For me it changes the normal display to spoiled....
For me it changes a spoiled display to an normal looking one.
Hard_Configurator - Windows Hardening Configurator
- Thread starter Andy Ful
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
I moved the standalone versions of DocumentsAntiExploit and FirewallHardening to another GitHub repository. Together with standalone ConfigureDefender and RunBySmartscreen, all of these standalone tools are included in H_C_HardeningTools:
https://github.com/AndyFul/ConfigureDefender/blob/master/H_C_HardeningTools.zip
https://github.com/AndyFul/ConfigureDefender/blob/master/H_C_HardeningTools.zip
A user could use it to fix a spoiled display (not a working one). If it's working ok for a user he/she wouldn't look for a fix in the manual.For me it changes the normal display to spoiled.
We cannot be certain that this works as you think. It would be good if other users who have display problems with rescaled fonts, could test it.A user could use it to fix a spoiled display (not a working one). If it's working ok for a user he/she wouldn't look for a fix in the manual.
Thanks for your time and patience Andy. I just wanted to avoid that we talk past each other so I tried to phrase it clearer 
Unzipping that file raised an eyebrow from EAM:I moved the standalone versions of DocumentsAntiExploit and FirewallHardening to another GitHub repository. Together with standalone ConfigureDefender and RunBySmartscreen, all of these standalone tools are included in H_C_HardeningTools:
https://github.com/AndyFul/ConfigureDefender/blob/master/H_C_HardeningTools.zip
2020/05/24 10:30:57
Malware "Zum.Androm.1 (B)" detected and blocked on behalf of explorer.exe
Last edited:
Yes, it probably should block it. My programs are often blocked until I send them for whitelisting. These files are whitelisted by Avast and Windows Defender. I submitted them also to Symantec and Bitdefender, but these vendors do not send back-information about whitelisting.Unzipping that file raised an eyebrow from EAM:
2020/05/24 10:30:57
Malware "Zum.Androm.1 (B)" detected and blocked on behalf of explorer.exe
The CUP project is evolving. Here are some screenshots.
CUP with H_C (beta) Recommended Settings:
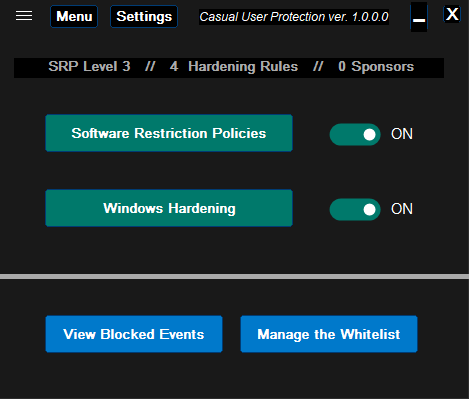
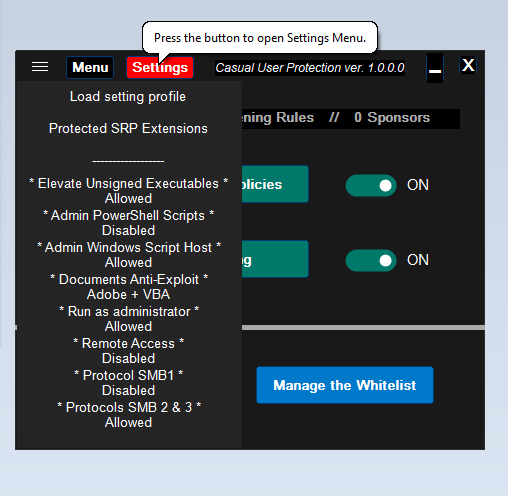
The 4 Hardening Rules can be explicitly seen (3 Disabled and 'Adobe + VBA').
When one chooses the hardening option, for example, * Admin Windows Script Host * then the alert is displayed:
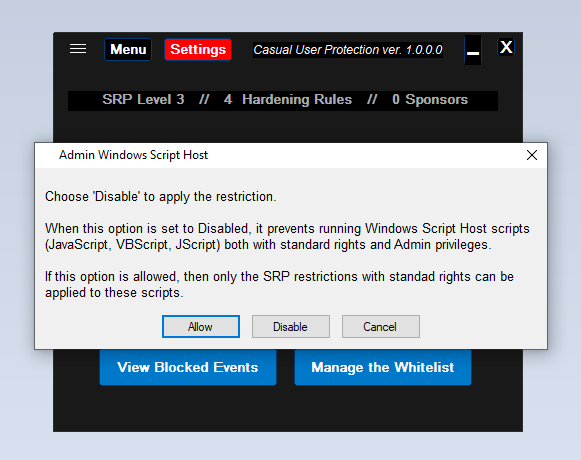
After choosing <Disable>, the * Admin Windows Script Host * setting changes to Disabled.
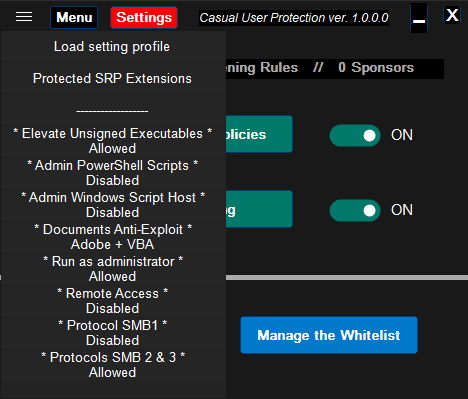
The number of Hardening Rules changes from 4 to 5.
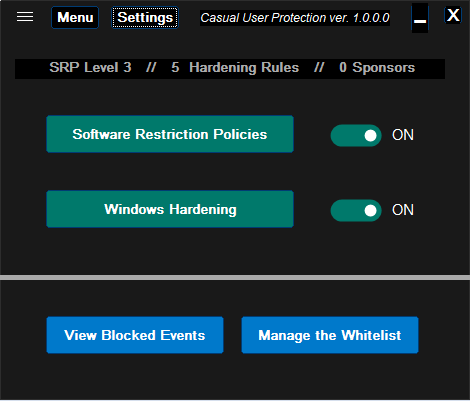
The "SRP Level" depends on EXE and MSI restrictions. It cannot be changed in CUP, but can be loaded via setting profile:
CUP with H_C (beta) Recommended Settings:
The 4 Hardening Rules can be explicitly seen (3 Disabled and 'Adobe + VBA').
When one chooses the hardening option, for example, * Admin Windows Script Host * then the alert is displayed:
After choosing <Disable>, the * Admin Windows Script Host * setting changes to Disabled.
The number of Hardening Rules changes from 4 to 5.
The "SRP Level" depends on EXE and MSI restrictions. It cannot be changed in CUP, but can be loaded via setting profile:
- Level 1 - EXE and MSI files not blocked (like in the H_C profile: Basic Recommended Settings).
- Level 2 - EXE files not blocked. MSI files blocked, except when in ProgramData or user AppData hidden folders (like in the H_C profile: Avast Hardened Mode Aggressive).
- Level 3 - EXE and MSI files blocked in UserSpace, except when in ProgramData or user AppData hidden folders (like in the H_C Recommended Settings).
- Level 4 - EXE and MSI files blocked in UserSpace (like in the H_C Strict Recommended Settings).
Last edited:
It's just my opinion...so don't shoot ... but the settings seem a bit confusing, at least for a non-geek / noob, I think it will be hard for them to choose which settings. I belive some predefined settings (profiles /Level 1 to 4) and a custom settings for advanced users will be more than enough.
... but the settings seem a bit confusing, at least for a non-geek / noob, I think it will be hard for them to choose which settings. I belive some predefined settings (profiles /Level 1 to 4) and a custom settings for advanced users will be more than enough.
Last edited:
I thought there would only be one setup - Level One - like Windows_Security option in H_C. This looks like it will be confusing for the truly casual user, who may not know anything about User Space, Program Data or AppData.
Agree with OS, if the intent of this is that casual users will be able to use and understand this then the simpler the better, Off/On, levels of protection, that's it, they don't need to have to try to figure out what should be allowed or disabled. Of course what do I know, Andy is the genius not I.
CUP will install with the Basic Recommended Settings, which have SRP Level 1 (EXE and MSI files not blocked) and some important Hardening Rules (like those from the previous post). There will be also a few predefined setting profiles (SRP Levels 1-4 with Hardening Rules) so the user will not usually need to tweak anything, just load the profile. One can consider these profiles as profiles with growing number of restrictions (from Level 1 to Level 4).It's just my opinion...so don't shoot... but the settings seem a bit confusing, at least for a non-geeek / noob, I think it will be hard for them to choose which settings. I belive some predefined settings (profiles /Level 1 to 4) and a custom settings for advanced users will be more than enough.
Anyway, there are some users who want to use PowerShell as Admin or like to prevent the elevation of unsigned executables, etc.. These users will have the ability to change the Hardening Rules. It is easy because there are only a few rules available.
I thought there would only be one setup - Level One - like Windows_Security option in H_C. This looks like it will be confusing for the truly casual user, who may not know anything about User Space, Program Data or AppData.
I think, that the term "Casual User Protection" may be misunderstood. The casual users should not touch anything that can be configured on Windows 10, because this would end not good for them. The casual user is a target for whom the hardened setup is made.Agree with OS, if the intent of this is that casual users will be able to use and understand this then the simpler the better, Off/On, levels of protection, that's it, they don't need to have to try to figure out what should be allowed or disabled. Of course what do I know, Andy is the genius not I.
The CUP is not intended to be configured by casual users, but by semi-advanced users on the computers of casual users. Of course, if the semi-advanced user wants, then he/she may configure his/her own computer too.
The CUP is a simpler version of Hard_Configurator - the H_C is intended for advanced users, because it is rather complex and requires some knowledge to create a sensible custom setup.
Last edited:
I had indeed (also) misunderstood.I think, that the term "Casual User Protection" may be misunderstood. The casual users should not touch anything that can be configured on Windows 10, because this would end not good for them. The casual user is a target for whom the hardened setup is made.
The CUP is not intended to be configured by casual users, but by semi-advanced users on the computers of casual users. Of course, if the semi-advanced user wants, then he/she may configure his/her own computer too.
The CUP is a simpler version of Hard_Configurator - the H_C is intended for advanced users, because it is rather complex and requires some knowledge to create a sensible custom setup.
Thanks for clarifying your meaning and intention of 'Casual User Protection' (CUP).
It is possible to make something even simpler, like CUP with only SRP Level 1 and predefined (not configurable) Hardening Rules for disabling remote access and SMB1 protocol. Anyway, there should be still some configurable Hardening Rules like disabling/enabling
* Run as administrator *, * Elevate Unsigned Executables*, and * Documents Anti-Exploit *.
* Run as administrator *, * Elevate Unsigned Executables*, and * Documents Anti-Exploit *.
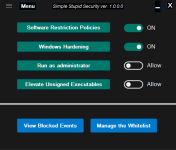
It would have the advantage to be a portable application. I have already the name for it:It is possible to make something even simpler, like CUP with only SRP Level 1 and predefined (not configurable) Hardening Rules for disabling remote access and SMB1 protocol. Anyway, there should be still some configurable Hardening Rules like disabling/enabling
* Run as administrator *, * Elevate Unsigned Executables*, and * Documents Anti-Exploit *.
Simple Stupid Security
I think, that it could work with SRP set to block the programs started with high privileges. It would be slightly stronger as compared to SysHardener default settings.
Last edited:
F
ForgottenSeer 85179
I would replace the "stupid" because of language.Simple Stupid Security
Even if the "kiss" principle use that term
I would replace the "stupid" because of language.
I have to agree with this. I know there are some that avoid software that use "unprofessional" language even if the functionality is perfect. The names "ConfigureDefender" and "Hard_Configurator" have a sense of professionalism and trust. Perhaps something like Simple Windows Security would fare better.
I'm going to be using it regardless of whatever you choose to call it since I love your work!
The name is not so important, but I really like it. So, we will see. I can always change the name to something like "Simple Windows Hardening", "Simple Windows Security", etc. I do not think that in the case of such an application, the name should be attractive. On the contrary, it should not. The user should use it, because of its protection and good reputation. In this way, there will be fewer disappointed users, who used it because they had anything better to do.
You may also like...
-
-
FAI Tells It Like It Is - Microsoft's Wonky Default Deny Roadmaps, Users as Guinea Pigs, "Dilemmas and Paradoxes," and Why SRP Remains King
- Started by ForgottenSeer 114717
- Replies: 44
-
Security News Microsoft testing Windows 11 batch file security improvements
- Started by Parkinsond
- Replies: 0
-
Malware News CrySome RAT : An Advanced Persistent .NET Remote Access Trojan
- Started by Khushal
- Replies: 3
-