CryptXXX 3.0 is a file-encrypting ransomware, which will encrypt the personal documents found on victim’s computer using RSA-2048 key (AES CBC 256-bit encryption algorithm), appending the .crypz extension to encrypted files. CryptXXX 3.0 then displays a message which offers to decrypt the data if a payment of about 2.4 bitcoins, or approximately $1,000 USD is made.
06 June 2016: We cannot help your recover your files, and we can only recommend that you use ShadowExplorer or (free) file recovery software to restore your documents. This guide was written to help you remove the infection itself, and if a 100% proven method to recover the encrypted files is found, we will update this guide.
At this moment, there is no decryptor available for the CryptXXX 3.0 ransomware. However, you can try to search these webpages for updates: https://decrypter.emsisoft.com/ or https://id-ransomware.malwarehunterteam.com/
1. How did the CryptXXX 3.0 virus got on my computer?
2. What is CryptXXX 3.0 Ransomware?
3. Is my computer infected with CryptXXX 3.0 virus?
4. Is it possible to decrypt files encrypted by CryptXXX 3.0?
5. How to remove the CryptXXX 3.0 ransomware (Virus Removal Guide)
6. How to prevent your computer from becoming infected by CryptXXX 3.0
1. How did the CryptXXX 3.0 ransomware got on my computer?
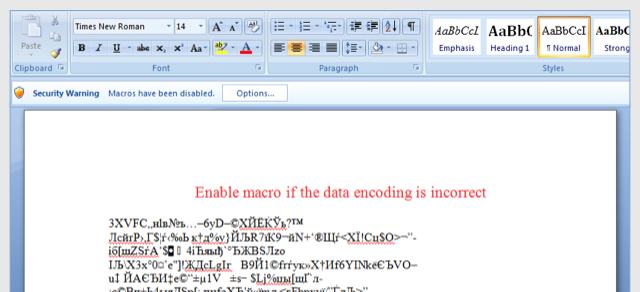
The CryptXXX 3.0 ransomware is distributed via spam email containing infected attachments or links to malicious websites. Cyber-criminals spam out an email, with forged header information, tricking you into believing that it is from a shipping company like DHL or FedEx. The email tells you that they tried to deliver a package to you, but failed for some reason. Sometimes the emails claim to be notifications of a shipment you have made. Either way, you can’t resist being curious as to what the email is referring to – and open the attached file (or click on a link embedded inside the email). And with that, your computer is infected with the CryptXXX 3.0 ransomware.
2. What is CryptXXX 3.0 Ransomware?
The CryptXXX 3.0 ransomware targets all versions of Windows including Windows 7, Windows 8 and Windows 10. This infection is notable due to how it encrypts the user’s files – namely, it uses AES-265 and RSA encryption method – in order to ensure that the affected user has no choice but to purchase the private key.
When the CryptXXX 3.0 ransomware is first installed on your computer it will create a random named executable in the %AppData% or %LocalAppData% folder. This executable will be launched and begin to scan all the drive letters on your computer for data files to encrypt.
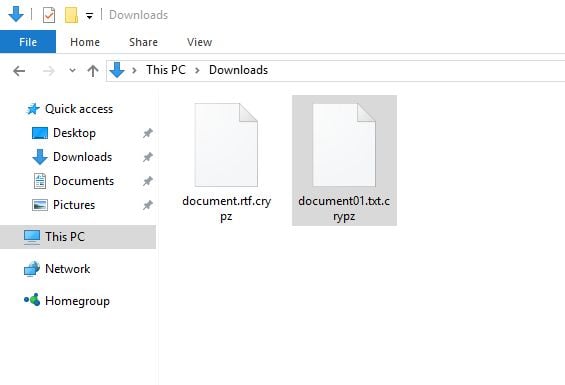
CryptXXX 3.0 ransomware searches for files with certain file extensions to encrypt. The files it encrypts include important productivity documents and files such as .doc, .docx, .xls, .pdf, among others. When these files are detected, this infection will change the extension to .crypz, so they are no longer able to be opened.
Files targeted are those commonly found on most PCs today; a list of file extensions for targeted files include:
.sql, .mp4, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mov, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm, .vcf, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .dba, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, wallet, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c, .p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt
Once your files are encrypted with the .crypz exntesion, the CryptXXX 3.0 ransomware will create the !Recovery_[victim_id].txt text files ransom note in each folder that a file has been encrypted and on the Windows desktop. The ransomware will also change your Windows desktop wallpaper to !Recovery_[victim_id].png.
These files are located in every folder that a file was encrypted as well as in the user’s Startup folder so that they are automatically displayed when a user logs in. These files will contain the information on how to access the payment site and get your files back.
When the infection has finished scanning your computer it will also delete all of the Shadow Volume Copies that are on the affected computer. It does this so that you cannot use the shadow volume copies to restore your encrypted files.
3. Is my computer infected with CryptXXX 3.0 virus?
When CryptXXX 3.0 infects your computer it will scan all the drive letters for targeted file types, encrypt them, and then append the .crypz extension to them. Once these files are encrypted, they will no longer able to be opened by your normal programs. When CryptXXX 3.0 has finished encrypting the victim’s files, it will change the desktop wallpaper to an image that acts like a ransom note. It will also display a HTML ransom note in your default browser. These ransom notes include instructions on how to connect to the CryptXXX Decrypt Service where you can learn more about what happened to your files and how you can make a CryptXXX ransom payment.
The messages displayed by this ransomware infection can be localized depending on the user’s location, with text written in the appropriate language.
This the message that the CryptXXX 3.0 ransomware may display:
@@@@@@@ NOT YOUR LANGUAGE? USE //translate.google.com @@@@@@@ What happened to your files ?
@@@@@@@ All of your files were protected by a strong encryption with RZA4096
@@@@@@@ More information about the en-Xryption keys using RZA4096 can be found here: http://en.wikipedia.org/wiki/RSA_(cryptosystem) @@@@@@@ How did this happen ?
@@@@@@@ !!! Specially for your PC was generated personal RZA4096 Key , both publik and private.
@@@@@@@ !!! ALL YOUR FILES were en-Xrypted with the publik key, which has been transferred to your computer via the Internet.
@@@@@@@ !!! Decrypting of your files is only possible with the help of the privatt key and de-crypt program , which is on our Secret Server @@@@@@@ What do I do ?
@@@@@@@ So , there are two ways you can choose: wait for a miracle and get your price doubled, or start obtaining BITCOIN NOW! , and restore your data easy way
@@@@@@@ If You have really valuable data, you better not waste your time, because there is no other way to get your files, except make a payment
Your personal ID: xxxxxxxxxxxxxxxx For more specific instructions, please visit your personal home page, there are a few different addresses pointing to your page below: 1 – http://2zqnpdpslpnsqzbw.onion.to
2 – http://2zqnpdpslpnsqzbw.onion.cab
3 – http://2zqnpdpslpnsqzbw.onion.city If for some reasons the addresses are not available, follow these steps: 1 – Download and install tor-browser: http://www.torproject.org/projects/torbrowser.html.en
2 – After a successful installation, run the browser
3 – Type in the address bar – http://2zqnpdpslpnsqzbw.onion
4 – Follow the instructions on the site Be sure to copy your personal ID and the instruction link to your notepad not to lose them.
4. Is it possible to decrypt files encrypted by CryptXXX 3.0?
No, at this time it’s not possible to recover the files encrypted by the CryptXXX 3.0 ransomware.
CryptXXX 3.0 is notable due to how it encrypts the user’s files – namely, it uses AES-265 and RSA encryption method – in order to ensure that the affected user has no choice but to purchase the private key. The RSA public key can only be decrypted with its corresponding private key. Since the AES key is hidden using RSA encryption and the RSA private key is not available, decrypting the files is not feasible as of this writing.
Brute forcing the decryption key is not realistic due to the length of time required to break an AES encryption key. Unfortunately, once the CryptXXX 3.0 encryption of the data is complete, decryption is not feasible without paying the ransom.
Because the needed private key to unlock the encrypted file is only available through the cyber criminals, victims may be tempted to purchase it and pay the exorbitant fee. However, doing so may encourage these bad guys to continue and even expand their operations. We strongly suggest that you do not send any money to these cyber criminals, and instead address to the law enforcement agency in your country to report this attack.
Restore your files encrypted by CryptXXX 3.0 ransomware with recovery software
In some cases, it may be possible to recover previous versions of the encrypted files using System Restore or other recovery software used to obtain “shadow copies” of files.
Option 1: Restore your files encrypted by CryptXXX 3.0 ransomware with ShadowExplorer
CryptXXX 3.0 will attempt to delete all shadow copies when you first start any executable on your computer after becoming infected. Thankfully, the infection is not always able to remove the shadow copies, so you should continue to try restoring your files using this method.
- You can download ShadowExplorer from the below link:
SHADOW EXPLORER DOWNLOAD LINK (This link will open a new web page from where you can download “ShadowExplorer”) - Once you have downloaded and installed ShadowExplorer, you can follow the below video guide on how to restore your files while using this program.
Alternatively, you can use the System Restore to try to recover the encrypted documents.
Option 2: Restore your files encrypted by CryptXXX 3.0 ransomware with File Recovery Software
When CryptXXX 3.0 encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you can use file recovery software such as:
- Recuva
You can follow the below guide on how to use Recuva:
- EaseUS Data Recovery Wizard Free
- R-Studio
5. How to remove the CryptXXX 3.0 ransomware (Virus Removal Guide)
It’s important to understand that by starting the removal process you risk losing your files, as we cannot guarantee that you will be able to recover them. Furthermore, your files may be permanently compromised when trying to remove this infection or trying to recover the encrypted documents.
This page is a comprehensive guide, which will remove the CryptXXX 3.0 infection from your computer, however we cannot guarantee that your personal files will be recovered. We cannot be held responsible for losing the documents during this removal process.
A. Remove CryptXXX 3.0 ransomware from your computer
Malwarebytes and HitmanPro can detect and remove this infection, but these programs cannot recover your encrypted files due to the nature of asymmetric encryption, which requires a private key to decrypt files encrypted with the public key.
STEP 1: Remove CryptXXX 3.0 virus with Malwarebytes Anti-Malware Free
Malwarebytes Anti-Malware Free uses industry-leading technology to detect and remove all traces of malware, including worms, Trojans, rootkits, rogues, dialers, spyware, and more.
It is important to note that Malwarebytes Anti-Malware works well and should run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download “Malwarebytes Anti-Malware Free”) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup” to start the installation of Malwarebytes Anti-Malware.

 You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation. - When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.
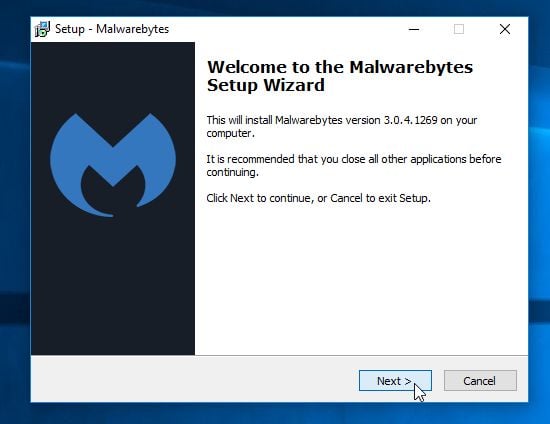
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
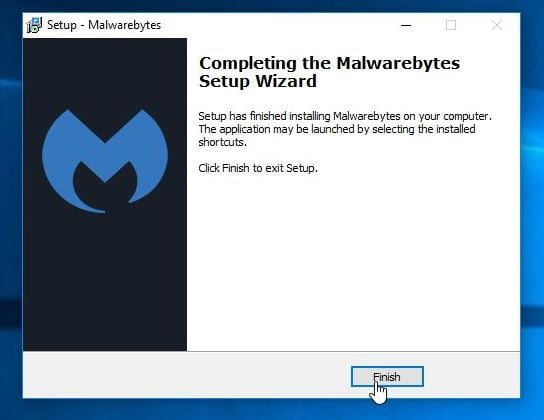
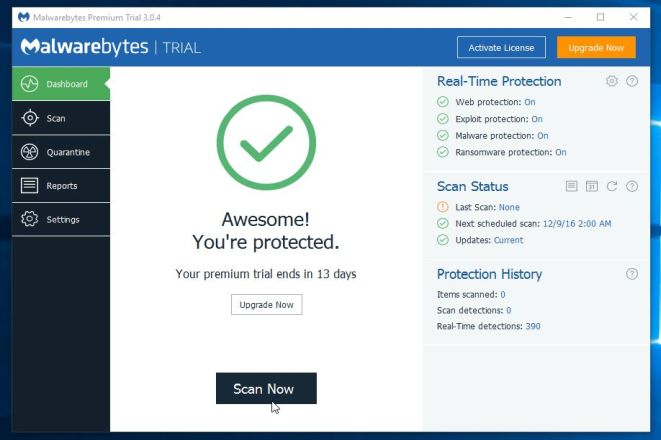
- Once installed, Malwarebytes Anti-Malware will automatically start and you will see a message stating that you should update the program, and that a scan has never been run on your system. To start a system scan you can click on the “Scan Now” button.
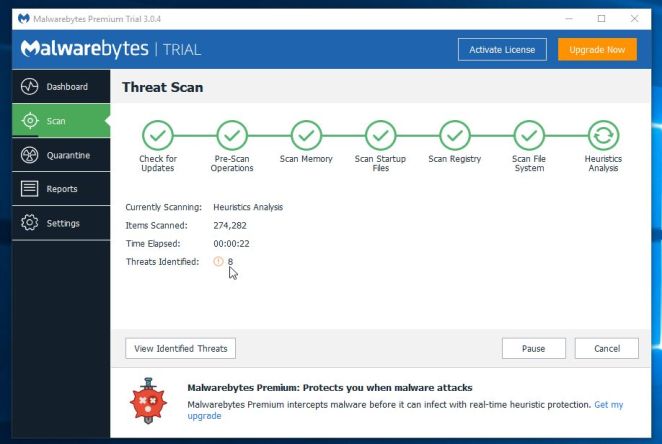
- Malwarebytes Anti-Malware will now start scanning your computer for malware. When Malwarebytes Anti-Malware is scanning it will look like the image below.
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Remove Selected” button.
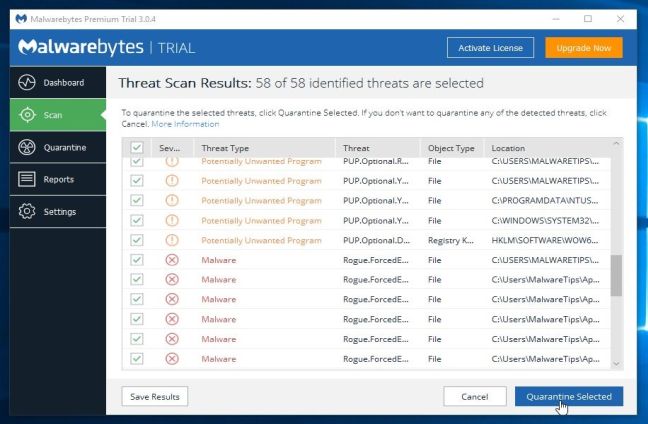
Please note that the infections found may be different than what is shown in the image. - Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
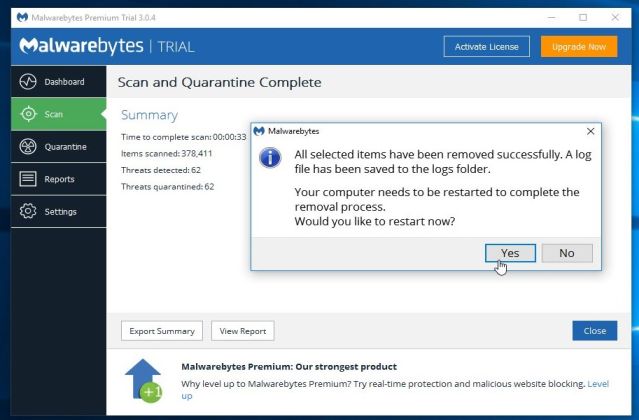
After your computer will restart, you should open Malwarebytes Anti-Malware and perform another “Threat Scan” scan to verify that there are no remaining threats
STEP 2: Double-check for the CryptXXX 3.0 malware infection with HitmanPro
HitmanPro is a second opinion scanner, designed to rescue your computer from malware (viruses, trojans, rootkits, etc.) that have infected your computer despite all the security measures you have taken (such as anti-virus software, firewalls, etc.). HitmanPro is designed to work alongside existing security programs without any conflicts. It scans the computer quickly (less than 5 minutes) and does not slow down the computer.
- You can download HitmanPro from the below link:
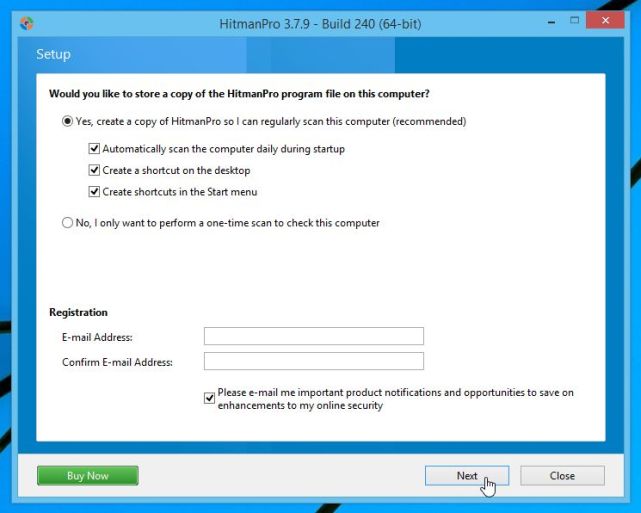
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.

Click on the “Next” button, to install HitmanPro on your computer.
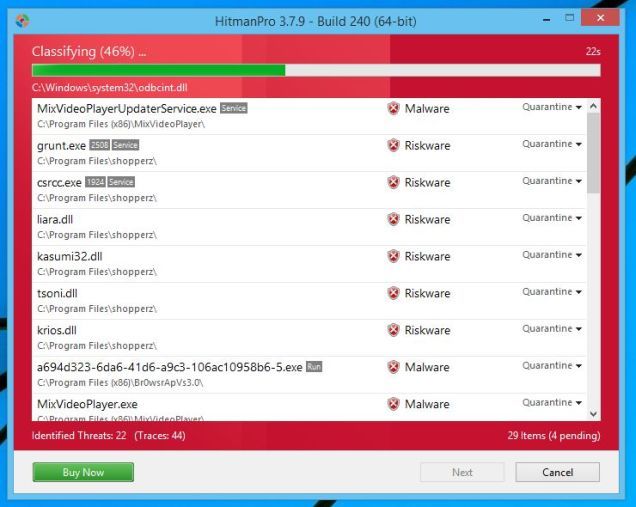
- HitmanPro will now begin to scan your computer for CryptXXX 3.0 malicious files.
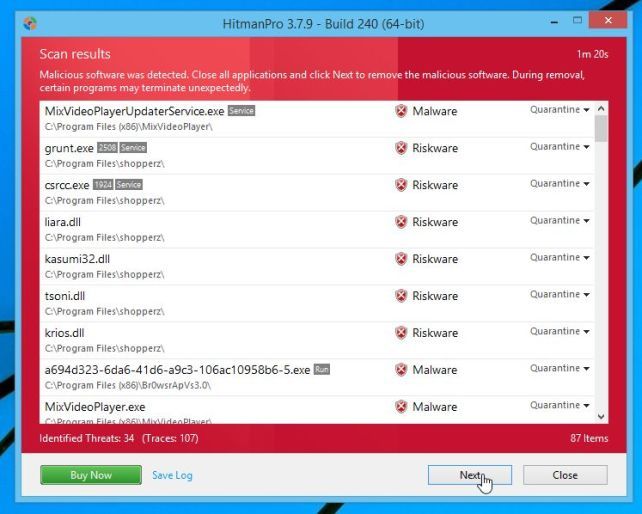
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove CryptXXX 3.0 virus.
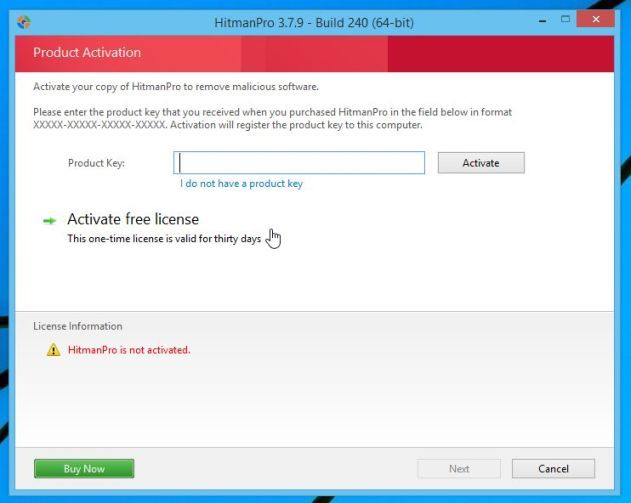
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
How to prevent your computer from becoming infected by CryptXXX 3.0
To protect your computer from the Cryptowall ransomware, you should always have an antivirus installed on your computer and always have a backup for your personal documents. As an extra protection method, you can use programs called HitmanPro.Alert or CryptoPrevent, which will prevent any file encrypting malware from running.
Your computer should now be free of the CryptXXX 3.0 ransomware infection.
If you are still experiencing problems while trying to remove virus from your machine, please do one of the following:
- Run a system scan with Emsisoft Emergency Kit.
- Start a new thread in our Malware Removal Assistance forum.


