I have a ton of these, and have a pretty good balance in Win 10 Pro, some may remember me posting some here and there.
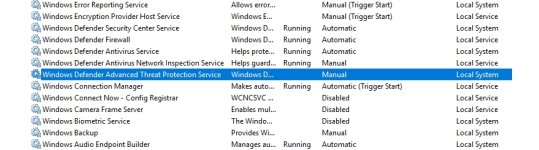
Things are changing, now MS is taking notice and at nearly every update of any importance resets "Services" that may have been user disabled, I used to notice it but not very often now I am seeing it more. kinda like how they reacted when you would remove one of the apps back in early Win10.
Wait for the list till after the Fall Update, and the first patch fix after that, then the list will have some new, and some wont work anymore (Most likely) so we could then skip having to re-edit it in such a short time.
Does that make sense ? I hope so lol
Things are changing, now MS is taking notice and at nearly every update of any importance resets "Services" that may have been user disabled, I used to notice it but not very often now I am seeing it more. kinda like how they reacted when you would remove one of the apps back in early Win10.
Wait for the list till after the Fall Update, and the first patch fix after that, then the list will have some new, and some wont work anymore (Most likely) so we could then skip having to re-edit it in such a short time.
Does that make sense ? I hope so lol