L
LabZero
Thread author
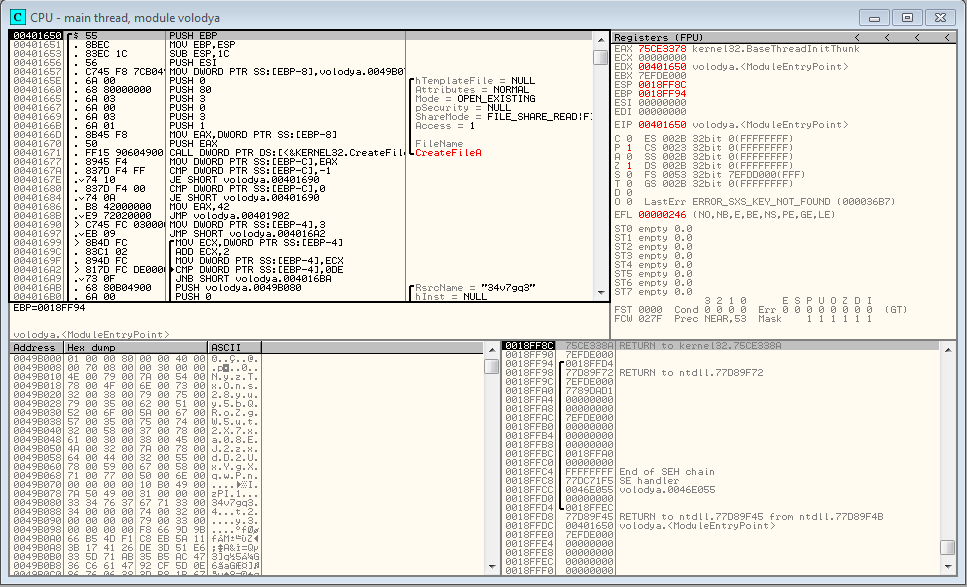
OllyDbg: it is a debugger that offers high performance in the context of dynamic analysis.
When you do not have the source code of the malware,then it will be necessary
to do an analysis binary file (executable file), where the static analysis
using the disassembler has not provided enough information you need to use
a debugger, for power controlling the execution of the low level code (assembly)
The assembly is a low-level language, similar to the machine language.
In machine language, the bitstreams specifications are associated with
basic instructions.
Assembly language associates of mnemonic instructions these opcodes.
In this screenshot i loaded the malware volodya ( .exe) and i started
debugging for elementary example :
When you do not have the source code of the malware,then it will be necessary
to do an analysis binary file (executable file), where the static analysis
using the disassembler has not provided enough information you need to use
a debugger, for power controlling the execution of the low level code (assembly)
The assembly is a low-level language, similar to the machine language.
In machine language, the bitstreams specifications are associated with
basic instructions.
Assembly language associates of mnemonic instructions these opcodes.
In this screenshot i loaded the malware volodya ( .exe) and i started
debugging for elementary example :
Last edited by a moderator: