lol. Swatting bugs is so fun.For the fun !
Who has already played with new W10 security features?
- Thread starter Windows_Security
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
You don't have to bypass it when you can can inject into explorer and then do what you wish to do.now the real bet is how long before someone bypass it ?
Good you pointed that out.You don't have to bypass it when you can can inject into explorer and then do what you wish to do.
It's a mistake for people to think that protected folders is total protection from ransomware. Because if ransomware hides its identity by injecting itself into a trusted process, protected folders won't help.
D
Deleted member 178
You don't have to bypass it when you can can inject into explorer and then do what you wish to do.
Which is a bypass to meGood you pointed that out.
It's a mistake for people to think that protected folders is total protection from ransomware. Because if ransomware hides its identity by injecting itself into a trusted process, protected folders won't help.
I was using the secure folders for a few days because I thought it's at least "basic protection" without whitelisting everything important. When you activate the secure folders, an information appears that you don't have to manually add your programs to the trusted list because Windows will check them automatically and allow them if they're trusted.
It sounds nice, but at the end it was just annoying. When I downloaded something with Firefox, I got many notifications that Windows prevented a potentially malicious action because I was trying to save the file at my desktop. I couldn't save anything with any programs on my computer to secure folders actually, even though Microsoft says that well known software will be allowed automatically. That prevented developing with XAMPP also, because out of curiosity I added my developement folder to the secure folders.
I thought this behavior exists to prevent drive-by downloads and similar, but somehow I could save anything to the downloads folder, even though this one was also protected by default.
At the end I even got notifications without doing anything because some Windows processes tried to access some folders I added to the secure folders.
Maybe they'll improve it in the future, but right now it's just annoying because I even got these warning notifications after I added my programs to the whitelist.
It sounds nice, but at the end it was just annoying. When I downloaded something with Firefox, I got many notifications that Windows prevented a potentially malicious action because I was trying to save the file at my desktop. I couldn't save anything with any programs on my computer to secure folders actually, even though Microsoft says that well known software will be allowed automatically. That prevented developing with XAMPP also, because out of curiosity I added my developement folder to the secure folders.
I thought this behavior exists to prevent drive-by downloads and similar, but somehow I could save anything to the downloads folder, even though this one was also protected by default.
At the end I even got notifications without doing anything because some Windows processes tried to access some folders I added to the secure folders.
Maybe they'll improve it in the future, but right now it's just annoying because I even got these warning notifications after I added my programs to the whitelist.
Here is a nice article to get an overview of the new security features...
6 new and noteworthy security features in Windows 10 Fall Creators Update
6 new and noteworthy security features in Windows 10 Fall Creators Update
F
ForgottenSeer 55474
Hey, not me I would not dare, because my PC knowledge is very little, so none of that!
Nice article.Here is a nice article to get an overview of the new security features...
6 new and noteworthy security features in Windows 10 Fall Creators Update
I remember some promises from MS to improve Windows Defender sandboxing, because some kernel vulnerabilities were discovered a few months ago.
Looks like that fix didn't happen.
D
Deleted member 178
UAC was kind of annoying for certain people, i think they will cry on the floor because:
- Protected folders = need a reboot
- Turning on/off mitigation = need a reboot
i don't know what are the purpose of the insiders, if they can't make MS understand that such basic stuff are real annoyance.
- Protected folders = need a reboot
- Turning on/off mitigation = need a reboot
i don't know what are the purpose of the insiders, if they can't make MS understand that such basic stuff are real annoyance.
Also, this is very intresting (C/P from Wilders):
Windows Defender Is Becoming the Powerful Antivirus That Windows 10 Needs
Also remember the four features in Windows Defender Exploit Guard : Exploit Protection, Attack Surface Reduction rules, Network Protection and Controlled Folder Access.
Exploit Protection and Controlled Folder Access you can set up directly in the Windows Defender Security Center UI.
Attack Surface Reduction rules and Network Protection needs to be configured through Group Policy or PowerShell.
"A real world example of Attack Surface Reduction rules blocking a exploit from being able to use a vulnerability in the critical time up until a patch becomes available :
https://blogs.technet.microsoft.com...t-for-cve-2017-8759-detected-and-neutralized/"
Windows Defender Is Becoming the Powerful Antivirus That Windows 10 Needs
Also remember the four features in Windows Defender Exploit Guard : Exploit Protection, Attack Surface Reduction rules, Network Protection and Controlled Folder Access.
Exploit Protection and Controlled Folder Access you can set up directly in the Windows Defender Security Center UI.
Attack Surface Reduction rules and Network Protection needs to be configured through Group Policy or PowerShell.
"A real world example of Attack Surface Reduction rules blocking a exploit from being able to use a vulnerability in the critical time up until a patch becomes available :
https://blogs.technet.microsoft.com...t-for-cve-2017-8759-detected-and-neutralized/"
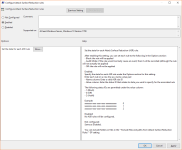
I am running EMET, which Exploit Protection is based on, and it comes with templates. I will screenshot the EMET settings from Chrome, which is on their "popular software" template:Would it be good to add a browser (eg Chrome) to Exploit Protection> Program Settings?
View attachment 170287
If it is added, do you still need to adjust something? What?
It looks like they added a default/deny level of protection. How do ya like that.CFA block something when Chrome is installed:
View attachment 170283
This is one new settings - Zero Tolerance
View attachment 170284
This is second new settings - Block dangerous sites/domains
View attachment 170285
Also, set Win Defender update to every 1h
View attachment 170286
I like it, just need to do some test but can't find the free time...
I would like to someone (@cruelsister) test all this new settings set to max
I would like to someone (@cruelsister) test all this new settings set to max
+1 !!!I like it, just need to do some test but can't find the free time...
I would like to someone (@cruelsister) test all this new settings set to max
You don't have to bypass it when you can can inject into explorer and then do what you wish to do.
Well protected folder is simply one of the new security features Microsoft has implemented.Good you pointed that out.
It's a mistake for people to think that protected folders is total protection from ransomware. Because if ransomware hides its identity by injecting itself into a trusted process, protected folders won't help.
I assume this combine with attack surface reduction and exploit protection should have all users covered.
It all has these great-sounding names, but...Well protected folder is simply one of the new security features Microsoft has implemented.
I assume this combine with attack surface reduction and exploit protection should have all users covered.
Windows_Security
Level 24
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Thx to blog ov AV-comparatives Spotlight on security: New Windows 10 security features - AV-Comparatives Weblog I now the En-US names for the exploit features
No it is more, I added extra protections Office and Alpbelli Photobook:
Disable extension points
Disables various extensibility mechanisms that allow DLL injection into all processes, such as AppInit DLLs, window hooks, and Winsock service providers.
Do not allow child processes
Prevents an app from creating child processes.
Exploit Guard is just EMET integrated into Windows.
No it is more, I added extra protections Office and Alpbelli Photobook:
Disable extension points
Disables various extensibility mechanisms that allow DLL injection into all processes, such as AppInit DLLs, window hooks, and Winsock service providers.
Do not allow child processes
Prevents an app from creating child processes.
Last edited:
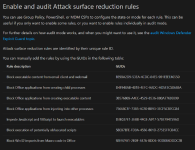
One more useful tweak in GPE - Attack Surface Reduction
You have to add some CODE for blocking witch can be found here:
Enable ASR rules individually to protect your organization
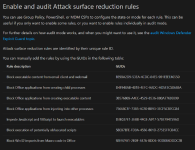
You have to add some CODE for blocking witch can be found here:
Enable ASR rules individually to protect your organization
You may also like...
-
S
-
New Update Windows 11 24H2 KB5060829 June non-security update
- Started by Gandalf_The_Grey
- Replies: 0
-
New Update Google rolling out auto-restart security feature to Android
- Started by Gandalf_The_Grey
- Replies: 0