I'll give Foxit a go then since we use it at work and get it from the Microsoft Store. Foxit MobilePDF works on WIndows 10 laptop right? Is it better or more secure than the free one from it's website?I am not sure if Adobe Reader DC (it is not the UWP app in AppContainer) can be safer than Foxit Reader. The first has the Attack Surface much bigger even if you use the AppContainer setting for Adobe Reader DC. Did you try Foxit MobilePDF?
Hard_Configurator - Windows Hardening Configurator
- Thread starter Andy Ful
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Foxit MobilePDF is a free PDF viewer. It is a Universal Windows Platform app fully in AppContainer. It is much safer than the desktop version but also has fewer features.I'll give Foxit a go then since we use it at work and get it from the Microsoft Store. Foxit MobilePDF works on WIndows 10 laptop right? Is it better or more secure than the free one from it's website?
Use Settings option to adjust the app.

Buy Foxit MobilePDF - Microsoft Store
Download this app from Microsoft Store for Windows 10, Windows 10 Mobile, Windows 10 Team (Surface Hub), HoloLens. See screenshots, read the latest customer reviews, and compare ratings for Foxit MobilePDF.
www.microsoft.com
If the malicious PDF can exploit the reader and run something, then there are several ways to get Internet access. You do not need the web browser for that.
If one does not want to open URLs embedded in the document and the Reader does not alert opening the URLs, then Exploit Protection can be used to block child processes.
Other reason why I use OSA:

F
ForgottenSeer 85179
Or just use Windows internal "EMET" aka anti exploit protection.
also did you really use XP? Or is this a theme? I hope it's a theme.
Ah and your "moon" browser doesn't have a good sandbox and also miss important maintaining
Or just use Windows internal "EMET" aka anti exploit protection.
also did you really use XP? Or is this a theme? I hope it's a theme.
Ah and your "moon" browser doesn't have a good sandbox and also miss important maintaining
It's XP.
With XP the sandbox browser is not important, especially if the FS is FAT32 like mine.
Study the reason in my 3D of the security configuration.
P.S.
What do you mean?
I would not go too OT in this 3D can we continue the discussion in my 3D of the Security Configuration?
Last edited:
Please guys, this thread is far away from Windows XP and @Sampei Nihira config.It's not always easy to put an app from the Microsoft Store on the anti-exploit list.
Often the name of the app is different from the executable.
Make sure you have this aspect under control.
View attachment 234638
I'm probably going to try out the beta next week or wait for stable. Is it best to do an uninstall of the previous version first or will it upgrade and replace the old profile?
Eric
Eric
Install the new version and press <Recommended Settings>. This will replace the previous restrictions and will preserve your whitelisting entries, ConfigureDefender settings, and FirewallHardening settings.I'm probably going to try out the beta next week or wait for stable. Is it best to do an uninstall of the previous version first or will it upgrade and replace the old profile?
Eric
If you do not use many custom whitelisting rules and you use the old H_C version, then it is simpler to uninstall H_C and install the new version. Next, use <ConfigureDefender> and <Firewall Hardening> options to set non-default protection.
Some posts on GitHub and MT motivated me to find a way to apply changes in SRP settings in H_C without logging off the account or refreshing Explorer. After some testing, it turned out that adding/removing the protected file extension from <Designated File Types> did the job.
I am testing this for several days and it works without any issue from Windows Vista to Windows 10.
The only exception is when one changes <Enforcement> settings, which still require logging off or refreshing Explorer. But, the H_C Recommended Settings and all H_C profiles (except "ALL OFF") use in fact "Skip DLLs" setting - so, there is no problem.
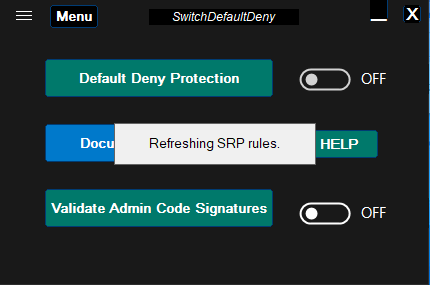
So, in the next beta version after pressing <APPLY CHANGES> button, the splash window will be usually displayed (for 1.5 s), to inform the user that SRP rules were refreshed.
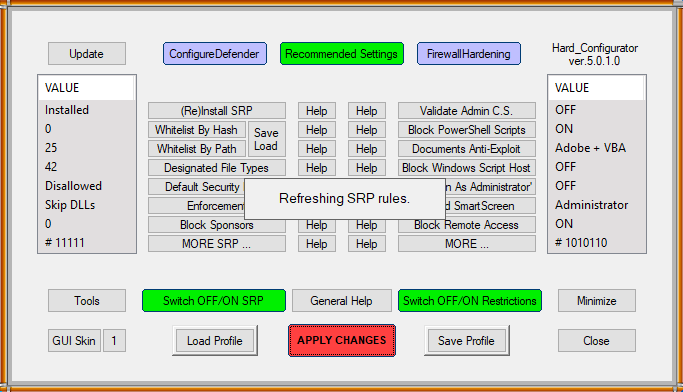
I also added the Explzh archiver support to H_C.
I am testing this for several days and it works without any issue from Windows Vista to Windows 10.
The only exception is when one changes <Enforcement> settings, which still require logging off or refreshing Explorer. But, the H_C Recommended Settings and all H_C profiles (except "ALL OFF") use in fact "Skip DLLs" setting - so, there is no problem.
So, in the next beta version after pressing <APPLY CHANGES> button, the splash window will be usually displayed (for 1.5 s), to inform the user that SRP rules were refreshed.
I also added the Explzh archiver support to H_C.
Last edited:
@Andy Ful
You could check the SMB rule.
It seems to me that it is not possible to return to OFF after applying an ON1 (or ON123?) rule.
TH.
You could check the SMB rule.
It seems to me that it is not possible to return to OFF after applying an ON1 (or ON123?) rule.
TH.
It is usually not possible on Windows 10, because SMB1 is uninstalled (so it is automatically disabled). The OFF setting means that SMB1, SMB2, and SMB3 are enabled (default setting on older Windows 10 and prior Windows versions). The ON1 setting means that SMB2 and SMB3 are enabled (SMB1 is disabled). The ON123 setting means that al SMB is disabled (see <Disable SMB> help).@Andy Ful
You could check the SMB rule.
It seems to me that it is not possible to return to OFF after applying an ON1 (or ON123?) rule.
TH.
Last edited:
TH.
Got it, so there is only 1 option on W.10:
disabling the SMB2+3 protocols.
In light of this new vulnerability SMBv3 would you recommend this setting on a non-business PC?
SMB2 and 3 are somehow integrated with Windows, so they have to be disabled together. If not needed, then they should be disabled. The SMB protocol can be used by some devices like for example NAS. But, it is not easy to use SMB vulnerabilities in the home environment due to the router NAT.
TH.
Got it, so there is only 1 option on W.10:
disabling the SMB2+3 protocols.
In light of this new vulnerability SMBv3 would you recommend this setting on a non-business PC?
Thanks again for your availability.
I noticed that disabling the 2 protocols requires restarting the pc.
I noticed that disabling the 2 protocols requires restarting the pc.
Yes. If you will change <Disable SMB> settings, then after pressing <APPLY CHANGES> button H_C should display the alert.Thanks again for your availability.
I noticed that disabling the 2 protocols requires restarting the pc.
F
ForgottenSeer 85179
Better use the work around from Microsoft until they publish the update which fix the vulnerability
TH.
Got it, so there is only 1 option on W.10:
disabling the SMB2+3 protocols.
In light of this new vulnerability SMBv3 would you recommend this setting on a non-business PC?
H_C uses the method described for SMB in the article:

After applying it, the user can check if SMB v2/v3 is disabled by using PowerShell:
Get-SmbServerConfiguration | Select EnableSMB2Protocol
Disabling SMB2 disables automatically also SMB3.

Detect, enable, and disable SMBv1, SMBv2, and SMBv3 in Windows
See various ways to detect, enable, and disable the Server Message Block (SMB) protocol (SMBv1, SMBv2, and SMBv3) in Windows client and server environments.
docs.microsoft.com
After applying it, the user can check if SMB v2/v3 is disabled by using PowerShell:
Get-SmbServerConfiguration | Select EnableSMB2Protocol
Disabling SMB2 disables automatically also SMB3.
Is Chromium Edge the best browser to run alongside H_C or does it not matter if you have the WD addon say in Chrome or FF? Just curious.
F
ForgottenSeer 85179
Only Chromium Edge can be most secure configured in anti exploit protection.Is Chromium Edge the best browser to run alongside H_C or does it not matter if you have the WD addon say in Chrome or FF? Just curious.
Firefox also doesn't have the sandbox Chromium and chrome have.
For H_C none of that is important
You may also like...
-
-
FAI Tells It Like It Is - Microsoft's Wonky Default Deny Roadmaps, Users as Guinea Pigs, "Dilemmas and Paradoxes," and Why SRP Remains King
- Started by ForgottenSeer 114717
- Replies: 44
-
Microsoft testing Windows 11 batch file security improvements
- Started by Parkinsond
- Replies: 0
-
Malware News CrySome RAT : An Advanced Persistent .NET Remote Access Trojan
- Started by Khushal
- Replies: 3
-
