OK. Noticed UAC Virtualization last night. Any plain and simple benefit to enabling UACV?
App Review Ransom Buster by Trend Micro
- Thread starter cruelsister
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
It is advised to take all reviews with a grain of salt. In extreme cases some reviews use dramatization for entertainment purposes.
The below article has a good explanation:OK. Noticed UAC Virtualization last night. Any plain and simple benefit to enabling UACV?
Tales of Application Compatibility Weirdness – Demystifying UAC Virtualization
The UACV is only for compatibility with old applications that try to save data, config files, etc. in Program Files or Windows folders (UAC protected) or store some data in the HKLM registry hive, etc.. Such actions would fail due to insufficient access rights. There is no need to turn ON UACV If you do not use such old applications.
Some users complained that the malware could use UACV for hiding in unexpected disk/registry locations but I did not tested it. For example, some tools could miss malware entries in the registry virtual store:
HKU\<User SID>_Classes\VirtualStore\Machine\Software
Andy Ful wrote:
"But generally, the real danger is when using an Admin account."
Is there an add-on or software to easily switch from admin rights at any time?
"But generally, the real danger is when using an Admin account."
Is there an add-on or software to easily switch from admin rights at any time?
Yes. Windows built-in Software Restrictions Policies.Andy Ful wrote:
"But generally, the real danger is when using an Admin account."
Is there an add-on or software to easily switch from admin rights at any time?
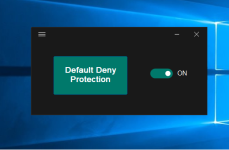
You can easily switch Default Deny Security Level to Unrestricted like I do in Hard_Configurator using SwitchDefaultDeny utility (see attachment). It works only with Hard_Configurator, but it is easy to make a GUI tool that can do the same for the standard SRP.
Also one can use Simple Software Restriction Policies tool, that has switch ON/OF option.
Attachments
Last edited:
Please, look at my previous post which I edited, so you could miss it.- addon or software.. button, Off/On switch, any?
In fact, SRP on admin account do much more. If SRP are off, then you have the normal admin account. If SRP are ON, then new executables are blocked by default, except when run with admin rights or added to the white list.
The downside of the above (for many users) is adding the new applications to the white list when they installed untypically (outside Program Files) or use the executable image to execute in the Temp folder (wrapped launchers).
The downside of the above (for many users) is adding the new applications to the white list when they installed untypically (outside Program Files) or use the executable image to execute in the Temp folder (wrapped launchers).
Last edited:
The UACV is only for compatibility with old applications that try to save data, config files, etc. in Program Files or Windows folders (UAC protected) or store some data in the HKLM registry hive, etc.. Such actions would fail due to insufficient access rights. There is no need to turn ON UACV If you do not use such old applications.
Thanks.
"Also one can use Simple Software Restriction Policies tool, that has switch ON/OF option."
Thank you Andy Ful for this software!
thewindowsclub.com: Simple Software Restriction Policy is a security add-on for Windows
ghacks.net: Lock-down your Windows system with Simple Software-restriction Policy - gHacks Tech News
bleepingcomputer.com: Is Simple Software-Restriction Policy safe? - General Security
"Heads up! ZenMate Web Firewall blocked this site from loading as it's classified under Security Threats.
Simple Software-restriction Policy "
- I've clicked "Continue anyway": (too cause TrafficLight says: "Safe page")
-so I could read sourceforge.net: Simple Software-restriction Policy
Thank you Andy Ful for this software!
thewindowsclub.com: Simple Software Restriction Policy is a security add-on for Windows
ghacks.net: Lock-down your Windows system with Simple Software-restriction Policy - gHacks Tech News
bleepingcomputer.com: Is Simple Software-Restriction Policy safe? - General Security
"Heads up! ZenMate Web Firewall blocked this site from loading as it's classified under Security Threats.
Simple Software-restriction Policy "
- I've clicked "Continue anyway": (too cause TrafficLight says: "Safe page")
-so I could read sourceforge.net: Simple Software-restriction Policy
Last edited:
Please, learn about SRP first, because this handy tool will allow you to blacklist anything you want. If you will do something wrong then you will not be happy....
-so I could read sourceforge.net: Simple Software-restriction Policy
You may also like...
-
App Review Trend Micro Maximum Security 2025
- Started by Shadowra
- Replies: 83
-
-
-
-