Hi,
I have a few questions.
So if i understand correctly:
Example:
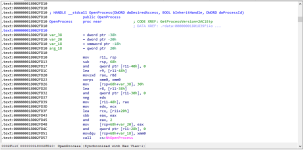
OpenProcess is a function Win32 API (wrapper?) that calls ntdll.dll (NATIVE API) which in turn calls the corresponding function in the kernel right? what function does it call in the kernel?
the prefix Nt (Example: NtOpenProcess) and Zw (Example: ZwOpenProcess) are aliases?
NtOpenProcess / ZwOpenProcess is just usermode?
what function need to use in the kernel?
PS: sry for bad english >.>
I have a few questions.
So if i understand correctly:
Example:
OpenProcess is a function Win32 API (wrapper?) that calls ntdll.dll (NATIVE API) which in turn calls the corresponding function in the kernel right? what function does it call in the kernel?
the prefix Nt (Example: NtOpenProcess) and Zw (Example: ZwOpenProcess) are aliases?
NtOpenProcess / ZwOpenProcess is just usermode?
what function need to use in the kernel?
PS: sry for bad english >.>