What do you mean by "... could have interacted ..."?Is it possible the C_D setting to warn on vulnerable signed drivers could have interacted with the old driver?
Hard_Configurator - Windows Hardening Configurator
- Thread starter Andy Ful
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Installed H_C v6.0.0.0 beta1 over the top v5.1.1.2 on Windows 10 x64, and without any problems, thank!https://github.com/AndyFul/Hard_Configurator/raw/master/H_C_6_beta1.exe This beta version can be installed over the previous version (5.1.1.2).
I understand that this is just the beginning of a new version, but what are the plans for a stable release?
This beta will be close to the stable version. I am focused on making it fully compatible with Windows 11. Some changes in ConfigureDefender are possible too.Installed H_C v6.0.0.0 beta1 over the top v5.1.1.2 on Windows 10 x64, and without any problems, thank!
I understand that this is just the beginning of a new version, but what are the plans for a stable release?
H_C does not protect firewall rules. The rules made specifically by H_C (can be seen in the FirewallHardening BlockList) are protected by the system. They require high privileges and system reboot to apply changes.H_C protects firewall rules from creating new rules or modifying existing rules by applications with elevated privileges (as admin)?
Thank! I guess it's hard to make all existing firewall rules protected so that programs from the admin can't create their own rules? That would be a very strong hardening.H_C does not protect firewall rules.
F
ForgottenSeer 85179
You can archive that with limited/ restricted Windows accountThank! I guess it's hard to make all existing firewall rules protected so that programs from the admin can't create their own rules? That would be a very strong hardening.
It is not possible via Windows native hardening (Administrative Windows Firewall Policies). One could create 3rd party driver to monitor Windows Firewall rules and prevent changing them by high privileged malware. But, even such protection can be bypassed when the attacker knows the protective driver.Thank! I guess it's hard to make all existing firewall rules protected so that programs from the admin can't create their own rules? That would be a very strong hardening.
Another solution is already included in H_C. It simply tries to prevent malware execution.
No malware execution = No malicious changes
Last edited:
I wondered if the outdated WiFi driver had been silently blocked by the ASR rule. Even though Microsoft says the 2018 driver was the "best" driver, I manually installed the latest one from Intel, which is 3 years newer. I look forward to installing the next version of C_D by itself to rule out any problem with that component, and if that's OK, I'll try the non-beta H_C 6.What do you mean by "... could have interacted ..."?
Yes. It is possible when using MAX or custom ConfigureDefender settings (although Defender alerts about blocked action). In the HIGH or INTERACTIVE settings, you should see an alert with the option to unblock the action. But, this should not end with crashing. Anyway, this ASR rule is new, so we cannot know it for sure.I wondered if the outdated WiFi driver had been silently blocked by the ASR rule. Even though Microsoft says the 2018 driver was the "best" driver, I manually installed the latest one from Intel, which is 3 years newer. I look forward to installing the next version of C_D by itself to rule out any problem with that component, and if that's OK, I'll try the non-beta H_C 6.
Edit.
The unblock option does not mean that the installation will continue. The user has to make the installation again in one day. After 24 hours it will be blocked again.
Last edited:
This weekend I replaced the desktop of an aunt from Windows7 to Windows10. Because NVT SysHardener is not maintained I decided to use Hard_Configurator to replace SysHardener with following settings:
Default allow SRP with some hardening:
- blocking scripts sponsors
- protecting Windows folders
- documents Anti-Exploit (VBA)
- protect mail clients
- harden SMB
- elevate only signed programs
- disable Windows Script
- block powershell scripts
Additional manual hardening
Furthermore I disabled command and scripts with registry editor. I also disable mshta.exe by enabling all possible Exploit Protections in MD app& browser control plus I enable code integrity guard for Explorer and Edge. In the Firewall rules I enable blocking all sponsors except explorer.exe (I thought that Explorer needs outbound connection for smart screen?). I also set Configure_Defender on Max.
Question to @Andy Ful
Would you please make disabling commands and scripts an extra option in the MORE ... (right column hardening of H_C). By hiding this in the MORE hardening options, you could set it default to enabled. I know disabling command should only be done on a Vanilla Windows10 install (no need for third party to enable stuff through commands). I have disabled cmd.exe since Microsoft replaced it as default command shell (link).
P.S.
I always install a cheap digital license Office Home&Student version. MD with the ASR rules enabled by ConfigureDefender is in my opinion the best anti-virus for use with M$Office.
Default allow SRP with some hardening:
- blocking scripts sponsors
- protecting Windows folders
- documents Anti-Exploit (VBA)
- protect mail clients
- harden SMB
- elevate only signed programs
- disable Windows Script
- block powershell scripts
Additional manual hardening
Furthermore I disabled command and scripts with registry editor. I also disable mshta.exe by enabling all possible Exploit Protections in MD app& browser control plus I enable code integrity guard for Explorer and Edge. In the Firewall rules I enable blocking all sponsors except explorer.exe (I thought that Explorer needs outbound connection for smart screen?). I also set Configure_Defender on Max.
Question to @Andy Ful
Would you please make disabling commands and scripts an extra option in the MORE ... (right column hardening of H_C). By hiding this in the MORE hardening options, you could set it default to enabled. I know disabling command should only be done on a Vanilla Windows10 install (no need for third party to enable stuff through commands). I have disabled cmd.exe since Microsoft replaced it as default command shell (link).
P.S.
I always install a cheap digital license Office Home&Student version. MD with the ASR rules enabled by ConfigureDefender is in my opinion the best anti-virus for use with M$Office.
Last edited:
Almost, except points 9 and 10 in the changelog.@Andy Ful
Is beta of stand alone Configure Defender identical to the configure defender of Hard_Configurator beta?
It is not Explorer that needs an outbound connection for SmartScreen. Non of LOLBins in FH can disturb SmartScreen.In the Firewall rules I enable blocking all sponsors except explorer.exe (I thought that Explorer needs outbound connection for smart screen?).
Your proposition is OK, but I do not plan changes for now. For most users, it will not be better than the current layout. One can easily see that scripts are blocked.Question to @Andy Ful
Would you please make disabling commands and scripts an extra option in the MORE ... (right column hardening of H_C). By hiding this in the MORE hardening options, you could set it default to enabled.
Please check if the options marked in green are properly set in your setup.
Nowadays, abusing some other LOLBins (Bitsadmin, Finger, MSBuild, Wmic, etc.) is also a common event. In your setup, the shortcuts are not blocked, so most LOLBins can still be abused. More natural would be blocking Sponsors by the Enhanced option in <Block Sponsors>.
You should consider blocking shortcuts to enhance the protection.
Last edited:
@Andy Ful
RE: Explorer: - Ok, thx will block explorer outbound also.
Re: Sponsors: I have 23 blocked
RE: blocking CMD.exe and scripts: As I read the right column H_C is only blocking powershell scripts (ps1) and windows scripts (vbs, wsf etc). Are bat and cmd-scripts already blocked also (your quote " One can easily see that scripts are blocked")
RE: Explorer: - Ok, thx will block explorer outbound also.
Re: Sponsors: I have 23 blocked
RE: blocking CMD.exe and scripts: As I read the right column H_C is only blocking powershell scripts (ps1) and windows scripts (vbs, wsf etc). Are bat and cmd-scripts already blocked also (your quote " One can easily see that scripts are blocked")
Last edited:
In your H_C setup, the scripting is restricted except *.bat and *.cmd scripts that can still be run. These scripts are blocked in H_C only in the default-deny setup. Blocking the Sponsor cmd.exe blocks only the command lines that use cmd.exe (that is how Microsoft created CMD). Anyway, you have written "I disabled command and scripts with registry editor", so I assume that you have applied the right reg tweak:@Andy Ful
RE: Explorer: - Ok, thx will block explorer outbound also.
RE: blocking CMD.exe and scripts: As I read the right column H_C is only blocking powershell scripts (ps1) and windows scripts (vbs, wsf etc). Are bat and cmd-scripts already blocked also (your quote " One can easily see that scripts are blocked")
HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\System
DisableCMD REG_DWORD 1
This has to be repeated on each user account where CMD is going to be blocked.
Why do you keep unrestricted shortcuts?@Andy Ful
RE: Explorer: - Ok, thx will block explorer outbound also.
Re: Sponsors: I have 23 blocked
RE: blocking CMD.exe and scripts: As I read the right column H_C is only blocking powershell scripts (ps1) and windows scripts (vbs, wsf etc). Are bat and cmd-scripts already blocked also (your quote " One can easily see that scripts are blocked")
I think that you could simply apply the profile Windows_10_Basic_Recommended_Settings and additionally:
Edit.
If you remove the file extensions from the Designated File Types, then you will get the equivalent of the settings from your previous post (*.bat and *.cmd scripts will be protected).
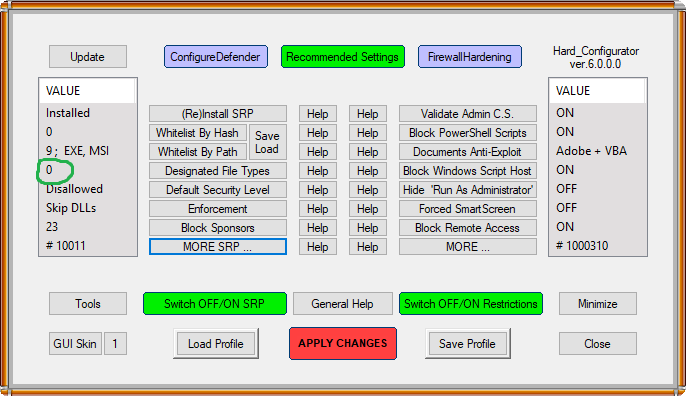
To protect also shortcuts you have to keep LNK file extension and set <Protecte Shortcuts> = ON
This setup is almost default-deny even when Default Security Level = Disallowed.
- Enhanced Sponsors + CMD
- Validate Admin C.S. = ON
- Block Windows Script Host = ON
- Disable SMB = ON123
Edit.
If you remove the file extensions from the Designated File Types, then you will get the equivalent of the settings from your previous post (*.bat and *.cmd scripts will be protected).
To protect also shortcuts you have to keep LNK file extension and set <Protecte Shortcuts> = ON
This setup is almost default-deny even when Default Security Level = Disallowed.
Last edited:
I've replaced built-in SRP with Hard_Configurator_6_Beta1, starting out with "Recommended Settings".
Thanks Andy
Thanks Andy
Last edited:
You may also like...
-
-
FAI Tells It Like It Is - Microsoft's Wonky Default Deny Roadmaps, Users as Guinea Pigs, "Dilemmas and Paradoxes," and Why SRP Remains King
- Started by ForgottenSeer 114717
- Replies: 44
-
Microsoft testing Windows 11 batch file security improvements
- Started by Parkinsond
- Replies: 0
-
Malware News CrySome RAT : An Advanced Persistent .NET Remote Access Trojan
- Started by Khushal
- Replies: 3
-