$42 seems reasonably doable. I rarely reboot, and IIRC you need to reboot all the time when using this type of software, in order to keep a "clean" & update version ready to reboot into. yes??It's costly likely USD $41.99 for one workstation for 1 year. It's not for regular users.
App Review K7 Total Security 2024
- Thread starter Shadowra
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
It is advised to take all reviews with a grain of salt. In extreme cases some reviews use dramatization for entertainment purposes.
- Content created by
- Shadowra
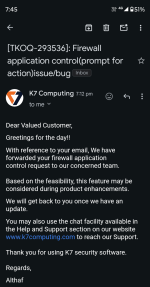
Great news
Yes i finally reproduced this and indeed a bug in their firewall application control module for prompt for action. I don't use this option so i was not experienced with this. I always use Deny Access. Thanks for sharing thisShadowDefender does not work on Win11 24H2 (at least not w/o workaround by the time i upgraded), and i do not have a VM employed, so i stopped testing, but I'm pretty sure the issue persists.
If you have a VM, you might want to double-check, simply get a bunch of scriptors from MlwrBazaar (abusech), and remove wscript and and others from the rules list. Once trying to call out, they should appear, being autotrusted (prompt for action setting in firewall).
Yes i finally reproduced this and indeed a bug in their firewall application control module for prompt for action. I don't use this option so i was not experienced with this. I always use Deny Access. Thanks for sharing this@Dreams&Visions Hope they (K7) fixed it As soon as possible.
Last edited by a moderator:
On the one hand, I kinda support the idea to autoallow trusted services, however, this should be limited to Windows Update related services IMO.@Dreams&Visions what's your takes on it.
I've blocked explorer.exe in Evorim Free Firewall as well as in K7 (in K7 manually, it was trusted; wscript.exe nor powershell weren't active yet, it would result in a firewall alert by Evorim), and did not observe any inconvenience so far.
IMO K7 should not make a difference whether a file is trusted or not if the user decides to switch to "prompt for action". IDK why they disabled "Learn mode", I once asked, I do not remember the full answer, but they did not state a reason, but they told me it is disabled in Home user environment - which is obvious.
P.S. As far as I remember, QuickHeal 's firewall module works similar, it also does autoallow certain processes.
As for scriptors, I threw some on the only machine still at Win10 w/ SD yesterday, powershell might have called out, however, one script was shut down doing something with powershell by the BB (suspicious program). The others did autoclose instantly after run. It was #lockbit. Seems all were droppers, unlike #netwalker, which hollowed explorer.exe to perform encryption as per my observation and was hard to tackle.
Last edited:
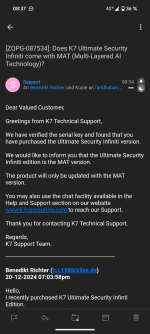
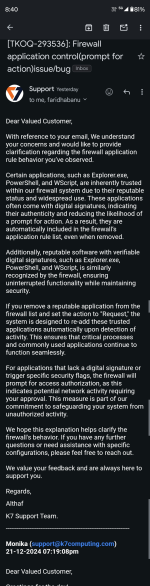
Wow, they're pretty responsive lately! Hopefully they will implement your requestGood news from K7 team! Answer of my mail View attachment 286944
Thank you for sharing @Captain Awesome!
This, and
this are reasons I respect K7. They do indeed seem dedicated and responsive, as @Dreams&Visions posted.
BTW, how is performance machine-wise?
Very stable and impact is low on system.This, and
this are reasons I respect K7. They do indeed seem dedicated and responsive, as @Dreams&Visions posted.
BTW, how is performance machine-wise?
Considering buying a license because i have to have every single AV program hahaha.
Go ahead...Considering buying a license because i have to have every single AV program hahaha.
do they still have the infinity edition where you pay one time for a lifetime and is it the same as ultimate security?Go ahead...
Yes, K7 Ultimate Security Infiniti Edition | Lifetime Validity Antivirusdo they still have the infinity edition where you pay one time for a lifetime and is it the same as ultimate security?
As for your question: see post #42 (yes, it's the same as the Ultimate version (with their machine learning module MAT, i asked staff on that), plus it covers 5 devices of choice (see FAQs on the product page of Infiniti):
- Which K7 antivirus is covered by the Infiniti Offer?
This is an antivirus bundle that protects any 5 Windows, Mac, Android, or iOS devices i.e., you can protect 5 Windows devices or 2 Windows + 1 iPhone + 1 iPad + 1 Android device or any other combination of 5 devices. The one-time payment gives you feature and malware definition updates for all 5 devices.
OK, I took the plunge and installed the trial version of K7 TS. 




If you try K7 use with my config.See #32 postOK, I took the plunge and installed the trial version of K7 TS.
Impressive!View attachment 286961
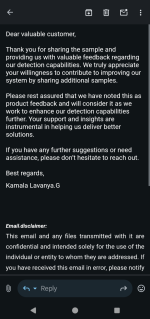
Regarding Scripts & Others injection detection of K7. They are doing great in feedbacks of users. Most Antivirus company never communicated with their users.
I hope it isn't just hot air, however, being a long-time user of K7, I've clearly seen improvements, which I cannot say about the product it replaced, which I was using mainly because of it's VPN. They simply added detections, or did rely on their 3rd-party signatures (though updates were broken from time to time, and well documented on their forum). They never replied to any submission, feedback in their forum was mainly provided by users. I don't want to flame / rant about, I think it is clear which product I'm talking about, and I see it dying with the current transformation, which is a pity.
Hope for the bestImpressive!
I hope it isn't just hot air, however, being a long-time user of K7, I've clearly seen improvements, which I cannot say about the product it replaced, which I was using mainly because of it's VPN. They simply added detections, or did rely on their 3rd-party signatures (though updates were broken from time to time, and well documented on their forum). They never replied to any submission, feedback in their forum was mainly provided by users. I don't want to flame / rant about, I think it is clear which product I'm talking about, and I see it dying with the current transformation, which is a pity.
You may also like...
-
App Review K7 Ultimate Security 2026
- Started by Shadowra
- Replies: 8
-
App Review K7 Ultimate Security 2025
- Started by Shadowra
- Replies: 40
-
App Review QuickHeal Total Security 2026
- Started by Shadowra
- Replies: 13
-
App Review Norton 360 Deluxe 2026
- Started by Shadowra
- Replies: 23
-
App Review F-Secure Internet Security 2026
- Started by Shadowra
- Replies: 21