- Feb 4, 2016
- 2,520
source (bleepingcomputer.com): Firefox Master Password System Has Been Poorly Secured for the Past 9 Years
For at past nine years, Mozilla has been using an insufficiently strong encryption mechanism for the "master password" feature.
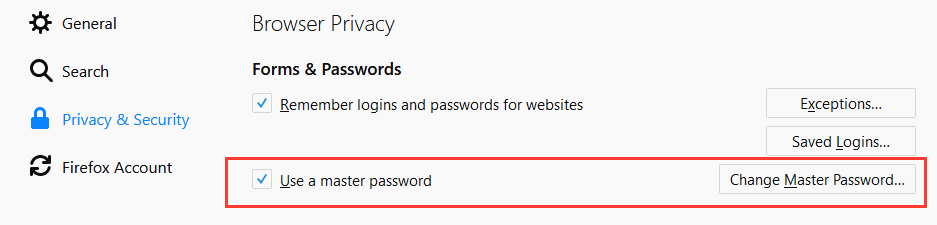
Both Firefox and Thunderbird allow users to set up a "master password" through their settings panel. This master password plays the role of an encryption key that is used to encrypt each password string the user saves in his browser or email client.
Experts have lauded the feature because up until that point browsers would store passwords locally in cleartext, leaving them vulnerable to malware or attackers with physical access to a victim's computer.
But Wladimir Palant, the author of the AdBlock Plus extension, says the encryption scheme used by the master password feature is weak and can be easily brute-forced.
Master password encryption uses low SHA1 iteration count
"I looked into the source code," Palant says, "I eventually found the sftkdb_passwordToKey() function that converts a [website] password into an encryption key by means of applying SHA-1 hashing to a string consisting of a random salt and your actual master password."
"Anybody who ever designed a login function on a website will likely see the red flag here," Palant says


