It is mostly redundant, when using H_C default-deny settings.So what would be the benefit of using SysHardener with H_C?or is redundant
Hard_Configurator - Windows Hardening Configurator
- Thread starter Andy Ful
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
F
ForgottenSeer 72227
The firewall rules for Sponsors are used in SysHardener, because it cannot block the execution of Sponsors via shortcuts, CHM files and some other files with dangerous extensions. Those vectors of attack are covered by H_C default-deny settings even without blocking Sponsors.
There is no need to use firewall rules or block Sponsors in H_C default-deny settings, when using Windows 10 with updated system/software. Simply, access to the command line will be blocked, and the Sponsor will not be executed. You can see that also from Malware Hub tests. See the sample in the wild:

Shifty new variant of Qbot banking trojan spreads
An active malware campaign primarily targeting U.S. corporations with a new polymorphic variant of the Qbot banking trojan has been compromising thousands of victims around the world, researchers have reported. The worm-like malware, whose original version is roughly a decade old, allows...malwaretips.com
I tried to explain in the FAQ when the user should block Sponsors, especially Interpreters. In rare situations, the user could also use firewall rules instead, when some special software cannot work with blocked Sponsor. This would not be especially effective, but better than nothing. The similar idea would be blocking some special executables by the firewall (like rundll32.exe), which cannot be blocked in H_C, because they are often used in Windows. I am not sure it this help much, but can be done.
Thanks for the clarification. I didn't understand it fully and assumed that the firewall rules were needed as well. In that case I will remove Syshardener as it's already covered in H_C via another method.
Thanks for clarifying it!
If you are a big fan of Sandboxie (paid version), then you do not need H_C. Just use two Explorer instances. One standard Explorer, and the second Sandboxed Explorer. The Sandboxed Explorer should be run via the special shortcut.I'm tempted to try Hard Configurator again. What type of software would be good to add? (If any is needed).
I think about HardConfigurator + Sandboxie (mandatory for me) + X What should X be? System Hardener, Voodoo Shield or...
Would be glad for any helpful input
The daily work can be done in Sandboxed Explorer. Administrator work, installing applications, and updating, via standard Explorer. Unsafe tasks can be run from the standard Explorer right-click menu in the restricted sandbox. You can also block Interpreters by preparing another total-block sandbox, that can run only notepad + disabled Internet connection + disabled read/write access to all drives.
If you want to use Forced SmartScreen for installing applications, then use my Run By SmartScreen tool.
Last edited:
@Andy Ful Guilty as charged, i really like Sandboxie (paid). Thanks for your helpful suggestion to use a sandboxed explorer.
I sandboxed browsers, pdf reader, mediaplayer... but never really thought about the explorer
I sandboxed browsers, pdf reader, mediaplayer... but never really thought about the explorer
Be careful! Do not choose to automatically sandbox the executable explorer.exe, because Sandboxie will sandbox all instances of Windows Explorer. Just make a shortcut that can run Explorer in the sandbox, then you can manually run one instance of explorer.exe in the sandbox.@Andy Ful Guilty as charged, i really like Sandboxie (paid). Thanks for your helpful suggestion to use a sandboxed explorer.
I sandboxed browsers, pdf reader, mediaplayer... but never really thought about the explorer
Last edited:
Like Andy said, if you use Sandboxie paid, and you know what you are doing, and you are disciplined, it can really do a lot.
The guru of sandboxing is Bo Elam. You can find him at Wilders Security and at the official SBIE support forum.
But it isn't easy to build security on Sandboxie alone. There are easier and less frustrating ways of doing it.
The guru of sandboxing is Bo Elam. You can find him at Wilders Security and at the official SBIE support forum.
But it isn't easy to build security on Sandboxie alone. There are easier and less frustrating ways of doing it.
@shmu26 Sadly i don't think my knowledge is good enough to use sandboxie alone. That's why i wanted to use it in a layered approach.
Testing Hard Configurator and Sandboxie on my old laptop. On my main pc i try SUA to see if SUA and i can work together (tried it years ago and i got bad memorys about it). If all went well i think about a clean install (which i hate) and using sandboxie and Hard Configurator also on the main pc.
(tried it years ago and i got bad memorys about it). If all went well i think about a clean install (which i hate) and using sandboxie and Hard Configurator also on the main pc.
Testing Hard Configurator and Sandboxie on my old laptop. On my main pc i try SUA to see if SUA and i can work together
I wouldn't do it either, to tell you the truth. It would be more of a hobby than a practical security setup. But it's fun to talk about it.Sadly i don't think my knowledge is good enough to use sandboxie alone.
H_C on SUA is
If you want to use an old laptop with Windows 7 or Vista, then you cannot use SmartScreen. Furthermore, those Windows versions are easier to be exploited. The good setup would be:
I would like to advise you using first H_C (Recommended settings) on Admin account with Windows 10. You will have fewer problems with installing/updating applications. I assume that you have read the H_C FAQs related to installing and updating applications on SUA....
Testing Hard Configurator and Sandboxie on my old laptop. On my main pc i try SUA to see if SUA and i can work together(tried it years ago and i got bad memorys about it). If all went well i think about a clean install (which i hate) and using sandboxie and Hard Configurator also on the main pc.
If you want to use an old laptop with Windows 7 or Vista, then you cannot use SmartScreen. Furthermore, those Windows versions are easier to be exploited. The good setup would be:
- Apply the AV + H_C on SUA.
- Use applications which are installed in c:\Progran Files or c:\ProgramData (fewer problems with installations/updates).
- Do not use applications which install in the user profile (subfolder of c:\Users).
- Avoid installing applications in Sandboxie sandbox (sandboxes are located in the UserSpace). But, you can use most applications installed in c:\Program Files and run sandboxed.
Last edited:
WD Tamper Protection and ConfigureDefender:
https://malwaretips.com/threads/configuredefender-utility-for-windows-10.79039/post-801518
https://malwaretips.com/threads/configuredefender-utility-for-windows-10.79039/post-801518
Last edited:
Thanks shmu26. It looks very interesting. I will try to integrate some your important suggestions to the current version of FAQ.
Thanks, Andy.Thanks shmu26. It looks very interesting. I will try to integrate some your important suggestions to the current version of FAQ.
By the way, if my "editing" reveals that I misunderstood certain points, don't hesitate to comment. I am hear to learn.Thanks shmu26. It looks very interesting. I will try to integrate some your important suggestions to the current version of FAQ.
Gandalf_The_Grey
Level 85
Verified
Honorary Member
Top Poster
Content Creator
Well-known
Forum Veteran
When i open a new blank page in Word I always get a warning about macros being disabled. How do I remove that warning?
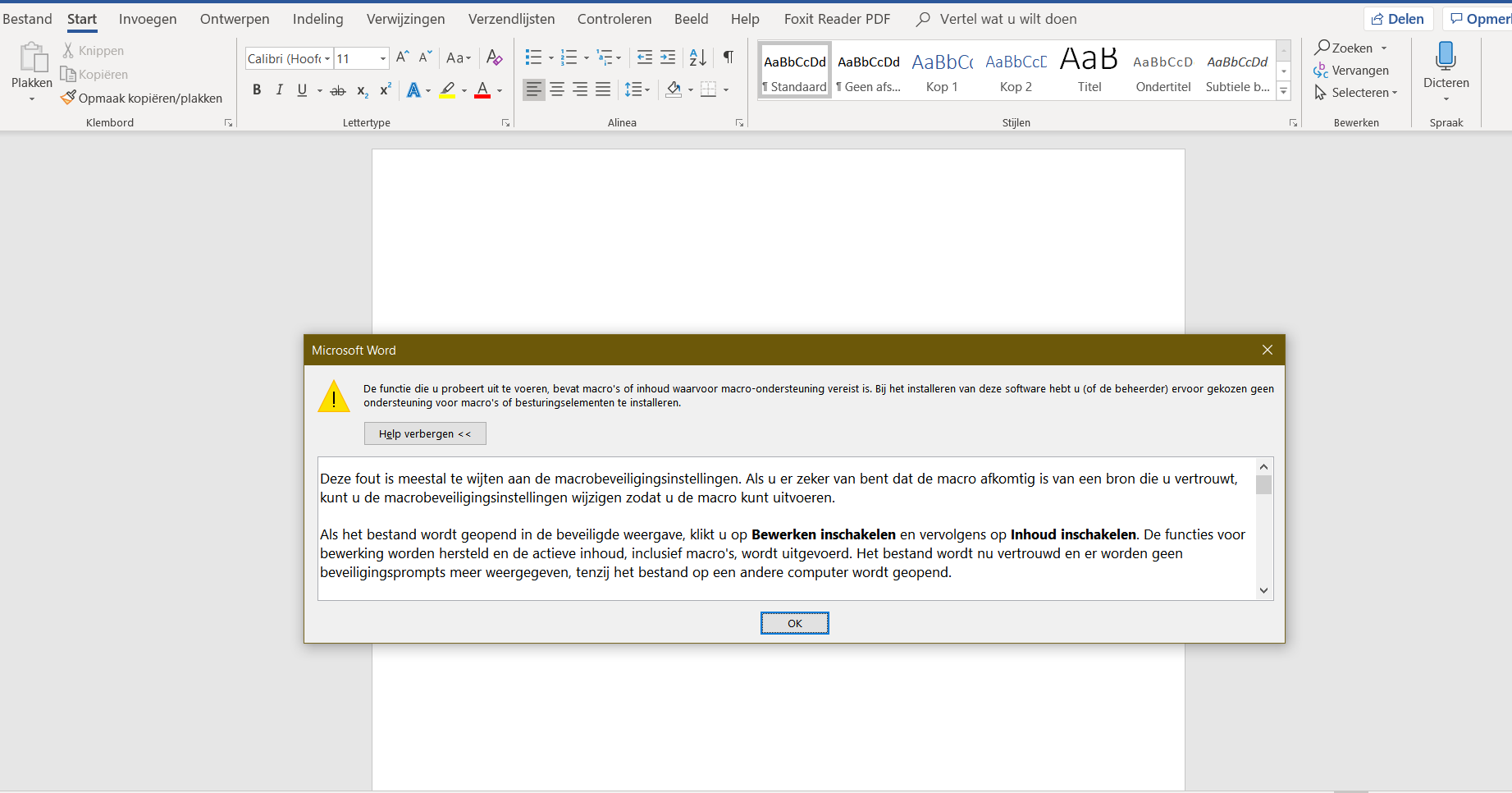
I'm using the Windows 10 Recommended Enhanced profile with Office 365.
I'm using the Windows 10 Recommended Enhanced profile with Office 365.
Have you got this alert before, or this is a new alert.When i open a new blank page in Word I always get a warning about macros being disabled. How do I remove that warning?
View attachment 210219
I'm using the Windows 10 Recommended Enhanced profile with Office 365.
This alert is a sign that something in your Word, tries to run a VBA code (Word template, VBA Add-in, etc.). The alert can be avoided by changing H_C settings, but it would be better to find out why Word tries to run VBA code (probably macro).
The similar problem had @shmu26. If I correctly remember, he used a Word template with macro.
If I correctly remember, he used a Word template with macro.
I believe you are correct.
Yup, if I use Word add-ons, I get various warnings.Have you got this alert before, or this is a new alert.
This alert is a sign that something in your Word, tries to run a VBA code (Word template, VBA Add-in, etc.). The alert can be avoided by changing H_C settings, but it would be better to find out why Word tries to run VBA code (probably macro).
The similar problem had @shmu26. If I correctly remember, he used a Word template with macro.
I can get them from ASR, and they are usually harmless, they don't affect functionality.
And I can get them from system-wide document anti-exploit. Those warnings are more debilitating. They don't let you carry on with your work. My solution is to use document anti-exploit for specific user accounts, but not system-wide.
The system-wide H_C option <Documents Anti-Exploit> set to 'Adobe + VBA' is a very strong mitigation, and it will block any attempts to use VBA code in MS Office applications. It is much stronger than blocking macros in MS Office documents. Usually, the users do not need VBA in MS Office, unless they need the automation macros in templates, Add-ins, etc. In such a case, the system-wide H_C option <Documents Anti-Exploit> should be set to 'Adobe'. Next, MS Office hardening can be done via Switch Default-Deny >> Documents Anti-Exploit . This hardening is valid only for the current account, so it should be done on all user accounts that use MS Office.
You may also like...
-
-
FAI Tells It Like It Is - Microsoft's Wonky Default Deny Roadmaps, Users as Guinea Pigs, "Dilemmas and Paradoxes," and Why SRP Remains King
- Started by ForgottenSeer 114717
- Replies: 44
-
Microsoft testing Windows 11 batch file security improvements
- Started by Parkinsond
- Replies: 0
-
Malware News CrySome RAT : An Advanced Persistent .NET Remote Access Trojan
- Started by Khushal
- Replies: 3
-