@upnorth asked me to do a small writeup of the sample used for testing here: https://malwaretips.com/threads/ransomware-loader-19-10-2020.104659/
This is not a fully detailed analysis, because that would take days to do. Instead I write all things down I can assess quickly.
Analysis of Downloader
Sample: VirusTotal
File type: Office Open XML document
Malware type: downloader
File name: UBC-COVID19-Survey-Mandatory.docx
After unpacking with 7zip you can find those images in word/media/:

The detection names suggest use of CVE-2017-0199.
Description of the CVE is consistent with the behaviour in any.run which shows winword.exe as doing the download and execute.
Contacted URLs by winword.exe:
hxxp://canarytokens(.)com/about/d4yeyvldfg6bn5y29by4e9fs3/post(.)jsp
hxxp://isrg.trustid.ocsp.identrust(.)com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D
Persistence for the downloaded file:
schtasks.exe /create /sc minute /mo 3 /tn "Internet Explorer Error Handling" /tr %APPDATA%\Byxor\polisen.exe
Analysis of Downloaded file
Sample:
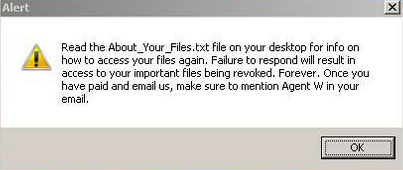
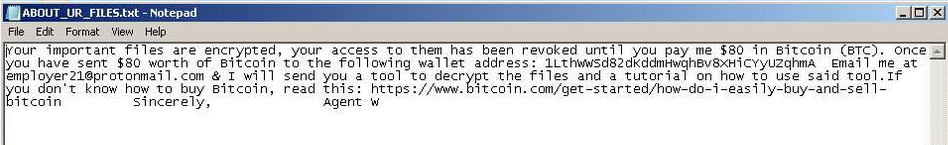
Malware type: ransomware
File type: PE 32 bit
File name: polisen.exe
Compiler: The ransomware is written in Go
Malware family: unknown, it's a new variant
Extension: .VAGGEN
E-Mail: employer21@protonmail.com
Note: ABOUT_UR_FILES.txt
BTC: 1LthWWSd82dKddmHwqhBv8XHiCYyUZqhmA --> link to blockchain
Go build ID: "VhhQ1UuEs3GW9JKPQlxr/KprNrDUoWKeN0_4zmFd8/dAiZDE9z9QKTx20ba5as/lfKWFUWyhFMg8VVGN2TT"
-----BEGIN RSA TESTING KEY-----
MIICXgIBAAKBgQDuLnQAI3mDgey3VBzWnB2L39JUU4txjeVE6myuDqkM/uGlfjb9
SjY1bIw4iA5sBBZzHi3z0h1YV8QPuxEbi4nW91IJm2gsvvZhIrCHS3l6afab4pZB
l2+XsDulrKBxKKtD1rGxlG4LjncdabFn9gvLZad2bSysqz/qTAUStTvqJQIDAQAB
AoGAGRzwwir7XvBOAy5tM/uV6e+Zf6anZzus1s1Y1ClbjbE6HXbnWWF/wbZGOpet
3Zm4vD6MXc7jpTLryzTQIvVdfQbRc6+MUVeLKwZatTXtdZrhu+Jk7hx0nTPy8Jcb
uJqFk541aEw+mMogY/xEcfbWd6IOkp+4xqjlFLBEDytgbIECQQDvH/E6nk+hgN4H
qzzVtxxr397vWrjrIgPbJpQvBsafG7b0dA4AFjwVbFLmQcj2PprIMmPcQrooz8vp
jy4SHEg1AkEA/v13/5M47K9vCxmb8QeD/asydfsgS5TeuNi8DoUBEmiSJwma7FXY
fFUtxuvL7XvjwjN5B30pNEbc6Iuyt7y4MQJBAIt21su4b3sjXNueLKH85Q+phy2U
fQtuUE9txblTu14q3N7gHRZB4ZMhFYyDy8CKrN2cPg/Fvyt0Xlp/DoCzjA0CQQDU
y2ptGsuSmgUtWj3NM9xuwYPm+Z/F84K6+ARYiZ6PYj013sovGKUFfYAqVXVlxtIX
qyUBnu3X9ps8ZfjLZO7BAkEAlT4R5Yl6cGhaJQYZHOde3JEMhNRcVFMO8dJDaFeo
f9Oeos0UUothgiDktdQHxdNEwLjQf7lJJBzV+5OtwswCWA==
-----END RSA TESTING KEY-----
Library referenced:

 github.com
Did not see any indication of wallpaper change in any.run. But there is a wallpaper seen in a screenshot referenced by this tweet.
github.com
Did not see any indication of wallpaper change in any.run. But there is a wallpaper seen in a screenshot referenced by this tweet.
Library referenced:

 github.com
Indication that XXTEA encryption algorithm is used
github.com
Indication that XXTEA encryption algorithm is used
Class/Function names:
This is not a fully detailed analysis, because that would take days to do. Instead I write all things down I can assess quickly.
Analysis of Downloader
Sample: VirusTotal
File type: Office Open XML document
Malware type: downloader
File name: UBC-COVID19-Survey-Mandatory.docx
After unpacking with 7zip you can find those images in word/media/:
The detection names suggest use of CVE-2017-0199.
Description of the CVE is consistent with the behaviour in any.run which shows winword.exe as doing the download and execute.
Contacted URLs by winword.exe:
hxxp://canarytokens(.)com/about/d4yeyvldfg6bn5y29by4e9fs3/post(.)jsp
hxxp://isrg.trustid.ocsp.identrust(.)com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D
Persistence for the downloaded file:
schtasks.exe /create /sc minute /mo 3 /tn "Internet Explorer Error Handling" /tr %APPDATA%\Byxor\polisen.exe
Analysis of Downloaded file
Sample:
File type: PE 32 bit
File name: polisen.exe
Compiler: The ransomware is written in Go
Malware family: unknown, it's a new variant
Extension: .VAGGEN
E-Mail: employer21@protonmail.com
Note: ABOUT_UR_FILES.txt
BTC: 1LthWWSd82dKddmHwqhBv8XHiCYyUZqhmA --> link to blockchain
Go build ID: "VhhQ1UuEs3GW9JKPQlxr/KprNrDUoWKeN0_4zmFd8/dAiZDE9z9QKTx20ba5as/lfKWFUWyhFMg8VVGN2TT"
-----BEGIN RSA TESTING KEY-----
MIICXgIBAAKBgQDuLnQAI3mDgey3VBzWnB2L39JUU4txjeVE6myuDqkM/uGlfjb9
SjY1bIw4iA5sBBZzHi3z0h1YV8QPuxEbi4nW91IJm2gsvvZhIrCHS3l6afab4pZB
l2+XsDulrKBxKKtD1rGxlG4LjncdabFn9gvLZad2bSysqz/qTAUStTvqJQIDAQAB
AoGAGRzwwir7XvBOAy5tM/uV6e+Zf6anZzus1s1Y1ClbjbE6HXbnWWF/wbZGOpet
3Zm4vD6MXc7jpTLryzTQIvVdfQbRc6+MUVeLKwZatTXtdZrhu+Jk7hx0nTPy8Jcb
uJqFk541aEw+mMogY/xEcfbWd6IOkp+4xqjlFLBEDytgbIECQQDvH/E6nk+hgN4H
qzzVtxxr397vWrjrIgPbJpQvBsafG7b0dA4AFjwVbFLmQcj2PprIMmPcQrooz8vp
jy4SHEg1AkEA/v13/5M47K9vCxmb8QeD/asydfsgS5TeuNi8DoUBEmiSJwma7FXY
fFUtxuvL7XvjwjN5B30pNEbc6Iuyt7y4MQJBAIt21su4b3sjXNueLKH85Q+phy2U
fQtuUE9txblTu14q3N7gHRZB4ZMhFYyDy8CKrN2cPg/Fvyt0Xlp/DoCzjA0CQQDU
y2ptGsuSmgUtWj3NM9xuwYPm+Z/F84K6+ARYiZ6PYj013sovGKUFfYAqVXVlxtIX
qyUBnu3X9ps8ZfjLZO7BAkEAlT4R5Yl6cGhaJQYZHOde3JEMhNRcVFMO8dJDaFeo
f9Oeos0UUothgiDktdQHxdNEwLjQf7lJJBzV+5OtwswCWA==
-----END RSA TESTING KEY-----
Library referenced:
reujab/wallpaper
A cross-platform Golang library for getting and setting desktop wallpapers - reujab/wallpaper
Library referenced:
xxtea/xxtea-go
XXTEA encryption algorithm library for Golang. Contribute to xxtea/xxtea-go development by creating an account on GitHub.
Class/Function names:
- main.KILLME
- main.TVINGAMIG
- main.RINGAHUSET
- main.main
Last edited:
