NoVirusThanks OSArmor
- Thread starter Evjl's Rain
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
F
ForgottenSeer 823865
It is a different beast, If you were comfortable and liked to create custom rules in v3, then v4 is for you even if you have to learn its more sophisticated rules editor. It is the most efficient one I ever came across for an anti-exe.Thanks Umbra! I've been running EXE Radar Pro v.3.1 for a long time, and I'm thinking about upgrading to v.4. Anything I should know regarding v.4?
Anyway v3 is abandoned, sooner you jump to v4, better it is.
I checked this 3-4 months ago and then 9 out of 10 was KMS. Good to see other malwares have taken over some spots
OS Armor has not yet included Edge-chromium in the Exploit protection.
I added one custom block rule in OS_Armor (basically don't allowing msedge.exe to start other executables):
[%PARENTPROCESS%: *\msedge.exe] [%PROCESS%: *\*.exe]
And added an allow exception for msedge.exe itself, so broker process can load spawned GPU and renderer msedge subprocesses:
[%PARENTPROCESS%: *\msedge.exe] [%PROCESS%: *\msedge.exe] [%FILESIGNER%: Microsoft*]
I added one custom block rule in OS_Armor (basically don't allowing msedge.exe to start other executables):
[%PARENTPROCESS%: *\msedge.exe] [%PROCESS%: *\*.exe]
And added an allow exception for msedge.exe itself, so broker process can load spawned GPU and renderer msedge subprocesses:
[%PARENTPROCESS%: *\msedge.exe] [%PROCESS%: *\msedge.exe] [%FILESIGNER%: Microsoft*]
Whenever I need software for Windows, I can usually find a free or open-source program, even advanced photo and video editors like PhotoDemon and AVIDemux or sophisticated file tools like PeaZip.I've been tempted to use cracked/pirated software but always had visions of something nasty setting up housekeeping on my machine. So, I do something similar. If I really think I need a piece of software, I cruise the many giveaway sites looking for it. Often, I find something similar, play with it for a while, and discover I didn't need it after all.
Hello,
I'm wondering if NVT OSA is still in development because there ar no more update since March 24, 2019
I'm wondering if NVT OSA is still in development because there ar no more update since March 24, 2019
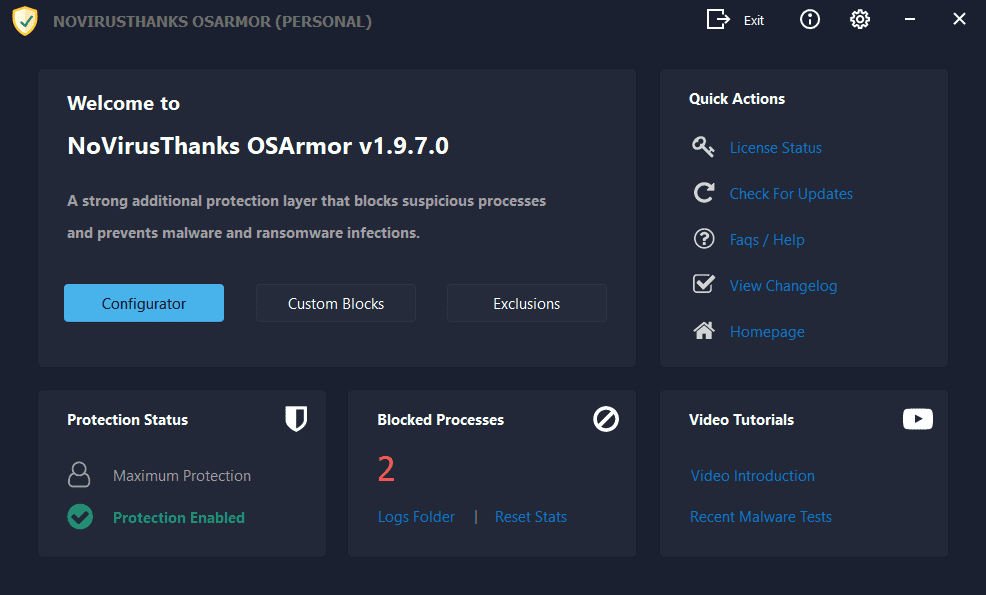
Prevent Malware & Ransomware Infections on Windows PC | OSArmor
OSArmor is a Windows application that focuses on preventing malware and ransomware infections by blocking malware delivery methods and suspicious processes behaviors.
www.novirusthanks.org
Hello,
I'm wondering if NVT OSA is still in development because there ar no more update since March 24, 2019
Prevent Malware & Ransomware Infections on Windows PC | OSArmor
OSArmor is a Windows application that focuses on preventing malware and ransomware infections by blocking malware delivery methods and suspicious processes behaviors.www.novirusthanks.org
I also participated in the development of OSA (Andreas).
Then after a certain period there were differences of views.
The driving distance from my city to the NVT headquarters is about 170 km.
Often I say "once or another I go to Perugia and inquire" but then for one reason or another ..........
Does it need any update?Hello,
I'm wondering if NVT OSA is still in development because there ar no more update since March 24, 2019
Prevent Malware & Ransomware Infections on Windows PC | OSArmor
OSArmor is a Windows application that focuses on preventing malware and ransomware infections by blocking malware delivery methods and suspicious processes behaviors.www.novirusthanks.org
F
ForgottenSeer 823865
Andreas is probably on some business projects as usually, freewares can't expect to be on the fast track.Hello,
I'm wondering if NVT OSA is still in development because there ar no more update since March 24, 2019
Prevent Malware & Ransomware Infections on Windows PC | OSArmor
OSArmor is a Windows application that focuses on preventing malware and ransomware infections by blocking malware delivery methods and suspicious processes behaviors.www.novirusthanks.org
no, 1909 don't have any significant changes over 1903. Also, LOLbins don't change path and even if they change, you just create custom rules.Does it need any update?
I also participated in the development of OSA (Andreas).
Then after a certain period there were differences of views.
The driving distance from my city to the NVT headquarters is about 170 km.
Often I say "once or another I go to Perugia and inquire" but then for one reason or another ..........
Does it need any update?
Thanks @Sampei Nihira , @Azure & @Umbra for for these detailsAndreas is probably on some business projects as usually, freewares can't expect to be on the fast track.
no, 1909 don't have any significant changes over 1903. Also, LOLbins don't change path and even if they change, you just create custom rules.
I used OSA for about 2 yr. but decided to replace it with Hard Configurator because H_C's developer, @Andy Ful (and others with the project) is very active here and responds to questions and concerns. I'm not an expert, but I'd say an average home user is just as protected with Hard Configurator.Hello,
I'm wondering if NVT OSA is still in development because there ar no more update since March 24, 2019
Prevent Malware & Ransomware Infections on Windows PC | OSArmor
OSArmor is a Windows application that focuses on preventing malware and ransomware infections by blocking malware delivery methods and suspicious processes behaviors.www.novirusthanks.org
This is probably a much repeated question....but does OS Armour do the same job as Voodooshield ?
I use Voodooshield but have never tried OS Armour.
I use Voodooshield but have never tried OS Armour.
OSA is a Basic Anti-Exploit that can easily gel with VoodooShield.This is probably a much repeated question....but does OS Armour do the same job as Voodooshield ?
I use Voodooshield but have never tried OS Armour.
F
ForgottenSeer 823865
NO ! OSA is an anti Post-Exploitation software. Unless an apps can monitor and prevent memory attacks, it can't be categorized as an Anti-Exploit (whatever marketing shenanigans a vendor may say).OSA is a Basic Anti-Exploit
OSA is a Basic Anti-Exploit that can easily gel with VoodooShield.
So wich tool is better to support a Main AV under Win 10 1909?
OSA at default settings is much less in-your-face. You probably will not even notice it is there. However, Voodoo at default settings is much stronger protection. It all depends on what kind of protection you are trying to achieve, and how you will configure the products.So wich tool is better to support a Main AV under Windows 10 1909?
OSA has basic anti-exploit protection that analyzes parent processes and child processes blocking exploit payloads.
OSA is not intended to block strictly the exploits, especially memory exploits. But, it can block several exploit delivery methods, and also several payload delivery methods. It can also block the execution of many payloads. But in the default settings, many payloads can pass by the OSA protection.
So, OSA has anti-exploit prevention abilities. Both on the pre-execution and post-execution levels.
So, OSA has anti-exploit prevention abilities. Both on the pre-execution and post-execution levels.
Last edited:
F
ForgottenSeer 823865
this is not anti-exploit, this is default-deny.OSA has basic anti-exploit protection that analyzes parent processes and child processes blocking exploit payloads.
To me, delivery is not exploitation, exploitation is the act of abusing a vulnerability. Eternal Blue is an kernel exploit, it abuse a vulnerability.But, it can block several exploit delivery methods, and also several payload delivery methods. .
Default-deny tools (anti-exe, etc...) don't prevent exploitation of vulnerabilities.
The only thing they can do, is they will prevent (as you said) either delivery of the exploit or the post-exploitation part of the attack chain (like abusing rundll32.exe, etc....)
Anti-Exploit software are HMPA, MBAE, Windows 10 Exploit Protection and some components in suites, which can prevent exploitation of vulnerabilities, which occurs most of the time via memory attacks.
There is no such thing as "basic anti-exploit", this is just marketing shenanigans made by some vendors to make their solutions more appealing. And many fall for it and parrot it across boards, so unaware people believe that your so-called basic anti-exploit (aka Default-Deny) will protect them from in-memory REAL exploits/attacks.
this is not anti-exploit, this is default-deny.
To me, delivery is not exploitation, exploitation is the act of abusing a vulnerability. Eternal Blue is an kernel exploit, it abuse a vulnerability.
Default-deny tools (anti-exe, etc...) don't prevent exploitation of vulnerabilities.
The only thing they can do, is they will prevent (as you said) either delivery of the exploit or the post-exploitation part of the attack chain (like abusing rundll32.exe, etc....)
Anti-Exploit software are HMPA, MBAE, Windows 10 Exploit Protection and some components in suites, which can prevent exploitation of vulnerabilities, which occurs most of the time via memory attacks.
There is no such thing as "basic anti-exploit", this is just marketing shenanigans made by some vendors to make their solutions more appealing. And many fall for it and parrot it across boards, so unaware people believe that your so-called basic anti-exploit (aka Default-Deny) will protect them from in-memory REAL exploits/attacks.
The DEP test of the Exploit Test Tool (HPA) is blocked by OSA.
This is a memory test.
.......This test allocates a piece of non-executable memory on the heap and copies shellcode to start calc.exe to this memory. Then it jumps to that shellcode. This will trigger a DEP exception which, will be intercepted......
However I understand what you mean, I also don't consider OSA a pure Anti-Exploit.
You may also like...
-
Security News AI Codex Exploits Samsung TV Driver Flaw to Gain Root Access
- Started by Brownie2019
- Replies: 1
-
On Sale! Emsisoft Anti-Malware 2026 - 1PC, 1Yr, $ 21.36
- Started by Brownie2019
- Replies: 8
-
Malware News CrySome RAT : An Advanced Persistent .NET Remote Access Trojan
- Started by Khushal
- Replies: 3
-
Serious Discussion BYOVD attacks, prevention, and Core Isolation.
- Started by Andy Ful
- Replies: 13
-
On Sale! Avast Premium Security 1 Device 1 Year 9.99€
- Started by Brownie2019
- Replies: 0
