Hi Everybody,
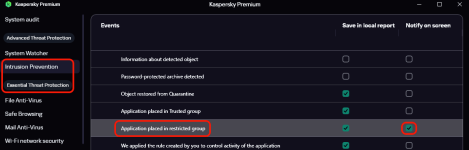
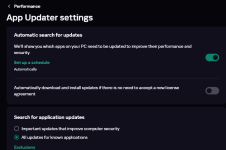
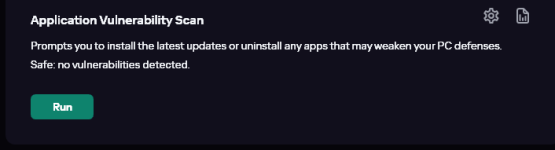
Just got my hands on Kaspersky Plus a few days ago. The reason I bought it is for it's ability to stop Process Injection / Memory Injection. Picus's 2026 Red Report says process injection attacks occurs in ~30% of all the malware it studied (1.1 million) So I think it is high noon that they be stopped. Another reasson I bought K is because it has App Updater which is vulnerability scanning I hope, because I don't like running Nessus with Administrator rights.
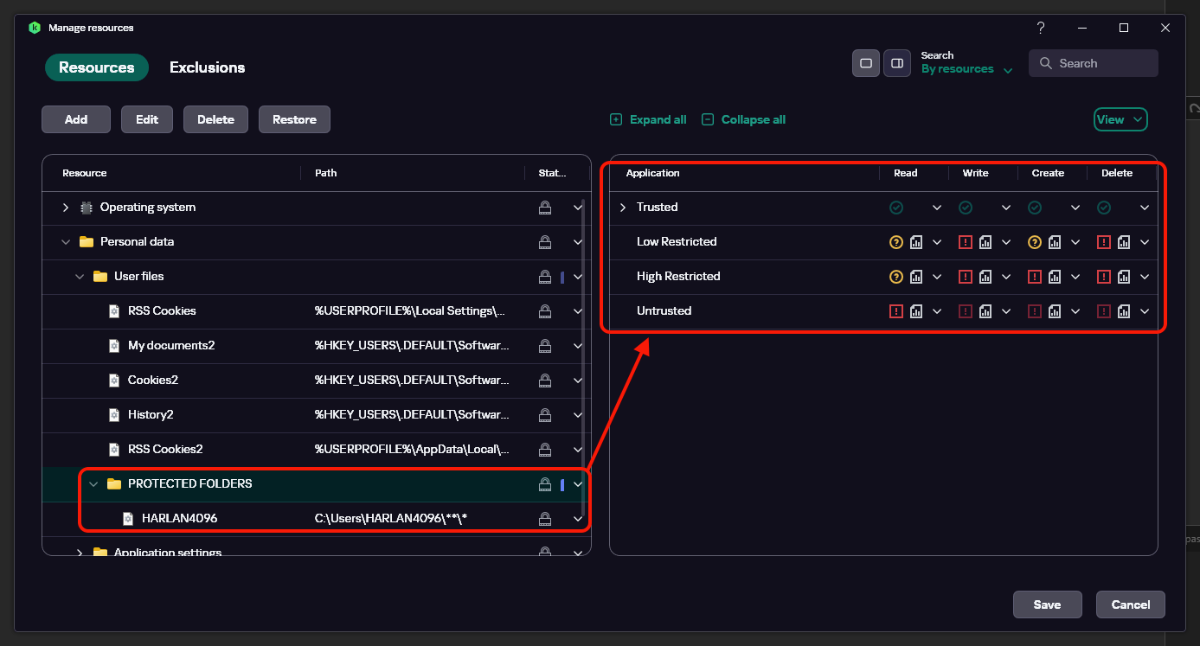
So I did what AppGuard does - stop injection originating from Office and PDF apps which has macros, javascript, vbscript what not.
Then I stopped networking for Office, Macrium, Intel apps, other useless driver related apps. Only allowing updaters and browsers network access.
What else do you guys configure ?
Just got my hands on Kaspersky Plus a few days ago. The reason I bought it is for it's ability to stop Process Injection / Memory Injection. Picus's 2026 Red Report says process injection attacks occurs in ~30% of all the malware it studied (1.1 million) So I think it is high noon that they be stopped. Another reasson I bought K is because it has App Updater which is vulnerability scanning I hope, because I don't like running Nessus with Administrator rights.
So I did what AppGuard does - stop injection originating from Office and PDF apps which has macros, javascript, vbscript what not.
Then I stopped networking for Office, Macrium, Intel apps, other useless driver related apps. Only allowing updaters and browsers network access.
What else do you guys configure ?
Last edited: