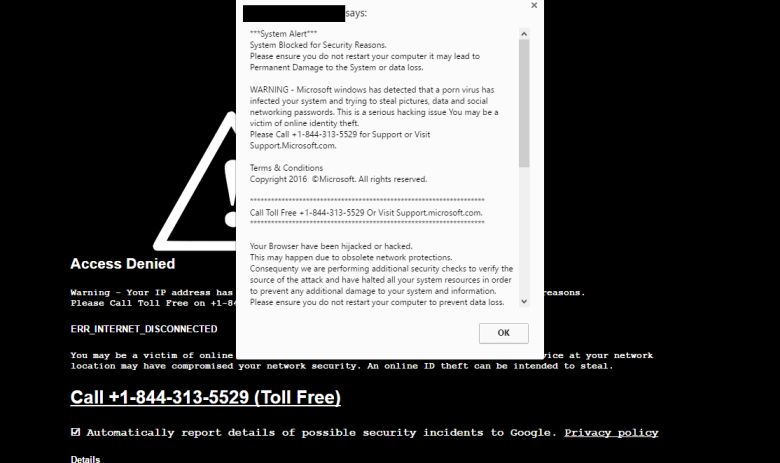
If you are seeing a Cyber Security Warning pop-up, asking you to call a support number, then your computer is infected with an adware program (Rogue.Tech-Support-Scam).
Please ignore these “Cyber Security Warning” alerts and do not call the displayed number because these pop-ups are a scam.
The Cyber Security Warning alert is shown in such a way as to trick the user into thinking their computer has crashed or that a virus has been detected on the computer. It does this to try and scare the infected user into calling one of the listed numbers in order to receive support. In reality, though, they will only be greeted with people who are trying to sell them unneeded support contracts and services.
The “Cyber Security Warning” pop-up ads are caused by a malicious program, which is typically bundled with other software that you can download for free from the Internet. When the malicious program is installed, an “Cyber Security Warning” alert will randomly pop-up. The “Cyber Security Warning” pop-up will have this message:
YOUR COMPUTER HAS BEEN LOCKED!
Your computer has been locked due to violation of the cyber security Act of 2016 (SCA 2016, A. 2077) of the United States Of America. Your IP address was used to visit websites containing Virus, Malware, Trojan and Key Logger. Your computer also contains files that has infected with virus. Spam-messages which contains virus were also sent from your computer.
The computer lock is aimed to stop your illegal activity.
To Unlock The Computer Please Call Support At +1-844-245-8878
And Ask For The Activation Key From Our Support Specialist.
Please call our support immediately otherwise all your Files & Data will be deleted from your computer.
You must call the support at +1-844-245-8878 to get your computer unlocked. Please do not attempt to shutdown or restart your computer, doing that may lead to data loss and identity theft as illegal activity has been initiated from your computer without your knowledge or consent, your PC may be infected by malware, thus you are violating the law of Neglectful Use of Personal Computer.
All suspicious files from your computer were transmitted to a special server and shall be used as evidences. Don’t try to corrupt any data or unblock your computer in an unauthorized way.
In order to resolve the situation in an above mentioned way you should call our support immediately. Please call support specialist at Toll Free +1-844-245-8878 And Get Your Computer Unlocked!
A Suspicious Connection Was Trying to Access Your Logins, Banking Details & Tracking Your Internet Activity.
Security Center & Firewall Services are Disabled, Error code 0x8007042c; .
Your TCP Connection Was Blocked by Your Firewall. Your Accounts May be Suspended Until You Take an Action.
Your Personal Information May Have Leaked. IMMEDIATE RESPONSE REQUIRED
Your Hard Disk May Have Trojan Virus! Please Do Not Try to Fix Manually, It May Crash Your Data.
Please Visit Your Nearest Service Center OR Call Help Desk+1-844-245-8878Customer Service: +1-844-245-8878 (TOLL-FREE)
PLEASE DO NOT SHUT DOWN OR RESTART YOUR COMPUTER, DOING THAT MAY LEAD TO DATA LOSS AND FAILIURE OF OPERATING SYSTEM , HENCE NON BOOTABLE SITUATION RESULTING COMPLETE DATA LOSS . CONTACT ADMINISTRATOR DEPARTMENT TO RESOLVE THE ISSUE.
*IMMEDIATE RESPONSE REQUIRED
Your System32 .net frame work file missing due to some harmful virus, Debug malware error 895-system 32.exe failure. Please contact network administration to rectify the issue. Please do not open internet browser for your security issue to avoid data corruption on your registery of your system. Please contact network administration department at +1-844-245-8878 (TOLL-FREE)
Virus Info: A Trojan horse, or Trojan, in computing is a non-self-replicating type of malware program containing malicious code that, when executed, carries out actions determied by the nature of the Trojan, typically causing loss or theft of data, and possible system harm. The term is derived from the story of the wooden horse used to trick defenders of Troy into taking concealed warriors into their city in ancient Greece, because computer Trojans often employ a form of social engineering, presenting themselves as routine, useful, or interesting in order to persuade victims to install them on their computers.
A Trojan often acts as a backdoor, contacting a controller which can then have unauthorized access to the affected computer. The Trojan and backdoors are not themselves easily detectable, but if they carry out significant computing or communications activity may cause the computer to run noticeably slowly. Malicious programs are classified as Trojans if they do not attempt to inject themselves into other files (computer virus) or otherwise propagate themselves (worm).
A computer may host a Trojan via a malicious program a user is duped into executing files or browsing internet. Please contact network administration department at +1-844-245-8878 (TOLL-FREE)
As you can see, this program was created for the sole purpose of displaying fake Windows alerts in order to scare you into purchasing remote support services. If you are infected with this program, please ignore any alerts that are displayed and do not call the displayed number. To remove this Trojan and any related software, please use the removal guide below.
How to remove Cyber Security Warning pop-ups (Removal Guide)
This page is a comprehensive guide which will remove Cyber Security Warning pop-ups from Windows.
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
To remove Cyber Security Warning pop-ups, follow these steps:
STEP 1: Scan your computer with AdwCleaner
STEP 2: Scan your computer with Malwarebytes Anti-Malware
STEP 3: Scan your computer with HitmanPro
(OPTIONAL) STEP 4: Scan your computer with Zemana AntiMalware
(OPTIONAL) STEP 5: Reset your browser to default settings
(OPTIONAL) Remove the Cyber Security Warning pop-ups
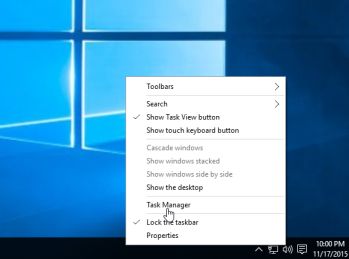
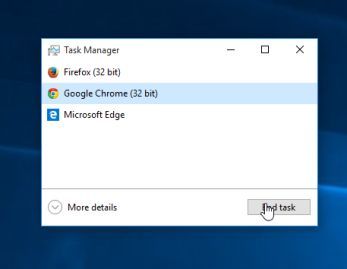
This step is needed if the malicious pop-ups will not allow you to close your browser.
- Open Task Manager by right-clicking the taskbar, and then clicking Start Task Manager. Alternatively to start the Windows Task Manager, you can press Ctrl+Alt+Del and click on Task Manager or simply press on Ctrl+Shift+Esc.
- Scroll through the list till you see your web browser’s process and left-click on it once so it becomes highlighted. Once you have selected the browser’s process, click on the End Task button as show in the picture below.
- Your browser window should now be closed. The next time you open your browser, do not allow the browser to open the last opened page.
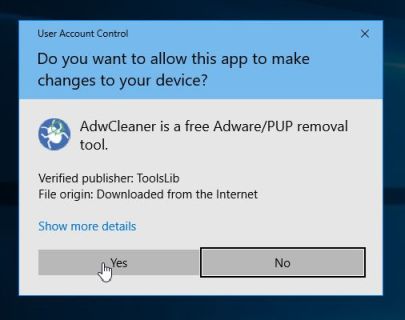
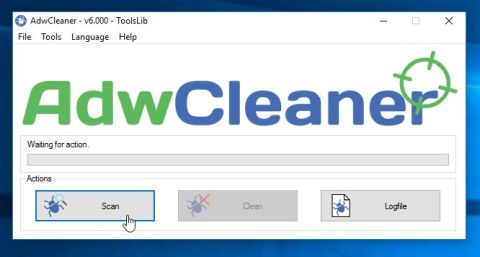
STEP 1: Scan your computer with AdwCleaner
AdwCleaner is a free utility, which will scan your computer and web browser for the Cyber Security Warning redirect.
- You can download AdwCleaner from the below link.
ADWCLEANER DOWNLOAD LINK (This link will open a new web page from where you can download “AdwCleaner”) - Before starting AdwCleaner, close your web browser, then double-click on the AdwCleaner icon.
If Windows prompts you as to whether or not you wish to run AdwCleaner, please allow it to run.
- When the AdwCleaner program will open, click on the “Scan” button as shown below.
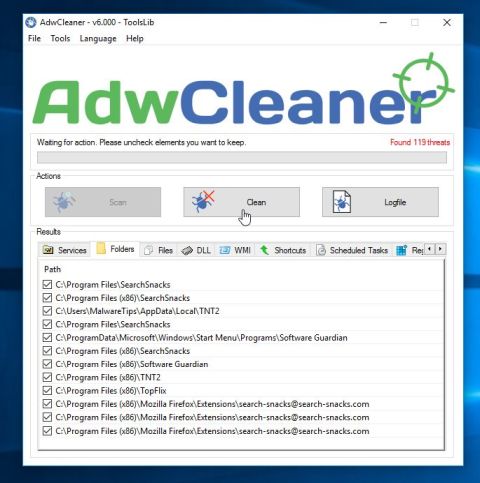
AdwCleaner will now start to search for the Cyber Security Warning adware and other malicious programs. - To remove the malicious files that were detected in the previous step, please click on the “Clean” button.
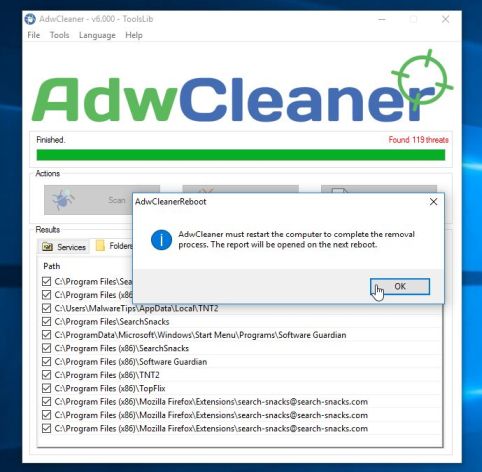
- AdwCleaner will prompt you to save any open files or documents, as the program will need to reboot the computer to complete the cleaning process. Please do so, and then click on the “OK” button.
When your computer reboots and you are logged in, AdwCleaner will automatically open a log file that contains the files, registry keys, and programs that were removed from your computer. Please review this log file and then close the notepad window.
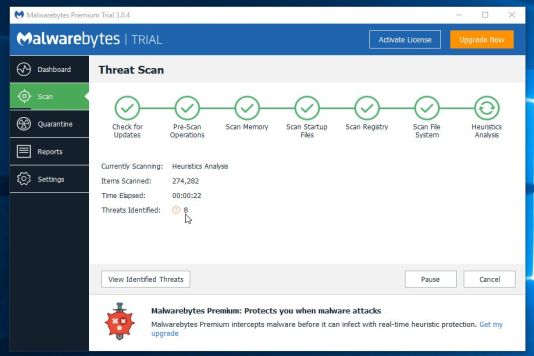
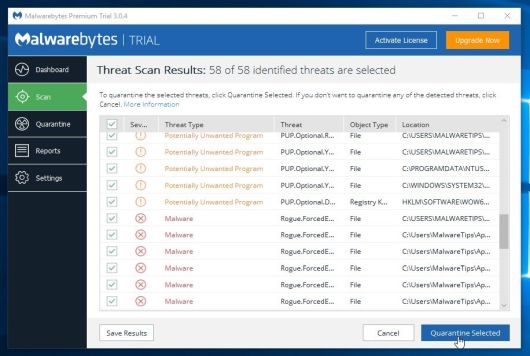
STEP 2: Scan your computer with Malwarebytes Anti-Malware
Malwarebytes Anti-Malware is a powerful on-demand scanner which will remove the Cyber Security Warning pop-ups from your machine. It is important to note that Malwarebytes Anti-Malware will run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download “Malwarebytes Anti-Malware”) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup” to start the installation of Malwarebytes Anti-Malware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
- Once installed, Malwarebytes Anti-Malware will automatically start and will update the antivirus database. To start a system scan you can click on the “Scan Now” button.
- Malwarebytes Anti-Malware will now start scanning your computer for the Cyber Security Warning malware. When Malwarebytes Anti-Malware is scanning it will look like the image below.
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Remove Selected” button.
- Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
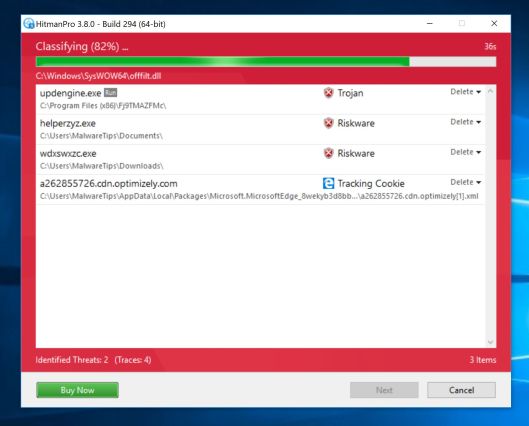
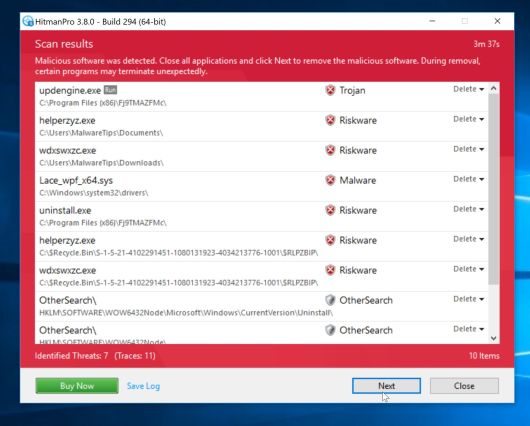
STEP 3: Scan your computer with HitmanPro
HitmanPro finds and removes malware, adware, bots, and other threats that even the best antivirus suite can oftentimes miss. It’s designed to run alongside your antivirus suite, firewall, and other security tools.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows).
Click on the “Next” button, to install HitmanPro on your computer.
- HitmanPro will now begin to scan your computer for malware.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
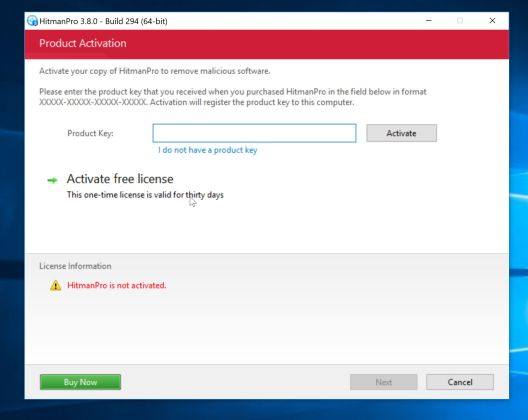
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
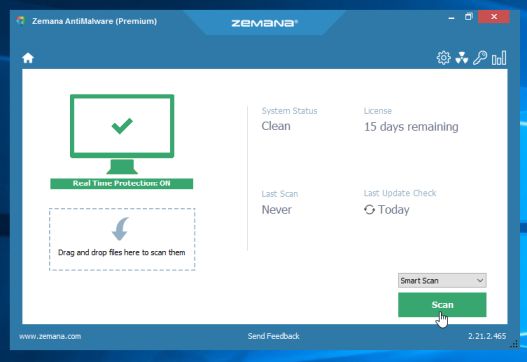
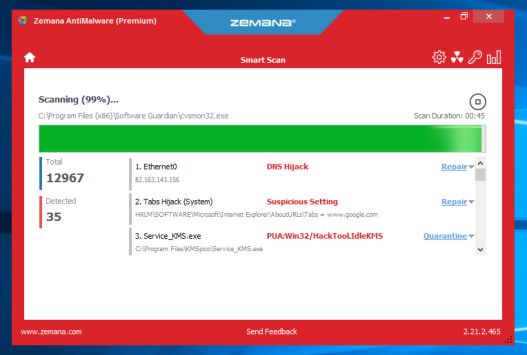
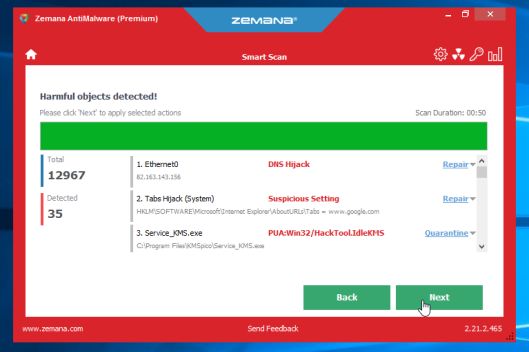
(OPTIONAL) STEP 4: Scan your computer with Zemana AntiMalware
Zemana AntiMalware is a powerful utility which will remove Cyber Security Warning redirect and other malware from your machine.
This step should be performed only if your issues have not been solved by the previous steps.
- You can download Zemana AntiMalware from the below link:
ZEMANA ANTIMALWARE DOWNLOAD LINK (This link will start the download of “Zemana AntiMalware”) - Double-click on the file named “Zemana.AntiMalware.Setup.exe” to start the installation of Zemana AntiMalware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- Click on the “Next” button, to install Zemana AntiMalware on your computer.
- When Zemana AntiMalware will start, click on the “Scan” button.
- Zemana AntiMalware will now scan computer for malicious files. This process can take up to 10 minutes.
- When Zemana AntiMalware has finished it will display a list of all the malware that the program found. Click on the “Next” button, to remove the malicious files from your computer.
Zemana AntiMalware will now remove all the detected malicious files, and at the end a system reboot may be required to remove all traces of malware.
(OPTIONAL) STEP 5: Reset your browser to default settings
If you are still experiencing issues with the Cyber Security Warning browser hijacker in Internet Explorer, Firefox or Chrome, we will need to reset your browser to its default settings.
This step should be performed only if your issues have not been solved by the previous steps.
Internet Explorer
- Open Internet Explorer, click on the “gear icon”
in the upper right part of your browser, then click again on Internet Options.
- In the “Internet Options” dialog box, click on the “Advanced” tab, then click on the “Reset” button.
- In the “Reset Internet Explorer settings” section, select the “Delete personal settings” check box, then click on “Reset” button.
- When Internet Explorer has completed its task, click on the “Close” button in the confirmation dialogue box. You will now need to close your browser, and then you can open Internet Explorer again.
Mozilla Firefox
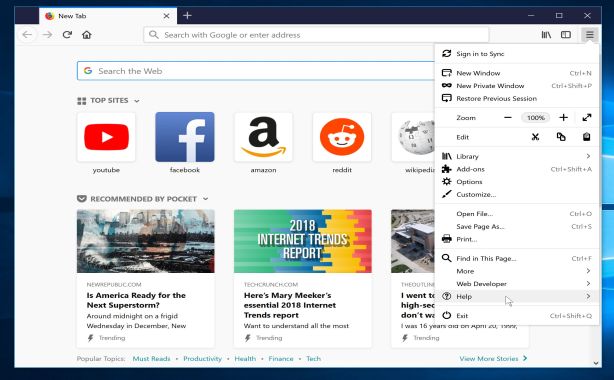
- In the upper-right corner of the Firefox window, click the Firefox menu button (
), then click on the “Help” (
) button.
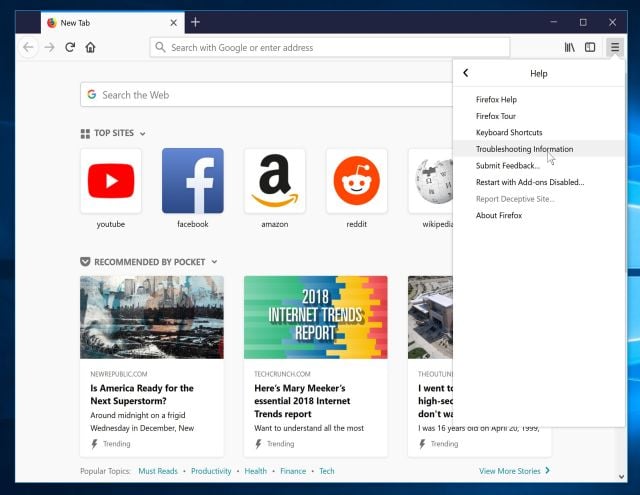
- From the Help menu, choose Troubleshooting Information.
If you’re unable to access the Help menu, type about:support in your address bar to bring up the Troubleshooting information page.
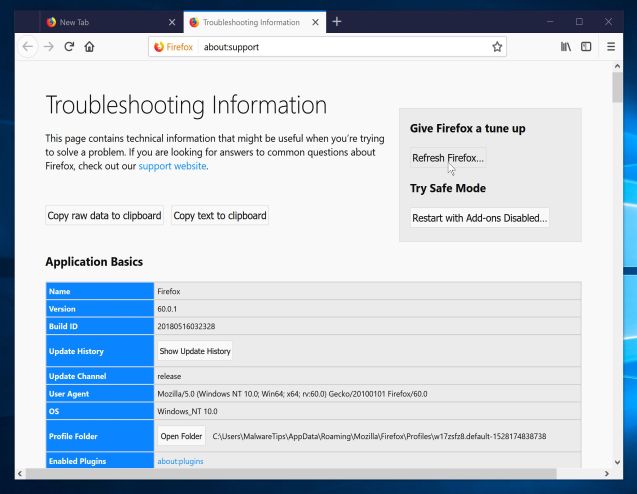
- Click the “Refresh Firefox” button in the upper-right corner of the “Troubleshooting Information” page.
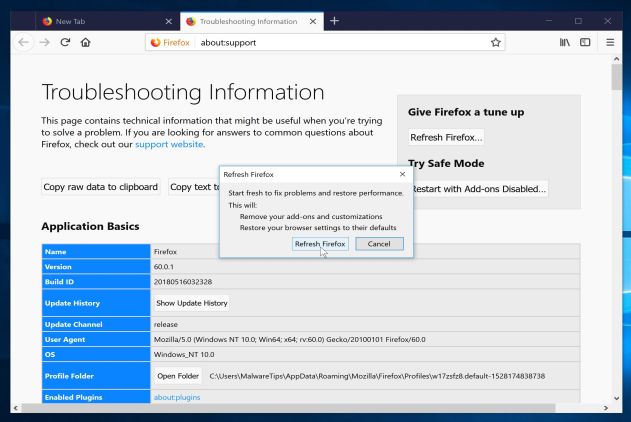
- To continue, click on the “Refresh Firefox” button in the new confirmation window that opens.
- Firefox will close itself and will revert to its default settings. When it’s done, a window will list the information that was imported. Click on the “Finish“.
Note: Your old Firefox profile will be placed on your desktop in a folder named “Old Firefox Data“. If the reset didn’t fix your problem you can restore some of the information not saved by copying files to the new profile that was created. If you don’t need this folder any longer, you should delete it as it contains sensitive information.
Google Chrome
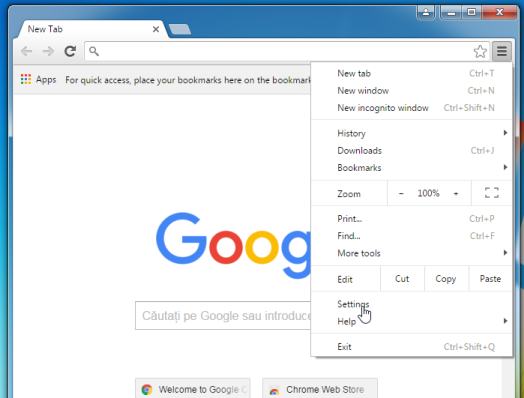
- Click on Chrome’s main menu button, represented by three horizontal lines (
). When the drop-down menu appears, select the option labeled Settings.
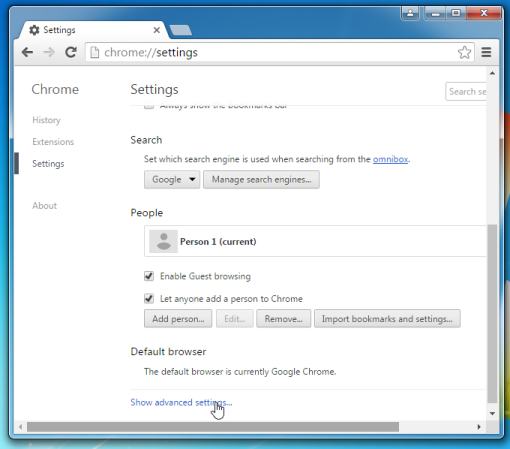
- Chrome’s Settings should now be displayed in a new tab or window, depending on your configuration. Next, scroll to the bottom of the page and click on the Show advanced settings link (as seen in the below example).
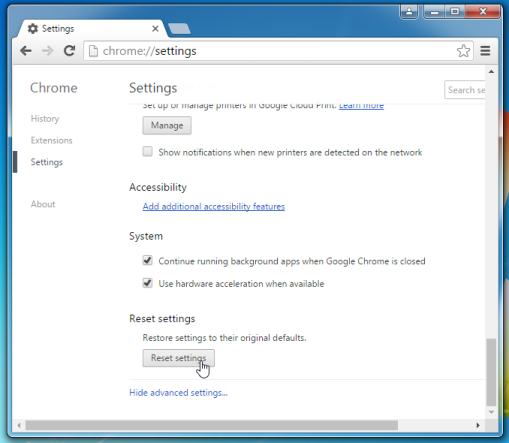
- Chrome’s advanced Settings should now be displayed. Scroll down until the Reset browser settings section is visible, as shown in the example below. Next, click on the Reset browser settings button.
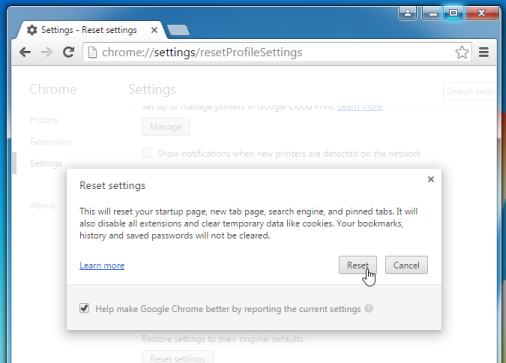
- A confirmation dialog should now be displayed, detailing the components that will be restored to their default state should you continue on with the reset process. To complete the restoration process, click on the Reset button.
Your computer should now be free of the Cyber Security Warning pop-ups. You can remove AdwCleaner from your machine, however we recommend that you keep Malwarebytes Anti-Malware and HitmanPro installed and perform regular computer scans.
If you are still experiencing problems while trying to remove Cyber Security Warning redirect from your machine, please start a new thread in our Malware Removal Assistance forum.







![Click on the Gear Icon then on Internet Options [Image: Internet Options in Internet Explorer]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/Internet-Options-Internet-Explorer.jpg)
![In the Advanced tab click on the Reset button [Image: Reset Internet Explorer]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/Reset-Internet-Explorer.jpg)
![Click on the Reset button to revert IE to its default settings [Image: Reset Internet Explorer to its default settings]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/reset-button-Internet-Explorer.jpg)
![Click on the Close button [Image Reset Internet Explorer settings]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/Close-button-Reset.jpg)