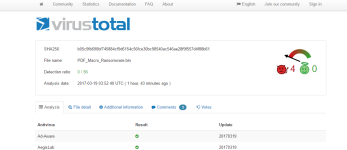
CryptoLocker file more than 40 hours in the wild but still undetected by AV's on VirusTotal (0/56)
- Thread starter GrujaRS
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
- May 7, 2016
- 1,287
Interesting.Do anyone have this ransomware sample post it on Malware Vault for SUD and test the BB.I don't test the AV but @Der.Reisende and othe av tester will check.More than 40 hours of virus circulating, and they enjoy the weekend!
For whom work AntiVirus company???
Whom they protect their clients or malware creators???
View attachment 143445
- Dec 27, 2014
- 3,423
https://malwaretips.com/threads/fud-cryptolocker-downloader.69755/Interesting.Do anyone have this ransomware sample post it on Malware Vault for SUD and test the BB.I don't test the AV but @Der.Reisende and othe av tester will check.
Does only work with M$ Office and enabled Macros it seems. Did not work with my Office 2007 installation.
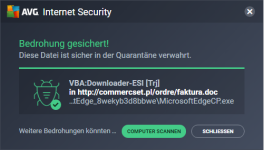
EDIT: AVG detects the payload via OnlineShield clicking on the link provided in the PDF.
Last edited:
- May 7, 2016
- 1,287
Downloaded file is detected as VBA Downloader-ESI[Trj] by avast.
Crypt0L0cker!!!(Zero DAY)
Crypt0L0cker!!!(Zero DAY)
- Apr 28, 2015
- 8,664
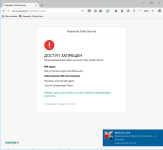
KTS2018 detects the site as malicious, soon at MWHub:https://malwaretips.com/threads/fud-cryptolocker-downloader.69755/
Does only work with M$ Office and enabled Macros it seems. Did not work with my Office 2007 installation.
EDIT: AVG detects the payload via OnlineShield clicking on the link provided in the PDF.
- Mar 15, 2011
- 13,070
I'm not surprise.
As we all know, Antivirus work are done within weekdays regardless if some are implemented with robotic mechanism to gather information.
So likely it's time to change that lax operation.
As we all know, Antivirus work are done within weekdays regardless if some are implemented with robotic mechanism to gather information.
So likely it's time to change that lax operation.
- Feb 21, 2015
- 456
- Aug 7, 2016
- 228
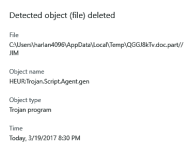
Finally, thank God!
Bravo for ESET!
- Feb 21, 2017
- 613
Does anyone know how to rescan withouth having the file?Finally, thank God!
Bravo for ESET!
I used it like 1 year ago but forgot how its done
- Apr 28, 2015
- 8,664
Here is when different layer protection approach come into... in this case blocking the remote site would be enough to protect the user.
- Jul 22, 2014
- 2,525
I think that lower/no definitions update during weekends is a shame, user should consider this when choosing an AV.
Considering the huge nr. of users some AV have it's incredible they cannot employ someone on the weekends and leave millions of user with lower protection.
Considering the huge nr. of users some AV have it's incredible they cannot employ someone on the weekends and leave millions of user with lower protection.
- Jul 22, 2014
- 2,525
The problem is many AV just have a list of bad sites, no heuristic or other method to detect them.Here is when different layer protection approach come into... in this case blocking the remote site would be enough to protect the user.
If MW author change the site or have multiples (some have 1000+) the AV has problems/won't detect them all.
- Apr 28, 2015
- 8,664
About the lack of Heuristic in Web AV module, not the case of Kaspersky  but agree, even in Kaspersky I've noticed that they relax at weekends, prolonging signature updates, also KL VirusDesk final verdict today is taking longer, as usually at weekends...
but agree, even in Kaspersky I've noticed that they relax at weekends, prolonging signature updates, also KL VirusDesk final verdict today is taking longer, as usually at weekends...
Last edited:
- Jul 22, 2014
- 2,525
Just found a fresh example...It checks 1088 links
Antivirus scan for dd37147fdb5da4de7146e226e5d974d8d553d7e56d35690df5198b699fbb3b7e at 2017-03-19 14:53:25 UTC - VirusTotal
Antivirus scan for dd37147fdb5da4de7146e226e5d974d8d553d7e56d35690df5198b699fbb3b7e at 2017-03-19 14:53:25 UTC - VirusTotal
- Apr 28, 2015
- 8,664
- Jul 22, 2014
- 2,525
Kis is one of the few AV I know that has heuristic for links as a module for scripts... It's most of the time between the first to detect, bad URLs, malware .js,.jse.,.jar etc
- Dec 19, 2012
- 1,244
- Sep 9, 2012
- 470
Some malware which go undetected for several years. What is Flame Malware | Definition and Risks | Kaspersky Lab
- Sep 9, 2012
- 470
Certain together after exclusion will work but KIS is definitely enough. Maybe it just needs a little set KIS and it is.Hi sorry to be off topic but would KIS work with Webroot or is that too much?
Kaspersky Internet Security 2017 Recommended Settings
- Jan 9, 2013
- 1,457
This one is blocked by 360's BB.
Does not work in my netbook without MS Word. If Word Macros are disabled, then you are safe.
Does not work in my netbook without MS Word. If Word Macros are disabled, then you are safe.
Similar threads
- Replies
- 68
- Views
- 7,583
F
Serious Discussion
Harmony Endpoint by Check Point
- Replies
- 677
- Views
- 45,248