After making several successful POCs and submitting them to Microsoft, I noticed the first signs of Defender's behavior-based detections. One of the executables involved in the UAC bypass is recognized as malicious (I did not submit it to Microsoft). That is good. But, after doing some unimportant changes in the code, the POC works again. Defender suspends two executables and checks them against the cloud backend. Next, the POC disables Defender successfully and runs a payload. I have also sent a message via LinkedIn to Cole Sodja (see the last Security Unlocked podcast) about this MT thread. It seems that Microsoft works on the "Automating threat actor tracking" to determine the scope of the compromise and predict how the attack will progress:
Of course, "threat actors" are related to APT groups in the wild, so I do not think that someone from Microsoft will be interested in our thread (which is about the danger of the possible attack method). The interesting thing about this attack method is that the attacker can adjust the malware with minimum telemetry send to Microsoft. All files used in the attack (before disabling Defender) are not malicious and the attack can be detected only when the attack context is understood (it is not for now).
I did not submit the POC with UAC bypass yet. I am curious if Microsoft will be able to recognize from telemetry that something successfully bypasses UAC to disable Defender (it would be welcome). Usually, such bypasses are not urgent to Microsoft.
Automating threat actor tracking: Understanding attacker behavior for intelligence and contextual alerting | Microsoft Security Blog
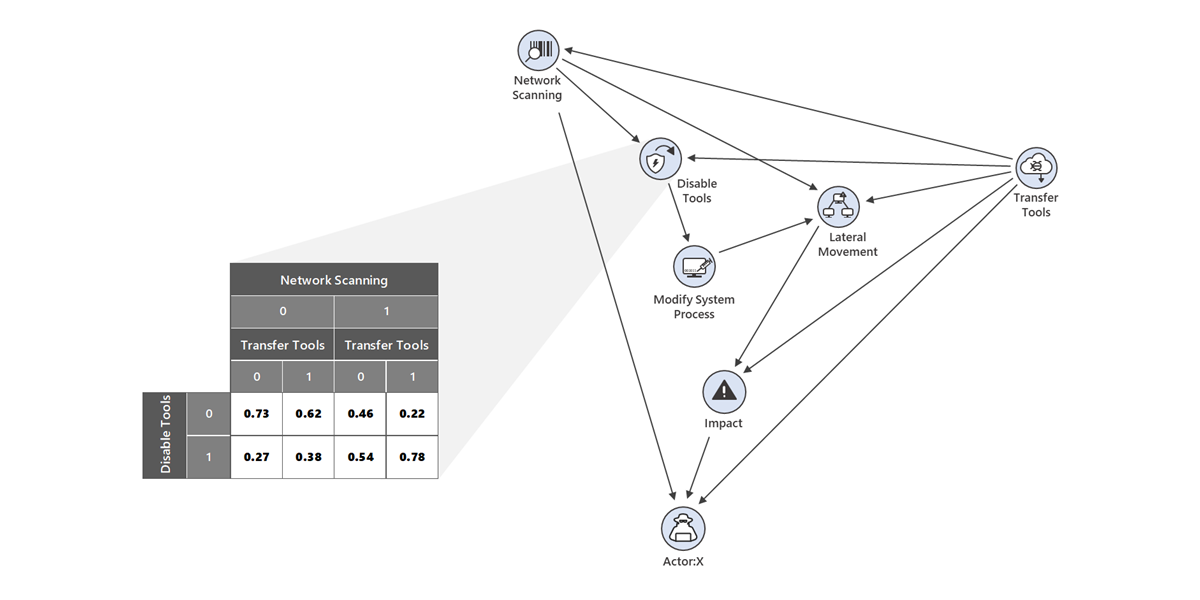
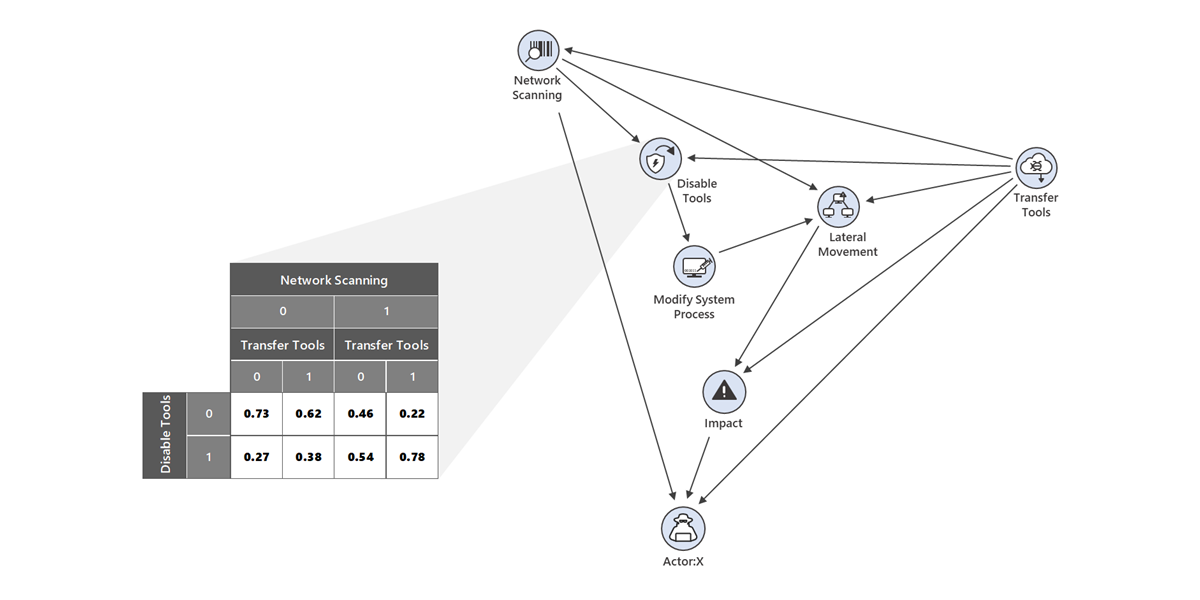
A probabilistic graphical modeling framework used by Microsoft 365 Defender research and intelligence teams for threat actor tracking enables us to quickly predict the likely threat group responsible for an attack, as well as the likely next attack stages.
www.microsoft.com
Of course, "threat actors" are related to APT groups in the wild, so I do not think that someone from Microsoft will be interested in our thread (which is about the danger of the possible attack method). The interesting thing about this attack method is that the attacker can adjust the malware with minimum telemetry send to Microsoft. All files used in the attack (before disabling Defender) are not malicious and the attack can be detected only when the attack context is understood (it is not for now).
I did not submit the POC with UAC bypass yet. I am curious if Microsoft will be able to recognize from telemetry that something successfully bypasses UAC to disable Defender (it would be welcome). Usually, such bypasses are not urgent to Microsoft.
Last edited:

