- May 4, 2019
- 801
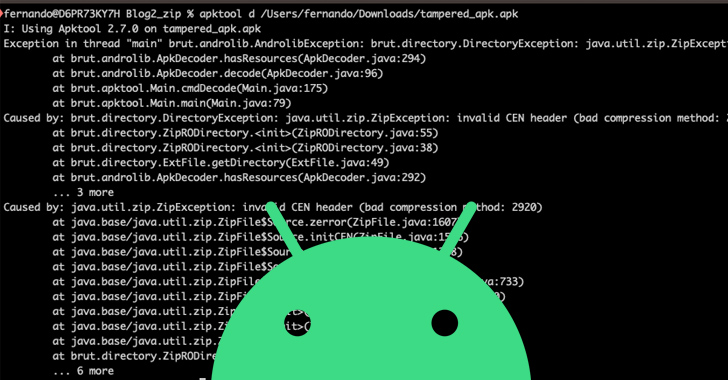
Threat actors are using Android Package (APK) files with unknown or unsupported compression methods to elude malware analysis.
That's according to findings from Zimperium, which found 3,300 artifacts leveraging such compression algorithms in the wild. 71 of the identified samples can be loaded on the operating system without any problems.
There is no evidence that the apps were available on the Google Play Store at any point in time, indicating that the apps were distributed through other means, typically via untrusted app stores or social engineering to trick the victims into sideloading them.
Thousands of Android Malware Apps Using Stealthy APK Compression to Evade Detection
Hackers are using sneaky compression methods in Android APK files to evade malware detection

