- Jun 7, 2020
- 11
Hello Team,
Could you please help me to decrypt all files on my personal laptop.
1. My laptop is attacked by Ransomware i.e. .pezi , below is information , also text file demanding $490 ransome.
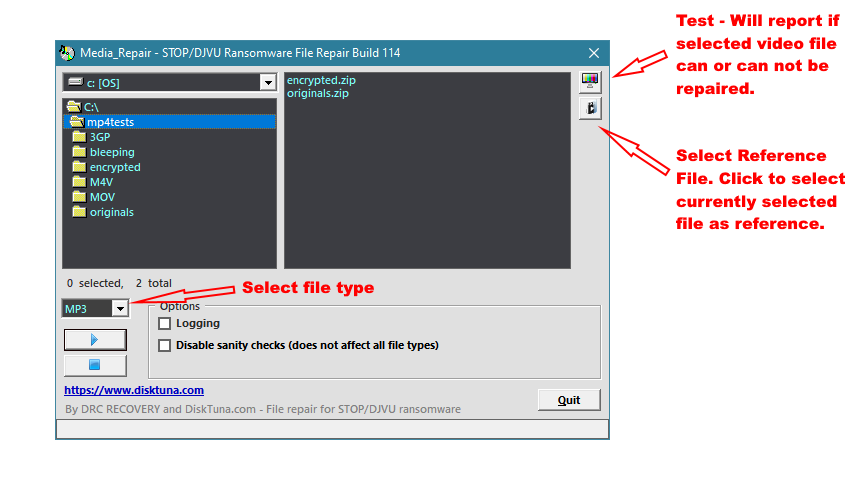
2. I have already tried steps given in one of your article - How to remove PEZI ransomware (Virus Removal Guide) - but didn't help.
3. Reason is - encryption is done using ONLINE key so EMSISOFT is unable to decrypt files.
4. this attack has happened on 1st of June 2020.
Please help me to recover/decrypt al files , Thank you much in advance.
Could you please help me to decrypt all files on my personal laptop.
1. My laptop is attacked by Ransomware i.e. .pezi , below is information , also text file demanding $490 ransome.
2. I have already tried steps given in one of your article - How to remove PEZI ransomware (Virus Removal Guide) - but didn't help.
3. Reason is - encryption is done using ONLINE key so EMSISOFT is unable to decrypt files.
4. this attack has happened on 1st of June 2020.
Please help me to recover/decrypt al files , Thank you much in advance.
| Contact | restoreadmin@firemail.cc, helpmanager@mail.ch |
| Ransom amount | $490/$980 in Bitcoins |