Zeus Trojan (or Zbot Trojan) is a computer virus that attempts to steal confidential information from the compromised computer.
The Trojan itself is primarily distributed through spam campaigns and drive-by downloads, though given its versatility, other vectors may also be utilized. The user may receive an email message purporting to be from organizations such as the FDIC, IRS, MySpace, Facebook, or Microsoft. The message body warns the user of a problem with their financial information, online account, or software and suggests they visit a link provided in the email. The computer is compromised if the user visits the link, if it is not protected.
The Zeus Trojan has primarily been designed to steal confidential information from the computers it compromises. It specifically targets system information, online credentials, and banking details, but can be customized through the toolkit to gather any sort of information. This is done by tailoring configuration files that are compiled into the Trojan installer by the attacker. These can later be updated to target other information, if the attacker so wishes.
Confidential information is gathered through multiple methods. Upon execution the Trojan automatically gathers any Internet Explorer, FTP, or POP3 passwords that are contained within Protected Storage (PStore). However, its most effective method for gathering information is by monitoring Web sites included in the configuration file, sometimes intercepting the legitimate Web pages and inserting extra fields (e.g. adding a date of birth field to a banking Web page that originally only requested a username and password).
Additionally, Zeus Trojan contacts a command-and-control (C&C) server and makes itself available to perform additional functions. This allows a remote attacker to command the Trojan to download and execute further files, shutdown or reboot the computer, or even delete system files, rendering the computer unusable without reinstalling the operating system.
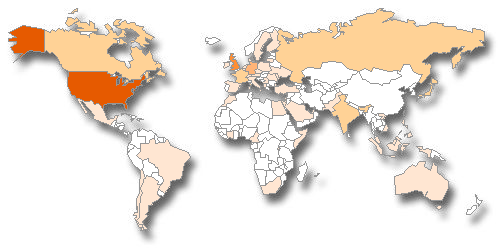
Symantec has observed the following geographic distribution of this threat:
Zeus Trojan can be detected by the security products as: Trojan-Spy:W32/Zbot [F-Secure],PWS-Zbot [McAfee],Trojan-Spy.Win32.Zbot [Kaspersky], Win32/Zbot [Microsoft],Infostealer.Monstres [Symantec], Infostealer.Banker.C [Symantec],Trojan.Wsnpoem [Symantec] or Troj/Zbot-LG [Sophos].
How to remove Zeus malware (Virus Removal Guide)
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
- STEP 1: Use Rkill to terminate the ZEUS Fake Windows Process
- STEP 2: Use Malwarebytes to remove ZEUS malware
- STEP 3: Use HitmanPro to scan for ZEUS virus
- STEP 4: Use Zemana AntiMalware Free to remove Potentially Unwanted Programs
- (OPTIONAL) STEP 5: Double-check for malicious programs with Emsisoft Emergency Kit
- (OPTIONAL) STEP 6: Reset your browser to default settings
STEP 1: Use Rkill to terminate the ZEUS Fake Windows Process
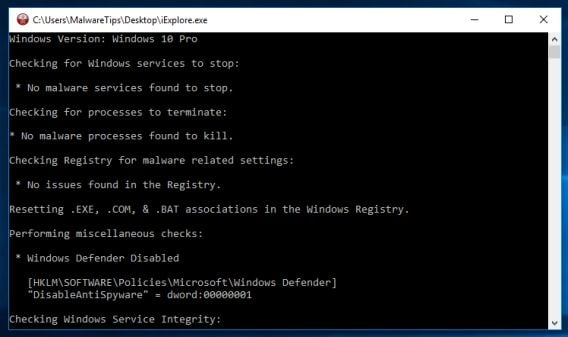
RKill is a program that will attempt to terminate all malicious processes associated with this infection, so that we will be able to perform the next step without being interrupted by this malicious software.
-
Download Rkill.
You can download RKill by clicking the link below.
RKILL DOWNLOAD LINK (This link will open a new web page from where you can download “RKill”) -
Double-click on the RKill icon.
Double click on Rkill program to stop the malicious programs from running.
-
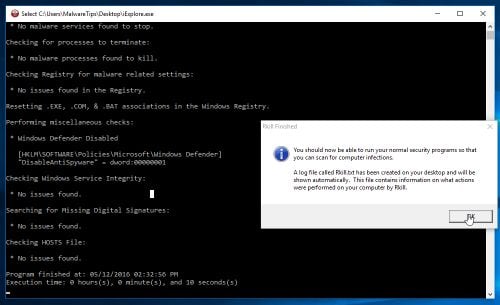
Wait for the RKill scan to complete.
RKill will now start working in the background, please be patient while this utility looks for malicious process and tries to end them.
-
RKill will stop the malicious programs. Continue with the other steps.
When the Rkill tool has completed its task, it will generate a log. Do not reboot your computer after running RKill as the malware programs will start again.
STEP 2: Use Malwarebytes to remove ZEUS malware
Malwarebytes is one of the most popular and most used anti-malware software for Windows, and for good reasons. It is able to destroy many types of malware that other software tends to miss, without costing you absolutely nothing. When it comes to cleaning up an infected device, Malwarebytes has always been free and we recommend it as an essential tool in the fight against malware.
The first time you install Malwarebytes, you’re given a free 14-day trial of the premium edition, which includes preventative tools like real-time scanning and specific protection from ransomware. After two weeks, it automatically reverts to the basic free version that will detect and clean up malware infections only when you run a scan. It is important to note that Malwarebytes will run alongside antivirus software without conflicts.
-
Download Malwarebytes.
You can download Malwarebytes by clicking the link below.
MALWAREBYTES DOWNLOAD LINK
(The above link will open a new page from where you can download Malwarebytes) -
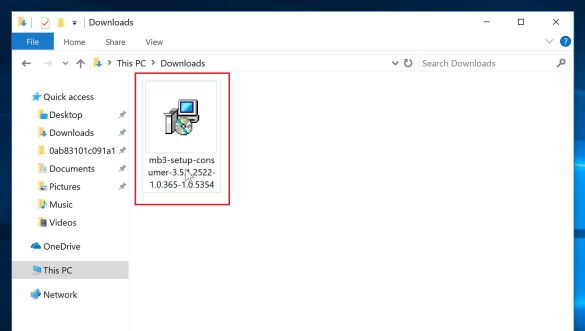
Double-click on the Malwarebytes setup file.
When Malwarebytes has finished downloading, double-click on the mb3-setup-consumer-x.x.x.xxxx.exe file to install Malwarebytes on your PC. In most cases, downloaded files are saved to the Downloads folder.
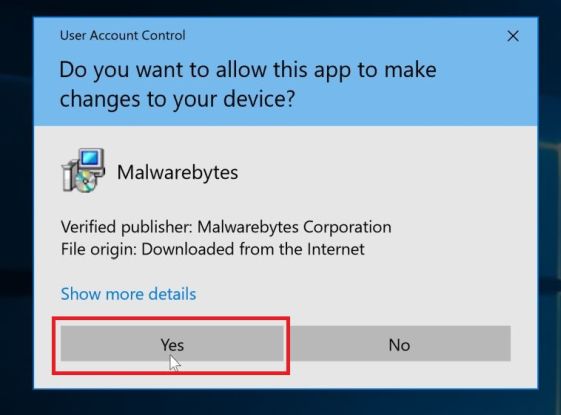
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
-
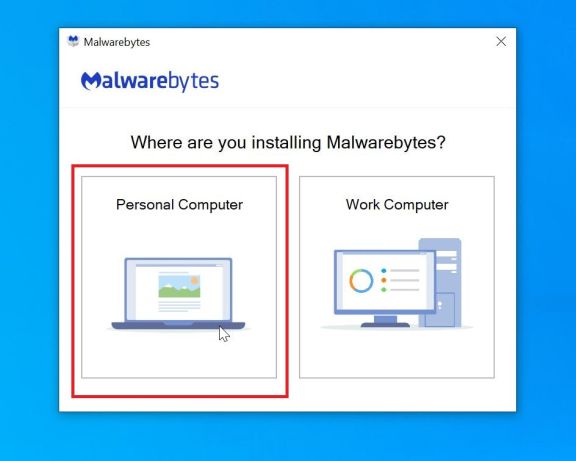
Follow the on-screen prompts to install Malwarebytes.
When the Malwarebytes installation begins, you will see the Malwarebytes Setup Wizard which will guide you through the installation process. To install Malwarebytes on your PC, click on the “Agree and Install” button.
-
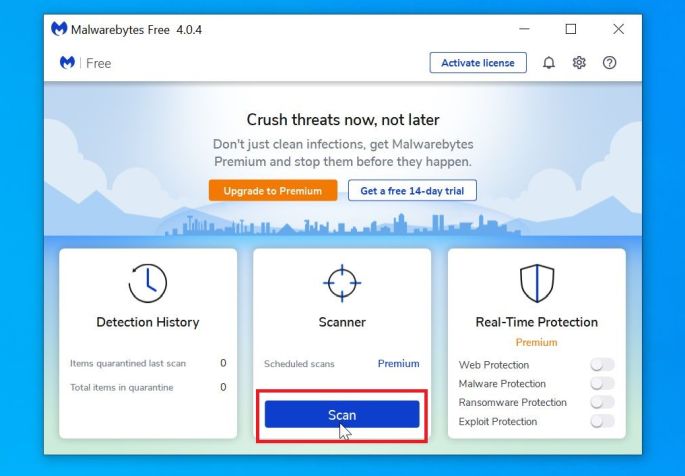
Click on “Scan Now”.
Once installed, Malwarebytes will automatically start and update the antivirus database. To perform a system scan, click on the “Scan Now” button.
-
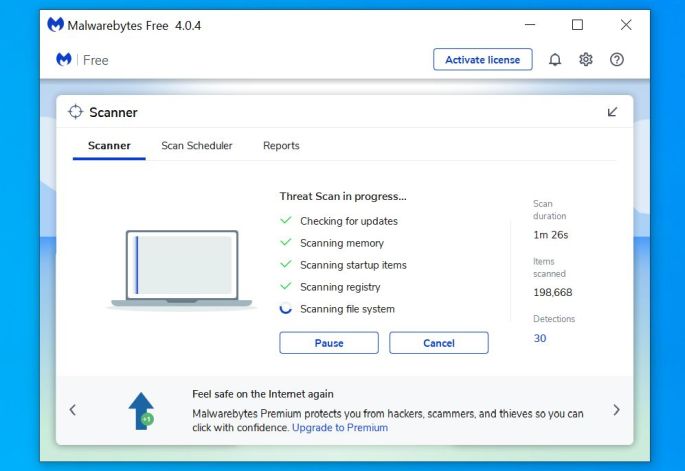
Wait for the Malwarebytes scan to complete.
Malwarebytes will now start scanning your computer for adware and other malicious programs. This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
-
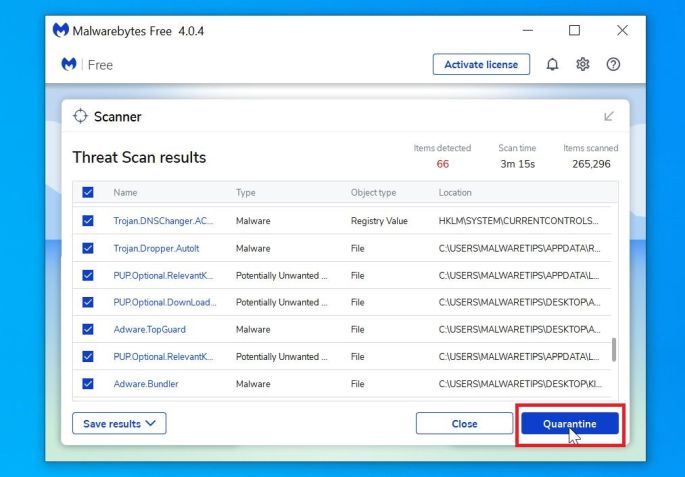
Click on “Quarantine Selected”.
When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected. To remove the malicious programs that Malwarebytes has found, click on the “Quarantine Selected” button.
-
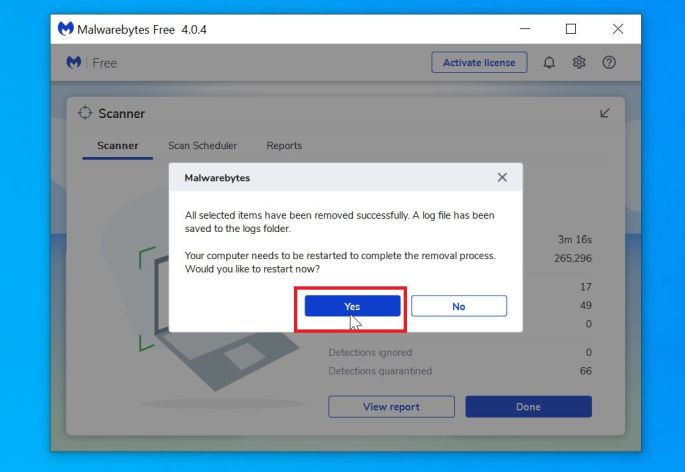
Reboot your computer.
Malwarebytes will now remove all the malicious files and registry keys that it has found. To complete the malware removal process, Malwarebytes may ask you to restart your computer.
When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
STEP 3: Use HitmanPro to scan for the ZEUS virus
HitmanPro is a second opinion scanner that takes a unique cloud-based approach to malware scanning. HitmanPro scans the behavior of active files and also files in locations where malware normally resides for suspicious activity. If it finds a suspicious file that’s not already known, HitmanPro sends it to their clouds to be scanned by two of the best antivirus engines today, which are Bitdefender and Kaspersky.
Although HitmanPro is shareware and costs $24.95 for 1 year on 1 PC, there is actually no limit in scanning. The limitation only kicks in when there is a need to remove or quarantine detected malware by HitmanPro on your system and by then, you can activate the one time 30 day trial to enable the clean up.
-
Download HitmanPro.
You can download HitmanPro by clicking the link below.
HITMANPRO DOWNLOAD LINK
(The above link will open a new web page from where you can download HitmanPro) -
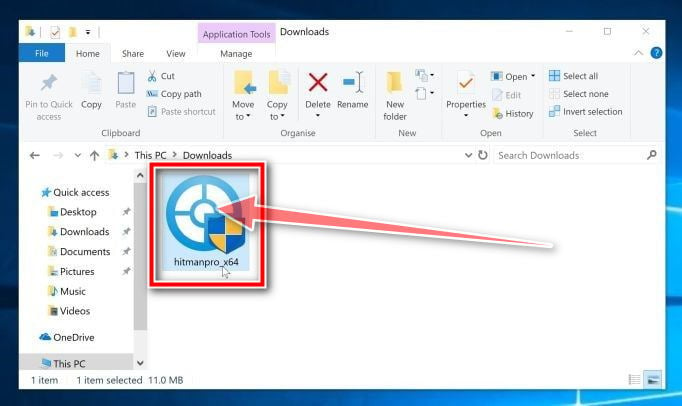
Install HitmanPro.
When HitmanPro has finished downloading, double-click on “hitmanpro.exe” (for 32-bit versions of Windows) or “hitmanpro_x64.exe” (for 64-bit versions of Windows) to install this program on your PC. In most cases, downloaded files are saved to the Downloads folder.
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation. -
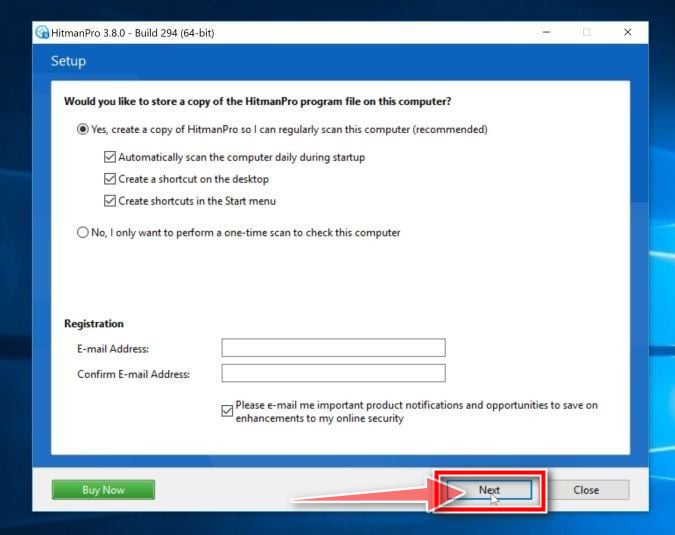
Follow the on-screen prompts.
When HitmanPro starts you will be presented with the start screen as shown below. Click on the “Next” button to perform a system scan.
-
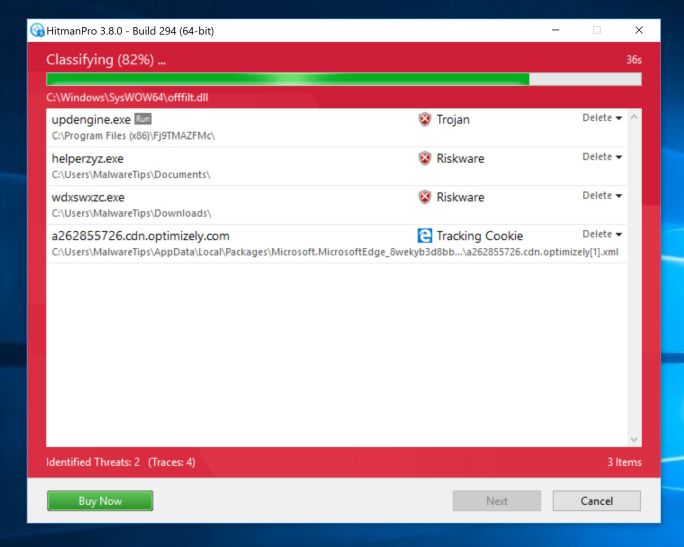
Wait for the HitmanPro scan to complete.
HitmanPro will now begin to scan your computer for malicious programs. This process will take a few minutes.
-
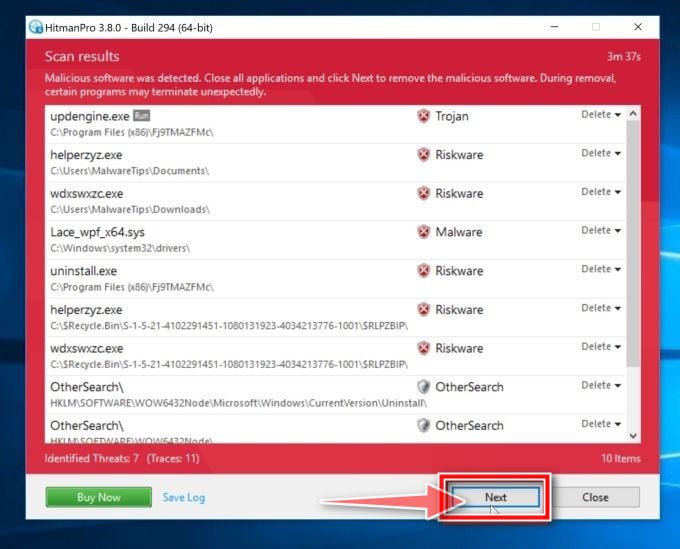
Click on “Next”.
When HitmanPro has finished the scan, it will display a list of all the malware that the program has found. Click on the “Next” button to remove the malicious programs.
-
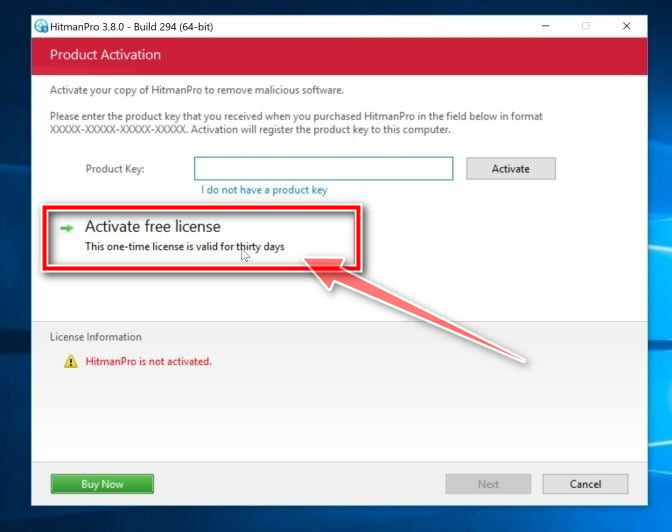
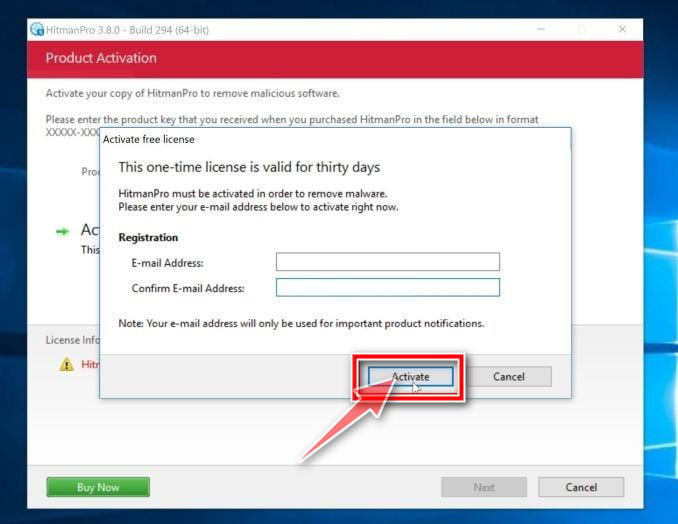
Click on “Activate free license”.
Click on the “Activate free license” button to begin the free 30 days trial and remove all the malicious files from your PC.
When the process is complete, you can close HitmanPro and continue with the rest of the instructions.
STEP 4: Use Zemana AntiMalware Free to remove Potentially Unwanted Programs
Zemana AntiMalware is a free popular on-demand antivirus scanner which can detect and remove malware that even the most well-known anti-virus and anti-malware applications fail to find.
-
Download Zemana AntiMalware.
You can download Zemana AntiMalware Free by clicking the link below.
ZEMANA ANTIMALWARE DOWNLOAD LINK
(The above link will open a new web page from where you can download Zemana AntiMalware) -
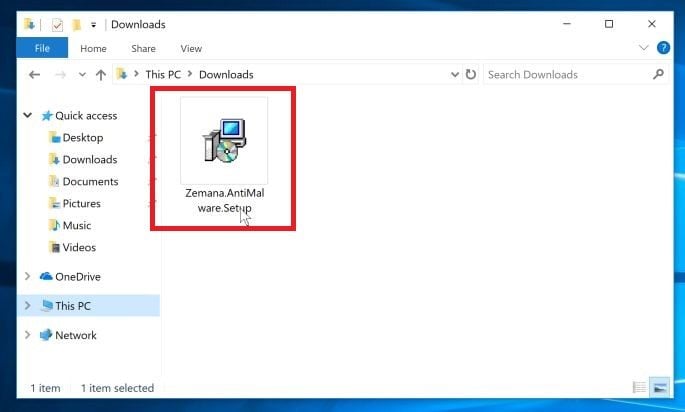
Double-click on the setup file.
Double-click on the file named “Zemana.AntiMalware.Setup.exe” to start the installation of Zemana AntiMalware. In most cases, downloaded files are saved to the Downloads folder.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
-
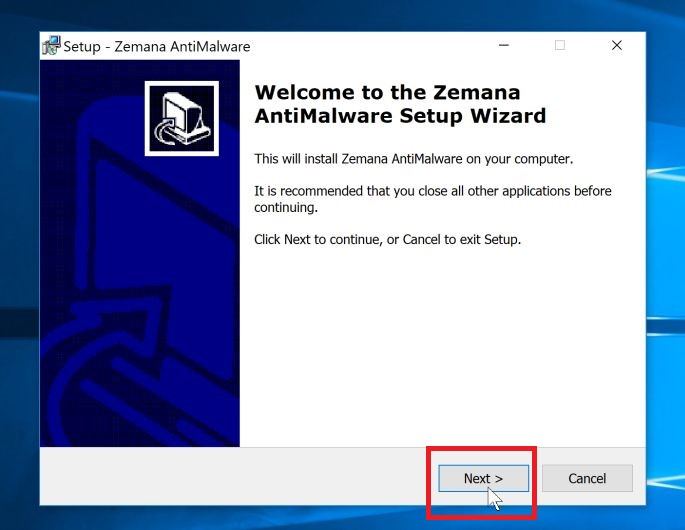
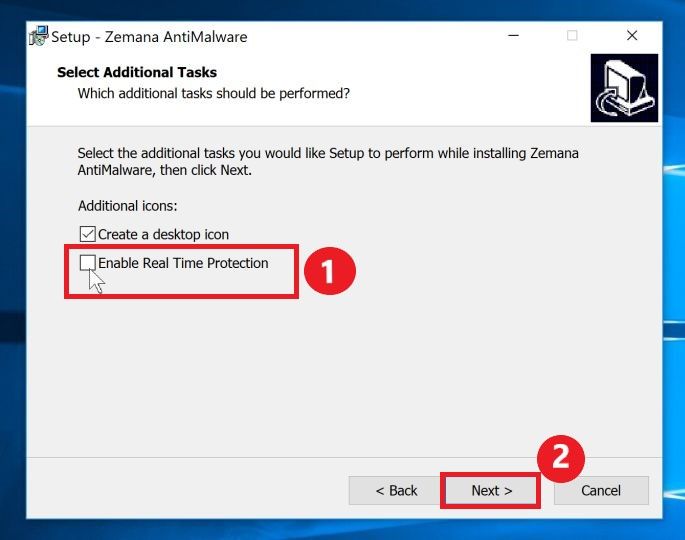
Install Zemana AntiMalware Free.
Click on the “Next” button to install Zemana AntiMalware on your PC. Follow the on-screen prompts to complete the install process.
When you reach the “Select Additional Tasks” screen, you need to opt-out the “Enable Real Time Protection” option, then click on the “Next” button.
-
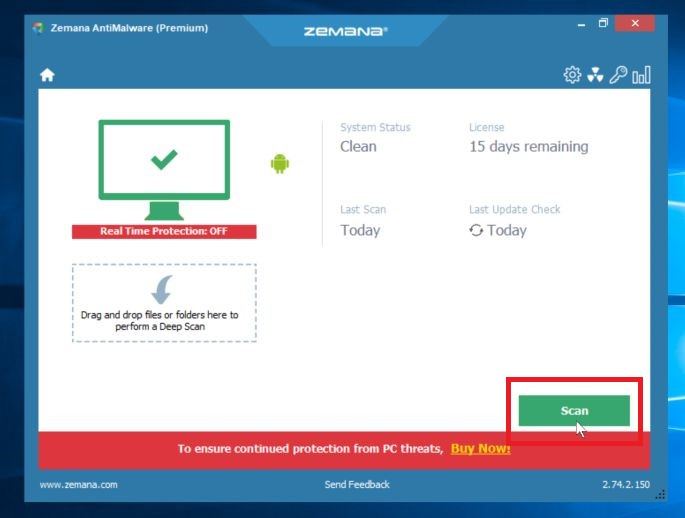
Click on “Scan”.
When Zemana AntiMalware will start, click on the “Scan” button to perform a system scan.
-
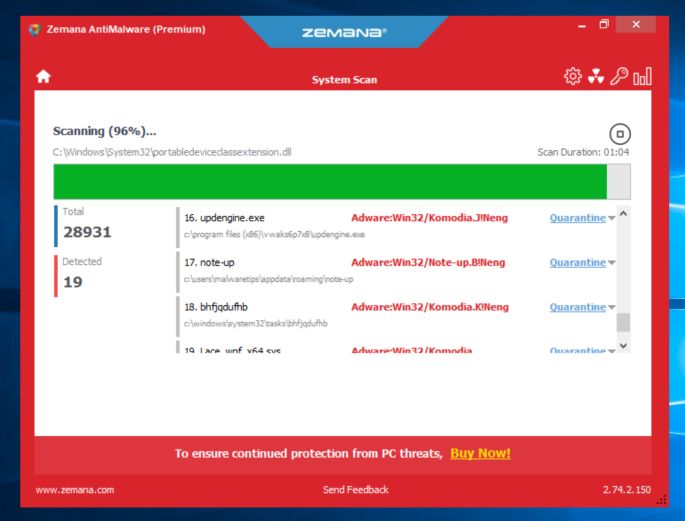
Wait for the Zemana AntiMalware scan to complete.
Zemana AntiMalware will now scan your PC for malicious files. This process can take a few minutes.
-
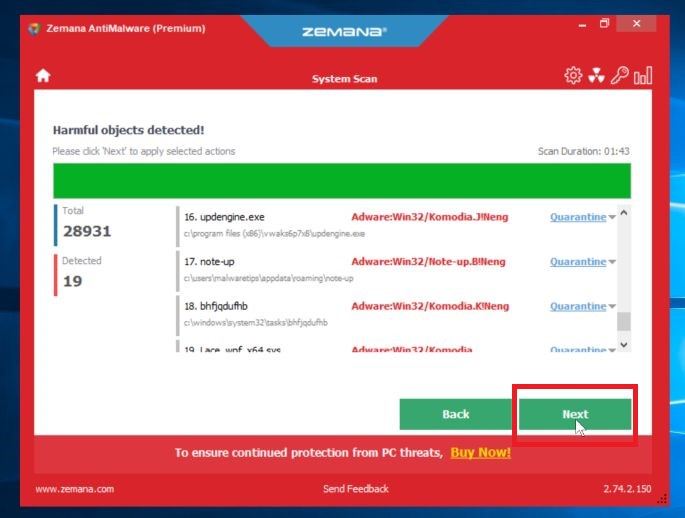
Click on “Next”.
When Zemana AntiMalware has finished it will display a list of all the malware that the program found. Click on the “Next” button to remove the malicious files from your computer.
-
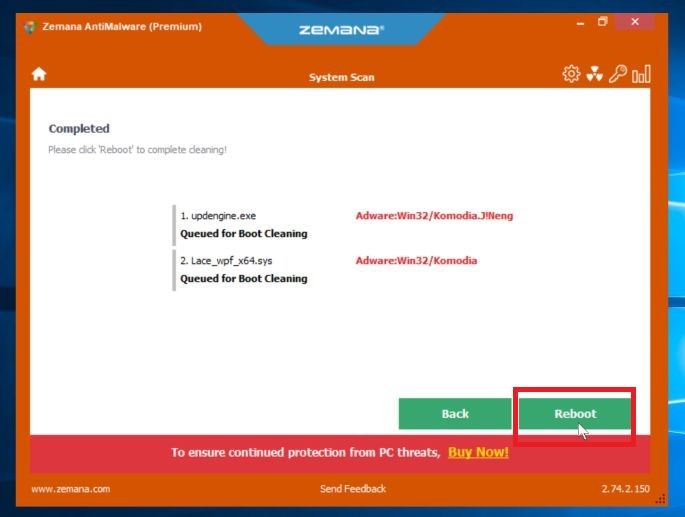
Restart your PC.
When the malware removal process is complete, Zemana AntiMalware may need to restart your computer. Click on the “Reebot” button to reset your PC.
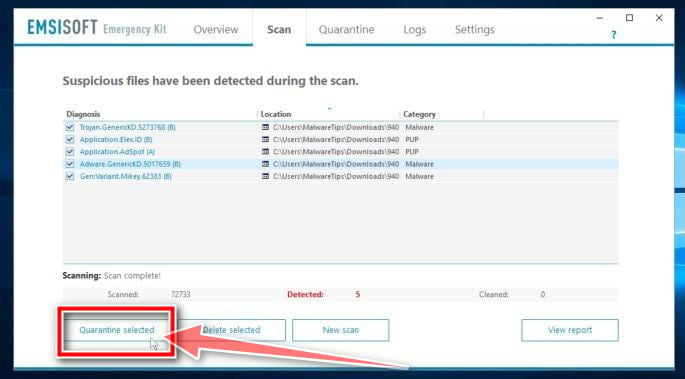
(OPTIONAL) STEP 5: Double-check for malicious programs with Emsisoft Emergency Kit
Emsisoft Emergency Kit is a free and powerful on-demand scanner that can be used to remove viruses, trojans, spyware, adware, worms, and other malicious programs.
While the previous scans are more than enough, we’re recommending Emsisoft Emergency Kit to users who still have malware related issues or just want make sure their PC is 100% clean.
-
Download Emsisoft Emergency Kit.
You can download Emsisoft Emergency Kit by clicking the link below.
EMSISOFT EMERGENCY KIT DOWNLOAD LINK
(The above link will open a new web page from where you can download Emsisoft Emergency Kit) -
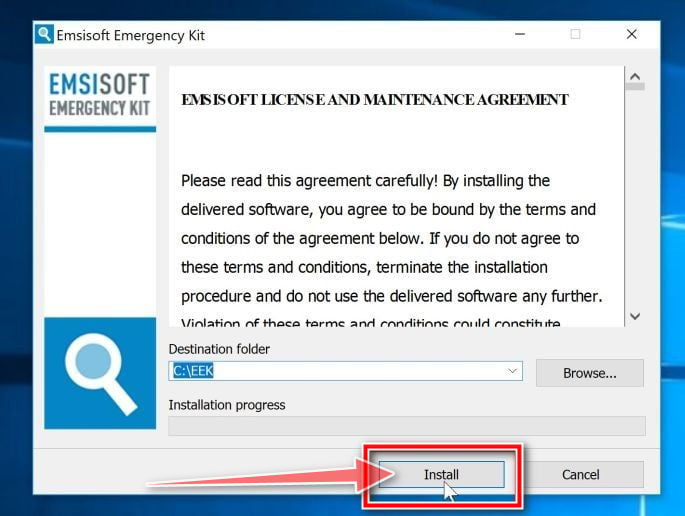
Install Emsisoft Emergency Kit.
Double-click on the EmsisoftEmergencyKit setup file to start the installation process, then click on the “Install” button.
-
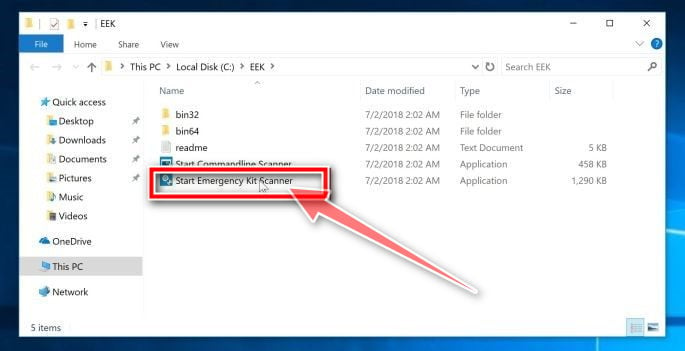
Start Emsisoft Emergency Kit.
On your desktop the “EEK” folder (C:\EEK) should now be open. To start Emsisoft, click on the “Start Emsisoft Emergency Kit” file to open this program.
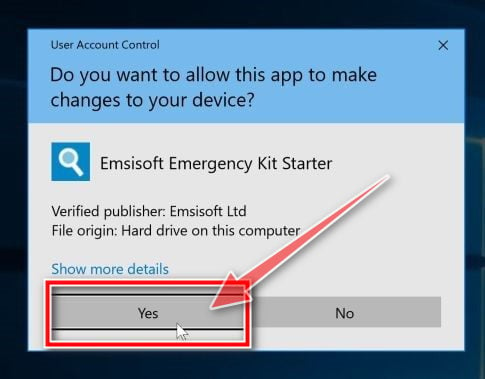
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
-
Click on “Malware Scan”.
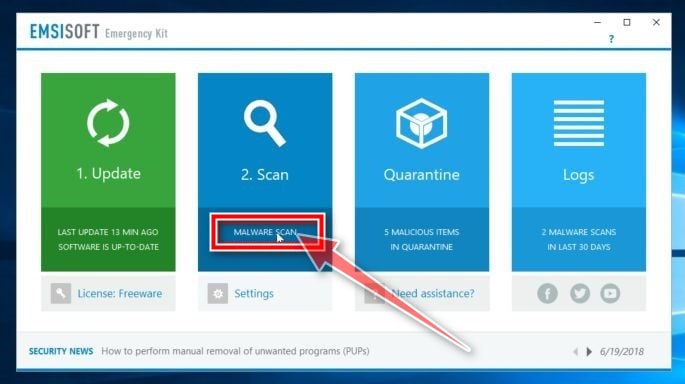
Emsisoft Emergency Kit will start and it will ask you for permission to update itself. Once the update process is complete, click on the “Scan” tab, and perform a “Malware Scan“.
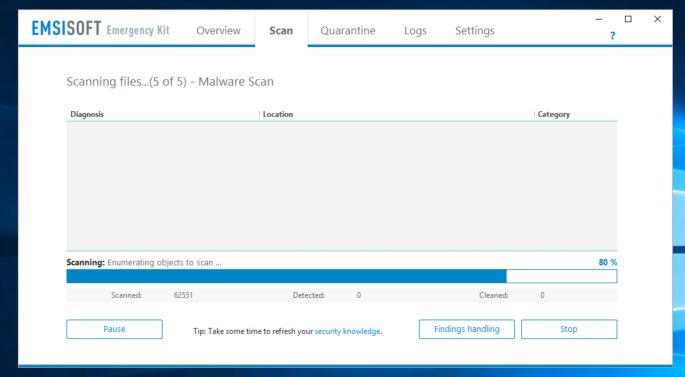
Emsisoft Emergency Kit will now scan your PC for malicious files. This process can take a few minutes.
-
Click on “Quarantine selected”.
When the Emsisoft scan has finished, you will be presented with a screen reporting which malicious files were detected on your computer. To remove the malicious programs, click on the “Quarantine selected“.
When the malware removal process is complete, Emsisoft Emergency Kit may need to restart your computer. Click on the “Reebot” button to restart your PC.
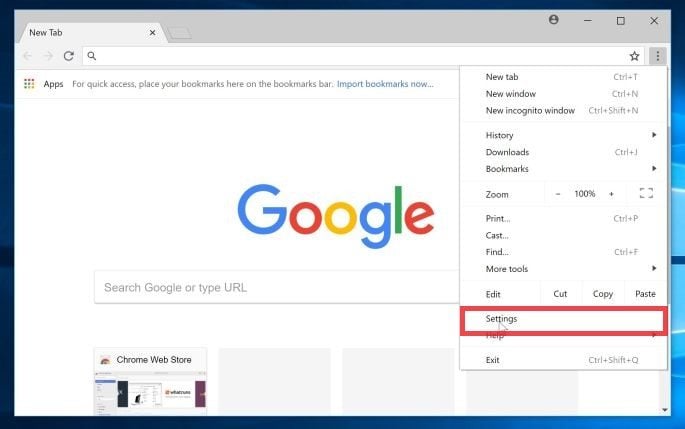
(OPTIONAL) STEP 6: Reset the browser settings to their original defaults
If your browser is being redirected or seeing unwanted advertisements, we will need to reset the web browser settings to their original defaults. This step should be performed only if your issues have not been solved by the previous steps.
Google Chrome
-
Click on the three dots at the top right and click “Settings”.
Click on Chrome’s main menu button, represented by three dots at the top right corner. Now click on the menu option labeled Settings as shown by the arrow in the picture below, which will open the basic settings screen.
-
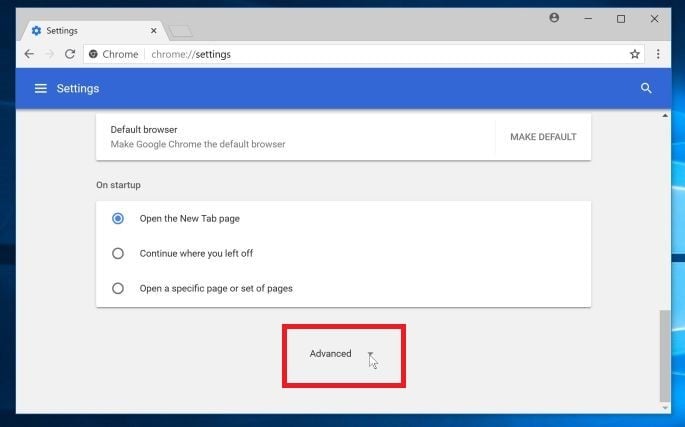
At the bottom, click “Advanced”.
Chrome’s “Settings” should now be displayed in a new tab or window, depending on your configuration. Next, scroll to the bottom of the page and click on the “Advanced” link (as seen in the below example).
-
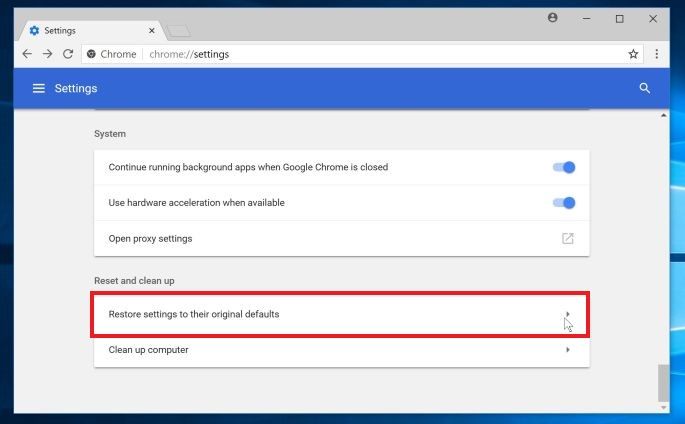
Under the section “Reset,” click “Reset”.
Chrome’s advanced settings should now be displayed. Scroll down until the “Reset and clean up” section is visible, as shown in the example below. Next, click on the “Reset settings to their original defaults” button.
-
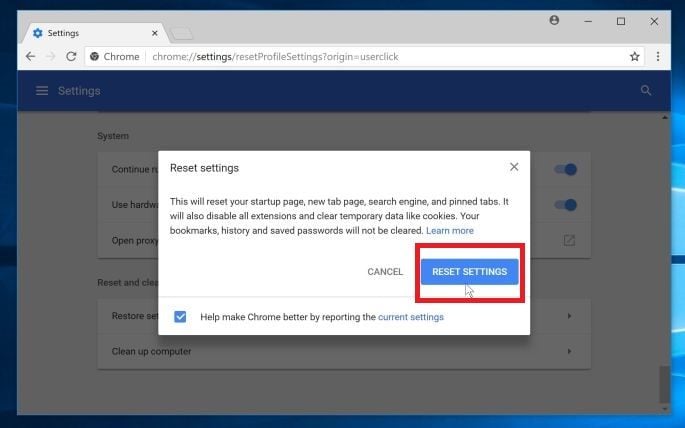
Confirm by clicking “Reset”.
A confirmation dialog should now be displayed, detailing the components that will be restored to their default state should you continue on with the reset process. To complete the restoration process, click on the “Reset Settings” button.
Mozilla Firefox
-
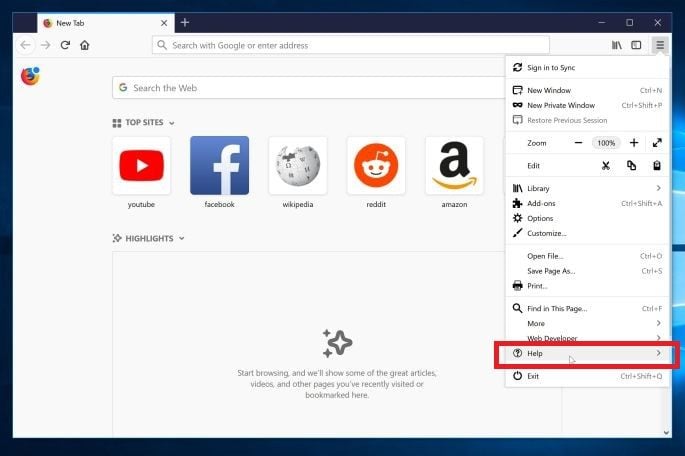
Go to the “Help” menu.
Click on Firefox’s main menu button, represented by three horizontal lines. When the drop-down menu appears, select the option labeled “Help“.
-
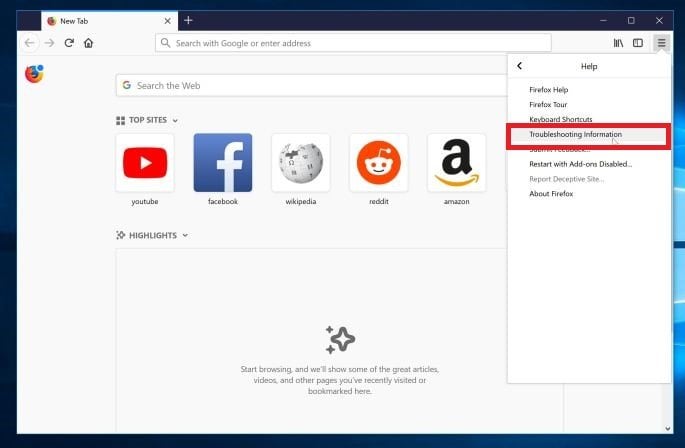
Click “Troubleshooting Information”.
From the Help menu, click on “Troubleshooting Information“.
If you’re unable to access the “Help” menu, type about:support in your address bar to bring up the Troubleshooting information page. -
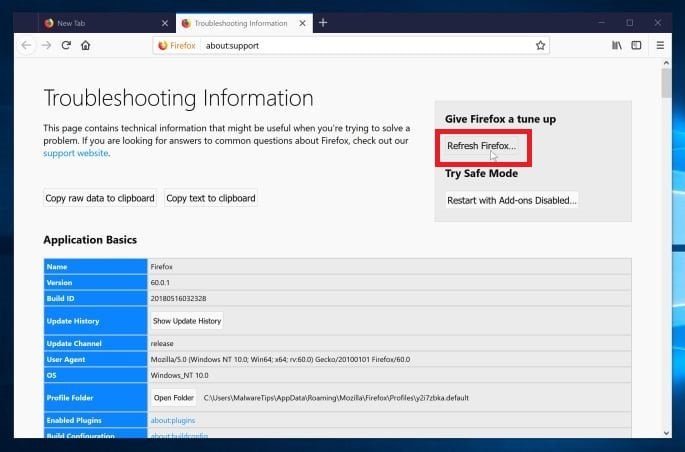
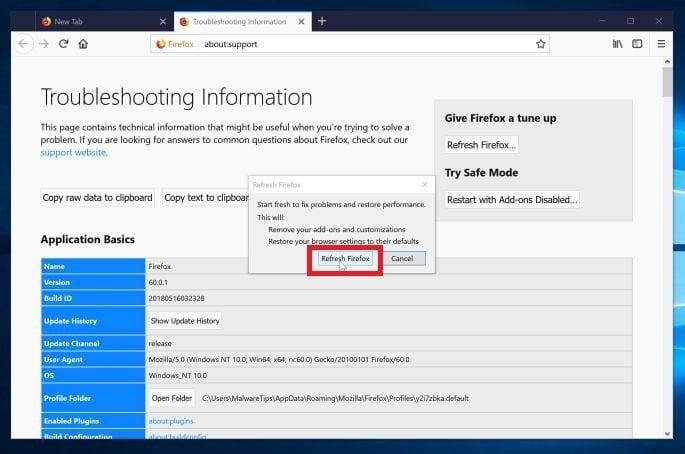
Click on “Refresh Firefox”
Click the “Refresh Firefox” button in the upper-right corner of the “Troubleshooting Information” page.
-
Confirm.
To continue, click on the “Refresh Firefox” button in the new confirmation window that opens.
-
Click on “Finish”.
Firefox will close itself and will revert to its default settings. When it’s done, a window will list the information that was imported. Click on the “Finish“.
Internet Explorer
-
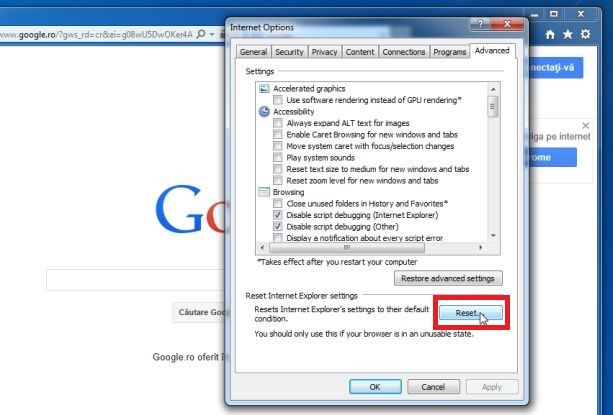
Go to “Internet Options”.
Open Internet Explorer, click on the gear icon in the upper right part of your browser, then select “Internet Options“.
-
Select the “Advanced” tab, then click “Reset”
In the “Internet Options” dialog box, select the “Advanced” tab, then click on the “Reset” button.
-
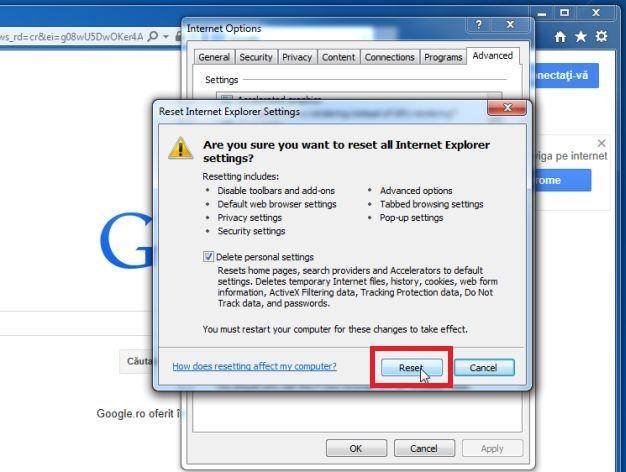
Click on “Reset”.
In the “Reset Internet Explorer settings” section, select the “Delete personal settings” check box, then click on “Reset” button.
-
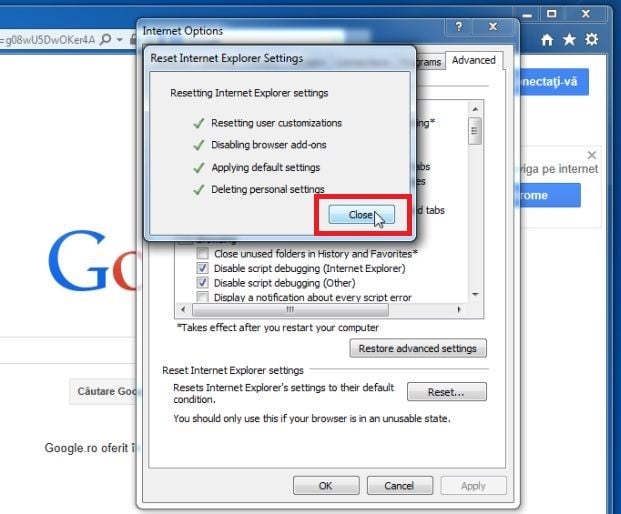
Click on “Close”.
When Internet Explorer has completed its task, click on the “Close” button in the confirmation dialogue box.
You will now need to close your browser, and then you can open Internet Explorer again.
Microsoft Edge
-
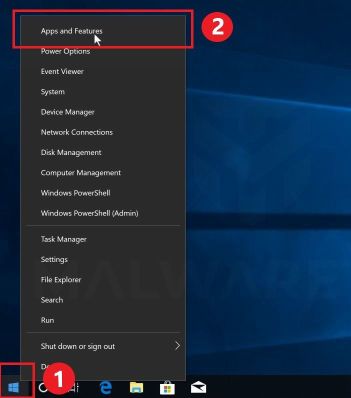
Go to “Apps and Features”.
Right-click on the Start
button in the lower-left corner and select “Apps and Features“. This will take you directly to your list of installed programs.
-
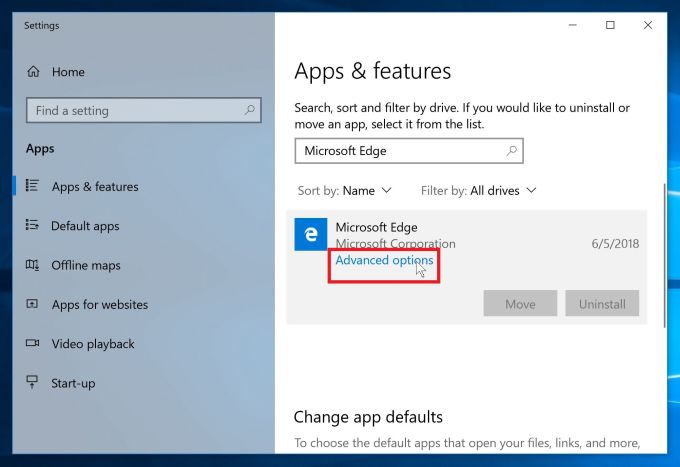
Find Microsoft Edge, then select “Advanced Options”.
The “App and Features” screen will be displayed with a list of all the programs installed on your PC. Scroll through the list until you find “Microsoft Edge”, click it, and then click on the “Advanced options” link.
-
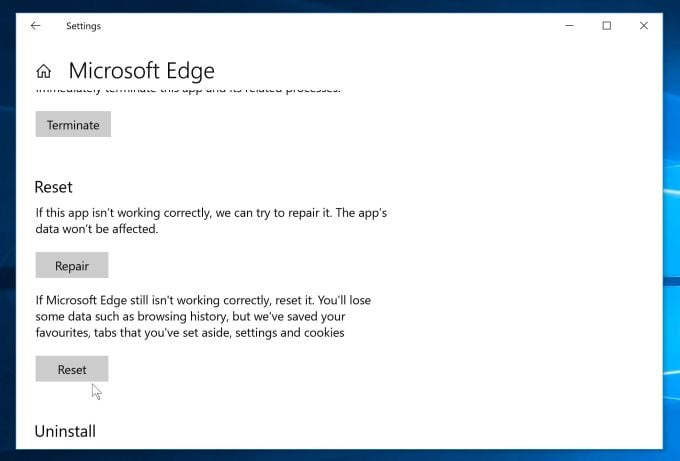
Click on “Reset”.
The “Advanced Options” screen will now be displayed. Scroll down until the “Reset” section is visible, as shown in the example below. Next, click on the “Reset” button.
Your computer should now be free of the ZEUS malware. If you are still experiencing problems while trying to remove ZEUS malicious process from your device, you can ask for help in our Malware Removal Assistance for Windows forum.













Stelian, my daughters computer just got this stupid Zues virus that says her hard drive will be erased if she closed any screens and to call customer support 800 number. What should she do. I figured these folks relied on your knowledge, so I figured why not. Her current McAfee protection expired and she hadn’t downloaded here Kaspersky yet. Will she be able to or need to download virus protection software before going through what these folks did? Any help would be appreciated. Thanks
HI Stelian
Many thanks for this excellent advice. I think I may only have been scammed that I have the Zeus virus rather than actually having it, as the programmes you suggest above did not detect it.
As a worrier, I went through the whole process anyway (Maleware, HitManPro etc.), except the final step of Zemana AntiMalware which would not install. Seemed to suggest it was conflicting with my Firewell or Security, which I am too dumb to alter. Any tips how to get around that, or do you think I should be safe anyway?
Many thanks again,
Sue
Hello Levi,
You should be able to fix it yourself. You are most likely not infected by the Zeus Trojan, instead you are the victim of a tech support scam https://malwaretips.com/blogs/remove-windows-detected-zeus-virus-popups/
You can also ask for free malware removal support in the Malware Removal Assistance forum – https://malwaretips.com/forums/malware-removal-assistance.10/ . In this support forum, a trained staff member will help you clean-up your machine by using advanced tools. Never used a forum? Learn how- https://malwaretips.com/help/welcome-guide/
Hello Penny,
It would be best that you start a thread Malware Removal Assistance forum – https://malwaretips.com/forums/malware-removal-assistance.10/ , so that we may take a look at what’s going on.
In this support forum, a trained staff member will help you clean-up your machine by using advanced tools. Never used a forum? Learn how- https://malwaretips.com/help/welcome-guide/
Hello Penny,
Did the pop-ups look like these: https://malwaretips.com/blogs/remove-windows-detected-zeus-virus-popups/ ?- If yes, you were the victim of a tech support scam.
Do not pay for anything these guys are selling, and if you did, contact you bank and ask them to return your money as you were the victim o f a scam.
If you still have malware issues, you can ask for FREE malware removal support in the Malware Removal Assistance forum – https://malwaretips.com/forums/malware-removal-assistance.10/ . In this support forum, a trained staff member will help you clean-up your machine by using advanced tools. Never used a forum? Learn how- https://malwaretips.com/help/welcome-guide/