- May 26, 2014
- 1,339
Guys, today I was just doing some tests with Windows Defender Testground website and I realized how mediocre some antivirus solutions actually are; let me explain below.
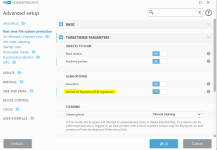
In this website there are some files to test if Windows Defender protection is working correctly. So I tried the CloudBlock file and noticed after execution that it shows a GUI similar of a Ransomware, but ofcourse without any functionality. (it just tests if cloud protection of WD is working)
I uploaded the sample at VirusTotal just for the lolz and noticed that many antivirus solutions detected it as if it was a real malware.
See here:
Cloud-delivered protection - Windows Defender Testground
Antivirus scan for cb49bb09669c7a55fe1963c73aefa940f7775ec4eb17f0044e0bdd68889c69ac at 2018-02-26 21:05:36 UTC - VirusTotal 28/66
So whats the problem with this?
The problem is that many antivirus players just copy Microsoft or Kaspersky signatures (Microsoft in this case) and it is done, no real research or advanced heuristics at play. I remember that some years ago Eugene Kaspersky complained about this and it seems that this situation still remains.
Serious guys, dont waste your money with those copycats, just use Comodo with @cruelsister settings or buy a real antimalware solution like Kaspersky or Emsisoft.
Ps: I am especially disappointed with ESET.
Ps 2: Pardon me for my english, I was at a hurry and it isnt my native language.
In this website there are some files to test if Windows Defender protection is working correctly. So I tried the CloudBlock file and noticed after execution that it shows a GUI similar of a Ransomware, but ofcourse without any functionality. (it just tests if cloud protection of WD is working)
I uploaded the sample at VirusTotal just for the lolz and noticed that many antivirus solutions detected it as if it was a real malware.
See here:
Cloud-delivered protection - Windows Defender Testground
Antivirus scan for cb49bb09669c7a55fe1963c73aefa940f7775ec4eb17f0044e0bdd68889c69ac at 2018-02-26 21:05:36 UTC - VirusTotal 28/66
So whats the problem with this?
The problem is that many antivirus players just copy Microsoft or Kaspersky signatures (Microsoft in this case) and it is done, no real research or advanced heuristics at play. I remember that some years ago Eugene Kaspersky complained about this and it seems that this situation still remains.
Serious guys, dont waste your money with those copycats, just use Comodo with @cruelsister settings or buy a real antimalware solution like Kaspersky or Emsisoft.
Ps: I am especially disappointed with ESET.
Ps 2: Pardon me for my english, I was at a hurry and it isnt my native language.
Last edited: