blown emulation in the cloud that has the time).
This is why it has become attackers favourite. Quite a lot of malware can be blocked by this detection.
So when Check Point was saying that fileless malware is not a problem for behavioural guard, they’ve not been joking.