@Andy Ful
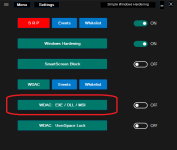
Last time I beg you, please run WDAC with (in smart mode)
1. Allow Microsoft + ISG (ISG is sort of similar to SAC)
2. Explicit allow rules for
a) Program Files
b Program files (x86)
c) Users\Admin\Apdata
d) Users\Admin\Local\temp
3. Microsoft advised block Rules for User space and kernel
4. SWH (SRP blocking risky file extensions and allowing exe, msi. tmp)
5. fall back to Audit mode when a driver fails to load
6. Exclude dynamic code and scripts (I told you so

)
This is really a huge improvement for most home users in terms of security, while it allows for most programs updates.
Your version is as strong as the UAC protection of 2 C and 2 D, so allowing ISG (which is similar to SAC) does not weaken it substantionally, only increasing useability. You provided us with excellent freebies (H_C, CD, SWH), I really have no idea why you would provide such a complex hybride hardening. I don't understand the logic behind it (when you allow UAC holes, you might as well add ISG). Normally I can follow you and applaude your tweaks, but you got me lost here.
Don't be offended, but I would propose three levels of protection
a) Basic (only old SWH)
b) Smart (as I outlined above)
c) Deny all (block all in user folders)
With option B and C the user additionally has an option to exclude user folders