- Jun 26, 2019
- 75
Sandboxie should be avoided in 2019 and above.
1. Sandboxie messes with the memory of processes belonging to other people's software.
First of all, messing with memory of other people's software can introduce additional vulnerabilities in other people's software. There's people out there who have a good track record with finding (and exploiting) vulnerabilities which are introduced by security software injecting code for one reason or another.
Second of all, messing with the memory of other people's software will tarnish code integrity defenses. Code integrity is there to validate that code is as it should be and hasn't been modified, but thanks to Sandboxie, those features can go flying out the window. You can trust Sandboxie to hook away at its own discretion, destroying effective use of code integrity to ensure that no one who shouldn't be messing with things in certain areas.
Third of all, messing with the memory of other people's software... breaks other people's software. Developers have enough on their plate without having to clean up Sandboxie's mess. People report compatibility issues even though it isn't the developers fault, but Sandboxie's fault. It's not acceptable given Sandboxie doesn't have to behave in the way it's behaving: there are modern model designs for sandbox systems which they are voluntarily deciding to ignore and not bother implementing.
2. Sandboxie has a lot of incompatibility problems.
Sandboxie is constantly forcing people to use beta versions for quicker compatibility patches, even though using a beta channel is not a good idea for security. General stability and security may differ when using a beta product compared to a release product. Beta products are in beta because they haven't been tested/vetted as much and are pending normal release until they can prove themselves to be stable and secure enough.
3. Sandboxie does not have a proper channel for reporting critical vulnerabilities.
There's someone on the forums asking for assistance in reporting a potential critical vulnerability. The claims are that the vulnerability, when exploited, can result in escalation of privileges. Of course, it took several days before an official employee could even reply to the thread.
Here's what some of the forum members over there have to say about Sandboxie.
 community.sophos.com
community.sophos.com
 community.sophos.com
community.sophos.com
Well, there we have it... two Sandboxie supporters themselves had some interesting things to say.
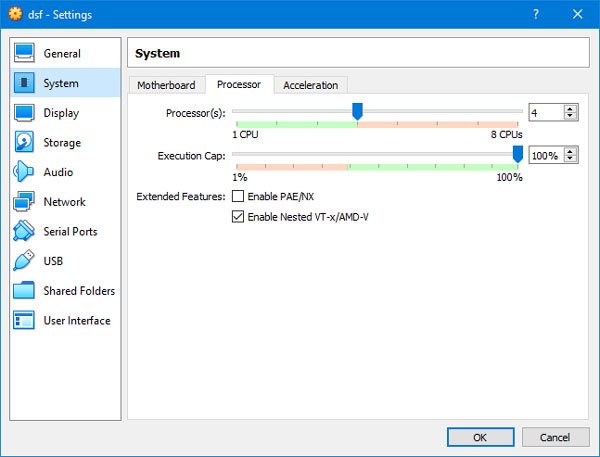
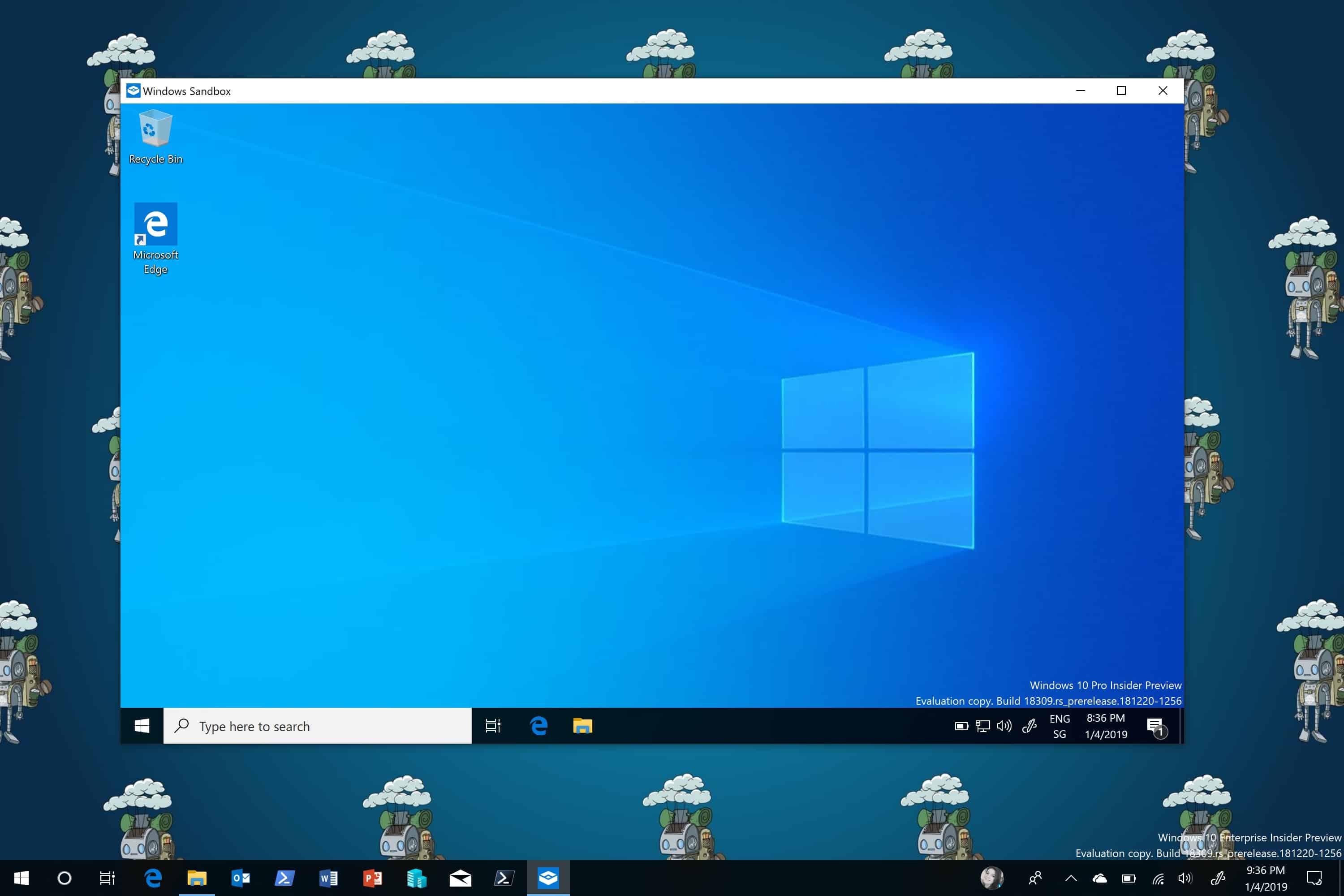
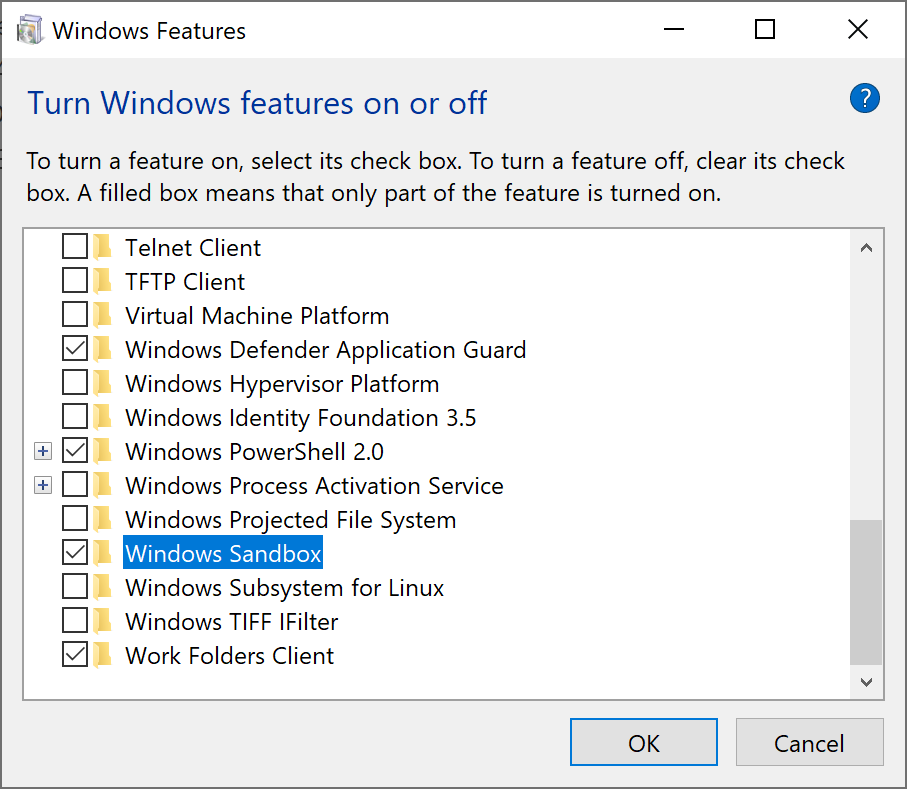
Windows 10 Professional (and above) users can switch to Microsoft Windows Sandbox - it works like a charm and doesn't have the above mentioned caveats - which is made by people who are willing to design a sandbox system that is robust and relatively secure. For anyone that is unaware, Windows 10's new sandbox feature is powered by Hyper-V (enterprise-grade virtual machine software).
You can find more information about the Windows 10 Sandbox here:
 techcommunity.microsoft.com
techcommunity.microsoft.com
Windows 10's Sandbox doesn't need to be updated on a daily basis to maintain compatibility, doesn't jeopardize your security to make geek users happy, and doesn't provide redundant and bloatware functionality that only a small portion of users would have genuinely needed to stay safe.
If you're not into Windows 10 Sandbox or you're not a Windows 10 Professional (or above) user, then look into ReHIPS, also much safer and robust than Sandboxie.
Thanks for reading. You know what to do if you have Sandboxie installed right now (*hint* Control Panel -> Uninstall programs -> Sandboxie -> Uninstall *hint*).
1. Sandboxie messes with the memory of processes belonging to other people's software.
First of all, messing with memory of other people's software can introduce additional vulnerabilities in other people's software. There's people out there who have a good track record with finding (and exploiting) vulnerabilities which are introduced by security software injecting code for one reason or another.
Second of all, messing with the memory of other people's software will tarnish code integrity defenses. Code integrity is there to validate that code is as it should be and hasn't been modified, but thanks to Sandboxie, those features can go flying out the window. You can trust Sandboxie to hook away at its own discretion, destroying effective use of code integrity to ensure that no one who shouldn't be messing with things in certain areas.
Third of all, messing with the memory of other people's software... breaks other people's software. Developers have enough on their plate without having to clean up Sandboxie's mess. People report compatibility issues even though it isn't the developers fault, but Sandboxie's fault. It's not acceptable given Sandboxie doesn't have to behave in the way it's behaving: there are modern model designs for sandbox systems which they are voluntarily deciding to ignore and not bother implementing.
2. Sandboxie has a lot of incompatibility problems.
Sandboxie is constantly forcing people to use beta versions for quicker compatibility patches, even though using a beta channel is not a good idea for security. General stability and security may differ when using a beta product compared to a release product. Beta products are in beta because they haven't been tested/vetted as much and are pending normal release until they can prove themselves to be stable and secure enough.
3. Sandboxie does not have a proper channel for reporting critical vulnerabilities.
There's someone on the forums asking for assistance in reporting a potential critical vulnerability. The claims are that the vulnerability, when exploited, can result in escalation of privileges. Of course, it took several days before an official employee could even reply to the thread.
Here's what some of the forum members over there have to say about Sandboxie.
Just go ahead and post it here, so at least the few of us that are left can know what to look out for. Sophos won't do anything about it. Doubtful they even could.
Sophos ID - Login
What devs? Do you see any Sophos devs here? It took them months to recover from their own self-inflicted DDoS attack. The old forums are gone forever and we are left with this POS. And the buy links are still "in maintenance" after more than 2 months.
Since Sophos took over, they have done the absolute minimum required to keep Sandboxie barely running in Win 10 while they collected payments. There is a long list of problems that are being "looked in to" but not fixed.
I'm switching to the cracked version to get around this licensing incompetence. The crackers at least have some devs working. They maybe can do something about vul. if you post the details here assuming it is real.
Sophos ID - Login
Well, there we have it... two Sandboxie supporters themselves had some interesting things to say.
Windows 10 Professional (and above) users can switch to Microsoft Windows Sandbox - it works like a charm and doesn't have the above mentioned caveats - which is made by people who are willing to design a sandbox system that is robust and relatively secure. For anyone that is unaware, Windows 10's new sandbox feature is powered by Hyper-V (enterprise-grade virtual machine software).
You can find more information about the Windows 10 Sandbox here:
Windows Sandbox
Windows Sandbox is a new lightweight desktop environment tailored for safely running applications in isolation. How many times have you downloaded an executable file, but were afraid to run it? Have you ever been in a situation which required a clean installation of Windows, but didn’t want to...
Windows 10's Sandbox doesn't need to be updated on a daily basis to maintain compatibility, doesn't jeopardize your security to make geek users happy, and doesn't provide redundant and bloatware functionality that only a small portion of users would have genuinely needed to stay safe.
If you're not into Windows 10 Sandbox or you're not a Windows 10 Professional (or above) user, then look into ReHIPS, also much safer and robust than Sandboxie.
Thanks for reading. You know what to do if you have Sandboxie installed right now (*hint* Control Panel -> Uninstall programs -> Sandboxie -> Uninstall *hint*).